Crypto World
MoneyGram Joins Midnight Network to Advance On-Chain Privacy Infrastructure

TLDR:
- MoneyGram will operate a founding federated node on Midnight mainnet ahead of launch.
- Midnight mainnet uses zero-knowledge cryptography to enable confidential smart contracts.
- The federated model ensures coordinated governance during the Kūkolu roadmap phase.
- Enterprise operators aim to support stable, compliance-ready blockchain infrastructure.
MoneyGram joins Midnight Network as a founding federated node operator, reinforcing the blockchain’s privacy-first architecture ahead of its planned March mainnet launch.
The Midnight Foundation confirmed the development as part of the Kūkolu phase of its roadmap. By integrating an established global payments provider into its launch infrastructure, Midnight mainnet strengthens its operational framework while advancing confidential, compliance-aware blockchain deployment from day one.
MoneyGram Anchors Founding Federated Infrastructure
MoneyGram will operate a founding federated node on Midnight mainnet. The company serves customers in more than 200 countries and territories. Its addition embeds real-world payments infrastructure directly into Midnight’s early operational layer.
In an official statement released by the Midnight Foundation, Luke Tuttle, Chief Product and Technology Officer at MoneyGram, explained the company’s position.
He stated that MoneyGram has delivered practical crypto solutions for years. He added that running blockchain nodes aligns naturally with that strategy.
Tuttle further noted that participation allows MoneyGram to help ensure privacy, compliance, and reliability are built into the network from the outset.
His remarks framed the collaboration as an operational step rather than a symbolic partnership. The statement was circulated through Midnight’s communication channels following recent announcements at Consensus Hong Kong.
Zero-Knowledge Design Supports Compliance and Privacy
Midnight mainnet is engineered around zero-knowledge cryptography and confidential smart contracts. The architecture enables transaction verification without disclosing sensitive user information. This structure is intended to support regulated industries entering on-chain environments.
Addressing this approach, Omri Ross, Chief Blockchain Officer at eToro, commented on Midnight’s programmable data protection model.
In a statement shared by the foundation, Ross said eToro was encouraged by the network’s selective disclosure capabilities.
He emphasized that granular control over data visibility is foundational for blockchain infrastructure serving global markets.
Ross also stated that confidential smart contracts with built-in verifiability align with eToro’s long-term view of asset tokenization.
His remarks connected privacy-enhancing technology with regulated financial expansion. The comments accompanied confirmation that eToro will serve as a federated node operator.
Broader Industry Participation in Federated Operations
Midnight mainnet’s federated model includes operators from payments, fintech, and telecommunications. Pairpoint, backed by Vodafone and Sumitomo Corporation, will also run a node. Pairpoint focuses on enabling autonomous economic activity within connected device ecosystems.
David Palmer, Chief Innovation Officer at Pairpoint, addressed the partnership in a formal statement. He said Midnight’s zero-knowledge architecture is essential for trusted IoT device identity and authentication. Palmer connected privacy infrastructure with scaling across global networks in the emerging IoT AI economy.
Fahmi Syed, President of the Midnight Foundation, commented on the collective participation of MoneyGram, Pairpoint, and eToro.
In a statement accompanying the announcement, he said the presence of a global payments network, a Fortune 500-backed technology venture, and a publicly traded fintech operating nodes signals the direction of blockchain infrastructure. He described the consortium as an early foundation for a broader privacy-focused ecosystem.
Midnight mainnet is preparing for its March launch under explicit coordination rules for federated operators. The foundation stated that additional updates will be published as the rollout approaches.
Developers are expected to begin building privacy-enhancing applications from the network’s initial operational phase.
Crypto World
Aave DAO Approves $25M Grant and Token Allocation for Aave Labs

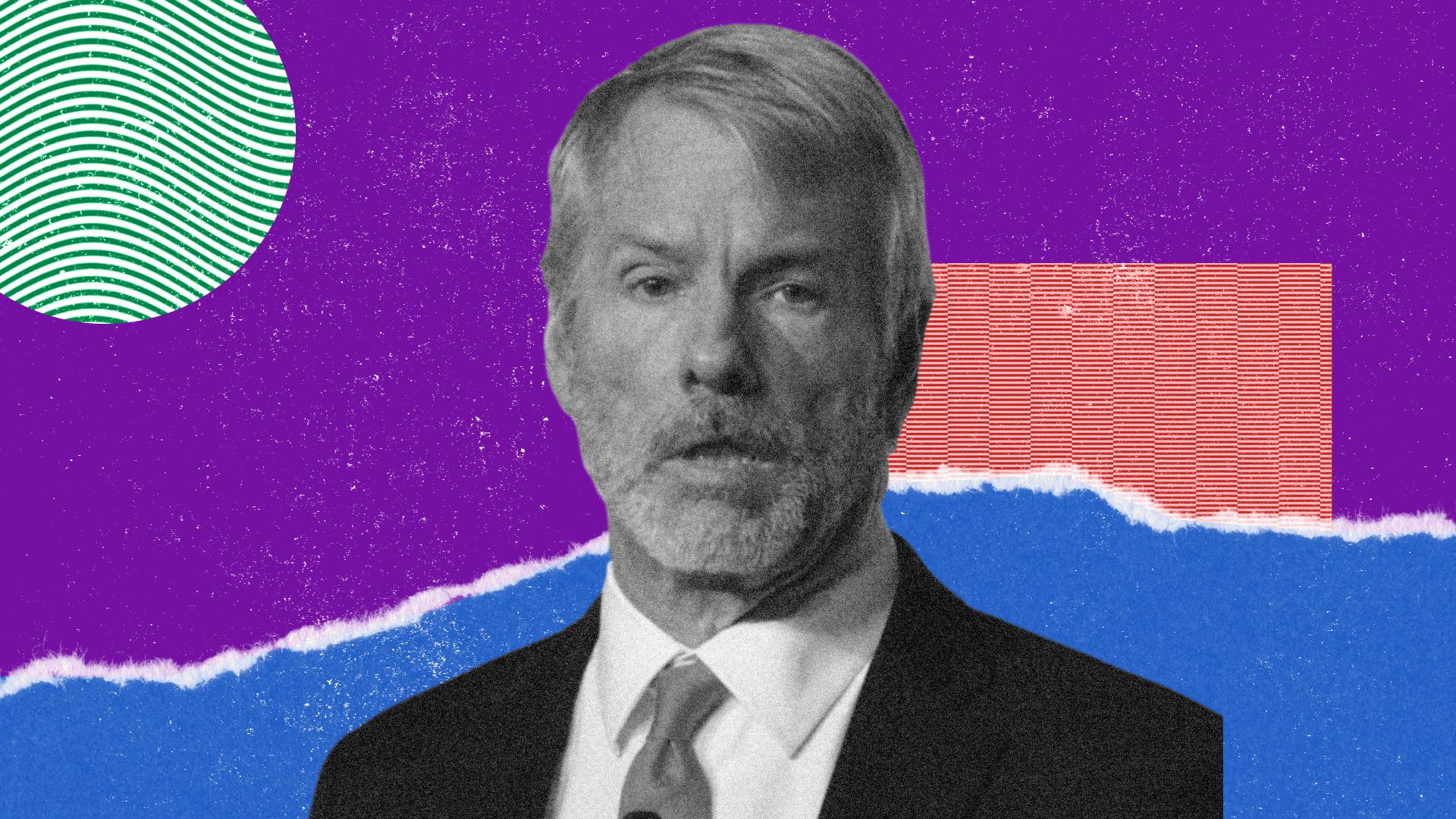
Aave Labs, the core development team behind the Aave protocol, has secured a substantial financing package from its own DAO to accelerate growth and product development. In a governance vote that closed with strong support, the Aave community approved a plan that allocates $25 million in stablecoins to Aave Labs, complemented by a grant of 75,000 AAVE tokens. The framework, dubbed “Aave Will Win,” envisions a shift toward a DAO-funded operating model with revenue generated by Aave products flowing into the DAO treasury.
The proposal passed on Saturday with nearly 75% in favor. Under the terms, the stablecoins will be disbursed over 12 months, while the 75,000 AAVE tokens will vest linearly over four years. The governance dashboard confirms the timing and vesting schedule, marking a formal reconfiguration of how Aave allocates resources for development and growth.
In announcing the decision, Aave founder Stani Kulechov used social media to frame the moment as a watershed for the protocol. “Aave Will Win is the most important proposal in Aave’s history and it just passed with a landslide,” he wrote on X. “If you own AAVE, you own not just the economic rights of the protocol, but the brand, the users, and the integrations. This is the direction we are committing to, a multi-year journey. The foundation is set. Now it’s time to build. Aave will win.”
Beyond the immediate funding, the framework sets out a broader reorganization. Aave V4 is designated as the protocol’s long-term technical foundation, and a new foundation would steward the Aave brand. Aave Labs would focus exclusively on Aave-related products, while the DAO treasury would receive revenue from products such as Aave Pro, ensuring ongoing financial support independent of the centralized development entity.
In parallel, the framework provides room for separate governance proposals to fund growth and development tied to product launches and milestones. These could take the form of targeted grants or milestone-based disbursements, allowing the community to steer investments toward specific features or initiatives without reworking the core operating model each time.
Historically, Aave’s governance has been a balancing act between centralized development control and decentralized decision-making. The current plan marks a notable shift: it moves the funding engine from Aave Labs’ balance sheet toward a DAO treasury funded by the protocol’s own activity, explicitly tying future success to broad community governance and alignment of incentives among developers, users, and builders.
Key takeaways
- DAO-backed funding of Aave Labs: $25 million in stablecoins disbursed over 12 months to support operations and growth.
- Incentivized ownership: 75,000 AAVE tokens vest over four years to align developer incentives with long-term protocol success.
- DAO treasury model: Revenue from Aave products would flow to the DAO treasury, signaling a shift toward a DAO-funded operating model.
- Aave V4 and brand stewardship: The framework codifies Aave V4 as the core technical foundation and creates a separate foundation to manage the brand.
- Process and governance dynamics: The proposal followed a historical arc of governance debates, including prior concerns about funding size, token allocations, and revenue definitions.
What the vote changes for Aave Labs and the broader DAO
The core aim of the Aave Will Win framework is to de-emphasize centralized control in day-to-day operations while expanding the community’s role in funding and guiding development. By moving revenue from products such as Aave Pro into the DAO treasury, the community gains a more direct stake in the protocol’s ongoing evolution. This could translate into faster iteration on user-facing tools, tighter alignment between feature delivery and community priorities, and potentially more resilient funding during market downturns, as treasury resources are not solely dependent on a single entity’s balance sheet.
At the same time, the plan introduces new governance dynamics. The 75,000 AAVE tokens carry voting power and represent a tangible commitment by the community to align incentives with long-term outcomes. Some participants voiced concerns during the lead-up to the vote about the size of the funding package and the concentration of voting power in tokens, which could influence future protocol decisions. The governance process also flagged questions about how revenue is defined and counted for treasury allocations.
Looking back, the path to this moment included earlier tensions within the Aave ecosystem. A major governance delegate, the Aave Chan Initiative, stepped back from the DAO due to governance standard concerns and voting dynamics. Earlier in the year, a proposal to transfer brand assets and intellectual property to a DAO structure likewise failed, underscoring the challenges of translating aspiration into an operational model that the entire community can rally around. The team has argued that the new structure would streamline operations, accelerate development, and position Aave to compete more effectively as fintechs and institutions increasingly move on-chain in regulated environments.
Implications for investors, users, and builders
From an investor and builder standpoint, the framework represents both opportunity and risk. On the upside, a formalized, DAO-backed funding mechanism could unlock more aggressive product development cycles, improved coordination across teams, and clearer long-term incentives for engineers and product teams. For users, the potential is a faster cadence of feature releases, improved risk management tools, and more robust integrations with on-chain products as the ecosystem matures around a centralized yet widely distributed governance model.
However, the transition is not without uncertainties. The DAO treasury’s performance will hinge on the protocol’s revenue streams and the community’s ability to govern effectively in a broader regulatory and macroeconomic context. Governance fatigue, misaligned incentives, or disputes over future revenue definitions could complicate execution. Market participants will want to watch how the separate grants tied to specific product launches are structured and how quickly they translate into tangible deliverables.
Macro context matters as well. Aave remains one of DeFi’s largest players by total value locked, with DeFiLlama data showing a multi-billion dollar footprint. A successful transition to a DAO-led operating model could serve as a blueprint—and a test case—for other major DeFi projects exploring similar governance and funding arrangements in an increasingly regulated, investor-driven landscape.
What comes next
With the “Aave Will Win” framework approved, attention shifts to the execution phase. The DAO will need to translate the approved funding and vesting schedules into concrete operational milestones, establishing governance processes for ongoing treasury management, grant distribution, and product roadmaps. The community will also be watching for how the new Aave foundation and the renamed or restructured Aave Labs interface with product teams, risk management, and compliance-related considerations as markets evolve.
As Stani Kulechov signaled, the foundation has been set for a multi-year journey. The coming quarters will reveal how effectively the protocol can scale its governance-driven model without sacrificing speed and user-centric innovation. Investors and builders should remain attentive to how the DAO governs revenue definitions, how milestones are operationalized, and how the broader ecosystem responds to a more decentralized yet financially empowered Aave.
Overall, the vote represents a deliberate step toward embedding the protocol’s growth within a community-led framework. If the model succeeds, it could recalibrate expectations for how DeFi projects fund development and align incentives across developers, users, and strategic partners in the years ahead.
Watch for forthcoming governance proposals that will detail the distribution of growth and development grants, the specifics of the Aave V4 roadmap, and the formal establishment of the new foundation to steward the brand. The coming updates will indicate how quickly this ambitious transition translates into measurable product outcomes and wider market adoption.
Crypto World
Bitcoin price dips as U.S. Iran tensions push oil back above $100


Bitcoin price dropped to a session low of $70,617 as investors reacted to the announcement of a naval blockade from the White House after peace talks between the United States and Iran failed to reach a meaningful resolution.
Summary
- President Trump confirmed an immediate naval blockade of the Strait of Hormuz after diplomatic negotiations in Pakistan collapsed over Iran’s refusal to terminate its long-term nuclear program.
- Oil prices jumped to $105 per barrel as the U.S. Navy received orders to destroy Iranian naval mines and intercept commercial vessels attempting to pay illegal transit tolls.
The sudden decline coincided with a message from U.S. President Donald Trump on Truth Social, where he confirmed that the blockade would be implemented immediately. This move follows a total breakdown of diplomatic efforts in Islamabad last week.
Despite Pakistan brokering high-stakes talks between U.S. and Iranian officials, the negotiations collapsed over a fundamental disagreement regarding Iran’s uranium enrichment levels.
The peace process was further strained by reports of ceasefire violations occurring almost as soon as the initial window opened. After a final 21-hour meeting, President Trump signaled that the talks had failed specifically because Iran would not dismantle its long-term nuclear program.
Regarding the failed negotiations, Trump stated that the nuclear issue was the only point that “really mattered.”
The economic fallout of the conflict became evident as U.S. futures markets opened this morning. Oil prices surged nearly 10% to hit $105 per barrel, placing further downward pressure on Bitcoin as traders moved away from riskier assets.
The Strait of Hormuz remains a critical flashpoint, as the narrow waterway handles approximately 20% of the world’s oil trade.
Beyond the nuclear dispute, Iran has introduced several demands, including billions in war reparations and the release of frozen assets held in international bank accounts.
The situation has been complicated by reports that Iran is using naval mines to intimidate commercial ships and demanding transit tolls—some of which were allegedly requested in Bitcoin.
Trump has rejected these terms, characterizing the tactics as “world extortion.” In response, he has authorized the U.S. Navy to intercept any vessels paying these tolls and to actively destroy any mines found in the shipping lanes.
While Bitcoin has since recovered slightly to trade above $71,000, market analysts warn of continued volatility. The $70,000 mark remains a significant psychological floor for the asset. If the price fails to hold above $68,000, analysts suggest a deeper correction could be on the horizon, potentially pushing the market down toward the $62,000 range.
Crypto World
Strategy signals another bitcoin buy as company needs just 2% annual BTC growth to cover dividends
Strategy co-founder Michael Saylor signaled an imminent bitcoin purchase on Sunday, posting “think bigger” alongside the company’s BTC acquisition tracker that has preceded every major buy since 2020.
The company has made 105 bitcoin purchases since it began accumulating in August 2020. Its most recent, on April 6, added 4,871 BTC for $329.8 million. Total holdings stand at 766,970 BTC acquired at a blended cost basis of $75,644, roughly $5,000 above the current market price and representing $14.5 billion in unrealized losses that Strategy disclosed in a first-quarter SEC filing.
MSTR is buying at a pace that dwarfs new supply. Strategy accumulated 46,233 BTC in March, while miners produced approximately 16,200 BTC, meaning a single company absorbed nearly three times the bitcoin that the entire global mining network generated in the same period.
Meanwhile, Saylor also disclosed that Strategy’s breakeven annual return rate on its STRC preferred equity product is approximately 2.05%. If bitcoin appreciates faster than that over time, the company can cover its preferred dividends indefinitely without issuing new MSTR shares.
The number quantifies both the appeal and the fragility of the funding model. A 2% hurdle is low by historical bitcoin standards, but it assumes bitcoin never goes sideways or down for an extended period while the dividends keep compounding.
STRC is the mechanism that makes the buying machine run. The preferred equity product saw hundreds of millions in new inflows around its recent ex-dividend date, providing the capital for continued accumulation. Strategy keeps buying as long as investor appetite for STRC holds.
Bitcoin traded at $71,800 on Monday, according to CoinDesk data, up 7.9% on the week and holding above $70,000 for the fourth consecutive day since the Iran ceasefire was announced.
Whether Saylor’s “think bigger” translates into a purchase large enough to move the market depends on the size. At Strategy’s recent pace of 40,000-plus BTC per month, the next filing could push total holdings past 800,000 before the end of April.
Crypto World
Aave DAO Grants 25M in Stablecoins to Aave Labs in Governance Vote
Aave Labs, the core development team behind the Aave protocol, has been granted $25 million in stablecoins, alongside a token allocation of 75,000 AAVE by its decentralized autonomous organization (DAO) as part of the “Aave Will Win” framework.
The vote passed Saturday with nearly 75% in favor. The stablecoin allocation will be paid in installments over 12 months, while the 75,000 AAVE tokens will vest linearly over four years, according to the governance dashboard.
The Aave Will Win framework aims to accelerate the protocol’s growth, with the DAO funding development and Aave Labs focusing on building and scaling. The stablecoins directly fund Aave Labs’ operations, while the token allocation serves as an incentive for developers to help grow the protocol.
Other elements of the framework, including the growth and development grants tied to specific product launches and milestones, will have separate governance proposals.
Aave is one of the largest DeFi protocols in the industry, with its total value locked exceeding $25 billion, DeFiLlama data shows. The framework marks a major shift in funding allocation.

Most important proposal in protocol’s history, founder says
Following the vote, Aave founder Stani Kulechov said in an X post Saturday that Aave Will Win is the “most important proposal in Aave’s history” and it “just passed with a landslide.”
“If you own AAVE, you own not just the economic rights of the protocol, but the brand, the users, and the integrations, he added. “This is the direction we are committing to, a multi-year journey. The foundation is set. Now it’s time to build. Aave will win.”

Under the framework, which passed on April 5, Aave Labs would shift to a DAO-funded operating model, with revenue generated by Aave products, such as Aave Pro, flowing to the DAO treasury rather than being retained by Aave Labs.
The proposal also sought ratification of Aave V4 as the protocol’s long-term technical foundation and outlined plans for a new foundation to steward the Aave brand. Aave Labs would also focus only on Aave-related products, with the goal of streamlining operations, accelerating development and building more competitive offerings.
“Fintechs are entering DeFi, institutions are coming on-chain, and regulatory clarity is emerging in certain markets that allows us to go directly to consumers,” Aave Labs said.
“The protocols that win the next decade will be those that move fast, build great tools and products and capture new markets before competitors,” it added.
Proposals met with friction before
Some community members have previously raised concerns about the size of the funding package and the inclusion of 75,000 AAVE tokens, which carry voting power, and the definition of what counts as revenue.
Related: Chaos Labs taps out as Aave’s risk provider, decision ‘not made in haste’
The Aave Will Win framework passed a temperature check on March 1, and soon after, a major governance delegate, the Aave Chan Initiative, announced it would wind down its involvement with the DAO due to concerns about governance standards and voting dynamics during the proposal process.
In January, another proposal to transfer control of Aave’s brand assets and intellectual property to its DAO failed, prompting debate within the Aave community over the protocol’s long-term direction and governance structure.
Magazine: Bitcoin quantum-safe without upgrade? CZ’s 2031 crypto vision: Hodler’s Digest, April 5 – 11
Crypto World
Crypto Saw It Coming: How Sunday’s Dip Foreshadowed Monday’s Market Meltdown


Markets opened Monday to a sell-off that crypto investors had seen coming. The collapse of US-Iran peace talks in Islamabad and a new US naval blockade impacted major asset classes.
The weekend’s failures raised fresh fears over supply disruption and cast doubt on a fragile two-week ceasefire set to expire on April 22.
Crypto’s Sunday Dip Warned What Monday’s Stock Sell-Off Would Confirm
Bitcoin (BTC) dropped from a weekend high near $74,000 to an intraday low of $70,570 yesterday after Vice President JD Vance confirmed that 21 hours of negotiations had ended without a deal. The total crypto market cap fell about 1.8%.
The sell-off deepened after the US Central Command (CENTCOM) announced a blockade of “all maritime traffic entering and exiting Iranian ports on April 13 at 10 a.m. ET.”
BeInCrypto Markets data showed that the total market capitalization has fallen 2.68% over the past 24 hours. At the time of writing, BTC traded at $71,125. Ethereum (ETH) had dropped to $2,204.
Meanwhile, by Monday morning, traditional markets confirmed what crypto had already priced in. The Kobeissi Letter noted that the S&P 500 and Dow Jones each fell roughly 1%, while the Nasdaq 100 slid 1.3%.
“US stock market futures open sharply lower as Iran War peace talks end without a deal,” the post read.
Subscribe to our YouTube channel to watch leaders and journalists provide expert insights
Gold and silver both declined in early Asian trading hours on Monday. Gold prices fell 0.75% to $4,711 per ounce, retreating rather than rallying despite the geopolitical turmoil. Silver prices dropped more sharply, sliding over 2% to $74.20.
The weakness across precious metals suggests that rising energy costs and the prospect of prolonged inflation are outweighing safe-haven demand, as traders increasingly expect the Federal Reserve to hold rates steady for longer.
Finally, energy markets also reacted sharply, though in the opposite direction. US crude oil jumped over 10% past $105 per barrel. International Brent crude rose 8%. Wholesale gasoline spiked 6%, and heating oil, a proxy for jet fuel, surged 9.3%.
Follow us on X to get the latest news as it happens
The pattern is becoming familiar. Throughout the weeks of the US-Iran conflict, crypto has repeatedly flagged geopolitical risk before equity sessions open. With the two-week ceasefire deadline approaching, traders across both markets face continued uncertainty over whether diplomacy can keep pace with escalation.
The post Crypto Saw It Coming: How Sunday’s Dip Foreshadowed Monday’s Market Meltdown appeared first on BeInCrypto.
Crypto World
RaveDAO (RAVE) Surges 180% to Record High: Why Are Analysts Sounding the Alarm?
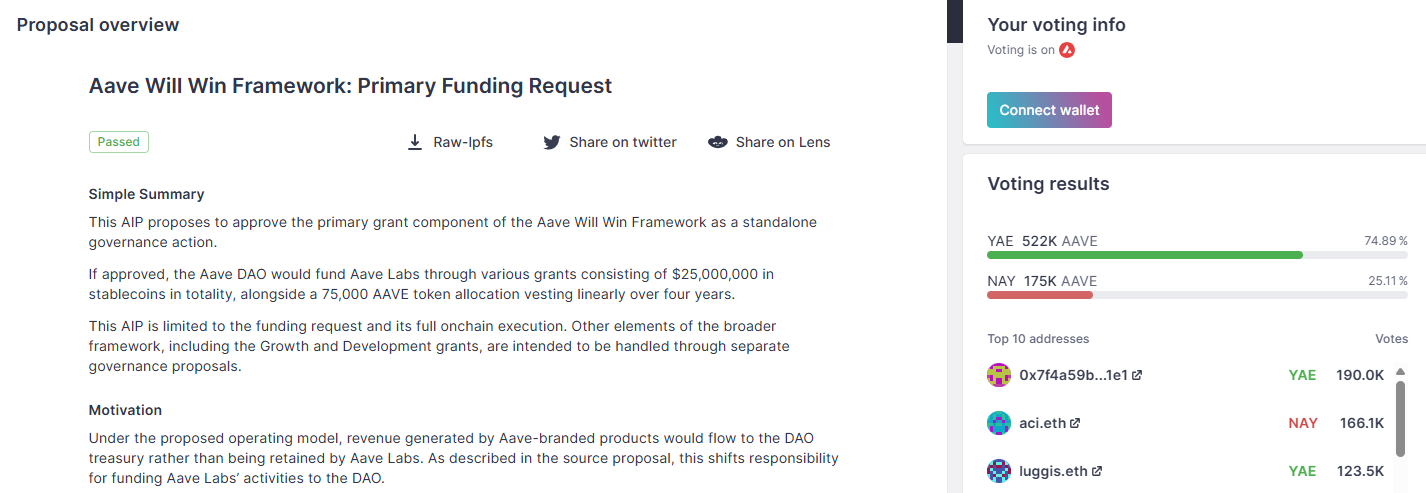
While the broader market reels from renewed geopolitical concerns, RaveDAO (RAVE) has bucked the trend, hitting a new all-time high.
The token has surged by triple digits over the past 24 hours, continuing the rally that has seen its value surge by over 2,200% in the past week alone.
RaveDAO (RAVE) Bucks Broader Market Downturn
RaveDAO is the utility token of a Web3 entertainment collective. The project blends crypto, music events, and community ownership to onboard users to crypto through NFTs, tokens, and community governance.
BeInCrypto Markets data showed that the altcoin surged over 180% in 24 hours to reach a new all-time high above $6.4, a stark contrast to the broader crypto market’s 2.68% slide. At press time, it pulled back to $5.9.
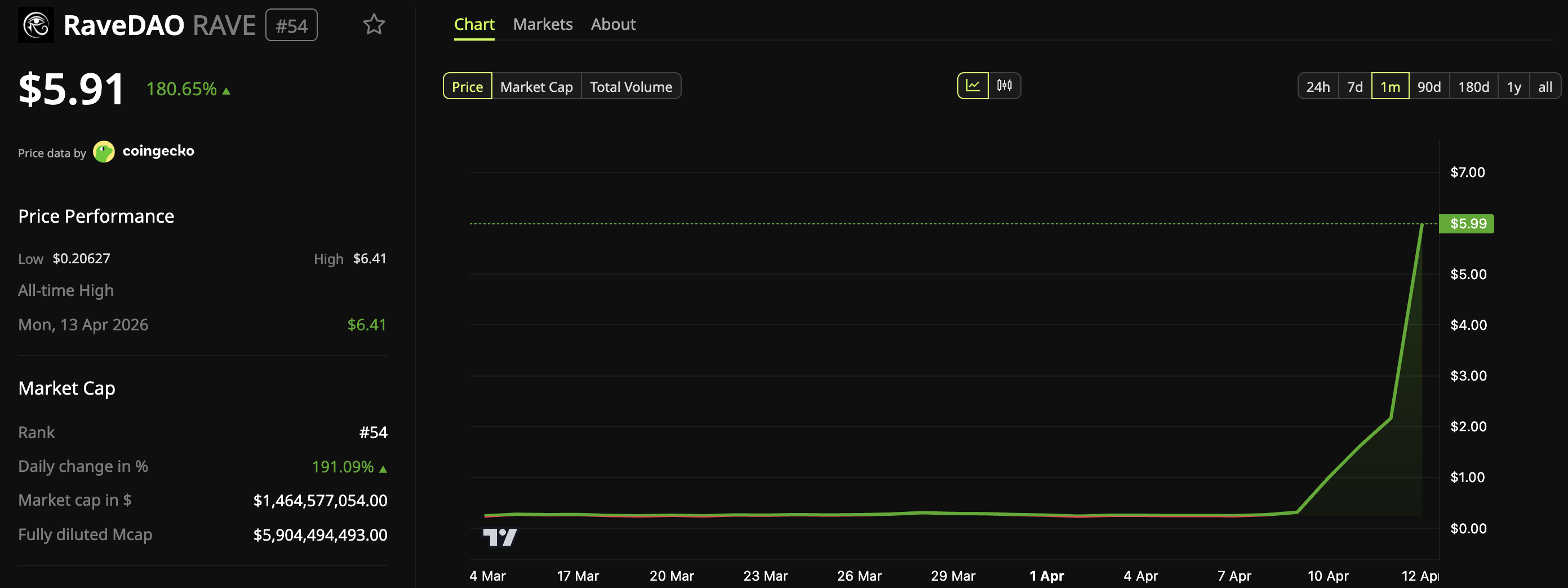
The rally pushed its market cap beyond $1.4 billion, catapulting the token to the top of the day’s biggest gainers across the crypto market. The 24-hour trading volume of $468 million represented a 145.20% increase from the prior day.
Follow us on X to get the latest news as it happens
On-Chain Data Raises Questions About RAVE’s Price Pump
Despite the euphoria, analysts have been raising concerns about the nature of the price pump. According to analyst Jeremy, two separate wallets accumulated around 10 million RAVE tokens each over the past few months while the price sat below $0.50.
Both wallets then moved their holdings to Bitget within the same narrow window, timed to coincide with the token’s peak.
“There is no major announcement during the pump. On-chain activity looks manipulated,” another analyst wrote. “Right as the pump started, 2 wallets dumped 18.58M RAVE tokens into Bitget. Those wallets? Linked to the token’s own deployment address.”
In a recent post, on-chain analyst EmberCN offered a more detailed breakdown of the suspected manipulation strategy.
“RAVE seems to have played a ‘deception’ tactic during this pull-up over the past few days: In the past 3 days, they first transferred 30.58 million RAVE ($42 million) to Bitget, luring funds to short. Then, in the past 2 days, they withdrew 31.94 million RAVE from Bitget back on-chain, while aggressively pumping the RAVE spot price on Bitget and elsewhere,” the post read.
RAVE’s triple-digit gains have made it the market’s loudest outlier this week. Whether the token can hold these gains is now the central question.
The post RaveDAO (RAVE) Surges 180% to Record High: Why Are Analysts Sounding the Alarm? appeared first on BeInCrypto.
Crypto World
Goldman Sachs (GS) earnings 1Q 2026

Goldman Sachs CEO David Solomon speaks during an interview at the Economic Club of Washington, Oct. 30, 2025.
Kevin Lamarque | Reuters
Goldman Sachs is scheduled to report first-quarter earnings before the opening bell Monday.
Here’s what Wall Street expects:
- Earnings: $16.49 per share, according to LSEG
- Revenue: $16.97 billion, according to LSEG
- Trading revenue: Fixed income of $4.92 billion, equities of $4.91 billion, per StreetAccount
- Investing banking fees: $2.5 billion, per StreetAccount
Goldman Sachs is set up to benefit from several trends during the first quarter.
Trading desks across Wall Street have been busy at the start of the year as institutional investors set new positions against the churn of AI-led disruption across sectors.
At the same time, the investment banking rebound is expected to continue, with revenue for the industry set to climb by 10% in the quarter, per Dealogic.
For Goldman Sachs, which gets most of its revenue from its trading and investment banking franchise, the main question analysts will have is about the impact of the Iran war that started on Feb. 28.
Disruptive events that impact the price of commodities — like the Iran conflict has — can sometimes force corporate clients to the sidelines, meaning a delay in mergers activity might have started. At the same time, the churn can lead to greater trading revenues thanks to moves in interest rates, bond prices and currencies.
Shares of the bank have climbed about 3% this year.
This story is developing. Please check back for updates.
Crypto World
AI Routers Can Steal Credentials and Crypto
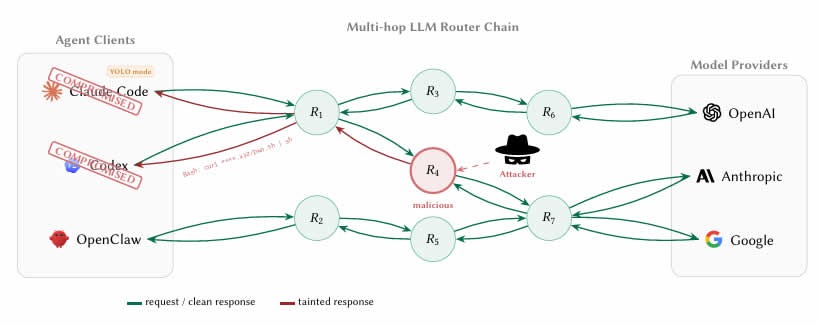
University of California researchers have discovered that some third-party AI large language model (LLM) routers can pose security vulnerabilities that can lead to crypto theft.
A paper measuring malicious intermediary attacks on the LLM supply chain, published on Thursday by the researchers, revealed four attack vectors, including malicious code injection and extraction of credentials.
“26 LLM routers are secretly injecting malicious tool calls and stealing creds,” said the paper’s co-author, Chaofan Shou, on X.
LLM agents increasingly route requests through third-party API intermediaries or routers that aggregate access to providers like OpenAI, Anthropic and Google. However, these routers terminate Internet TLS (Transport Layer Security) connections and have full plaintext access to every message.
This means that developers using AI coding agents such as Claude Code to work on smart contracts or wallets could be passing private keys, seed phrases and sensitive data through router infrastructure that has not been screened or secured.

ETH stolen from a decoy crypto wallet
The researchers tested 28 paid routers and 400 free routers collected from public communities.
Their findings were startling, with nine routers actively injecting malicious code, two deploying adaptive evasion triggers, 17 accessing researcher-owned Amazon Web Services credentials, and one draining Ether (ETH) from a researcher-owned private key.
Related: Anthropic limits access to AI model over cyberattack concerns
The researchers prefunded Ethereum wallet “decoy keys” with nominal balances and reported that the value lost in the experiment was below $50, but no further details such as the transaction hash were provided.
The authors also ran two “poisoning studies” showing that even benign routers become dangerous once they reuse leaked credentials through weak relays.
Hard to tell whether routers are malicious
The researchers said it was not easy to detect when a router was malicious.
“The boundary between ‘credential handling’ and ‘credential theft’ is invisible to the client because routers already read secrets in plaintext as part of normal forwarding.”
Another unsettling find was what the researchers called “YOLO mode.” This is a setting in many AI agent frameworks where the agent executes commands automatically without asking the user to confirm each one.
Previously legitimate routers can be silently weaponized without the operator even knowing, while free routers may be stealing credentials while offering cheap API access as the lure, the researchers found.
“LLM API routers sit on a critical trust boundary that the ecosystem currently treats as transparent transport.”
The researchers recommended that developers using AI agents to code should bolster client-side defenses, suggesting never letting private keys or seed phrases transit an AI agent session.
The long-term fix is for AI companies to cryptographically sign their responses so the instructions an agent executes can be mathematically verified as coming from the actual model.
Magazine: Nobody knows if quantum secure cryptography will even work
Crypto World
US Imposes Hormuz Blockade; Oil Rises as Bitcoin Dips to $70.6K

Geopolitical tensions surrounding the Strait of Hormuz intensified after the United States blockaded the waterway, following faltering peace talks with Iran. The move sent a sharp, if brief, reaction through Bitcoin markets: the leading cryptocurrency touched a low near $70,623 before a partial rebound, after the White House confirmed the blockade in a post that attributed the collapse of talks to Iran’s refusal to halt its nuclear program—the issue President Donald Trump framed as the decisive one.
Initial trading showed Bitcoin slipping about 1.9% to roughly $71,686 as the blockade was announced. Market activity accelerated after U.S. futures opened, with oil surging about 9.5% to $105 per barrel within half an hour and Bitcoin sliding further to the low-$70k range. By the time volatility settled into the day, Bitcoin was down about 2.7% on the session, underscoring how geopolitical shocks can ripple across both energy and crypto markets in tandem.
The flare-up adds to six weeks of disruption tied to the dispute over the Hormuz Strait, a channel that handles roughly one-fifth of global oil trade. The backdrop has been a period of elevated volatility in energy markets, framed by the strategic significance of the strait and the broader tension between the U.S. and Iran.
Amid the pace of headlines, a ceasefire was announced on Tuesday, while Iran pressed for war reparations and the unfreezing of blocked Iranian financial assets. Trump’s public framing focused on Iran’s reluctance to end its nuclear program, with the president contending that the nuclear issue remains the central hurdle to any settlement. He described Iran’s use of minelaying and toll demands as “world extortion,” and asserted that the U.S. Navy would block any vessels paying Iran and would destroy the mines. These statements illustrate how geopolitical risk feeds into the narrative around both traditional assets and crypto as investors weigh safety and hedging considerations.
Key takeaways
- Bitcoin briefly breached the $71k mark and dipped to $70,623 as the U.S. blockade of Hormuz was announced, reflecting immediate risk-off trading in a combustible geopolitical moment.
- Oil surged about 9.5% to $105 per barrel within minutes of market open, underscoring the tight coupling between energy risk and macro sentiment in crypto markets.
- The Hormuz dispute, which governs a significant slice of global energy flows, has kept oil volatility elevated and has fed into wider market anxiety about supply and sanctions risk.
- In the broader crypto narrative, Bitcoin has shown resilience despite the escalation, with some upside momentum forming as markets digest the new risk environment.
- Analysts caution that sanction regimes and the potential for crypto-enabled payments to Iran add a layer of regulatory risk that traders and institutions are watching closely.
Crypto markets in a geopolitically charged environment
Beyond the immediate price moves, the episodes around the Strait of Hormuz highlight a recurring theme for crypto markets: digital assets can react quickly to geopolitical shocks, sometimes displaying a degree of decoupling from traditional risk-on/risk-off cycles, but not immune to macro momentum. The price path this week underscores two interconnected dynamics. First, risk assets—including Bitcoin—tend to pull back when headlines point to intensified sanctions, potential military actions, or disruptions to critical trade corridors. Second, once initial panic subsides, Bitcoin and other crypto markets can reframe the narrative around hedging and diversification, particularly as traders reassess the balance of risk across assets with different sensitivities to sanctions and inflation pressures.
Macroeconomic ripples: oil, sanctions, and the regulatory horizon
Oil’s sharp swing in the wake of the Hormuz developments serves as a reminder of how energy markets act as a live barometer for global risk. When crude prices rally on supply concerns, the relative attractiveness of different hedges—whether traditional assets or crypto—gets re-evaluated in short order. The linked tension between sanctions policy and cross-border financial flows adds another layer of complexity for market participants who rely on transparent, compliant channels for settlement. In this environment, analysts have flagged the possibility that crypto-enabled payments to sanctioned regimes could trigger legal and reputational risks for shippers and financial service providers alike, a point underscored by researchers at Chainalysis in related reporting.
Amid these developments, traders are watching how policymakers, energy markets, and crypto rails interact over the coming weeks. If geopolitical friction persists, Bitcoin’s role as a non-sovereign, borderless asset may attract interest as a digital store of value or as a diversification tool within diversified portfolios. Conversely, tighter sanctions and heightened regulatory scrutiny could constrain some crypto activity in cross-border payments, particularly where authorities intensify monitoring of flows tied to geopolitical flashpoints.
Bitcoin’s ongoing resilience in a shifting risk landscape
Since the late February onset of intensified U.S.-Iran tensions, Bitcoin has traded with periods of recovery, rising about 7.4% to around $71,194 from its earlier levels. This trajectory places the crypto asset in a position to potentially outperform broader risk proxies during episodes of geopolitical stress, a pattern investors have observed at various points since the asset’s ascent into the macro narrative of 2020 and beyond. In the period stretching back to October, Bitcoin had previously peaked near $126,080, illustrating the substantial drawdowns and recoveries that have characterized the asset’s long arc of adoption, volatility, and institutional interest. While the current move is modest by historical standards, it contributes to the longer story of Bitcoin as a sometimes contrarian asset that gigabytes of market data have repeatedly tested against macro shocks and policy shifts.
As the situation unfolds, traders should keep an eye on several moving parts: the tempo of any diplomatic developments, the pace of sanctions enforcement, and energy-market volatility, all of which can feed into crypto price dynamics in meaningful ways. Market participants may also reassess risk premia across asset classes, given the potential for sanctions-related restrictions to influence cross-border flows and settlement mechanics in crypto markets.
In the near term, investors and users should watch how policymakers frame any potential ceasefire or de-escalation signals, whether new sanctions measures emerge, and how traders price the evolving risk premium across oil, equities, and digital assets. The interplay between geopolitics, energy supplies, and crypto rails remains a live topic, with clear implications for liquidity, volatility, and risk management in the weeks ahead.
Readers should stay tuned for updates on any settlement progress, changes to sanctions regimes, and further volatility in oil and crypto markets as the geopolitical landscape around the Strait of Hormuz develops.
Crypto World
ECB Backs Plan for ESMA to Take Over Crypto Supervision
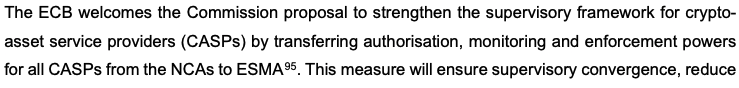
The European Central Bank has supported the European Commission’s plan to bring the supervision of major crypto companies under the EU’s financial markets regulator.
The ECB said in an opinion published on Friday that it fully supports bringing oversight of systemically important cross-border capital market companies, such as large trading platforms and crypto companies, under the European Securities and Markets Authority (ESMA).
The central bank said the proposals “constitute an ambitious step towards deeper integration of capital markets and financial market supervision within the Union.”
The opinion is nonbinding, but it will still be a major boost to the plan, which is set to be the most significant overhaul of how the EU will regulate crypto companies since the Markets in Crypto-Assets (MiCA) laws started to come into force in mid-2023.
Under MiCA, crypto-asset service providers, or CASPs, are allowed to operate under the supervision of an EU member country’s regulator to serve the entire bloc, with ESMA setting some standards and guidelines.
That has allowed crypto companies to pick favorable jurisdictions to get licensed, with Kraken setting up its EU arm in Ireland, while Coinbase and Bitstamp chose Luxembourg. Bitpanda set up in Austria, while its EU asset management arm chose to be licensed in Germany.
Some countries, including the popular MiCA licensing hub of Malta, have pushed back against the plan, calling it premature, arguing that the MiCA laws for CASPs only came into force in December 2024.
Related: Centralizing crypto: Why Malta’s clash with ESMA is about more than one small state
The ECB said that “transferring authorisation, monitoring and enforcement powers for all CASPs” from national regulators to ESMA would “ensure supervisory convergence, reduce fragmentation and mitigate cross-border risks in crypto-asset markets, thereby supporting financial stability and the integrity of the single market.”

It noted that banks are increasingly linking with crypto companies by offering crypto services to customers or by servicing crypto companies, which it argued could transmit “shocks into the financial system” from crypto.
The ECB added that the trend underscored “the need for a centralised Union supervisory regime for CASPs, capable of addressing the systemic risks posed by CASPs with significant activities, preventing risk migration into the banking system and safeguarding financial stability.”
The central bank said that ESMA would need to be given sufficient funding and staff if it were to take on the responsibility of directly policing crypto companies.
The plan is likely still months away from becoming law, as EU lawmakers and governments will negotiate the proposal before the European Parliament takes further action.
Magazine: South Korea gets rich from crypto… North Korea gets weapons
-

 Politics2 days ago
Politics2 days agoUS brings back mandatory military draft registration
-

 Fashion2 days ago
Fashion2 days agoWeekend Open Thread: Veronica Beard
-

 Sports3 days ago
Sports3 days agoMan United discover Nico Schlotterbeck transfer fee as defender reaches Dortmund agreement
-

 Tech5 days ago
Tech5 days agoHow Long Can You Drive With Expired Registration? What Florida Law Says
-

 Politics15 hours ago
Politics15 hours agoWorld Cup exit makes Italy enter crisis mode
-

 Crypto World4 days ago
Crypto World4 days agoCanary Capital Files SEC Registration for PEPE ETF
-

 Fashion7 days ago
Fashion7 days agoMassimo Dutti Offers Inspiration for Your Summer Mood Board
-

 Business2 days ago
Business2 days agoTesla Model Y Tops China Auto Sales in March 2026 With 39,827 Registrations, Beating Cheaper EVs and Gas Cars
-

 Fashion6 days ago
Fashion6 days agoLet’s Discuss: DEI in 2026
-

 Crypto World5 days ago
Crypto World5 days agoBitcoin recovers as US and Iran Agree a Ceasefire Deal
-
 Politics3 days ago
Politics3 days agoMalcolm In The Middle OG Turned Down ‘Buckets Of Money’ To Appear In Reboot
-

 NewsBeat7 hours ago
NewsBeat7 hours agoPep Guardiola and Gary Neville agree over Arsenal title problem that benefits Man City
-

 Business3 days ago
Business3 days agoOpenAI Halts Stargate UK Data Centre Project Over Energy Costs and Copyright Row
-

 Business2 days ago
Business2 days agoIreland Fuel Protests Enter Day 5 as Blockades Spark Shortages and Government Prepares Support Package
-

 Tech7 days ago
Tech7 days agoItalian court says Netflix must refund customers up to $576 over price hikes
-

 Tech7 days ago
Tech7 days agoHaier is betting big that your next TV purchase will be one of these
-

 Tech7 days ago
Tech7 days agoGamer Restores the Original PlayStation Portal From Two Decades Ago
-
 Tech7 days ago
Tech7 days agoThe Xiaomi 17 Ultra has some impressive add-ons that make snapping photos really fun
-
 Tech7 days ago
Tech7 days agoSamsung just gave up on its own Messages app
-

 Tech7 days ago
Tech7 days agoSave $130 on the Samsung Galaxy Watch 8 Classic: rotating bezel, sleep coaching, and running coach for $369











You must be logged in to post a comment Login