Crypto World
Bitcoin’s hard fork proposal to get back $5 billion in stolen Mt. Gox funds sees no takers


Mark Karpelès thought he had a reasonable ask.
The former CEO of defunct exchange MtGox, operating under his GitHub handle MagicalTux, submitted a pull request to Bitcoin Core over the weekend proposing a hard fork (a fundamental change in code that splits the blockchain) that would let 79,956 BTC be redirected from the address they’ve been sitting in since 2011.
At current prices, that’s roughly $5 billion in bitcoin that hasn’t moved in 15 years.
The proposal was narrow, with just under 60 lines of code. A single consensus rule change that would substitute one public key hash for another when validating transactions from the theft address, allowing the MtGox trustee to spend the coins and route them into Japan’s existing court-supervised rehabilitation process.
Read more: Mt Gox: The History of a Failed Bitcoin Exchange
The activation height was set to infinity, meaning nothing would happen unless the community explicitly agreed to turn it on.
It lasted about 17 hours.
The forum was auto-closed even before a discussion took place, with bitcoiners suggesting that Karpelès submitted a pull request directly when he should’ve first discussed the changes on the Bitcoin development list. Some of them said that Karpelès should first propose this as an official Bitcoin Improvement Proposal (BIP).
To be fair, bitcoin core github isn’t the appropriate forum for that kind of community discussion. bitcointalk, X, bitcoin mailing list(s), delving, etc are all a more appropriate forum.
— Matt Corallo 🟠 (@TheBlueMatt) February 27, 2026
The people it was supposed to help rejected it, too. Several MtGox creditors said publicly on X that they didn’t want Bitcoin’s rules rewritten on their behalf. The network’s guarantee that private keys equal ownership matters more to them than getting their coins back.
I’m a creditor. Absolutely not. Would break a key pillar of Bitcoin.
— spoon (@spoonmvn) February 27, 2026
Code is the law
Karpelès had anticipated the objections and listed them himself in the proposal.
The theft is unambiguous, and the coins haven’t moved in 15 years. A legal framework to distribute them already exists. The scope targets one address. Every argument for exceptionalism was there.
Once Bitcoin redirects coins for any reason, the question stops being whether it can and starts being when it will do it again.
Bitfinex victims, DeFi hack victims, and anyone who lost coins to a documented theft could cite this as precedent and seek the same remedy for their incidents. The line between one justified exception and a general mechanism is exactly the kind of subjective boundary Bitcoin was built to avoid.
This is not to say a change in code didn’t happen before.
Previous emergency interventions, such as the 2010 value overflow bug or the 2013 chain split, involved technical failures that threatened the network itself. This was different. The network was working exactly as designed. The proposal was asking it to work differently for one group of people, however sympathetic their case.
The pull request is now closed. $5 billion in bitcoin remains frozen at the same address it’s been at since 2011. And the creditors who might have benefited chose the principal over the payout.
Ultimately, Bitcoin’s fundamental principle of “code is the law” prevailed.
Crypto World
Texas man behind $20M Meta-1 Coin fraud gets 23-year sentence
A Texas man who helped orchestrate a cryptocurrency scam that defrauded roughly $20 million from about 1,000 investors was sentenced to 23 years in federal prison on Tuesday. U.S. District Judge LaShonda Hunt handed down the sentence to Robert Dunlap, who served as a trustee for the Meta-1 Coin project and helped market the fictitious token.
According to the U.S. Attorney’s Office for the Northern District of Illinois, Dunlap and his co-conspirators used a self-created Meta Exchange to inflate the token’s market price and trading volume with automated trading bots, while presenting investors with misleading assurances about asset backing and potential returns. Prosecutors said the scheme relied on false statements and concealed expenses, with funds ultimately used for personal purchases, including luxury vehicles such as a Ferrari.
The defendant was convicted in November on two counts of mail fraud, each carrying a potential sentence of up to 20 years in federal prison. Prosecutors noted in the sentencing memorandum that Dunlap was “unrepentant” and that his misrepresentations escalated over time, underscoring the seriousness of the case as a warning to would-be crypto scammers.
The SEC has been active in pursuing similar schemes. In March 2020, the agency ordered an asset freeze and other emergency relief against Dunlap, an alleged accomplice, Nicole Bowdler, and former Washington state Senator David Schmidt to stop marketing and selling Meta-1 Coin. The SEC alleged that investors were told Meta-1 Coin was risk-free and could deliver enormous returns—claims that investors later learned were false. The agency noted that the coins were never distributed and that funds were diverted to personal use.
Token claims, market manipulation, and the broader crackdown
The case centers on Meta-1 Coin, a token that prosecutors said was touted as backed by a $1 billion art collection—including works by Picasso and van Gogh—and $44 billion in gold. Those asset-backed claims were part of the fraud profile presented by the government, which also described how Dunlap and associates marketed the token through a trust structure from 2018 to 2023. The government alleged investors were promised returns that would dwarf typical crypto gains, with figures that were manipulated to create an illusion of robust trading activity.
Beyond the Meta-1 case, regulators and authorities have signaled a broader push to curb crypto fraud and manipulation. In parallel reporting, authorities have pursued other crypto-related prosecutions, including charges related to hacking and DeFi-related exploits, underscoring a tightening stance as enforcement agencies increasingly scrutinize market misconduct in digital assets.
What this means for investors and the market
The Dunlap sentence highlights the risk profile of investment projects that promise outsized, rapid returns and rely on opaque asset claims. For investors, the case emphasizes the importance of due diligence, independent verification of asset backing, and a healthy skepticism toward platforms that blend trading activity with promises of instant wealth. For the crypto industry, the outcome signals regulators’ willingness to pursue not only misrepresentation but also the operational mechanics that enable such fraud, including automated market manipulation tied to self-hosted exchanges.
Looking ahead, readers should watch how the regulatory pendulum continues to swing on disclosure standards, enforcement actions, and the treatment of asset-backed crypto products. While the Meta-1 saga has reached a definitive sentencing point, the broader crackdown on crypto scams is far from over, with ongoing investigations and charges shaping market expectations for investor protection and compliance in the sector.
According to the U.S. Attorney’s Office in Illinois, the case serves as a stark reminder that alleged crypto fraud carries serious, long-lasting consequences. For further context, the original SEC filing and press release detailing the 2020 asset freeze are available through the agency’s public records.
Crypto World
Circle Internet Group faces class action over failure to stop Drift Protocol exploit funds


- Circle is accused of failing to freeze exploit-linked transfers.
- Approximately $230 million in stolen funds was routed through Circle’s USDC.
- Drift plans $147.5 million recovery backed by future revenue.
Circle Internet Group, the issuer of the USDC stablecoin, is facing a class action lawsuit over its alleged failure to stop the movement of stolen funds linked to the Drift Protocol exploit.
The lawsuit, filed by Drift investor Joshua McCollum at the US district court in Massachusetts on behalf of over 100 impacted users, centres on whether the company had both the ability and the obligation to intervene as the exploit unfolded.
Lawsuit targets Circle’s role in fund transfers
The legal action stems from the April 2026 breach of Drift Protocol, a Solana-based decentralised exchange, where attackers drained roughly $285 million.
A significant portion of those funds, estimated at around $230 million, was quickly converted into USDC.
From there, the funds were moved across chains, primarily from Solana to Ethereum, using cross-chain infrastructure.
The transfers were not instantaneous. They occurred over several hours and were split into more than 100 transactions.
This detail sits at the centre of the lawsuit.
Plaintiffs argue that Circle had a window of opportunity to act.
According to the claim, the company could have frozen the affected wallets or halted the transfers, limiting the damage. Instead, the funds continued moving until they were fully out of reach.
The case accuses Circle of negligence and of indirectly facilitating the loss by failing to act despite having the technical capability to do so.
This argument is reinforced by previous instances where the company has frozen wallets tied to illicit activity, showing that such intervention is not only possible but already part of its operational toolkit.
At its core, the lawsuit raises a difficult question: when a centralised entity operates within a decentralised system, where does its responsibility begin and end?
Drift’s recovery plan
In response to the exploit, Drift Protocol has outlined a structured recovery plan aimed at addressing user losses while rebuilding the platform’s liquidity and operations.
The protocol is seeking to mobilise up to $147.5 million, with a significant portion backed by Tether and other ecosystem partners.
This figure, however, should not be viewed as immediate compensation.
A large share of the funding comes in the form of a revenue-linked credit facility estimated at around $100 million.
This means the protocol will draw funds over time and repay them using future trading fees and platform revenue rather than distributing the full amount upfront.
To manage user claims, Drift plans to issue a new recovery token, though its official name and final structure are yet to be confirmed.
This token will be distributed to affected users and will represent their share of the recovery pool.
It is expected to be transferable, allowing users to either hold it and wait for gradual repayments or sell it on secondary markets for immediate liquidity, likely at a discount.
The recovery pool itself will not rely solely on external funding.
It is designed to be continuously replenished through multiple sources, including protocol revenue, partner contributions, and any funds that may be recovered from the attackers.
This creates a system where repayments are tied directly to the platform’s ability to restart operations and generate consistent trading activity.
Despite these measures, there remains a clear shortfall.
With total losses estimated at approximately $285 million and recovery efforts targeting up to $150 million, a large portion of user funds is not immediately covered.
This gap highlights that users are unlikely to be fully reimbursed in the near term, and recovery will depend heavily on Drift’s long-term performance.
To support a relaunch, part of the recovery framework is also focused on restoring liquidity.
Incentives and financial support are being directed toward market makers to rebuild order books and improve trading conditions once the platform resumes full operations.
Without sufficient liquidity, even a technically sound relaunch would struggle to attract users back.
Another major shift is the protocol’s decision to move away from USDC as its primary settlement asset and instead adopt USDT.
This change comes after roughly $230 million of the stolen funds were converted into USDC and moved across chains during the exploit.
The switch signals a reassessment of risk and reflects a broader effort to restructure the platform’s core infrastructure following the incident.
Overall, Drift’s recovery plan is built around gradual restitution rather than immediate payouts.
Its success will depend on how quickly the platform can regain user trust, restore liquidity, and generate enough revenue to sustain long-term repayments.
Crypto World
Fake Ledger Device Sold Chinese Marketplace: Research
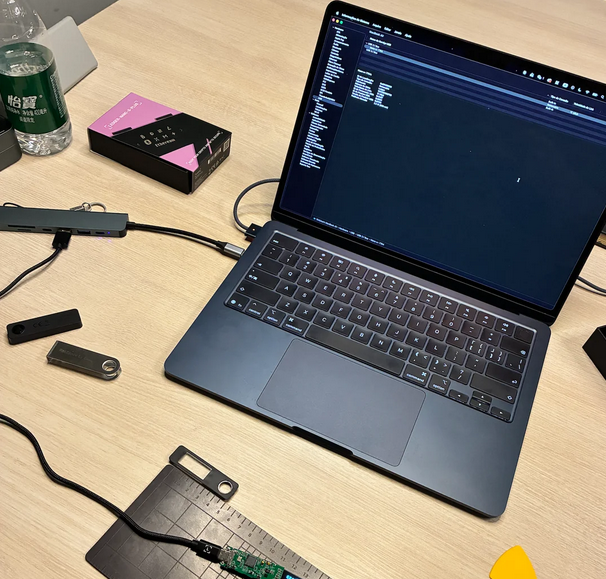
A Brazilian security researcher has warned others of the latest counterfeit Ledger device scam aimed at stealing users’ crypto.
Posting as “Past_Computer2901” on the “ledgerwallet” Reddit channel on Thursday, the security researcher said they purchased what they thought was a legitimate Ledger device for personal use, but soon realized after it arrived that it was a sophisticated counterfeit aimed at stealing user funds.
“This isn’t meant to cause panic, but rather to serve as a serious warning — I’m honestly still a bit shaken by the sheer scale of this operation,” they said.
Scammers are adopting increasingly sophisticated strategies to target users opting for self-custody, from supply chain attacks to social engineering and approval scams.
Earlier this month, more than 50 victims were tricked into revealing their seed phrases on a fake Ledger Live app that made its way to the Apple App Store via a bait-and-switch strategy. The victims lost a combined $9.5 million before Apple took down the malicious app.
How the counterfeit Ledger device scam works
The researcher said he bought the Ledger Nano S Plus from a Chinese marketplace, which was priced the same as the official Ledger store. The packaging and the listing also appeared legitimate at first.
However, when they connected the device to the genuine Ledger Live app — which was luckily already installed on their computer — it failed Ledger’s built-in “Genuine Check.”
This prompted them to pull apart the device, discovering modified hardware and firmware designed to capture and expose sensitive wallet data.
The security researcher said the scammers target first-time Ledger users, as the QR code that comes in the box would normally direct users to download a malicious version of the Ledger Live app that would show a fake “Genuine Check.”
Users continuing to follow the prompts will eventually allow scammers to obtain a user’s seed phrases and drain funds at any time.

“Stay safe out there. Only download Ledger Live from ledger.com. Only buy hardware from ledger.com,” the security researcher said.
“If your device fails the Genuine Check — stop using it immediately.”
After pulling apart the device, they discovered clear signs of tampering, including scraped chip markings and a WiFi and Bluetooth antenna embedded inside the unit.
Legitimate Ledger hardware products are designed to keep private keys fully offline.
Related: Musician loses $420K Bitcoin ‘retirement fund’ via fake Ledger app
The security researcher then looked into the firmware, putting the “chip into boot mode,” which initially identified the device as a Nano S Plus 7704 with an attached serial number.
However, once the boot sequence completed, another manufacturer’s name showed up: Espressif Systems, a publicly listed Chinese semiconductor company based in Shanghai.
Cointelegraph reached out to Espressif for comment but didn’t receive an immediate response.
Magazine: What’s a ‘Network State’ and are there real-life examples? Big Questions
Crypto World
Australian Dollar Pulls Back from Highs on Weaker Data

The Australian dollar is undergoing a corrective decline after reaching recent highs, with the current move driven by market reaction to newly released macroeconomic data. Earlier gains in AUD were supported by improving global risk sentiment and steady demand for commodity-linked currencies. However, weaker labour market figures have prompted a reassessment of expectations and triggered profit-taking.
Employment data published yesterday pointed to a slowdown in growth, raising concerns about the durability of the economic recovery. Although full-time employment increased, overall job growth came in below forecasts, while the unemployment rate showed little change. Together, these factors weighed on the Australian dollar and led to a reassessment of its short-term outlook following the prior rally.
Toward the end of the week, market participants will focus on upcoming macroeconomic releases, including data on economic activity, central bank commentary, and commodity market statistics. These factors may reshape expectations and influence the direction of commodity currencies.
AUD/USD
After reaching a yearly high near 0.7180, AUD/USD has pulled back, forming a “Bearish Harami” reversal pattern. A bearish close in the current session could increase the likelihood of a deeper correction towards 0.7100–0.7120.
At the same time, a renewed break above the recent high would signal continued bullish momentum and a return of buyers to the market.
Key events for AUD/USD:
- today at 13:00 (GMT+3): International Monetary Fund meetings;
- today at 18:30 (GMT+3): speech by FOMC member Mary Daly;
- today at 22:30 (GMT+3): CFTC net speculative positions on AUD.

AUD/CAD
AUD/CAD is also moving lower, reflecting both weakness in the Australian dollar and relative resilience of the Canadian currency. Commodity market dynamics remain an additional driver, with energy prices and global demand expectations continuing to play a key role.
Technical analysis suggests the potential for a correction towards 0.9730–0.9760, as a “Dark Cloud Cover” reversal pattern has formed on the daily timeframe. A retest of recent highs will help assess the strength of demand and the likelihood of a renewed uptrend.
Key events for AUD/CAD:
- today at 15:30 (GMT+3): Canadian housing starts;
- today at 15:30 (GMT+3): foreign investment in Canadian securities;
- today at 20:00 (GMT+3): Baker Hughes rig count.
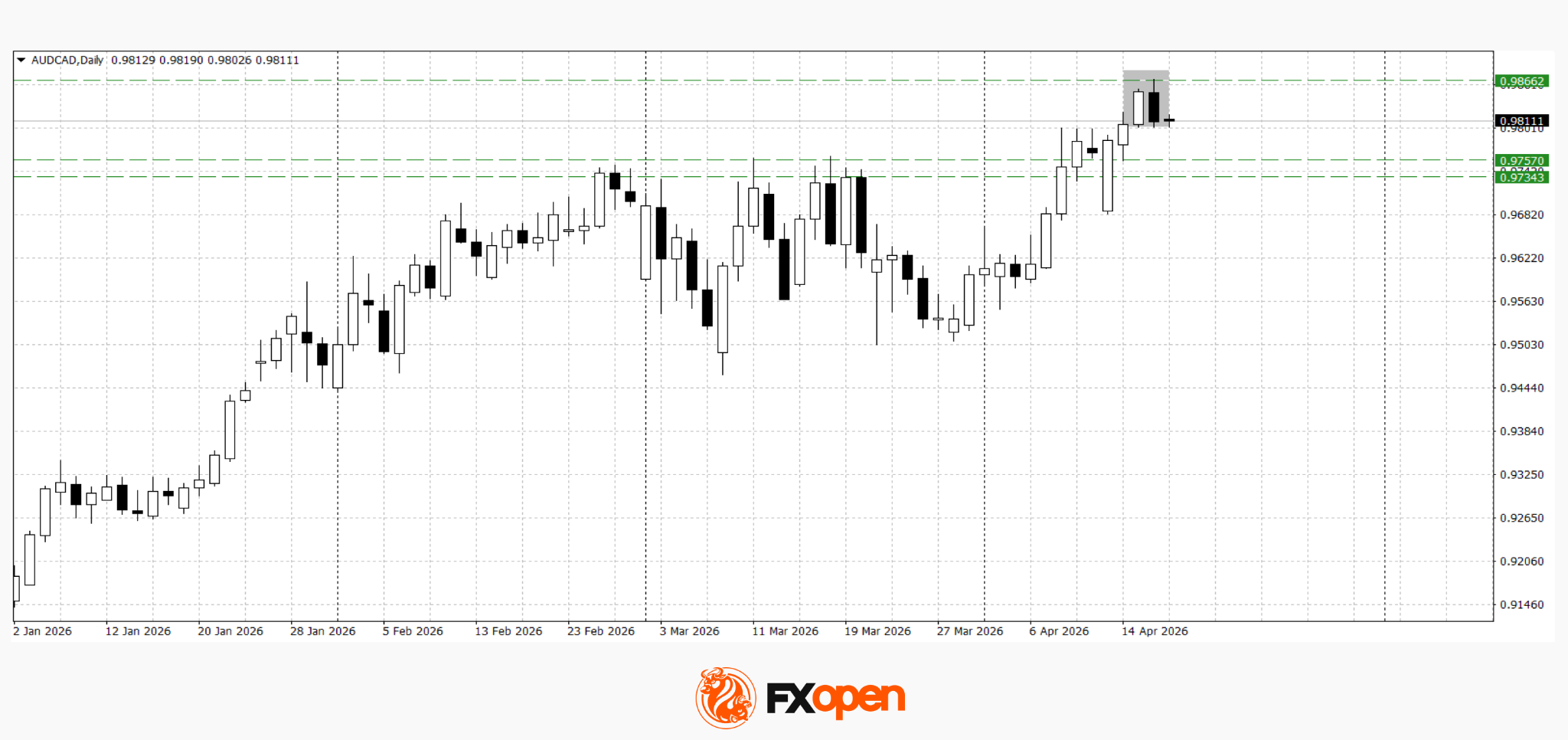
The current pullback in the Australian dollar follows weaker labour market data after a period of steady gains. If downward pressure persists, the correction may deepen. However, stabilisation in the external environment and supportive incoming data could allow the broader upward trend to resume.
Trade over 50 forex markets 24 hours a day with FXOpen. Take advantage of low commissions, deep liquidity, and spreads from 0.0 pips (additional fees may apply). Open your FXOpen account now or learn more about trading forex with FXOpen.
This article represents the opinion of the Companies operating under the FXOpen brand only. It is not to be construed as an offer, solicitation, or recommendation with respect to products and services provided by the Companies operating under the FXOpen brand, nor is it to be considered financial advice.
Crypto World
US Government Moves Over $606,000 Bitfinex Hack Bitcoin to Coinbase Prime


The US government transferred approximately 8.2 Bitcoins (BTC), worth roughly $606,000, to Coinbase Prime.
The transfer was tied to the 2016 Bitfinex hack seizure, according to on-chain data flagged by Arkham Intelligence.
Why These Bitcoins Are Unlikely to Hit the Market
The wallet executed two back-to-back outflows, splitting the move into a 7.999 BTC transaction and a smaller 0.197 BTC deposit routed to the same Coinbase Prime address.
Follow us on X to get the latest news as it happens
Exchange-bound transfers often spark speculation of an imminent liquidation. However, these specific coins are legally committed elsewhere.
A federal court approved the return of approximately 94,643 BTC to Bitfinex through restitution agreements in early 2025. The ruling established Bitfinex as the sole victim entitled to recovery.
Thursday’s outflow follows earlier 2026 transfers from the federal wallet on March 3 and April 10. US government wallets currently hold 328,361 Bitcoin worth roughly $24 billion as of April 2026, according to Arkham data. The latest transfer equals over 0.0024% of the stash.
Ilya Lichtenstein executed 2,000 fraudulent transactions to steal 119,754 BTC from Bitfinex in 2016. He received a 5-year prison sentence in November 2024.
Lichtenstein and his wife, Heather Morgan, pleaded guilty to conspiracy to commit money laundering in August 2023. He earned early release in January 2026 under the First Step Act.
The post US Government Moves Over $606,000 Bitfinex Hack Bitcoin to Coinbase Prime appeared first on BeInCrypto.
Crypto World
Ethereum Price Prediction: The Chain That Never Sleeps

Ethereum price, just like any other major alt, is hovering and holding the bullish prediction. The network also reminds us that ETH has never once stopped producing blocks.
At BUIDL Asia 2026, Ethereum Foundation researcher Luca Zanolini confirmed a roadmap target to reduce transaction finality to under one minute. Meanwhile, the long-to-short ratio sits at 1.54, a quiet signal that smart money is accumulating while retail hesitates.
Zanolini’s remarks, delivered April 17 at the Sofitel Ambassador Seoul, cut to the heart of Ethereum’s design philosophy.
“Ethereum was designed to keep producing blocks even if participation drops,” he said. “The next challenge is to preserve that feature while reducing transaction finality to less than one minute.”
In 2023, Ethereum kept producing blocks uninterrupted even after client errors knocked more than half of all validators offline. The finality improvement carries a 2029–2030 implementation target, and the fundamental thesis is getting reinforced.
Discover: The best pre-launch token sales
Ethereum Price Prediction: $2,420 the Target
ETH has traded in a tight bullish range between $2,285 and $2,360 over the past 24 hours, with 24-hour trading volume exceeding $18 billion. This figure reflects active participation at these levels, without liquidity drifting lower. The funding rate is essentially neutral at 0.0001%, suggesting no extreme leverage in either direction.

The critical support zone is $2,250. As long as ETH holds above that floor, the technical structure favors a push toward $2,420 resistance. A clean break above $2,420 opens the path to $2,870, a level that would approach territory last seen before the drawdown from ETH’s all-time high of $4,950. That’s still a 52% discount from peak. The upside, in percentage terms, remains substantial.
Open interest dynamics suggest the market is coiled with a sharp move in either direction plausible. The 1.54 long-to-short ratio implies directional conviction from larger players, but conviction alone doesn’t override macro headwinds. Watch the $2,250 level closely.
Discover: The best crypto to diversify your portfolio with
LiquidChain to Fix What ETH Can’t?
ETH may be the chain that never sleeps, but it also carries the weight of a $280B market cap. Meaningful upside from here requires macro tailwinds, a breakout above multi-week resistance, and sustained institutional demand. That’s a crowded list of conditions.
The make-or-break levels are tightening, and for traders sizing positions accordingly, the risk/reward at $2,330 is narrower than it was 5 years ago. Early-stage infrastructure plays offer a different equation entirely.
LiquidChain ($LIQUID) is a Layer 3 infrastructure project built around a single, operationally direct thesis: fuse Bitcoin, Ethereum, and Solana liquidity into one execution environment. The cross-chain fragmentation problem is real and expensive, and LiquidChain’s Unified Liquidity Layer targets it directly, with Single-Step Execution and Deploy-Once Architecture allowing developers to access all three ecosystems without redeployment overhead.
The presale is currently priced at $0.0145, with $675K raised to date, and not to forget the huge but limited 1600% APY staking for early buyers. Verifiable Settlement adds an institutional-grade accountability layer that early L3 competitors have largely ignored.
For those already positioned in ETH and watching this level with caution, it may be worth taking a closer look: research LiquidChain here.
The post Ethereum Price Prediction: The Chain That Never Sleeps appeared first on Cryptonews.
Crypto World
Mitsui & Co.’s Crypto Arm Brings Tokenized Metals Asset Zipangcoin to OP Mainnet


The shift to Optimism is ZPG’s first deployment on a public blockchain since launching in 2022, and the start of its global rollout.
Mitsui & Co. Digital Commodities (MDC), a subsidiary of Japanese trading giant Mitsui & Co., Ltd., its tokenized gold, silver, and platinum asset, Zipangcoin (ZPG), on Optimism’s Ethereum Layer 2, OP Mainnet, according to a press release shared with The Defiant.
ZPG has been issued under Japan’s regulatory framework since 2022 and currently runs on Miyabi, a proprietary private blockchain developed by longtime crypto exchange bitFlyer.
The OP Mainnet deployment marks the first time the asset will be issued in a public blockchain ecosystem. Per the release, Japanese CEX GMO Coin will list ZPG on April 20.
MDC’s parent, Mitsui & Co., is a Fortune Global 500 conglomerate with a market cap of over $94 billion, and Berkshire Hathaway as its largest shareholder, the release notes.
MDC also stated in the release that the choice of OP Mainnet follows deliberate due diligence, highlighting that OP Stack chains processed over 6 billion transactions in 2025 — 29x growth in two years.
According to DefiLlama, OP Mainnet currently has a total value locked in DeFi of over $393 million, making it the 17th largest chain in DeFi by TVL. The chain’s stablecoin market cap is approaching $579 million, and $30-day DEX volume is over $623 million.
Sho Miichi, MDC’s representative director & president, was quoted in the release saying: “We are pleased to partner with Optimism to bring a high-quality, commodity-linked digital asset from Japan to investors worldwide.”
Kyle Jenke, chief business officer at OP Labs, described Japan’s regulatory clarity as “one of the most compelling markets for on-chain finance,” adding:
“Zipangcoin is a commodity-backed cryptoasset issued by Mitsui & Co. Digital Commodities and will be the first cryptoasset issued by a Japanese company to launch on OP Mainnet.”
The ZPG launch on Optimism fits into a broader wave of institutional-grade assets moving on-chain.
On-chain tokenized RWAs tripled to roughly $18.6 billion over the course of 2025, with analysts projecting the market could reach $2 trillion by 2030.
Earlier this year, ether.fi migrated its crypto neobank — with $5.7 billion in TVL and around 50,000 active cards — from Scroll to OP Mainnet to access enterprise-grade payment infrastructure.
Tokenized precious metals trading has surged in recent months across both centralized and decentralized platforms. Earlier this week, decentralized perpetual exchange GMX launched 24/7 gold and silver markets on L2 Arbitrum, recording more than $10 million in trades on the first day.
This article was written with the assistance of AI workflows. All our stories are curated, edited and fact-checked by a human.
Crypto World
Bitcoin’s (BTC) Quantum Defense Plan Could Lock Away 1.7M BTC Forever

Key Takeaways
- Charles Hoskinson, founder of Cardano, claims Bitcoin’s BIP-361 quantum protection measure is misleadingly classified as a soft fork when it actually demands a hard fork.
- The BIP-361 framework suggests locking quantum-susceptible Bitcoin wallets and mandating users transition to quantum-resistant addresses.
- BIP-361’s zero-knowledge proof recovery mechanism fails to assist holders of approximately 1.7 million Bitcoin generated before 2013 seed phrase protocols were standardized.
- Roughly 1.1 million of these coins are attributed to Bitcoin creator Satoshi Nakamoto and would face permanent lockdown if the measure is implemented.
- Data reveals that by March 1, 2026, over 34% of circulating Bitcoin features exposed public keys susceptible to quantum computing threats.
Cardano’s creator Charles Hoskinson has openly challenged Bitcoin’s planned quantum computing countermeasure, claiming it carries a misleading technical classification and offers no safeguard for the network’s earliest holdings.
The measure under scrutiny is BIP-361, jointly developed by Bitcoin core developer Jameson Lopp alongside other contributors. The proposal seeks to eliminate Bitcoin addresses exposed to quantum computer vulnerabilities by locking those holdings and requiring users to transfer to more secure addresses.
During a livestream broadcast this week, Hoskinson referenced statistics indicating that by March 1, 2026, more than 34% of circulating Bitcoin will have public keys exposed on the blockchain. This represents approximately 8 million Bitcoin vulnerable to attack from advanced quantum computing systems.
BIP-361 incorporates a zero-knowledge proof recovery framework designed to enable holders with standard wallet seed phrases to verify ownership and retrieve frozen assets following migration.
However, Hoskinson contends this recovery mechanism fails for roughly 1.7 million Bitcoin stored in wallets created before the BIP-39 seed phrase protocol gained widespread adoption around 2013.
These legacy wallets utilized an alternative key generation approach from Bitcoin’s original client software. They depended on local key pools instead of recoverable seed phrases. Without seed phrase access, constructing the zero-knowledge proof necessary for coin retrieval becomes impossible.
“1.7 million coins can’t do that. It’s not possible. 1.1 million of which belong to Satoshi,” Hoskinson stated.
The Hard Fork Controversy
Beyond recovery limitations, Hoskinson contested BIP-361’s classification. He argued the proposal presents itself as a soft fork while functionally demanding a hard fork due to its invalidation of existing signature schemes that remain actively deployed.
“To actually do this, you need a hard fork,” Hoskinson explained. Bitcoin has never implemented a hard fork, and its development community has traditionally resisted such changes.
Lopp, one of the proposal’s co-authors, admitted on X this week that he personally dislikes the plan and characterized it as “a rough idea for a contingency plan” instead of a finalized specification.
Lopp has maintained that freezing inactive coins—which he calculates at 5.6 million Bitcoin—would be more favorable than allowing future quantum attackers to recover and liquidate them in markets.
Governance Structure and Institutional Influence
Hoskinson additionally contended that Bitcoin’s absence of formal on-chain governance infrastructure leaves it without clear procedures for resolving such critical decisions. He cited Cardano, Polkadot, and Tezos as blockchain networks equipped with structured governance frameworks capable of addressing similar matters through community-driven voting mechanisms.
He predicted that major institutional stakeholders, including asset management firms that have accumulated substantial Bitcoin positions in recent years, will ultimately force Bitcoin developers to implement changes despite potential community opposition.
Should BIP-361 be adopted in its present formulation, the approximately 1.7 million pre-2013 coins would become irreversibly frozen without any recovery mechanism available.
Crypto World
Bitcoin (BTC) has a perfect bottom indicator. It’s not flashing yet.

Here is something worth noting about bitcoin . Beneath all the noise from daily price swings, X posts and macro headlines, there is a remarkably simple indicator that has quietly called every major market bottom since 2015. Not once, but every single time.
To the dismay of bulls, it hasn’t fired yet, suggesting the broader bear market may not be over, and the recent bounce to $75,000 from $65,000 could be a temporary recovery.
The indicator
It involves two lines on the price chart. That’s it, no complex formula, analysis of blockchain data needed.
These two lines represent bitcoin’s average price over the past 50 and 100 weeks. They act as simple moving averages, showing near-term and long-term trends in bitcoin’s price.

Most of the time, the 50-week average is above the 100-week line. That’s the natural state for markets that trend upward over time, as is the case with bitcoin.
But occasionally, during periods of peak fear, when selling is relentless, and sentiment has collapsed, the 50-week average falls below the 100-week average. This crossover is known as a bear market signal.
It has occurred three times in bitcoin’s history. Each time, it has coincided with the end of a bear market, marking major price bottoms that have not been revisited since.
In other words, it’s been a contrary indicator, ironically marking bottoms rather than deeper downturns.
Three times, three bottoms
Look at the vertical lines on the chart going back to 2015. These mark the three bearish crossovers – April 2015, February 2019, and September 2022. Each one occurred near the bottoming phase, not precisely at the lowest point, but within the same range.
In 2015, BTC was written off as a failed experiment. Then the crossover happened. BTC subsequently rallied from $200 to nearly $20,000 by the end of 2017. A similar pattern played out after the early 2019 crossover.
The 2022 crypto winter, characterized by several bankruptcies and scams, shattered investor confidence. The downtrend, however, ran out of steam after the crossover happened in September. BTC bottomed out in the final months and later chalked out a rally to $126,000 by October 20205.
Each of these bull runs delivered returns far exceeding those of equities and other major asset classes.
What is it saying now?
As of April 17, the crossover has not happened.
Bitcoin has declined sharply from its October record high of over $126,000 to around $75,000, briefly reaching $60,000 in early February. As a result, the two averages are moving closer together, but the 50-week average still holds above the 100-week average.
The takeaway: If history is any guide, the broader bear market may still be intact and could worsen before finding a bottom. It also means that the recent bounce toward $75,000 is likely a temporary recovery rather than the start of a full-fledged bull market.
That said, historical patterns are just that – patterns – and they do not guarantee future outcomes. If U.S. equities, already at record highs, continue to advance, institutional demand for Bitcoin ETFs could strengthen, potentially supporting a price rally.
Crypto World
Why BIP-361 Can’t Rescue Satoshi’s Bitcoin, According to Charles Hoskinson


Cardano (ADA) founder Charles Hoskinson argues BIP-361’s zero-knowledge recovery mechanism cannot rescue roughly 1.7 million Bitcoin (BTC) locked in pre-2013 addresses. This includes roughly 1.1 million Bitcoins attributed to Satoshi Nakamoto.
Casa co-founder Jameson Lopp and five co-authors submitted the Bitcoin Improvement Proposal (BIP-361). It seeks to sunset legacy ECDSA/Schnorr signatures, rendering funds on those addresses unspendable.
Hoskinson Flags Fatal Gap in Bitcoin’s Quantum Plan
Estimates indicate that over 34% of Bitcoin is held in addresses potentially vulnerable to future quantum threats, prompting renewed focus on mitigation efforts. The BIP-361 proposal seeks to address the vulnerability.
The draft phases out legacy Bitcoin signatures in three stages. Phase A blocks new sends to vulnerable addresses. In Phase B, nodes would reject all transactions that rely on ECDSA and Schnorr signatures
Phase C, pending further research, would let holders recover frozen coins. They would submit a zero-knowledge proof of possession of a BIP-39 seed phrase. However, concerns remain over the feasibility of such recovery. In a recent video, Hoskinson stated that,
“1.7 million coins can’t do that. It’s not possible. 1.1 million of which belong to Satoshi.”
Subscribe to our YouTube channel to watch leaders and journalists provide expert insights
He explained that these coins originate from Bitcoin’s early architecture, which predates modern standards like BIP-39 seed phrases and hierarchical deterministic key generation.
As a result, they fall outside the assumptions required for zero-knowledge-based recovery systems, limiting the effectiveness of proposals like BIP-361 for older holdings.
“if you build a ZK system based upon proof of a statement, your bit 39 key, say I have these things, you can recover some of the 8 million Bitcoin, but 1.7 million are on not under this scheme. All of the 2013 Bitcoin and before,” he added.
The limitation is acknowledged in BIP-361 itself, which concedes it is “not possible to construct a proof of HD wallet ownership for UTXOs created before BIP-32 existed.”
“Phase C is also compatible with an ‘Hourglass’ style BIP for spending P2PK encumbered funds, provided such a BIP has activated by the time Phase C activates,” the draft reads.
Hoskinson also disputes the soft-fork classification. He says the plan would require a hard fork. The BIP-361 text acknowledges that consensus rules may eventually need to loosen.
“After Phase B, both senders and receivers will require upgraded wallets. Phase C, if activated in conjunction with Phase B, may be soft forkable, otherwise it would likely require a loosening of consensus rules (a hard fork) to allow vulnerable funds to be recovered,” the authors wrote.
Notably, Lopp acknowledged the discomfort with the proposal, stating that he does not like it himself but considers the alternative even less acceptable.
Follow us on X to get the latest news as it happens
The post Why BIP-361 Can’t Rescue Satoshi’s Bitcoin, According to Charles Hoskinson appeared first on BeInCrypto.
-

 Politics7 days ago
Politics7 days agoUS brings back mandatory military draft registration
-

 Sports7 days ago
Sports7 days agoMan United discover Nico Schlotterbeck transfer fee as defender reaches Dortmund agreement
-

 Fashion7 days ago
Fashion7 days agoWeekend Open Thread: Veronica Beard
-

 Politics5 days ago
Politics5 days agoWorld Cup exit makes Italy enter crisis mode
-

 Business7 days ago
Business7 days agoTesla Model Y Tops China Auto Sales in March 2026 With 39,827 Registrations, Beating Cheaper EVs and Gas Cars
-

 Crypto World4 days ago
Crypto World4 days agoThe SEC Conditionalises DeFi Platforms to Be Avoided for Broker Registration
-

 Crypto World3 days ago
Crypto World3 days agoSEC Signals Exemption for Crypto Interfaces From Broker Registration
-

 News Videos2 days ago
News Videos2 days agoSecure crypto trading starts with an FIU-registered
-

 NewsBeat4 days ago
NewsBeat4 days agoPep Guardiola and Gary Neville agree over Arsenal title problem that benefits Man City
-

 Business6 days ago
Business6 days agoIreland Fuel Protests Enter Day 5 as Blockades Spark Shortages and Government Prepares Support Package
-

 Business7 days ago
Business7 days agoOpenAI Halts Stargate UK Data Centre Project Over Energy Costs and Copyright Row
-

 Crypto World6 days ago
Crypto World6 days agoFederal judge blocks Arizona from bringing criminal charges against Kalshi
-

 NewsBeat3 days ago
NewsBeat3 days agoTrump and Pope Leo: Behind their disagreement over Iran war
-
 Crypto World3 days ago
Crypto World3 days agoSEC Proposes Certain Crypto Interfaces Don’t Need to Register as Brokers
-

 NewsBeat5 days ago
NewsBeat5 days agoJD Vance announces ‘no agreement’ with Iran over nuclear weapons fear
-
 Business6 days ago
Business6 days agoIMF retains floor for precautionary balances at SDR 20 billion
-

 Business6 days ago
Business6 days agoFormer Liverpool CEO eviscerates FIFA for World Cup ticket pricing
-

 Crypto World4 days ago
Crypto World4 days agoSei Network Enters Quiet Reset Phase as On-Chain Metrics Signal a Slowdown in 2026
-
Business6 days ago
Coreweave CSO Venturo sells $5.5m in class a common stock
-
Sports6 days ago
1st-Round WR Enters Vikings Mock Draft Orbit


 ⟁
⟁









You must be logged in to post a comment Login