The EPICS (Engineering Projects in Community Service) in IEEE program, administered by IEEE Educational Activities, has launched the Excellent EPICS in IEEE Contributor Awards. The recognitions honor the program’s outstanding students and faculty volunteers in Excellent Team Leader and Excellent Faculty Advisor categories.
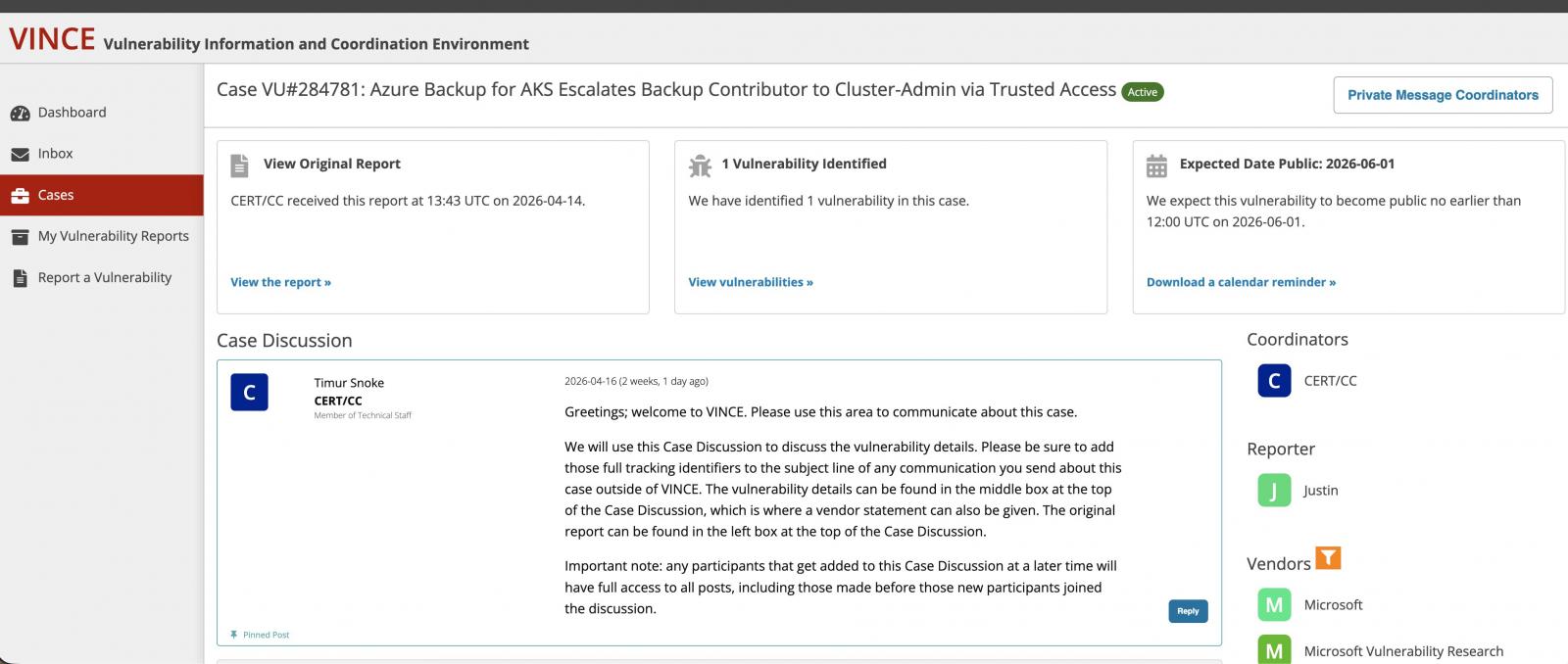
The awards recognize individuals whose leadership, mentorship, and commitment have meaningfully advanced the impact of EPICS projects. Candidates must demonstrate clear, measurable contributions that elevate both the student experience and the outcomes delivered to community partners. Reviewers also consider other awards, publications, presentations, and professional achievements that reinforce the nominee’s credibility and leadership.
Recipients must demonstrate outstanding project management and documentation, strong mentoring and collaboration, and high-quality outcomes.
Here are this year’s recipients.
Team Leader Award
Surattana Kakay is a computer engineering student at Rajamangala University of Technology Thanyaburi (RMUTT), located in IEEE Region 10 (Asia Pacific). Kakay, an IEEE student member, was honored for guiding her team in the design, development, and implementation of the Automatic Water Level Control System project, which aids rice farmers in Thailand.
As the team leader, Kakay played a pivotal role in transforming the student initiative into an operational, community‑centered solution. Her inspiration was purpose-driven, she says.
“My motivation was to apply engineering to real agricultural challenges, like water scarcity and climate change,” she says. “I wanted to bridge advanced technology with the tangible needs of local farmers.”
She managed the project end to end—coordinating workflow, assigning tasks based on team members’ strengths, and ensuring each phase of development aligned with the technical road map she created. She served as the primary liaison between the student team, the Pathum Thani Rice Research Center, and farmers to make sure the system was practical and user‑friendly, and that it addressed community needs.
“Watching students grow as they design solutions that improve lives has been both inspiring and deeply humbling.” —Elizabeth Vidal-Duarte
Under her leadership, the team developed a low‑cost IoT‑based alternate wetting and drying (AWD) system that lets farmers remotely monitor and control water levels in rice paddies using smartphones. Kakay oversaw the integration of noncontact laser time‑of‑flight sensors to withstand harsh field conditions, and she championed the use of long-range technology connected to a free community Wi‑Fi network to eliminate Internet service fees.
The results were transformative, Kakay says.
“Our AWD system reduces water consumption by 63 percent and methane emissions by 7 percent annually,” she says. “Turning an academic assignment into a real‑world solution that delivers measurable, sustainable results has been incredibly meaningful.”
Her achievements advanced sustainability for Thailand’s most water‑intensive crop while demonstrating the potential of accessible engineering solutions.
Beyond technical innovation, Kakay cultivated a culture of learning, continuity, and empowerment within her team. She introduced a mentorship framework to support future student cohorts. She and her team produced academic papers, visual media, and presentations to communicate the project’s value to scientific audiences as well as the general public.
“Surattana Kakay is a pivotal figure in turning innovation into reality and delivering tangible benefits to the community,” says IEEE Member Thanasin Bunnam, her faculty advisor and an assistant professor at RMUTT.
Kakay’s leadership journey became a personal milestone, she says: “Leading this project transformed me from a student into a team leader. As a female engineer, it empowered me to advocate for women in engineering and show that gender is no barrier to technical excellence.”
Through her guidance, the AWD project evolved from a classroom assignment into a solution that illustrates IEEE’s mission of advancing technology for humanity.
Faculty Advisor Awards
Navid Shaghaghi, a lecturer and researcher at Santa Clara University, in California, was recognized for his dedication to integrating service learning into engineering education and fostering student innovation that benefits underserved communities in IEEE Region 6 (Western USA).
During his more than six years of engagement with EPICS in IEEE, Shaghaghi, an IEEE senior member, has demonstrated exceptional leadership in advancing sustainable, human‑centered engineering through the long‑running Hydration Automation (HA) project and the HiveSpy initiative. They are part of Santa Clara University’s Frugal Innovation Hub and EPIC Research Laboratory.
Since 2019, Shaghaghi has served as principal investigator for the HA project, guiding its evolution from prototype to a robust, field‑tested irrigation automation system that supports small ranches and community farms in California.
The HA project is a low‑cost system that helps reduce water waste by monitoring soil moisture and automating watering. By combining ultrasonic tank sensing, soil sensors, and ongoing technical support, the project improves efficiency, lowers operational costs, and promotes more sustainable urban agriculture.
Under Shaghaghi’s guidance, more than 30 undergraduate and graduate students have gained hands-on experience in IoT development, field deployment, testing, and client collaboration.
His commitment to frugal innovation and human‑centric design has resulted in solutions that are minimalist, affordable, sustainable, portable, and rugged—often challenging conventional approaches to agricultural technology.
“Turning an academic assignment into a real‑world solution that delivers measurable, sustainable results has been incredibly meaningful.” —Surattana Kakay
The HA project has produced new research publications and earned recognition, including a third-place finish by Shaghaghi’s graduate students at this year’s IEEE Rising Stars Project Showcase. During the annual event, students and young professionals present their technical innovations to industry leaders and peers.
The HiveSpy project is a low‑cost, frame‑level IoT monitoring system that helps beekeepers automate labor‑intensive tasks and prevent hive swarming by tracking production yield in real time. By collecting frame‑weight data and generating optimized harvest schedules, the system reduces manual workload while improving the hive’s health and boosting honey output.
Shaghaghi says his mentorship has been shaped by the realities of student turnover, a challenge he embraces with optimism and adaptability.
“The transient nature of student teams is a challenge but one you must embrace, bear‑hug style,” he says. “By energizing your student community and welcoming new contributors, you’ll be amazed by the brilliant solutions they bring.”
His philosophy has allowed him to cultivate a thriving pipeline of student innovators, he says, and he has strengthened his own professional practice as well.
“I’ve been mentoring EPICS in IEEE students since 2019,” he says. “It has taught me resilience and how to operate on a tight budget while still delivering real‑world results.”
Beyond the technical achievements, Shaghaghi’s work reflects a commitment to humanitarian technology and service learning. As the founder and director of the EPIC (Ethical, Pragmatic, and Intelligent Computer) lab, he has built a diverse, interdisciplinary community dedicated to innovation for the benefit of humanity.
For him, he says, the EPICS in IEEE award carries profound meaning: “Receiving this award validates my deepest conviction in humanitarian technology research and strengthens my commitment to service‑learning education.”
His students echo those sentiments. One team member said “Professor Shaghaghi is an engine of progress who keeps forging ahead.”
Through his leadership, Shaghaghi has created an enduring model of mentorship, innovation, and community partnership that is helping to shape the next generation of socially responsible engineers.
Elizabeth Vidal-Duarte is celebrated for her impactful mentorship and leadership in expanding EPICS in IEEE engagement across Peru and IEEE Region 9 (Latin America and Caribbean). Vidal-Duarte, a research professor at San Agustin National University Arequipa, in Peru, is a faculty advisor and technical mentor for two EPICS in IEEE projects. She encouraged students to apply to the EPICS program, helped them identify community needs, and supported them in crafting proposals grounded in service‑learning principles.
Under her leadership, the students developed a functional soft robotic glove used at Clínica San Juan de Dios to help patients improve their fine-motor skills. The clinic’s therapists use the device to measure the range of motion of joints at the beginning and end of each patient’s therapy session to improve their assessments. Compared with traditional manual measurements using a goniometer, the glove significantly reduces evaluation time and enables digitally recorded data, improving clinical efficiency and decision-making.
The second project is an emotion‑recognition system for people with visual impairment. The AI‑powered wearable helps recognize a person’s emotions through real‑time facial‑expression detection and haptic feedback.
The project has resulted in the “Emotion-Aware Assistive System With Wearable Haptic Feedback for Visual Impairment” research paper, which is to be presented at the IEEE International Symposium on Computer-Based Medical Systems, to be held from 3 to 5 June in Limassol, Cyprus.
Vidal-Duarte’s mentorship extends beyond the classroom. She visits rehabilitation centers and clinics to find people with visual impairments to ensure that the technologies she is helping to develop meet their needs.
“EPICS in IEEE has moved me beyond teaching concepts to truly living engineering as a tool for human impact,” Vidal-Duarte says. “Watching students grow as they design solutions that improve lives has been both inspiring and deeply humbling.”
Throughout the development of both projects, Vidal-Duarte provided sustained technical and organizational guidance, helping students define requirements, structure work plans, and overcome challenges in prototyping, testing, and validation.
Reflecting on the broader impact of EPICS, she says the program has given her “more than methodologies and tools—it has given me perspective, purpose, and a global community that constantly challenges me to grow as a mentor and as a human being.”
Her mentorship fostered not only technical excellence but also empathy, ethical awareness, and professional maturity among her students, she says. She guided them in preparing articles for submission to IEEE conferences, interdisciplinary collaboration, and hands-on fieldwork that bridged theory and real‑world constraints.
“Her constant support, her belief in each student’s potential, and her commitment to developing leaders who make a difference define [her] as a faculty advisor,” says Valentina Chabilla, an EPICS in IEEE student team member.
The EPICS recognition reflects her passion for teaching, her dedication to the community, and her impact on projects and students. Her commitment to accessible, sustainable innovation strengthened partnerships between the university and community groups, benefiting underserved populations.
“Receiving this award is both an honor and a responsibility,” she says. “It reminds me of the real impact engineering can have on people’s lives and strengthens my commitment to guiding students in creating meaningful change.”
Her leadership continues to inspire students to view engineering not just as a discipline but also as a powerful force for inclusion, dignity, and social impact.
Advancing the mission
The Excellent Contributor Award recipients exemplify the best of EPICS in IEEE. Through their leadership, they have strengthened the bridge between engineering education and community service, inspiring students to use their skills to create sustainable, real‑world impacts.
As EPICS continues to expand its global reach, the contributions of Kakay, Shaghaghi, and Vidal-Duarte serve as powerful reminders of what is possible when educators, volunteers, and students work together to improve the lives of others through engineering.
From Your Site Articles
Related Articles Around the Web


















































You must be logged in to post a comment Login