Crypto World
NK-Linked Crypto Heists $578M in April After Kelp DAO Exploit

Kelp DAO’s $292 million breach on a Saturday emerged as the year’s largest crypto exploit, drawing attention to cross-chain security gaps and intensifying scrutiny of DPRK-linked cyber operations. Investigators point to LayerZero’s infrastructure as a factor, while researchers and industry players weigh the implications for DeFi security and governance models.
Kelp DAO has stated that the attack stemmed from weaknesses in LayerZero’s cross-chain messaging setup, specifically the use of a single verifier configuration to approve messages across chains. LayerZero, for its part, said preliminary indicators point to TraderTraitor, a subgroup of North Korea’s Lazarus Group, as the actor behind the breach. Independent researchers have traced stolen funds to Lazarus-linked activity, underscoring the persistent risk posed by the DPRK’s cyber operations to decentralized finance and users alike.
Key takeaways
- The Kelp DAO exploit is attributed to LayerZero’s cross-chain messaging framework and a single-verifier configuration, with initial attribution leaning toward TraderTraitor, a Lazarus Group subgroup.
- Arbitrum’s Security Council froze 30,766 ETH tied to the incident, illustrating a governance-driven move to curb losses even as it tests the bounds of decentralization and protocol sovereignty.
- North Korea-linked actors have escalated their DeFi-focused campaigns, with April’s Drift hack adding to a broader pattern that researchers say now totals hundreds of millions of dollars in attributed theft this spring.
- Retail crypto crime remains on the rise, according to the FBI’s IC3 2025 report, with losses and complaints spanning investment scams, fake job schemes, and social-engineering attacks tied to older and newer targets alike.
LayerZero, Kelp DAO and the cross-chain security debate
The Kelp DAO incident centers on how cross-chain messaging ecosystems—designed to move liquidity and data across networks—can become vectors for theft when misconfigurations align with attacker capabilities. Kelp DAO acknowledged that the breach exploited its reliance on LayerZero’s messaging framework, arguing that a single-verifier configuration enabled unauthorized cross-chain messages. LayerZero’s response framed the event as linked to the attacker cluster associated with Lazarus-linked figures, with initial signals pointing toward TraderTraitor, a subgroup identified by security researchers and industry observers.
The event surfaces a broader question: as DeFi protocols lean on sophisticated cross-chain infrastructures to unlock liquidity, how should governance and security balance between open, decentralized designs and the need for rapid, centralized interventions to prevent further harm? The Kelp episode also echoes earlier incidents where attackers leveraged infrastructure-level weaknesses rather than novel smart-contract bugs, highlighting how adversaries may increasingly target the supporting systems that enable cross-chain composability.
Independent researchers have noted that stolen funds from the Kelp breach appear to have mixed with earlier Lazarus-linked exploits, suggesting a pattern where DPRK-linked actors recycle and launder proceeds across wallets and chains. Such findings align with broader concerns that attacker ecosystems are becoming more coordinated and persistent, spanning multiple campaigns rather than isolated incidents.
North Korea’s evolving toolkit and the risk to the broader crypto ecosystem
The Kelp incident follows a string of high-profile DPRK-linked exploits in 2025 that have redirected attention to the group’s cyber espionage and fraud tactics. In April, the Drift protocol hack—an apparent North Korea-linked operation—accounted for roughly $285 million in losses, pushing the month’s attributed total to about $578 million across major incidents. Taken together with other incidents, analysts say these acts represent the most significant wave of DPRK crypto theft since the Bybit breach earlier in the year.
Security researchers and policy monitors have long warned that DPRK-backed actors blend traditional cyber-espionage playbooks with financially motivated operations. A recurring pattern involves recruiters and “IT worker” schemes designed to infiltrate legitimate tech and crypto companies, sometimes by posing as remote workers or contractors. This tactic, researchers note, funds the DPRK’s weapons-development programs, according to United Nations and other authorities cited in industry reporting.
U.S. authorities have responded with sanctions and public guidance. In March 2025, the U.S. Treasury sanctioned individuals and entities tied to North Korean IT worker fraud networks, while the FBI’s IC3 program issued guidance in mid-2025 urging employers to verify applicants’ professional histories and favor in-person verification where possible. Despite such measures, the Drift and Kelp breaches show that North Korean operatives are adapting—sometimes leveraging face-to-face interactions to build trust before initiating sophisticated cross-chain intrusions.
Beyond the headline hacks, smaller-scale incidents illustrate a broader leakage path into the retail space. For instance, Zerion reported DPRK-linked actors employing AI-assisted social engineering to steal modest sums, underscoring how crowding effects from larger hacks filter down to everyday users. The industry’s recurrent challenge remains immediate risk mitigation for users while authorities and firms continue to chase accountability for the perpetrators.
Governance, intervention and the ethics of freezing assets
One of the most consequential aspects of the Kelp episode was the Arbitrum Security Council’s decision to freeze 30,766 ETH implicated in the breach. The move—unprecedented in its explicit override of a blockchain state—has sparked a debate within the ecosystem about when, if ever, governance should intervene to preserve funds or protect users. Ledger’s chief technology officer Charles Guillemet described the outcome as “probably good, but not a comfortable one,” emphasizing that freezing the funds likely prevented further losses even as it exposed a difficult truth: decentralization does not always shield networks from governance actions in a crisis.
The Arbitrum decision, while preserving resources for affected users, illustrates the tension inherent in today’s rollup-based architectures. The governance mechanism exists by design to allow a trusted body to act when necessary, but it also challenges the ideal of credibly neutral infrastructure. In the Kelp case, the root cause was not a post-launch vulnerability in a single contract but a misconfiguration in cross-chain messaging that points to a broader risk: as ecosystems become more interconnected, the line between protocol weakness and systemic risk grows thinner.
Industry observers highlight that the Kelp incident reinforces a clear takeaway: attackers are increasingly probing the spaces between blockchains—bridges, relays, and validators—as much as they probe the individual protocols themselves. For builders, the imperative is not only to patch existing smart contracts but to harden the inter-chain fabric against cross-chain messaging failures, misconfigurations and governance overreach. For investors and users, the message is twofold: proceed with heightened caution around cross-chain liquidity, and demand transparent, timely disclosures when security incidents occur.
As these dynamics unfold, the broader market faces a persistent question: how to balance rapid recovery with principled governance? The Kelp and Drift cases provide a sobering test of whether the industry can coherently align incentives around safety, accountability, and the preservation of value when real-time decisions can alter the fate of funds that are already in motion.
Looking ahead, analysts expect continued attribution efforts and more formal investigations that could clarify whether TraderTraitor and other Lazarus-linked actors are systematically behind a wave of DeFi intrusions. Regulators may also intensify their focus on cross-chain security standards, while projects experiment with enhanced verification, multi-sig controls, and post-incident recovery playbooks to limit losses without compromising the decentralized ethos.
What to watch next: researchers will likely publish deeper analyses on LayerZero usage patterns and verifier configurations, while Arbitrum and LayerZero may roll out mitigations to reduce the likelihood of similar breaches. Stakeholders should monitor updates on governance policies, potential sanctions, and new best practices aimed at guarding users against both technical and social-engineering threats in a rapidly evolving threat landscape.
In the meantime, the fusion of infrastructure risk, state-sponsored threat activity, and governance mechanics offers a stark reminder: as DeFi grows more interconnected, securing the backbone—cross-chain messaging and related governance—will determine how quickly the sector can rebound from each major incident.
Crypto World
Nvidia CEO’s Foundation Donates $108M in CoreWeave Computing to Researchers

TLDR:
- Nvidia CEO’s foundation purchased $108.3M in CoreWeave computing time for university and nonprofit AI research.
- Nvidia offered free engineering services to select institutions receiving the CoreWeave computing grant donations.
- Nvidia invested $2 billion in CoreWeave in January, making it the company’s second-largest shareholder at the time.
- Nvidia’s $6.3B CoreWeave deal guarantees chip purchases of unsold cloud capacity, raising circular financing concerns.
The foundation of Nvidia CEO Jensen Huang and his wife, Lori, has purchased $108.3 million worth of computing time from CoreWeave.
The resources will be donated to universities and nonprofit institutions for science and artificial intelligence research.
Nvidia has also offered free engineering services to some grant recipients. The move adds to a growing list of financial ties between Nvidia and CoreWeave.
Huang Foundation Directs Computing Resources to Academic Institutions
A filing released Tuesday confirmed the donation, detailing how the computing time will support AI and science research.
According to the filing, the computing resources will be used for “science and artificial intelligence research.” The grant recipients include universities and other nonprofit organizations working on advanced research programs.
Nvidia stated in the filing that it plans to provide free engineering services to select institutions receiving the grant. The donation reflects Jensen Huang’s continued personal investment in expanding AI research infrastructure.
Beyond charitable giving, however, the move also channels more activity toward CoreWeave, a cloud provider specializing in AI workloads.
CoreWeave relies heavily on Nvidia’s graphics processing units, or GPUs, to serve its customers. The foundation’s purchase of CoreWeave computing time comes as Nvidia deepens its financial relationship with the company.
Reuters reported that in January, Nvidia invested $2 billion in CoreWeave, becoming the company’s second-largest shareholder at the time.
Nvidia’s Broader Financial Relationship With CoreWeave Draws Scrutiny
Nvidia signed a $6.3 billion cloud computing capacity deal with CoreWeave last year. Reuters noted the agreement guarantees that Nvidia “will purchase any cloud capacity not sold to customers.” That arrangement effectively made Nvidia a guaranteed buyer of CoreWeave’s unused computing resources.
CoreWeave raised the lower end of its capital spending forecast last week when it reported results. The company cited higher prices of components as the reason behind the updated forecast. That update came as investors continued to watch the financial ties between the two companies closely.
As Reuters reported, “The chip giant has drawn scrutiny for investing billions of dollars into AI firms including ChatGPT maker OpenAI and neoclouds.”
Investors have raised concerns about potential circular financing, where Nvidia’s capital flows back through companies that purchase its chips. Those concerns continue to grow alongside Nvidia’s expanding investment portfolio in the AI sector.
Crypto World
Bessent says U.S. leads, safety protocol planned

U.S. Treasury Secretary Scott Bessent waits for the first meeting of U.S. President Donald Trump’s anti-fraud task force convened by U.S. Vice President J.D. Vance at the Eisenhower Executive Office Building on the White House campus in Washington, D.C., U.S., March 27, 2026.
Jonathan Ernst | Reuters
The U.S. can talk to China about AI because “we are in the lead,” U.S. Treasury Secretary Scott Bessent told CNBC, as the countries unveiled a protocol on best practices for the rapidly improving technology.
“The two AI superpowers are gonna start talking. We’re gonna set up a protocol in terms of how do we go forward with best practices for AI to make sure non-state actors don’t get a hold of these models,” Bessent told Joe Kernen on Thursday, on the sidelines of President Donald Trump‘s two-day meeting in Beijing with Chinese President Xi Jinping.
“The reason we are able to have wholesome discussions with the Chinese on AI is because we are in the lead,” he added. “I do not think we would be having the same discussions if they were this far ahead of us,” he said.
U.S.-based Anthropic has alarmed many in Washington and other countries with the Mythos AI model, which is supposed to have powerful cyberattack capabilities. The company said it would initially release it to select business partners.
BEIJING, CHINA – MAY 14: China’s President Xi Jinping (R) and US President Donald Trump pose for a photo at the Temple of Heaven in Beijing on May 14, 2026. Xi warned Trump that the issue of Taiwan could push their two countries into “conflict” if mishandled, a stark opening salvo as a superpower summit set to tackle numerous thorny issues began in Beijing on May 14. (Photo by Brendan Smialowski – Pool/Getty Images)
China Pool | Getty Images News | Getty Images
Bessent told CNBC he anticipates a big “step-function jump” in upcoming large language model releases from Google‘s Gemini and OpenAI.
Washington has also sought to limit China’s AI development by restricting sales of advanced semiconductors, primarily from Nvidia, to the country. The chipmaker’s CEO, Jensen Huang, joined Trump’s delegation to China as a late addition.
When asked about a Reuters report that Washington had cleared sales of Nvidia’s H200 AI chips to several major Chinese technology firms, Bessent said there had been “a lot of back and forth” on the matter.
Trump and Xi wrapped up their first major meeting of this week’s China trip at 12 p.m. local time Thursday. Beijing’s readout said the Chinese leader emphasized that Taiwan is the most important issue for bilateral relations, and warned against mishandling the issue.
Beijing claims that Taiwan, a democratically self-ruled island, is part of its territory.
Bessent also told CNBC that Trump would say more on the issue of Taiwan “in the coming days.”
“Trump … understands the sensitivities around all this, and anyone who’s been saying other otherwise does not understand the negotiating style of Donald Trump,” he added.
Bessent’s week in Asia
Trump’s trip to China this week is the first time a sitting U.S. president has visited the country since 2017, when Trump visited during his first term. The summit kicked off Thursday morning and is due to wrap up Friday.
Ahead of the Trump-Xi meeting, Bessent met with Chinese Vice Premier He Lifeng in South Korea on Wednesday.
China’s Commerce Ministry described the preliminary talks as an effort to resolve trade issues and “further expand pragmatic cooperation,” according to a CNBC translation of the Chinese.
In a brief post on X Thursday morning, Bessent shares a picture of himself with He Lifeng, saying they had discussed “the economic and trade relationship between our nations.”
Crypto World
BitGo Posts $3.8B Revenue, $60.7M Loss amid Bitcoin Decline and IPO Costs in Q1
Digital asset infrastructure company BitGo reported a wider first-quarter net loss as Bitcoin treasury mark-to-market losses and IPO-related expenses outweighed stronger client growth and a year-over-year jump in revenue.
Revenue for the quarter ended March 31 was $3.8 billion, up from $1.8 billion a year earlier, driven by higher digital asset trading activity and growing contributions from its stablecoin business, the company announced Wednesday. Revenue fell 38.7% from Q4 2025’s $6.2 billion, partly due to a shift in client trading from spot to derivatives, a product BitGo launched at the start of the quarter that generated roughly $3 billion in notional volume.
However, net loss widened to $60.7 million from $25.7 million in Q1 2025, hit by a $53.7 million non-cash loss tied to the declining value of the company’s Bitcoin treasury, as well as stock-based compensation from its recent IPO. BitGo said stock compensation costs are expected to normalize going forward.
Adjusted EBITDA (earnings before interest, taxes, depreciation and amortization) swung to a loss of $1.7 million from a gain of $3.9 million a year ago, partly due to a $3 million in one-time legal and professional costs tied to the IPO.
Related: Circle to launch cirBTC wrapped Bitcoin, challenging BitGo and Coinbase
BitGo client base surges 42%
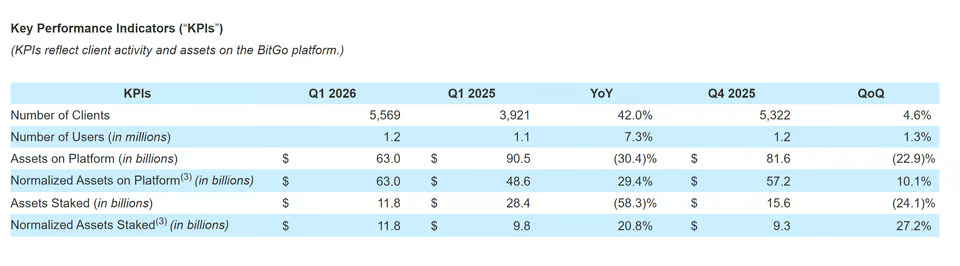
On the platform side, client count grew 42% year-over-year to 5,569. These are institutions like hedge funds, exchanges, fintech companies and other businesses that plug into BitGo’s infrastructure. Users on the platform also grew to 1.2 million, up 7.3% year-over-year.

BitGo KPIs. Source: BusinessWire
Stablecoin-as-a-service revenue jumped 43.6% to $38.2 million, while staking revenue dropped 66.2% to $49.4 million amid lower token prices.
BitGo ended the quarter with $186.6 million in cash and held 2,449 Bitcoin valued at approximately $167.1 million.
BTGO shares slipped 1.09% in overnight trading to $11.78 after the earnings release, according to Yahoo! Finance.
Related: BitGo launches portfolio-based crypto lending platform for institutions
Crypto companies post widening losses in Q1
A string of crypto companies reported deepening losses in the first quarter of 2026 amid the market decline. Coinbase swung to a $394.1 million net loss, missing revenue estimates of $1.5 billion with $1.41 billion. Exodus Movement more than doubled its losses to $32.1 million as revenue dropped 36.8% and active users slid.
Bitcoin miners, including Riot Platforms, Core Scientific, CleanSpark and TeraWulf, all posted widening losses in Q1 2026, with MARA topping the group at a $1.3 billion net loss, roughly $1 billion of which stemmed from non-cash mark-to-market adjustments on Bitcoin holdings.
Magazine: Guide to the top and emerging global crypto hubs — Mid-2026
Crypto World
Moody’s puts AAA rating stamp on Fidelity and BlackRock’s tokenized money market funds

Moody’s assigned its highest credit rating to tokenized money market funds from Fidelity and BlackRock, validating their safety as yield-bearing onchain products.
The AAA-mf rating signals an extremely strong ability to ensure high liquidity and capital preservation and the lowest level of risk.
Fidelity’s FILQ fund debuted on May 6. The product is powered by Swiss digital asset bank Sygnum’s Desygnate tokenization platform, which enables onchain fund registries, smart contract-based settlement and stablecoin subscriptions and redemptions.
It also includes infrastructure support from JPMorgan Chase for custody and fund administration, Apex Group for transfer agency services and Chainlink, which publishes the fund’s net asset value and distribution data onchain.
“There is no tokenized finance without tokenized liquidity. Once markets settle in real time, cash must settle in real time too,” Emma Pecenicic, head of digital assets distribution at Fidelity International, said in a statement.
BlackRock’s BUIDL, introduced in March 2024, is one of the largest tokenized Treasury funds in the world. The fund received a AAA rating yesterday, more than two years after its debut, according to a post on X by Securitize, its transfer agent and tokenization platform.
Money market funds deal in high-liquidity, short-term debt securities with maturities generally under one year, such as Treasury bills, commercial paper, and certificates of deposit. Investors use money market funds as a safe place to park cash while still earning some interest.
Tokenized U.S. government debt products, including Treasury bills, notes, bonds and money market funds, have rapidly gained traction among both traditional financial institutions and crypto-native firms.
The onchain tokenized Treasury sector now has total assets under management of over $15 billion, up from $1 billion in just two years, according to data source rwa.xyz. The growth is driven by demand for onchain versions of low-risk, yield-bearing instruments.
Crypto World
30-Year Treasury Auction Clears Above 5%, Highest Yield Since 2007
The US Treasury sold $25 billion worth of 30-year bonds on Wednesday, with the auction clearing at a yield of 5.046%.
The sale follows back-to-back US inflation reports this week that pointed to mounting price pressures driven by the US-Iran war.
Iran War Inflation Shock Drives Long-End Yields Higher
According to the Financial Times, the auction marked the first time since 2007 that the US government issued 30-year debt with a yield at 5%.
Meanwhile, secondary-market yields also climbed yesterday after the US Producer Price Index (PPI) Final Demand rose to 6%, the highest reading since January 2023.
The 30-year hit an intraday high of 5.05%, the highest since July 17, while the 10-year benchmark reached 4.49%. The 2-year yield, more sensitive to Fed policy, eased to 3.981%.
Follow us on X to get the latest news as it happens
Bond Stress Spills Into Bitcoin and Risk Assets
Rising Treasury yields tighten financial conditions by increasing borrowing costs and boosting the appeal of safer fixed-income investments.
A 30-year US Treasury yield above 5% also raises the opportunity cost of holding non-yielding assets such as Bitcoin and gold, potentially weighing on demand for risk assets.
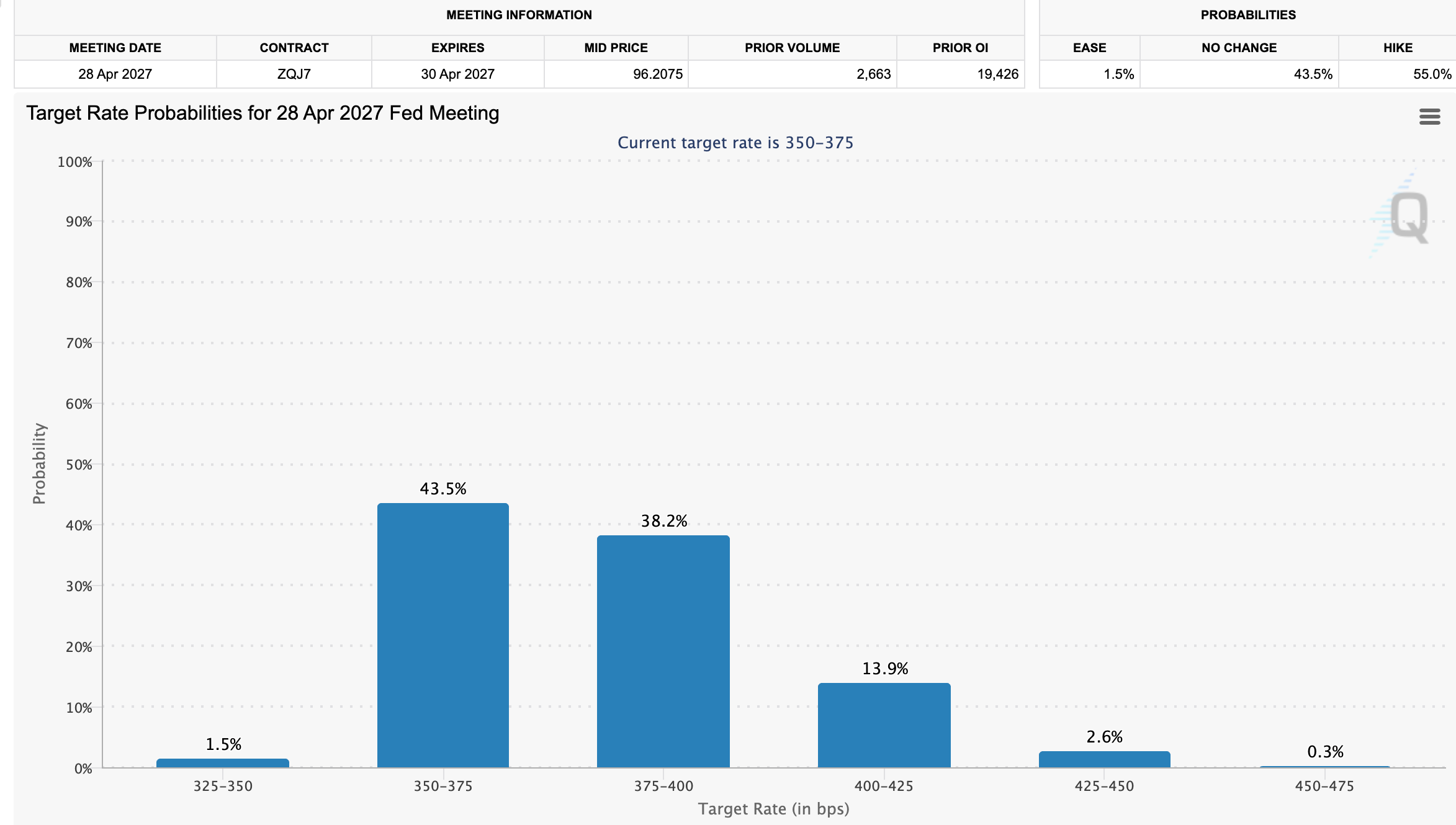
Meanwhile, markets are now pricing in a 55% probability of a Federal Reserve rate hike by April 2027. This reflects growing investor concern that inflation could remain elevated for longer, forcing policymakers to tighten further rather than ease rates as previously expected.
Higher interest rates further reduce appetite for risk assets by increasing financing costs and tightening liquidity.
Subscribe to our YouTube channel to watch leaders and journalists provide expert insights
The post 30-Year Treasury Auction Clears Above 5%, Highest Yield Since 2007 appeared first on BeInCrypto.
Crypto World
The CLARITY Act Vote Is Today, And XRP Just Broke a Level That Rejected It 4 Times This Month

XRP is pressing against a critical resistance zone with the Senate Banking Committee’s CLARITY Act markup scheduled for today, and traders are watching every tick.
The token was last trading at $1.47, up 2.5% in the last 24 hours after briefly dipping to $1.43, with the breakout level at a confirmed daily close above $1.50 drawing intense focus.
What happens in the next few hours could define XRP’s trajectory for the rest of the quarter.
The Senate Banking Committee, chaired by Tim Scott, scheduled the CLARITY Act markup for May 14 at 10:30 AM EST, a bill that would codify XRP’s commodity status into federal law following the SEC-CFTC joint ruling of March 17, 2025.
Over 120 crypto firms urged Senate passage in April, and community sentiment is running hot, with analyst noting: “The CLARITY Act markup becomes the setup.”
Polymarket passage odds currently sit between 62% and 72%. Spot XRP ETFs have absorbed $34.2M in inflows this week alone, pushing total AUM toward $1.5B since their November 2025 launches, the strongest single-day intake since January 5.
The confluence of on-chain accumulation data, institutional product flows, and a live legislative catalyst puts XRP at one of its most technically loaded junctures in months.
Can XRP Price Hit $1.80 This Week?
XRP recently broke $1.47 on the heaviest volume in weeks. That level had rejected the token 4 times this month.
This is not noise. On-chain data backs the move. Wallets holding 10,000 or more XRP have reached a record 332,230, signaling steady accumulation even as broader whale counts show some rotation. The bid has conviction behind it.
Immediate resistance lies between $1.50 and $1.60. The 200-day moving average at $1.80 is the next meaningful magnet above that. Key support sits at $1.28 with the $1.20 floor below it.

A clean CLARITY Act markup pushes XRP above $1.50 on strong volume, targeting $1.60, then the $1.80 to $1.85 range.
Standard Chartered is projecting $8 on full passage with $10 billion in ETF inflows materializing by year-end.
A disappointing or delayed markup fails to hold $1.40 and reopens a slide toward $1.30, potentially $1.20. A broad risk-off wave accelerates that move fast.
The setup is clean. The clock is ticking. If today’s session closes without a confirmed break above $1.50, momentum stalls, and the range trade resumes.
Maxi Doge Could Have 1000x Potential and Smart Money are Buying
XRP’s potential move to $1.80 is compelling, but at a $7B+ market cap, even a 25% gain requires significant institutional capital deployment.
Early-stage traders hunting asymmetric setups are increasingly eyeing presale opportunities where the entry price does the heavy lifting before any catalyst fires.
Maxi Doge (MAXI) is one project capturing that rotation. Built on Ethereum as an ERC-20 meme token with a distinct identity, a 240-lb canine juggernaut built around 1000x leverage trading culture, it pairs viral gym-bro humor with structured community mechanics (holder-only trading competitions, leaderboard rewards, and a Maxi Fund treasury for liquidity and partnerships).
The presale has raised $4,777,373.15 at a current price of $0.0002818, with dynamic staking APY available to participants.
Trader attention has been building steadily as the XRP regulatory narrative draws broader crypto interest. As with any presale, liquidity risk and execution uncertainty are real – position sizing matters. Those running their own numbers can
The post The CLARITY Act Vote Is Today, And XRP Just Broke a Level That Rejected It 4 Times This Month appeared first on Cryptonews.
Crypto World
Akamai (AKAM) Stock Surges to Highest Level Since 2000 Following Bank of America Upgrade
Key Highlights
- Bank of America elevated AKAM to Buy status, increasing the price target from $130 to $175
- Shares climbed 7.7% to reach $161.14, the highest level since March 2000
- An $1.8 billion seven-year contract — believed to be with Anthropic — is fueling optimism around AI infrastructure
- Shares have surged 57% in May alone and are up 86% year-to-date
- Cloud Infrastructure Services segment expanded 40% year-over-year, balancing a 7% drop in delivery operations
Akamai Technologies (AKAM) finished Wednesday’s trading session at $161.14, posting a 7.7% gain and reaching its strongest close since March 29, 2000.
Akamai Technologies, Inc., AKAM
The driving force: Bank of America analyst Tal Liani upgraded the stock to Buy and lifted his price objective from $130 to $175 — suggesting approximately 8% additional upside potential from Wednesday’s closing price.
This rating change follows Akamai’s announcement last week of an $1.8 billion, seven-year agreement with what the company described as a “leading frontier model provider” for its cloud infrastructure offerings. Bloomberg subsequently identified the customer as AI startup Anthropic, though neither party has officially confirmed this to Barron’s.
Liani noted in his report that “the story has shifted from a legacy delivery network to a credible AI infrastructure platform.” He views the contract as concrete proof of genuine demand for distributed AI capabilities, rather than mere speculation.
The analyst projects the agreement will generate $20–25 million in quarterly revenue beginning in the fourth quarter.
AKAM ranked among the S&P 500’s strongest performers Wednesday. The stock has now rallied 57% during May and 86% since the start of the year. Despite this impressive run, shares remain 51% below their all-time closing peak of $327.62 recorded on December 31, 1999.
AI-Driven Cloud Growth Underpins Positive Outlook
Bank of America highlighted the 40% year-over-year expansion in Akamai’s Cloud Infrastructure Services division as a primary rationale for the upgrade. This robust growth is being propelled by AI workloads and what Liani described as “edge inference use cases.”
The security services division also posted solid 11% year-over-year growth. Meanwhile, delivery services, representing the company’s traditional business, declined 7% — though analysts seem prepared to overlook this weakness for the time being.
Liani characterized the CIS segment as being “at an inflection point,” with momentum sufficient to drive accelerating annual profit expansion.
Morgan Stanley Maintains Optimistic Stance
Morgan Stanley analysts, who maintain an Overweight rating on AKAM, observed on Friday that the $1.8 billion contract eclipsed what was already a strong first-quarter earnings performance. Akamai exceeded Q1 expectations and increased the lower bound of its full-year earnings forecast.
This represents Akamai’s largest contract ever. Morgan Stanley analysts indicated it demonstrates the company is now “firmly entrenched in the AI narrative” — a perspective that has clearly resonated with the investment community.
Among 29 analysts tracked by FactSet, Akamai holds an average Overweight rating with a consensus price objective of $155.46.
GF Score metrics place Akamai at 88/100, with both profitability and growth scoring 9/10. Financial strength registers at 5/10, and the current P/E ratio of 53.83x substantially exceeds the historical median of 30.96x.
A cautionary note: company insiders have divested roughly $9.7 million worth of AKAM shares over the last three months, with zero insider purchases recorded. Bank of America acknowledged that risks persist, including uncertainties about the sustainability of CIS growth and Akamai’s long-term competitive positioning against hyperscale cloud providers.
As of Wednesday’s market close, AKAM’s market capitalization stood at approximately $23.24 billion.
Crypto World
Cardano Whales Keep Buying as ADA Crashes 71% in 9 Months
At $0.26, Cardano (ADA) continues to trade significantly below its previous market highs, but large holders of the 11th-largest crypto asset by market cap appear unfazed.
In fact, new data suggests that millionaire-tier Cardano wallets consistently expanded ADA holdings.
Aggressive ADA Buying Spree
According to crypto analytics platform Santiment, wallets holding at least 1 million ADA have steadily increased their share of the supply. These wallets now collectively hold 25.09 billion ADA, which represents 67.47% of the current circulating supply. The accumulation trend has continued even as Cardano’s market cap dropped more than 70% over the past nine months. Santiment said the “millionaire” tier of sharks and whales appears to be taking advantage of lower prices.
Amid continued accumulation by major Cardano holders, crypto analyst Ali Martinez recently pointed to the $0.25 level as a historically important price zone for ADA. According to Martinez, Cardano saw a strong recovery after holding that level in January 2023, as the asset rose more than 88% in the following weeks.
A similar trend unfolded in September 2023 as well, when ADA once again maintained support around $0.25 before later recording a 243% rally. With Cardano currently trading above $0.26, the same support range remains critical for the asset’s price structure.
Based on his analysis, continued strength above the $0.25 zone could support a move toward $0.36, while a broader rally could push ADA toward $0.53. However, he warned that losing the support range could lead to a deeper correction.
Scaling Debate Intensifies
Beyond price, Cardano continues to face criticism over the pace of its development and scaling progress. Responding to those concerns, Cardano founder Charles Hoskinson recently pushed back against claims that the network had “abandoned scaling in favor of governance.”
Hoskinson said Cardano’s scaling research has been ongoing since before the Shelley era and involved years of work across Layer 2 solutions, the extended UTXO accounting model, zero-knowledge technologies, partnerchains, and the Leios protocol. He explained that many of these initiatives required extensive research, scientific publications, and long-term engineering efforts that could not simply be accelerated by adding more developers.
Hoskinson also maintained that the implementation of the Voltaire governance system did not divert resources away from scaling research.
The post Cardano Whales Keep Buying as ADA Crashes 71% in 9 Months appeared first on CryptoPotato.
Crypto World
Trump Weighs 250 Pardons as Crypto Founders Push for Clemency
US President Donald Trump is reportedly considering pardoning 250 people to commemorate the country’s 250th birthday on July 4, according to The Wall Street Journal.
An official announcement could come on June 14, Trump’s birthday, or during the Independence Day event on July 4, the WSJ reported Thursday, citing people familiar with the matter.
However, the pardons are still in the preliminary stages and have yet to be confirmed. More than 16,000 formal requests for presidential pardons were submitted last year.
On his first day back in office last year, Trump issued more than 1,500 pardons to people involved with the storming of the US Capitol in 2021. Several jailed crypto founders and their supporters have been advocating for pardons from Trump since his inauguration.
Cointelegraph has contacted the White House for comment.
FTX, Samourai Wallet founders want pardons
FTX founder Sam Bankman-Fried was convicted on all seven counts connected to the collapse of the cryptocurrency exchange and was sentenced to 25 years in prison in 2024. He has waged a social media campaign in the hopes of getting a pardon, but Trump reportedly ruled it out earlier this year.
Keonne Rodriguez, one of the developers behind the crypto-mixing protocol Samourai Wallet, has also publicly expressed hopes for a pardon.
Trump said last December he would review Rodriguez’s case and explore a pardon. There is also a petition that has attracted 16,082 signatures as of Thursday.

Source: Keonne Rodriguez
Meanwhile, at least two petitions calling for a pardon for the Tornado Cash founders, Roman Storm and Roman Semenov, are currently live; however, they have only 22 and 9 signatures, respectively. Storm has not publicly asked for a pardon.
Storm was convicted last August on charges of conspiring to operate an unlicensed money transmitting business and is still facing charges of money laundering and sanctions violation conspiracy. Semenov is considered on the run and is wanted by the FBI.
The case against Rodriguez and Storm has been closely followed by crypto advocates, many of whom argue they shouldn’t be held responsible for the actions of third parties using their software.
Some crypto pardons already granted
Several crypto founders have already received pardons during Trump’s second term as president.
Last year, the White House pardoned the co-founders of crypto exchange BitMEX: Arthur Hayes, Benjamin Delo and Samuel Reed, who all pleaded guilty to failing to maintain anti-money laundering and know-your-customer programs in violation of the Bank Secrecy Act.
Related: US CLARITY Act sees ‘big step forward’ as markup set for May 14
Binance founder Changpeng “CZ” Zhao was also pardoned in 2025. He already served a four-month prison sentence after pleading guilty to one count of violating the US Bank Secrecy Act for failing to maintain an effective anti-money laundering program at Binance.
Silk Road founder Ross Ulbricht was one of the first to receive a pardon from Trump in January 2025 for his life sentence in connection with his operation of the dark web marketplace.
Magazine: eToro founder timed Bitcoin top perfectly due to belief in 4 year cycles
Crypto World
Micron (MU) Stock Rebounds From $700 Support as Insider Unloads $1.57M
TLDR
- Micron saw nearly $100 billion wiped from its valuation at Tuesday’s session low before aggressive buying pressure returned.
- Shares tested the $700 support zone before reversing course, creating a bullish candlestick formation that technical traders view as a dip-buying opportunity.
- The semiconductor sector broadly recovered alongside Micron, with the PHLX Semiconductor Index advancing and peers including Nvidia, Texas Instruments, and ON Semiconductor posting gains.
- The memory chip giant is positioned to breach a $900 billion market capitalization for the first time, potentially ranking it as the 11th-largest U.S. corporation.
- Days before the dramatic price action, a Micron director offloaded more than $1.57 million worth of shares in transactions dated May 11.
Micron Technology (MU) stock flirted with technical breakdown territory on Tuesday before an aggressive wave of buying interest transformed what appeared to be a rout into a textbook example of market strength.
During the session’s nadir, Micron witnessed approximately $100 billion evaporate from its market capitalization. Shares plunged toward the $700 threshold before bargain hunters emerged with sufficient conviction to generate an extended lower shadow on the daily candlestick—a technical formation that chart watchers generally interpret as price rejection at lower levels. Current trading data shows the stock hovering near $804.
The trading day began on shaky footing. Monday’s price action had produced an “evening star” candlestick configuration after MU failed to sustain momentum above $800—a development frequently interpreted as a bearish reversal signal following sustained upward movement. Tuesday’s early weakness appeared to validate that cautionary indicator.
However, the narrative took an unexpected turn.
Samsung Labor Tensions Provide Support
Among the factors sustaining buyer enthusiasm was an escalating situation at Samsung (SSNLF). Labor tensions sparked concerns about a potential 18-day work stoppage that could compromise chip manufacturing operations, potentially constraining memory supply during a period when AI applications are already straining available inventory.
This fundamental backdrop provided market participants with justification to overlook near-term technical deterioration and maintain their positions.
Micron’s recovery didn’t occur in isolation. The PHLX Semiconductor Index advanced 2.38%, while numerous major semiconductor stocks participated in the rebound. ON Semiconductor skyrocketed 11.14%, Texas Instruments gained 3.78%, Analog Devices rose 3.04%, and Nvidia increased 2.29%. Broadcom represented the primary exception, declining 0.60%.
For MU bulls, the critical question now centers on whether the $700 zone can function as reliable support. Should it hold, Tuesday’s session may ultimately be characterized as a technical shakeout rather than the initiation of a meaningful downtrend.
Historic Valuation Threshold Approaches
The figures surrounding Micron’s market capitalization command attention at this juncture. With shares advancing 4.83% during the session, Micron is positioned to close above a $900 billion valuation for the first time in company history, according to Dow Jones Market Data.
Achieving this milestone would establish it as the 11th-largest U.S. corporation by market capitalization. For perspective, pharmaceutical powerhouse Eli Lilly currently commands approximately $944 billion—Micron continues narrowing that differential. The stock requires a close at or above $798.06 to reach the threshold.
Within the analyst community, sentiment remains predominantly constructive. MU holds a Strong Buy consensus rating derived from 27 Buy recommendations, 3 Hold ratings, and zero Sell ratings issued over the preceding three months. The consensus price target stands at $608.33, which paradoxically suggests potential downside from present levels—a testament to how rapidly the stock has appreciated.
On May 11, mere days preceding Tuesday’s volatile trading, director Steven J. Gomo executed sales of 2,000 MU shares across two separate transactions at weighted average prices of $786.47 and $787.60, generating total proceeds of $1,574,070. Following these dispositions, he maintains direct ownership of 17,139 shares, according to a Form 4 disclosure filed with the SEC.
-

 Crypto World6 days ago
Crypto World6 days agoHarrisX Poll Found 52% of Registered Voters Support the CLARITY Act
-

 Fashion6 days ago
Fashion6 days agoWeekend Open Thread: Marianne Dress
-

 Fashion3 days ago
Fashion3 days agoCoffee Break: Travel Steam Iron
-

 Fashion3 days ago
Fashion3 days agoWhat to Know Before Buying a Curling Wand or Curling Iron
-

 Tech4 days ago
Tech4 days agoAuto Enthusiast Carves Functional Two-Stroke Engine from Solid Metal
-

 Politics2 days ago
Politics2 days agoWhat to expect when you’re expecting a budget
-

 Business5 days ago
Business5 days agoIgnore market noise, India’s long-term story intact, say D-Street bulls Ramesh Damani and Sunil Singhania
-
 Politics5 days ago
Politics5 days agoPolitics Home Article | Starmer Enters The Danger Zone
-

 Tech3 days ago
Tech3 days agoGM Agrees To Pay $12.75 Million To Settle California Lawsuit Over Misuse Of Customers’ Driving Data
-
 Politics7 days ago
Politics7 days agoSimon Cowell Says He Was ‘Horrible’ To Susan Boyle During BGT Audition
-

 Entertainment7 days ago
Entertainment7 days agoGeneral Hospital: Ric & Ava Bombshell – Ric’s Massive Secret Exposed!
-

 Entertainment7 days ago
Entertainment7 days agoWhy David Letterman Called CBS ‘Lying Weasels’
-

 Crypto World4 days ago
Crypto World4 days agoCZ says US crypto rivals tried to block Trump pardon
-

 Sports6 days ago
Sports6 days agoBayern Munich vs PSG UEFA Champions League SF2 live match time, streaming | Football News
-

 Entertainment6 days ago
Entertainment6 days agoYNW Melly Denied Bond Again Ahead Of Double Murder Retrial
-

 Tech2 days ago
Tech2 days agoGM agrees to $12.75M California settlement over sale of drivers’ data
-

 Politics7 days ago
Politics7 days agoEuphoria Creator Praises Sydney Sweeney Amid Season 3 Scenes Backlash
-
Entertainment7 days ago
Hantavirus — cause of death for Gene Hackman's wife — at the center of Dutch cruise outbreak
-

 Crypto World5 days ago
Crypto World5 days agoPROS explodes 48% as Upbit and Bithumb listings ignite demand
-
Crypto World6 days ago
The Hantavirus Danger: Can a Potential Outbreak Spark a New Meme Coin Frenzy?












You must be logged in to post a comment Login