Crypto World
Researcher uncovers fake Ledger Nano S modified to siphon crypto assets
This article has been updated with comments from a Ledger spokesperson.
A Brazilian security researcher has uncovered a sophisticated counterfeit Ledger device operation after discovering modified hardware designed to siphon cryptocurrency from unsuspecting users.
Summary
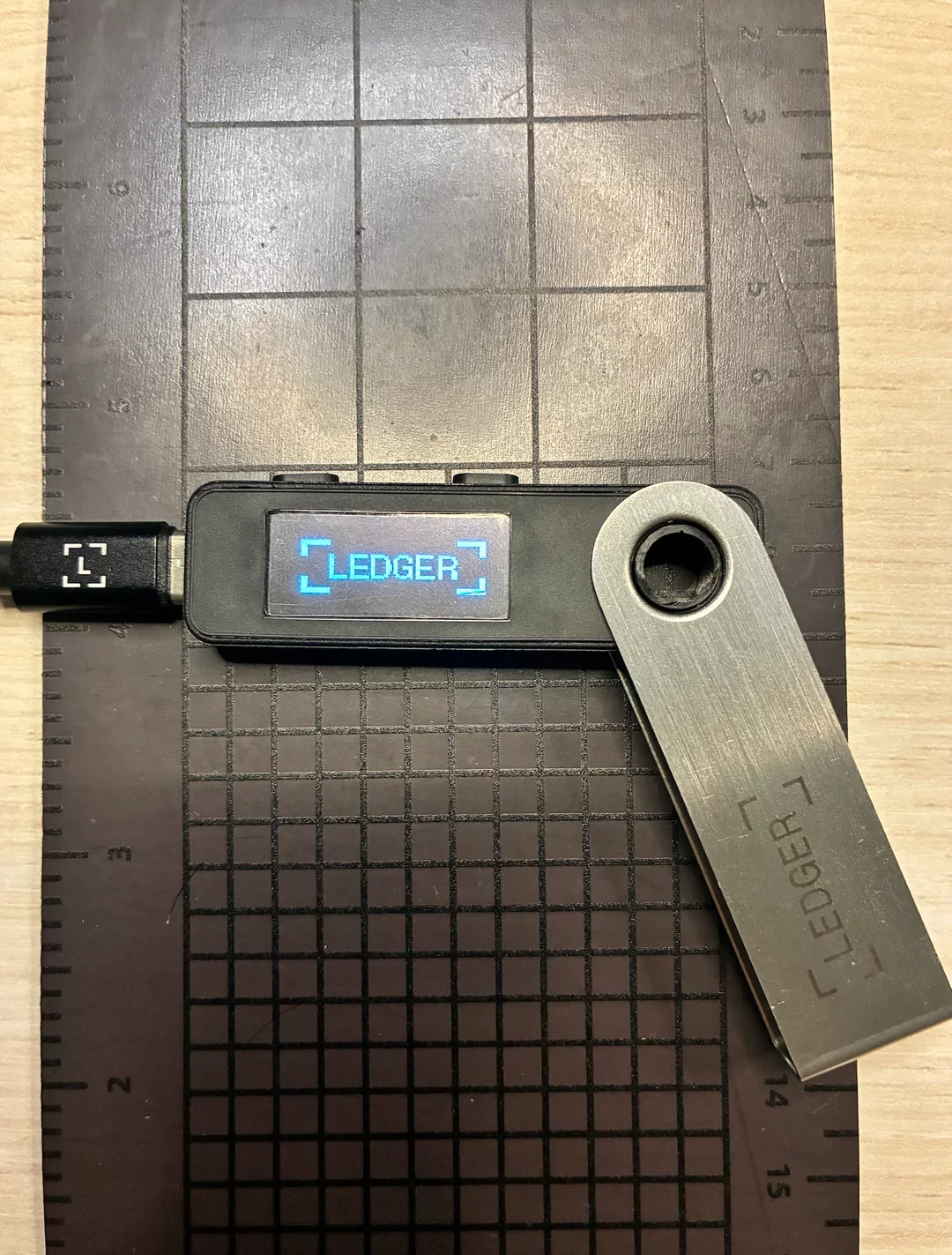
- A Brazilian security researcher identified a sophisticated hardware compromise in a counterfeit Ledger Nano S Plus that utilized modified firmware to capture user recovery phrases.
- Physical inspections of the fraudulent device revealed the addition of unauthorized WiFi and Bluetooth components alongside a secondary manufacturer’s chip hidden beneath scraped markings.
- The operation relies on a deceptive QR code included in the packaging to lure users into downloading a malicious application designed to bypass official security checks.
The security researcher, known online as “Past_Computer2901,” shared findings on Reddit after purchasing what appeared to be a standard Ledger Nano S Plus from a Chinese marketplace.
Despite the packaging and price point matching official retail standards, the unit failed a “Genuine Check” when connected to the authentic Ledger Live desktop application.
This red flag led to a physical teardown of the device, revealing that the internal circuitry had been altered to include WiFi and Bluetooth antennas—features entirely absent from the legitimate model.
Hardware manipulation and malicious redirects
Scammers are utilizing these tampered devices to exploit first-time buyers through a deceptive setup process.
A QR code included in the packaging directs users to a fraudulent version of the Ledger Live app, which is programmed to bypass security warnings and issue a fake verification of the hardware’s authenticity.
Once a user follows the prompts to generate or enter a seed phrase, the compromised firmware captures the data, allowing the attackers to drain the wallet at will.
“This isn’t meant to cause panic, but rather to serve as a serious warning — I’m honestly still a bit shaken by the sheer scale of this operation,” the researcher noted.
Internal analysis of the unit showed that the scammers went to great lengths to hide the fraud, including scraping off original chip markings.
Counterfeit Ledger device. Source: Reddit.
While the device initially identified itself as a Nano S Plus 7704 during the boot phase, the final sequence revealed the manufacturer as Espressif Systems, a Shanghai-based semiconductor firm.
These modifications fundamentally break the security premise of Ledger products, which are built to keep private keys in a strictly offline environment.
“When purchasing from a marketplace, Ledger strongly encourages users to verify the identity of the seller. Users should ensure they only download the official Ledger Wallet apps on desktop and mobile. The situation involved counterfeit hardware, paired with a fake companion app flow designed to simulate the onboarding process, distributed through unofficial channels,” a Ledger spokesperson told crypto.news.
“Ledger will never ask users for their 24 words. If anyone claiming to be Ledger, or any app that purports to be a Ledger app, asks for your 24 words, you should immediately assume it is a scam,” they added.
The discovery follows a separate incident earlier this month where a fraudulent app bypassed Apple App Store security via a bait-and-switch tactic. The malicious software successfully tricked over 50 people into revealing their recovery phrases, resulting in the theft of $9.5 million before the platform removed the listing. The app has since been removed for malicious bait-and-switch functionality, according to Apple.
“Stay safe out there. Only download Ledger Live from ledger.com. Only buy hardware from ledger.com. If your device fails the Genuine Check — stop using it immediately,” the researcher cautioned.
Crypto World
Ray Dalio questions Bitcoin safe-haven role as Saylor fires back


Bridgewater Associates founder Ray Dalio said Bitcoin has not acted as the safe-haven asset many investors expected.
Summary
- Ray Dalio said Bitcoin lacks privacy because transactions can be monitored and possibly controlled.
- Dalio argued investors often sell Bitcoin during market stress to raise liquidity elsewhere.
- Michael Saylor pushed back, calling gold analog capital and Bitcoin digital capital for collateral.
In a May 11 post, he said Bitcoin gets heavy attention but has fallen short when compared with gold during market stress.
Dalio pointed to three issues. He said Bitcoin lacks privacy, trades with a strong link to tech stocks, and remains small compared with gold. He also said gold has a deeper role in the global financial system.
Privacy remains a key concern
Dalio wrote, “First, Bitcoin lacks privacy.” He added that transactions can be monitored and potentially controlled. In his view, that makes Bitcoin less attractive to central banks as a reserve asset.
Bitcoin’s public ledger is part of its design. All confirmed transactions are recorded on a shared blockchain, allowing the network to verify ownership and spending without a central authority. That structure supports transparency, but it also creates the privacy concern Dalio raised.
Moreover, Dalio also said Bitcoin has not behaved like gold during stress periods. He said investors often sell Bitcoin when they need cash to cover pressure elsewhere in their portfolios. He added that Bitcoin’s link to tech stocks weakens its safe-haven case.
He contrasted that with gold, which he said remains widely held and deeply established. Earlier related coverage on crypto.news noted that Bitwise analysis found gold offered stronger downside protection during market drawdowns, while Bitcoin delivered stronger gains during recovery periods.
Saylor defends Bitcoin
Strategy executive chairman Michael Saylor pushed back against Dalio’s view. He said gold is “analog capital” while Bitcoin is “digital capital.” He also said Bitcoin’s transparency is a feature, not a flaw, because it supports its use as global collateral.
Saylor added that Bitcoin has outperformed gold since Strategy adopted its Bitcoin standard in August 2020. His response showed the split between investors who see Bitcoin as a risk asset and those who view it as a long-term monetary asset.
Dalio has not fully rejected crypto. Earlier crypto.news coverage noted that he has held some cryptocurrency, but prefers gold because of Bitcoin’s volatility, traceability, and uncertain reserve role.
Crypto World
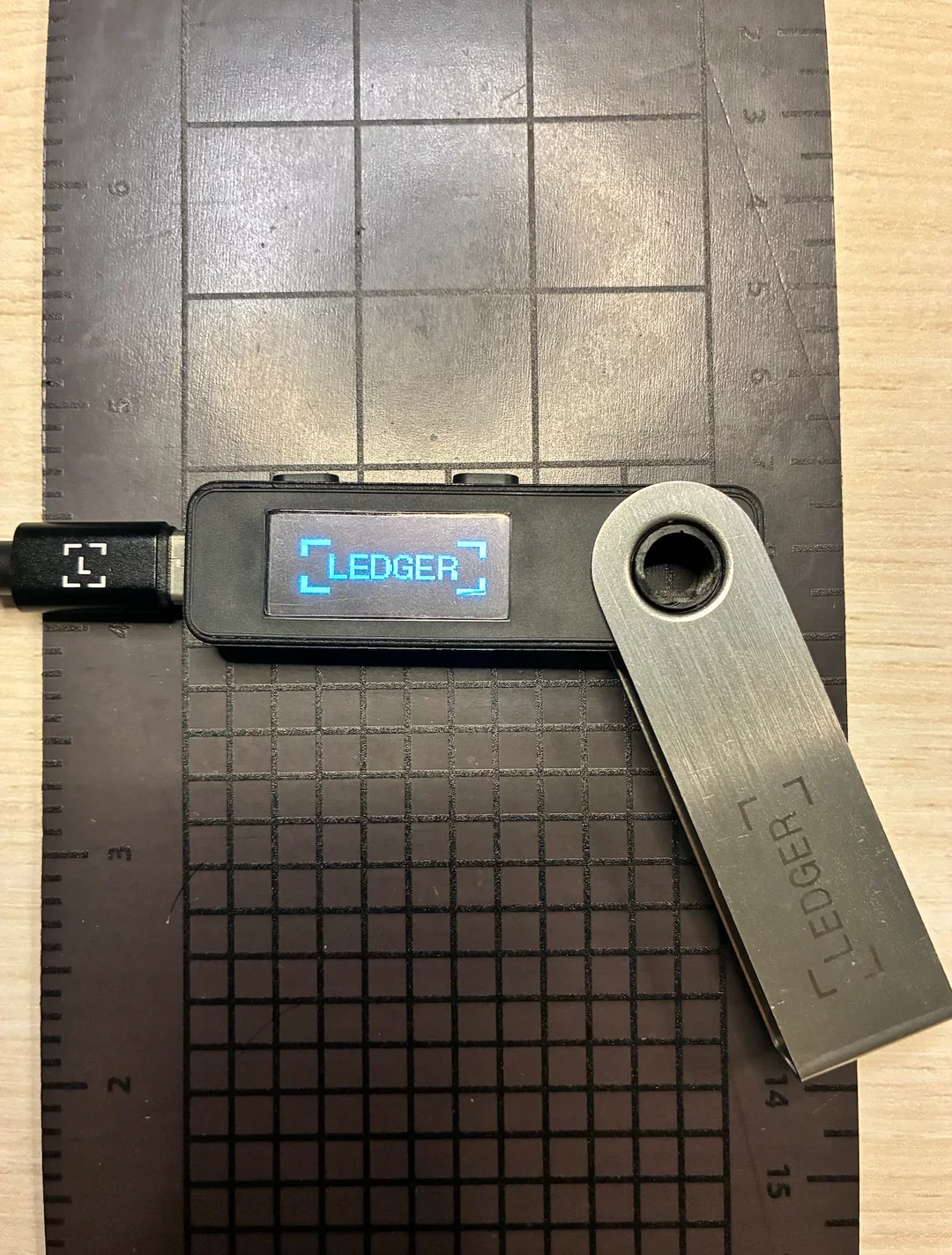
Whales Just Bet $832 Million on the Ethereum Price Dip, Here’s Why
Ethereum (ETH) price has lost 3.6% since May 10, dipping significantly inside a falling channel that has held since April 17. Whales used the dip to load up on $832 million in ETH.
Derivatives positioning shows the rally that preceded the breakdown was short-covering, not new longs piling in. That hands whales a low-leverage entry. The catch sits with long-term hodlers, who have cut accumulation by nearly 80% since late April.
Whales Bought $832 Million as the Price Slid
The Ethereum whale supply, excluding exchanges, tells a story the price chart misses. Whale wallets have steadily added ETH through the recent breakdown. The metric climbed from 124.69 million ETH to roughly 125.05 million across the period, an increase of 360,000 ETH.
Want more token insights like this? Sign up for Editor Harsh Notariya’s Daily Crypto Newsletter here.
At an current ETH price, those 360,000 tokens carry a market value of about $832 million.
The timing matters. The breakdown that started May 10 took ETH down 3.6% in two days. Whales added to their positions through that dip rather than reducing exposure. This kind of behavior usually signals confidence that the chart’s bearish pattern will not resolve to the downside. Whales rarely accumulate into a setup they expect to break lower.
The bigger question is why they are so confident. The answer sits in the derivatives data.
Ethereum Derivatives Confirm the Optimism Is Not Over-Leveraged
The derivatives side explains why whales are willing to accumulate into the breakdown. Ethereum open interest in perpetual futures dropped from $12.46 billion on May 7 to $11.98 billion on May 12. That is a decline of roughly $480 million.
Ethereum funding rate, the periodic payment between perpetual swap longs and shorts, has stayed elevated at around 0.012%. The rate was 0.010% on May 7.
The combination is telling. Falling open interest with elevated funding suggests shorts closed positions, not new longs adding leverage.
In other words, the optimism is real but conservative. There is no large stack of fresh long bets sitting on top of the market, waiting to be liquidated.
That is exactly the kind of backdrop whales prefer. The leverage stack is thin enough that an external shock will not trigger a cascading flush. But not every on-chain group agrees with the whale read.
Ethereum Hodlers Cut Accumulation by Nearly 80% Since Late April
The Ethereum hodler net position change tracks the daily change in ETH held by long-term wallets. The metric typically captures wallets that have held the token for over 155 days.
The reading peaked at 383,128 ETH on April 27. By May 11, that figure dropped to 77,675 ETH, a decline of roughly 80%.
Long-term holders have not stopped accumulating outright. They are still net buying, just at a sharply slower pace. The pace of spot buying from this cohort has thinned to roughly a fifth of the late-April rate.

The likely explanation is the same elevated funding rate that signals optimism on the derivatives side. Hodlers see funding above 0.01% as a warning that the market is leaning too long. They pull back from chasing the rally. That sets up the conflict. Whales see the falling open interest and call the optimism healthy. Hodlers see the elevated funding rate and call it overheated.
Whoever is right shapes the next leg, and the chart is the decider.
Ethereum Price Holds the Floor With $2,269 as the Trapdoor
Ethereum trades at $2,311 on the daily chart, down 1.2% on the day. The structure remains contained inside a descending channel that has held since the April 17 high.
Whale support has kept the price above $2,298, the 0.5 Fibonacci retracement of the broader pullback.
A clean daily close below $2,298 exposes $2,269, the 0.618 Fibonacci, as the next floor. That is just a 2% drop on the day.

Beneath $2,269, $2,227 and $2,174 come into the picture. A break below $2,174 exposes the lower trendline of the descending channel and risks a decisive draw lower.
On the upside, a reclaim of $2,327 puts the chart back toward neutral. A move above $2,363 shifts the structure to neutral-bullish. The target then becomes $2,422 in the short term.
Ethereum price is locked between whale buying at the floor and hodler caution above. $2,298 separates a slow recovery setup from a 2% slide that exposes $2,269 next.
The post Whales Just Bet $832 Million on the Ethereum Price Dip, Here’s Why appeared first on BeInCrypto.
Crypto World
Three Tennessee Men Indicted Over $6.5 Million Crypto Robbery Spree


A federal grand jury has indicted three Tennessee men over an alleged crypto robbery spree, including one incident where a victim was forced at gunpoint to surrender $6.5 million in digital assets.
Elijah Armstrong, Nino Chindavanh, and Jayden Rucker face conspiracy and kidnapping charges.
Tennessee Trio Hunted Crypto Holders
According to the press release, the defendants traveled from Tennessee and posed as delivery workers to enter victims’ homes. Investigators say the crew used guns, zip ties, and duct tape to restrain occupants.
“Armstrong, 21, of Tennessee; Chindavanh, 21, of Tennessee; and Rucker, 25, of Tennessee, are alleged to have conspired to kidnap and rob individuals in San Francisco, San Jose, Sunnyvale, and Los Angeles in efforts to steal cryptocurrency from the victims,” the press release read.
Follow us on X to get the latest news as it happens
Prosecutors detailed one incident where the alleged attackers forced one victim to log into his cryptocurrency accounts at gunpoint. A co-conspirator then transferred roughly $6.5 million from those wallets to addresses controlled by the group.
Armstrong and Rucker were arrested in Los Angeles on December 31. Chindavanh was detained earlier that month in Sunnyvale. All three remain in federal custody.
US Attorney Craig H. Missakian commented in the indictment announcement.
“These individuals, as alleged, terrorized their victims in the hopes of stealing vast sums of cryptocurrency. The scheme was not only sophisticated, it was brazen, violent, and dangerous,” he said.
If convicted, the defendants could face up to 20 years in prison and $250,000 in fines for charges including Conspiracy to Commit Hobbs Act Robbery, Attempted Hobbs Act Robbery, and Attempted Kidnapping. The Conspiracy to Commit Kidnapping charge carries a potential life sentence.
The development comes amid a sharp rise in physical crimes targeting cryptocurrency holders. Blockchain security firm CertiK documented 34 verified physical attacks on cryptocurrency holders between January and April 2026, a 41% rise year-over-year. CertiK projects that 2026 will close with around 130 wrench attacks if the current pace holds.
Subscribe to our YouTube channel to watch leaders and journalists provide expert insights
The post Three Tennessee Men Indicted Over $6.5 Million Crypto Robbery Spree appeared first on BeInCrypto.
Crypto World
Michael Saylor defends Strategy’s Bitcoin sales plan amid dividend concerns


Michael Saylor has defended Strategy’s ability to sell limited amounts of Bitcoin while continuing to expand its BTC treasury, arguing the company should avoid becoming a net seller rather than follow an absolute “never sell” stance.
Summary
- Strategy said limited Bitcoin sales could still support a larger BTC accumulation plan rather than reduce its treasury exposure.
- Michael Saylor described STRC and MSTR as part of a Bitcoin-backed capital structure built around digital credit and equity products.
According to comments shared by Saylor on May 10 and statements made during his recent appearance at Consensus in Miami, Strategy’s Bitcoin strategy now revolves around using its holdings to support a layered capital structure tied to preferred stock products and equity financing.
Saylor said any future Bitcoin sale would only happen within a larger accumulation cycle.
“Even if we were to sell one Bitcoin, we’d be buying 10 to 20 more Bitcoin,” he said while responding to concerns that Strategy could eventually reduce its exposure to BTC.
Recent debate around the company’s treasury model intensified after Strategy disclosed that its preferred stock products carry roughly $1.5 billion in annual dividend obligations.
Crypto.news previously reported that the company posted a $12.54 billion net loss during Q1 2026 while holding 818,334 BTC as of May 3, acquired at an average purchase price of $75,537.
Speaking with CoinDesk senior analyst James Van Straten at Consensus, Saylor described fears surrounding potential Bitcoin sales as economically insignificant.
He said Strategy could still buy roughly 20 BTC for every one Bitcoin sold if dividends were entirely funded through BTC sales. Saylor also argued the scale of any such sale would remain small compared with Bitcoin’s daily market liquidity, which he estimated at between $20 billion and $50 billion.
Strategy expands Bitcoin financing model
During his Bitcoin 2026 keynote and subsequent posts on X, Saylor described Strategy’s structure as a three-part capital system built around Bitcoin reserves.
In Saylor’s framework, Bitcoin functions as “digital capital,” STRC operates as “digital credit,” and MSTR represents the leveraged equity layer tied to the company’s BTC treasury.
He said Strategy is “converting digital capital Bitcoin into digital credit (STRC) and digital equity (MSTR).”
STRC, also called “Stretch,” is Strategy’s perpetual preferred stock product designed to maintain a price close to its $100 par value.
According to Saylor’s Bitcoin 2026 presentation and Strategy’s digital credit dashboard, the company adjusts STRC’s monthly dividend rate while using an at-the-market issuance program to sell new shares when the product trades at or above par.
Cash raised through those sales is then used to purchase more Bitcoin for the company’s reserve balance.
During the same presentation, Saylor said STRC had grown to roughly $8.5 billion in assets under management within about nine months. He also described the product as targeting the private credit market, which he estimated at $3.5 trillion.
Meanwhile, KuCoin’s summary of the Bitcoin 2026 conference noted that STRC’s design channels Bitcoin-related returns into monthly income products.
The report added that the instrument was structured around an 11% yield assumption tied to Bitcoin’s 38% annualized return and a 5:1 collateral ratio intended to absorb steep BTC price declines.
On the equity side, MSTR continues to function as Strategy’s public-market Bitcoin exposure vehicle.
A recent BitcoinTreasuries profile noted that the company now holds more than 800,000 BTC, while Yahoo Finance reported that roughly 85% of a recent $2.5 billion Bitcoin purchase by Strategy was financed through STRC issuance.
Elsewhere in the discussion, Saylor rejected criticism from gold advocate Peter Schiff, who argued that Strategy’s financing structure could face pressure during periods of Bitcoin weakness or rising dividend obligations.
Saylor responded that critics who do not accept Bitcoin as “digital capital” are unlikely to support financial products built around it.
Crypto World
Aptos encrypted mempool targets frontrunning and censorship
Aptos plans to launch a native encrypted mempool to protect transaction intent at the protocol layer.
Summary
- Aptos says its encrypted mempool will hide transaction details during block ordering before execution.
- The feature still needs governance approval before Aptos can roll it out to users.
- Aptos Labs says batched threshold encryption can limit latency while keeping network trust assumptions.
The network said the feature will keep pending transaction details hidden during block ordering, then reveal them before execution.
The feature still depends on governance approval. Aptos said, “Pending governance approval, Aptos will be the first L1 to offer a native encrypted mempool.” The project says users will be able to send protected transactions with one click, without changing the normal on-chain record after confirmation.
Aptos keeps transaction intent hidden
Aptos Labs said most blockchains expose pending transactions before they reach a block. That visibility can let validators, bots, or other actors delay, reorder, copy, or censor trades before confirmation.
The encrypted mempool is designed to reduce that risk. Aptos Labs said transaction details remain confidential until execution, protecting users from frontrunning, censorship, and order-flow manipulation while confirmed transactions remain public on-chain as usual.
Moreover, Aptos Labs said the system uses batched threshold encryption. Under the design, validators can collectively decrypt batches of transactions in one operation, reducing communication and computing overhead compared with decrypting each transaction separately.
The team said this approach can work inside the Aptos consensus process while keeping the same trust assumptions as the network. Aptos Labs added that users should be able to submit encrypted transactions with “no impact to latency” once the system is live.
Institutional market push grows
Aptos framed the encrypted mempool as part of a wider push for large on-chain markets. The network said the feature can help protect large transactions from censorship and frontrunning, which remain common concerns in decentralized trading.
The move also follows wider ecosystem spending. Earlier reports noted that Aptos Foundation and Aptos Labs committed more than $50 million to support trading, AI agents, research, and protocol infrastructure. That plan includes Decibel, an on-chain order book and perpetuals exchange that Aptos said had crossed $1 billion in cumulative volume.
Aptos has also been adding privacy-focused features for institutional use. Related coverage noted that Confidential APT launched in April, allowing concealed transfer data while keeping verifiability. The encrypted mempool would add another layer by protecting transaction intent before execution.
Crypto World
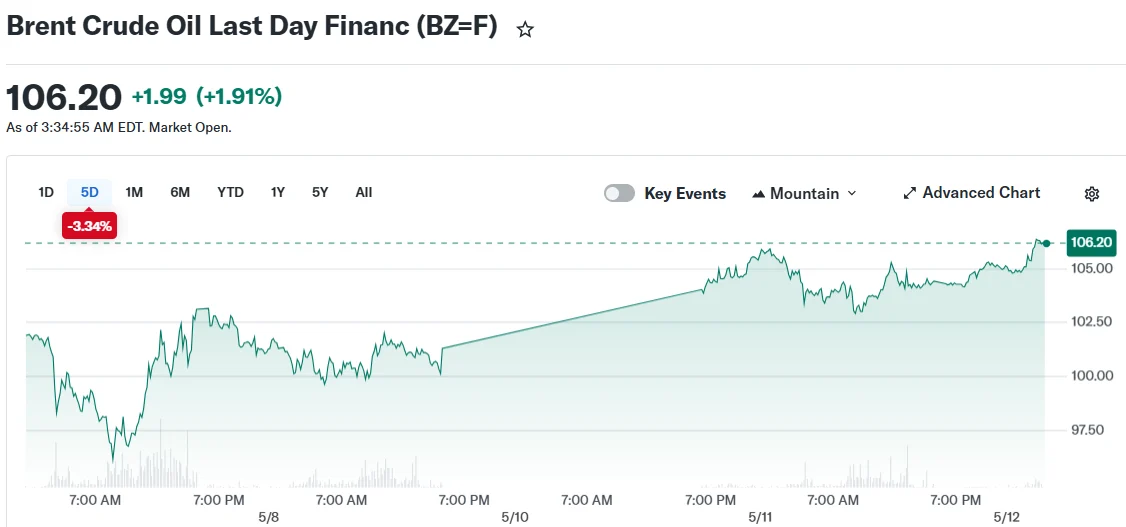
Trump Calls Iran Ceasefire ‘On Life Support’ as Oil Prices Surge Past $105

TLDR
- President Trump dismissed Iran’s peace proposal as “totally unacceptable,” declaring the ceasefire is on “massive life support”
- Oil prices surged with Brent crude reaching approximately $105 per barrel and WTI approaching $99
- Tehran’s demands included ending the US naval blockade, sanctions relief, and maintaining partial authority over Strait of Hormuz operations
- Aramco’s chief executive stated global markets are hemorrhaging 100 million barrels weekly due to the strait closure
- Market participants are monitoring upcoming inflation reports and Trump’s Beijing meeting with President Xi for market direction
President Trump dismissed Iran’s most recent peace proposal on Monday, branding it “totally unacceptable” and referring to it as a “piece of garbage.” Speaking to the press, he characterized the ceasefire as being on “massive life support,” amplifying concerns that the conflict entering its tenth week could reignite.
[[EMBED_0]]
Oil markets responded sharply on Tuesday, with Brent crude advancing to approximately $105 per barrel, extending gains of nearly 3% from the previous trading session. West Texas Intermediate similarly climbed to roughly $99 per barrel.
The military confrontation commenced approximately ten weeks ago, with a tenuous ceasefire established in early April. However, continued maritime attacks throughout the region have sustained elevated geopolitical tensions.
Tehran’s counter-proposal to Washington’s peace framework contained multiple conditions: termination of the American naval blockade, comprehensive sanctions relief, restoration of Iranian petroleum exports, compensation for war-related damages, and preservation of partial oversight regarding maritime traffic through the Strait of Hormuz.
The Strait of Hormuz represents a critical artery for global energy transportation. Approximately 20% of the world’s oil and refined fuel products transit through this strategic waterway.
Supply Chain Impact of the Strait Blockade
Amin Nasser, chief executive of Saudi Aramco, revealed that global energy markets are forfeiting 100 million barrels of oil supply weekly while the strait remains inaccessible. While Aramco has redirected certain shipments through its Red Sea facilities, crude prices remain historically elevated and major purchasers like China have significantly reduced their import volumes.
Domestic gasoline prices across America have spiked considerably, creating substantial political pressure on President Trump and congressional Republicans as the November midterm elections approach. The administration has authorized strategic petroleum reserve releases in efforts to stabilize consumer fuel costs.
Analysts at Bloomberg Economics assessed that comprehensive peace negotiations appear improbable. Their outlook suggests hostilities may resume but would potentially stabilize into sporadic, lower-intensity confrontations, characterizing this scenario as “the new normal.”
Axios has reported that Trump is convening his national security advisors to evaluate potential resumption of military operations. In a Fox News interview, the President indicated he’s reconsidering a proposal to provide naval escorts for commercial vessels traversing the strait.
Market Focus Points Going Forward
Financial markets are intensely focused on Tuesday’s US Consumer Price Index release. Economic forecasters anticipated the headline inflation metric would accelerate to 3.7% from the prior 3.3% year-over-year reading, partially attributable to elevated energy expenses stemming from the Middle East crisis.
Wednesday’s producer price index figures are similarly projected to reveal mounting cost pressures from increased gasoline and transportation expenses throughout the supply chain.
Accelerating inflation could complicate Federal Reserve policy decisions and potentially sustain elevated interest rates for an extended period.
Market participants are simultaneously monitoring President Trump’s scheduled diplomatic engagement with Chinese President Xi Jinping in Beijing. The bilateral discussions are anticipated to address Iran policy, commercial relations, and energy security frameworks. China maintains its position as Iran’s largest petroleum customer and exercises considerable diplomatic leverage with Tehran.
The Treasury Department imposed additional sanctions Monday targeting entities facilitating Iranian oil sales to Chinese buyers. Market observers suggested the Trump-Xi summit outcome could prove decisive in determining the conflict’s trajectory.
Technical market strength indicators have deteriorated in recent trading sessions as certain refineries have reduced their purchasing activity.
Crypto World
ABA Pushes Banks to Lobby Senators Over Stablecoin Yield Provisions
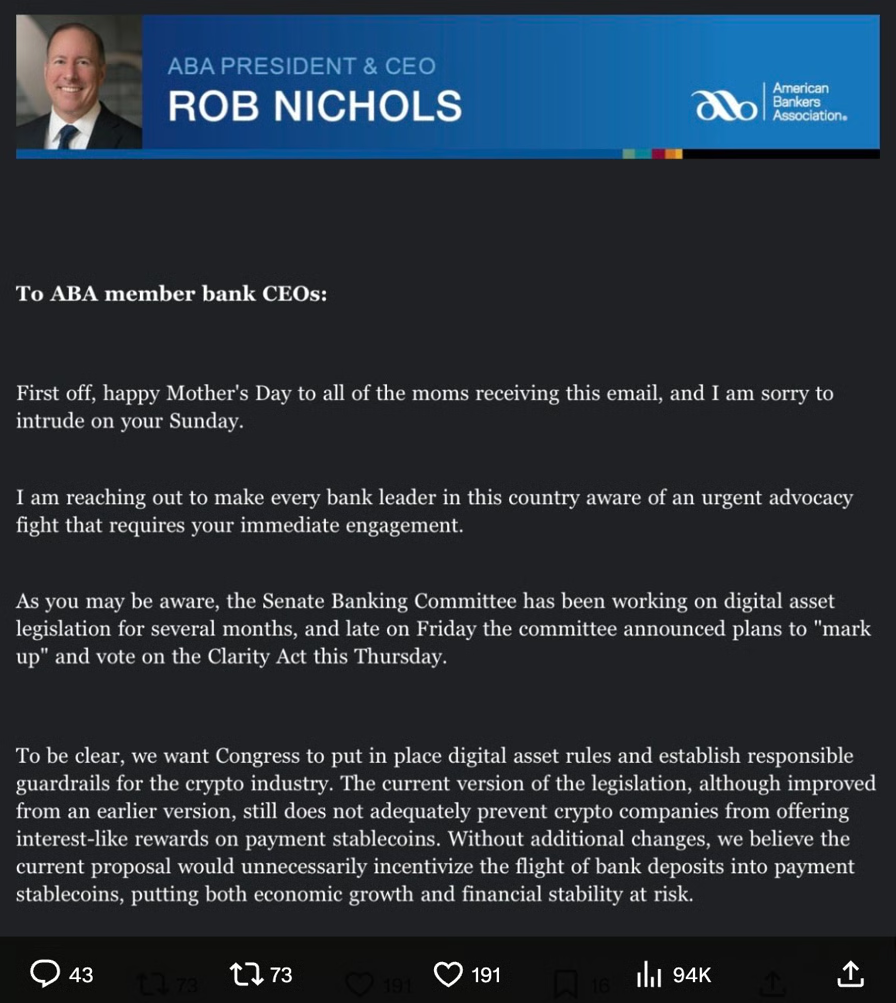
The American Bankers Association is lobbying US senators ahead of this week’s Senate Banking Committee markup of crypto legislation, warning that proposed stablecoin rules could incentivize consumers to move deposits out of banks.
In a Sunday message to member bank CEOs shared on X by Punchbowl News reporter Brendan Pedersen, ABA president and CEO Rob Nichols said the current version of the CLARITY Act does not adequately prevent crypto companies from offering interest-like rewards tied to payment stablecoins.
Nichols urged bankers to contact senators and encourage employees to do the same before Thursday’s committee markup, describing the issue as an “urgent advocacy fight” for the banking industry.
“The legislation would permit stablecoin issuers and associated business partners to pay interest or interest-like incentives to stablecoin holders,” Nichols wrote, adding that the provision could create “a digital asset loophole” that would allow deposits to migrate outside the traditional banking system.

Source: Brendan Pederson
Nichols said the ABA had been “working hard behind the scenes for months” on the issue and warned that allowing non-bank stablecoin issuers to offer interest-like incentives could threaten “economic growth and financial stability.”
The latest lobbying effort follows a Friday letter from the ABA and other major US banking associations urging Senate lawmakers to strengthen the bill’s stablecoin yield restrictions, arguing the current language still allows structures that could incentivize users to move deposits out of banks.
Related: 7 Democrats seen as ‘key’ to advancing CLARITY Act: Galaxy
CLARITY Act stablecoin yield fight continues ahead of Senate vote
The CLARITY Act, which aims to establish a federal regulatory framework for digital assets and is scheduled for a Senate Banking Committee vote on Thursday, has fueled months of debate between banks and the crypto industry over stablecoin yield provisions.
In April, the ABA criticized a White House report that said banning stablecoin yield would have only a limited impact on bank lending, while Bank of America CEO Brian Moynihan warned earlier this year that such products could pull as much as $6 trillion out of the banking system.
Crypto companies, meanwhile, have pushed back against the banking industry’s position, with Coinbase CEO Brian Armstrong among the most vocal critics of banks for offering near-zero interest rates on customer deposits while opposing yield-bearing stablecoin products.

X post Sept. 29, 2025. Source: Brian Armstrong
Earlier this month, lawmakers attempted to strike a compromise by publishing updated stablecoin yield provisions prohibiting crypto companies from offering interest or yield solely for holding payment stablecoins while still permitting rewards tied to “bona fide activities.” However, some banking groups argued the revised restrictions did not go far enough.
While debate over stablecoin yield provisions continues, recent polling suggests support for broader crypto legislation is growing across party lines.
A HarrisX survey of 2,008 registered US voters found that 52% support the CLARITY Act, while 47% said they would consider voting across party lines for a candidate who backed the legislation.
Prediction market Polymarket at last look gives the CLARITY Act a 65% chance of being signed into law before the end of the year, up from around 46% at the end of April. Platform users have staked $672,289 on the outcome, at last look.

Source: Polymarket
Magazine: XRP ‘probably going to $12,’ Bitcoin ETFs add $1B: Market Moves
Crypto World
This Is How Much the Iran War Is Adding to Every American’s Fuel Bill
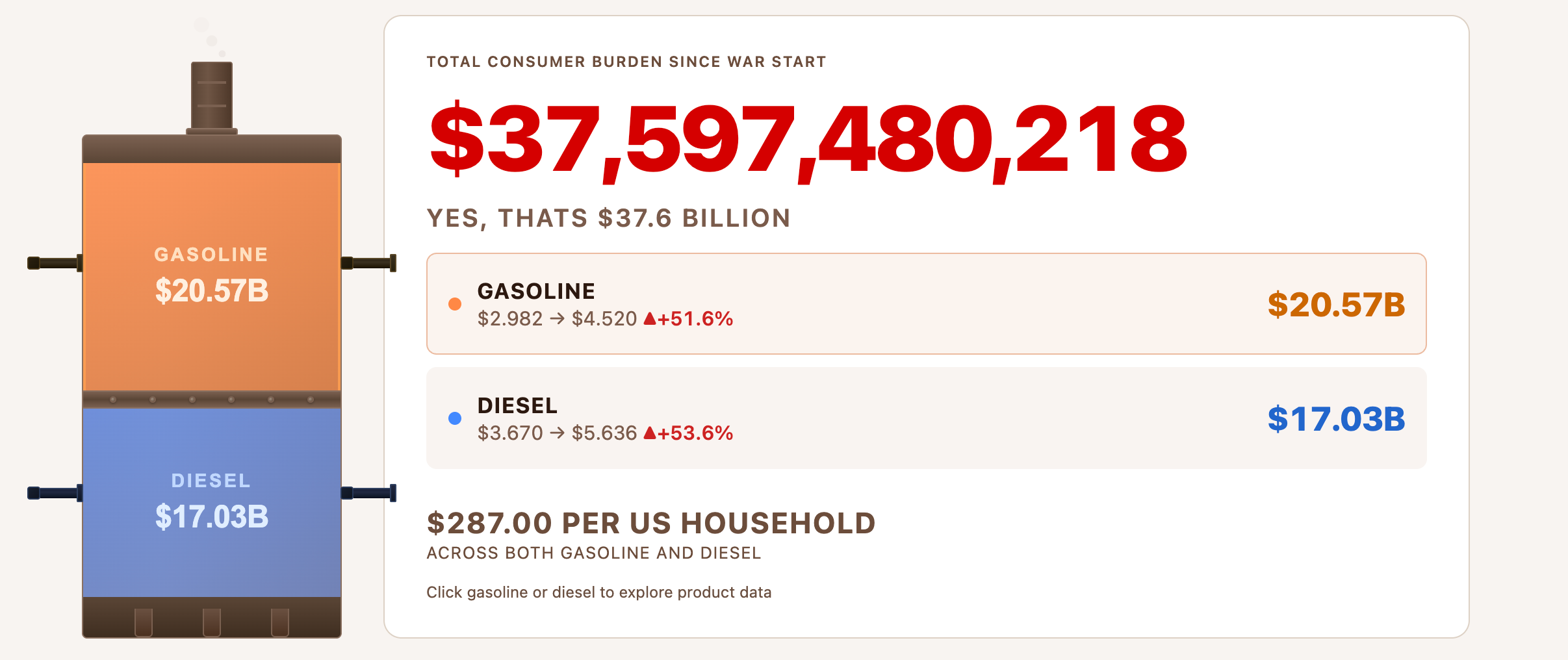
Americans have spent $37.6 billion more on gasoline and diesel since the Iran war erupted on February 28.
This data comes from a live tracker from Brown University’s Watson School of International and Public Affairs.
The Iran War Has Cost Every American Household $287 in Extra Fuel So Far
The figure breaks down to about $287 per US household, with national gas prices now averaging $4.52 a gallon. The price marks a 51.6% jump from the pre-war level of $2.98 over just 72 days.
“Fuel costs are just one part of a war’s consequences, but they come directly out of Americans’ pockets. These costs are rising everyday,” the website reads.
Follow us on X to get the latest news as it happens

The Iran War Energy Cost Tracker is led by Jeff Colgan, director of the Climate Solutions Lab at Brown’s Watson School.
The model compares fuel data from the American Automobile Association with estimated levels had the conflict not occurred. The gap between actual and counterfactual prices forms the cost calculation.
“This is an expense coming directly out of the pockets of American consumers, and consumers,” Colgan said.
It’s not just the households. BeInCrypto previously reported that US airlines spent $5.06 billion on jet fuel in March. That was a 56% jump from February as the conflict disrupted global supply.
Hormuz Closure Drives the Squeeze at the Pump
This highlights the broader economic impact of the conflict, which has led to the closure of the Strait of Hormuz, a critical passage for nearly 20% of global energy shipments.
The impact has also extended beyond energy markets. Inflation among US food and beverage companies rose 7.9% year-over-year in March, marking the sharpest increase in at least a year.
Meanwhile, public sentiment has also turned. A Generation Lab survey of Americans found 77% believe the strikes against Iran were the wrong call.
Subscribe to our YouTube channel to watch leaders and journalists provide expert insights
The post This Is How Much the Iran War Is Adding to Every American’s Fuel Bill appeared first on BeInCrypto.
Crypto World
Goliath CEO Apologizes to Investors Over Alleged Ponzi
Christopher Delgado, the former CEO of Goliath Ventures, has publicly apologized to investors for what US prosecutors allege was a $328 million crypto investment Ponzi scheme.
“They put their trust in me, and I failed them,” Delgado told ABC-affiliated television station WFTV in an interview aired on Monday. Delgado said he wanted to publicly explain what happened “from beginning to end” and express “how sorry I am.”
Delgado claimed that he voluntarily returned to the US to face charges of fraud and money laundering brought by the Orlando US Attorney’s Office on Feb. 20. He faces a maximum penalty of 30 years in federal prison if convicted on all counts.
He has been accused of soliciting victims into investing substantial sums of money under false and fraudulent promises of monthly returns generated through crypto liquidity pools. WFTV reported that investors ranged from nurses and teachers to firefighters and retirees.

Christopher Delgado speaking in an interview with WFTV. Source: WFTV
Delgado said Goliath was paying people “an astronomical amount of money” when questioned on how the company allegedly used millions of dollars in investor funds.
The US Attorney’s Office alleged that Delgado ran Goliath as a Ponzi scheme between January 2023 and January 2026 and used some of the funds to purchase four properties in Florida valued at a combined $14.5 million.
The investor funds were also allegedly used to pay for “Goliath’s extravagant business gatherings, Christmas parties, and luxury travel accommodations,” the US Attorney’s Office said.
It claimed one investor lost around $720,000 despite promises from Goliath that he would get a guaranteed return and that his investment could be returned at any time.
WFTV said Delgado is currently on bail, wearing an ankle monitor while confined to his 11,000 square foot estate that was allegedly purchased with investor funds.

Delgado’s 11,000 square foot estate in Florida. Source: WFTV
Delgado claimed there was only $160,000 left in the Goliath Ventures bank account around the time of his arrest.
Delgado said that he didn’t act alone and that he is cooperating with federal law enforcement to provide information about what he claimed is his former colleagues’ involvement in the alleged Ponzi scheme.
JPMorgan sued over ties to Goliath
In March, investors sued Wall Street bank JPMorgan Chase, claiming it helped facilitate fund flows to Goliath.
Related: California man jailed for 78 months over $250M crypto theft conspiracy
A proposed class lawsuit claimed that JPMorgan knew, by virtue of its Know Your Customer obligations, that Goliath was operating as a private equity-style cryptocurrency investment pool despite not being licensed to offer or sell those types of investment products.
The investors alleged that $253 million was deposited into a JPMorgan bank account between January 2023 and June 2025, with roughly $123 million later transferred to Goliath wallets at Coinbase.
Last month, a Florida federal court judge extended the deadline for prosecutors to file an indictment against Delgado to June 26.
Magazine: North Korea denies crypto hacks, Upbit’s bank tests Ripple: Asia Express
Crypto World
Glamsterdam Milestones Hit, Ethereum Foundation Names Protocol Leads

The Ethereum Foundation has reported notable progress on the upcoming Glamsterdam upgrade, outlining a credible post-upgrade target and accelerating preparations on several parallel fronts. In a blog post, the foundation said it has established a 200 million gas limit floor as part of Glamsterdam’s rollout, a substantial increase from the current level around 60 million. The move is geared toward delivering a meaningful speed boost for post-upgrade network throughput and set the stage for the long-term scaling roadmap.
The foundation reiterated that the immediate priority is shipping Glamsterdam, which programmers had originally slated for June but are now targeting in the third quarter of 2026. Glamsterdam is billed as a foundational upgrade for the layer-1 chain, aimed at rethinking how the network processes transactions and manages its rapidly expanding data store, effectively “fundamentally updating how Ethereum creates and verifies blocks.”
Beyond Glamsterdam, Ethereum’s roadmap remains anchored by ongoing work on Hegotà, the anticipated next major upgrade, and the Strawmap, the project’s roadmap for quantum-readiness. The Ethereum Foundation noted that Glamsterdam devnets are live and that scoping for Hegotà is well underway, with continued progress being tracked at an interop event held in Svalbard, Norway.
Key takeaways
- Glamsterdam targets a 200 million gas limit floor, a major step up from current levels and a potential driver of higher throughput after the upgrade.
- Official timing has shifted from June toward the third quarter of 2026, with the focus remaining on delivering Glamsterdam and its scaling innovations.
- Enshrined Proposer-Builder Separation (ePBS) stabilization has been confirmed, integrating the division of block-building duties more deeply into Ethereum’s rules.
- EIP-8037, which prices data storage more efficiently, has been finalized to curb uncontrolled state growth as gas limits rise.
- The Ethereum Foundation is undergoing a leadership transition in its Protocol cluster, bringing in new leads while several core developers move on or take sabbaticals.
Glamsterdam: scaling the L1 and redefining block creation
At its core, Glamsterdam is designed to reorganize Ethereum’s transaction processing and block verification so the network can handle a larger daily load without compromising safety. The plan to establish a 200 million gas floor signals the network’s intent to push forward with higher-capacity blocks while maintaining stability during the transition. The move aligns with broader efforts to improve L1 efficiency ahead of subsequent upgrades that promise to broaden the ecosystem’s capabilities for decentralized applications and user experience.
The Ethereum Foundation emphasized that the immediate aim is to ship Glamsterdam, with a revised timeline placing the upgrade in Q3 2026 rather than June. Developers are reportedly actively testing and refining the upgrade in devnets. The Svalbard interop event cited ongoing collaboration and alignment among researchers, developers, and infrastructure teams as they validate cross-component interactions and ensure the upgrade’s components work cohesively in practice.
In parallel with Glamsterdam, the Foundation remains focused on Hegotà, the forthcoming major upgrade, and the Strawmap, Ethereum’s strategic plan for quantum resistance and long-term data management. The combination of these tracks reflects a deliberate, multi-layered approach to scaling Ethereum while preserving its security guarantees and decentralization ethos. The Strawmap, in particular, remains a touchstone for how Ethereum intends to evolve in the quantum era, balancing forward-looking security with practical deployment paths.
Smarter data storage and a more resilient block-building model
Two significant protocol milestones were highlighted as part of the ongoing evolution. First, the enshrined Proposer-Builder Separation (ePBS) has reached stabilization, formalizing how validators outsource block-building duties to a set of specialized builders within Ethereum’s consensus rules. This enshrinement minimizes reliance on external relays and gives the network a longer runway to accommodate larger blocks safely. The shift aims to reduce latency and improve block production efficiency without compromising the core safety properties that underpin Ethereum’s security model.
Second, EIP-8037 has been finalized, introducing smarter pricing for storing state data. By raising the cost of state-creation operations, the proposal helps prevent unsustainable growth of on-chain state as block gas limits rise. The combination of ePBS and EIP-8037 is intended to bolster Ethereum’s data management framework at a time when higher throughput could otherwise accelerate state growth if not properly priced and managed.
These changes are not standalone; they are part of a cohesive effort to ensure that Glamsterdam and subsequent upgrades can deliver meaningful improvements in performance and cost-efficiency while keeping the network resilient against data bloat and security risks associated with larger blocks.
Protocol leadership enters a transitional phase
The Ethereum Foundation also disclosed a leadership transition within its Protocol cluster. Will Corcoran, Kev Wedderburn, and Fredrik have been named as new leads guiding protocol development, signaling a renewed wave of coordination and direction for core research and implementation work. In parallel, two long-standing contributors, Barnabé Monnot and Tim Beiko, are moving on from Foundation roles, and Alex Stokes will be taking sabbatical leave for a period. Corcoran commented that the Protocol cluster is entering a new chapter that emphasizes broad collaboration and continued delivery of Glamsterdam, Hegotà, and the Strawmap. Monnot underscored a commitment to making Ethereum’s distinctive features more accessible to users and to participating in a plural approach to how Ethereum gets built.
The leadership changes come as Ethereum’s development cadence remains intense, with multiple upgrade tracks running in parallel. The aim is to ensure that the core protocol remains adaptable to emerging technologies and user needs while maintaining the reliability that large-scale decentralized applications require. Observers will want to watch how this leadership transition influences cross-team coordination and the prioritization of Glamsterdam’s milestones against Hegotà and the quantum-resilience roadmap embedded in Strawmap.
Roadmap momentum: Hegotà and the quantum-ready Strawmap
Glamsterdam is the first major upgrade in Ethereum’s extended roadmap, but it sits within a broader program that includes Hegotà and Strawmap. Hegotà is described as the next major upgrade after Glamsterdam, with planning and scoping already underway. Meanwhile, Strawmap continues to guide Ethereum’s approach to future data management and quantum resistance, ensuring that the network remains prepared for anticipated cryptographic challenges and workload growth. The interop activity in Svalbard underscores a shared effort among developers to validate compatibility across components and to align on a coherent sequence of upgrades that collectively advance Ethereum’s long-term vision.
What remains uncertain—and what readers should monitor closely—is the exact timing and readiness of each milestone, especially as Glamsterdam’s timeline shifts earlier or later depending on testing outcomes, network conditions, and coordination across ecosystems. Investors, developers, and users will want to keep an eye on devnet stability, the pace of Hegotà scoping, and the practical implications of ePBS and EIP-8037 on on-chain data costs and validator operations.
Looking ahead, the Ethereum ecosystem appears intent on balancing aggressive scaling with disciplined governance. Glamsterdam’s rollout, paired with smarter data pricing and a strengthened block-building model, positions Ethereum to absorb higher demand while maintaining robustness. As the Foundation continues to rotate leadership and align cross-team priorities, market watchers should watch for concrete milestones in devnet testing, cross-client interoperability, and the emergence of tangible upgrades that translate into improved user experiences and more scalable infrastructure for decentralized applications.
As the roadmap unfolds, traders and builders should stay tuned for updates on Glamsterdam’s progress, the pacing of Hegotà development, and the ongoing refinement of Strawmap’s quantum-ready framework. The coming quarters will be critical in determining how quickly Ethereum can translate these architectural changes into real-world benefits for developers, protocols, and end users alike.
-

 Crypto World4 days ago
Crypto World4 days agoHarrisX Poll Found 52% of Registered Voters Support the CLARITY Act
-

 Fashion4 days ago
Fashion4 days agoWeekend Open Thread: Marianne Dress
-

 Crypto World5 days ago
Crypto World5 days agoUpbit adds B3 Korean won pair as Base token gains Korea access
-

 NewsBeat5 days ago
NewsBeat5 days agoNCP car park operator enters administration putting 340 UK sites at risk of closure
-

 Fashion15 hours ago
Fashion15 hours agoCoffee Break: Travel Steam Iron
-

 Tech2 days ago
Tech2 days agoAuto Enthusiast Carves Functional Two-Stroke Engine from Solid Metal
-

 Politics10 hours ago
Politics10 hours agoWhat to expect when you’re expecting a budget
-

 Fashion1 day ago
Fashion1 day agoWhat to Know Before Buying a Curling Wand or Curling Iron
-
 Politics3 days ago
Politics3 days agoPolitics Home Article | Starmer Enters The Danger Zone
-

 Business3 days ago
Business3 days agoIgnore market noise, India’s long-term story intact, say D-Street bulls Ramesh Damani and Sunil Singhania
-

 Crypto World7 days ago
Crypto World7 days agoUAE Free Zone Deploys Blockchain IDs to Verify Registered Firms
-

 Tech1 day ago
Tech1 day agoGM Agrees To Pay $12.75 Million To Settle California Lawsuit Over Misuse Of Customers’ Driving Data
-
 Crypto World6 days ago
Crypto World6 days agoBlackRock CEO Larry Fink Discusses a New Asset Class
-

 Entertainment5 days ago
Entertainment5 days agoSarah Paulson Called Out For Met Gala ‘Hypocrisy’
-

 Crypto World5 days ago
Crypto World5 days agoRobinhood says Wall Street is building onchain
-
Sports6 days ago
NBA playoff winners and losers: Austin Reaves is not loving Lakers vs. Thunder matchup, but Chet Holmgren is
-

 Entertainment5 days ago
Entertainment5 days agoGeneral Hospital: Ric & Ava Bombshell – Ric’s Massive Secret Exposed!
-
 Entertainment6 days ago
Entertainment6 days agoBold and Beautiful Early Spoilers May 11-15: Steffy Revolted & Liam Overjoyed!
-

 Tech6 days ago
Tech6 days agoApple and Samsung are dominating smartphone sales so thoroughly that only one other company makes the top 10
-

 Fashion5 days ago
Fashion5 days agoThe Best Work Pants for Women in 2026












You must be logged in to post a comment Login