Crypto World
Quantum Computing Crypto: Act Now, Coinbase Warns


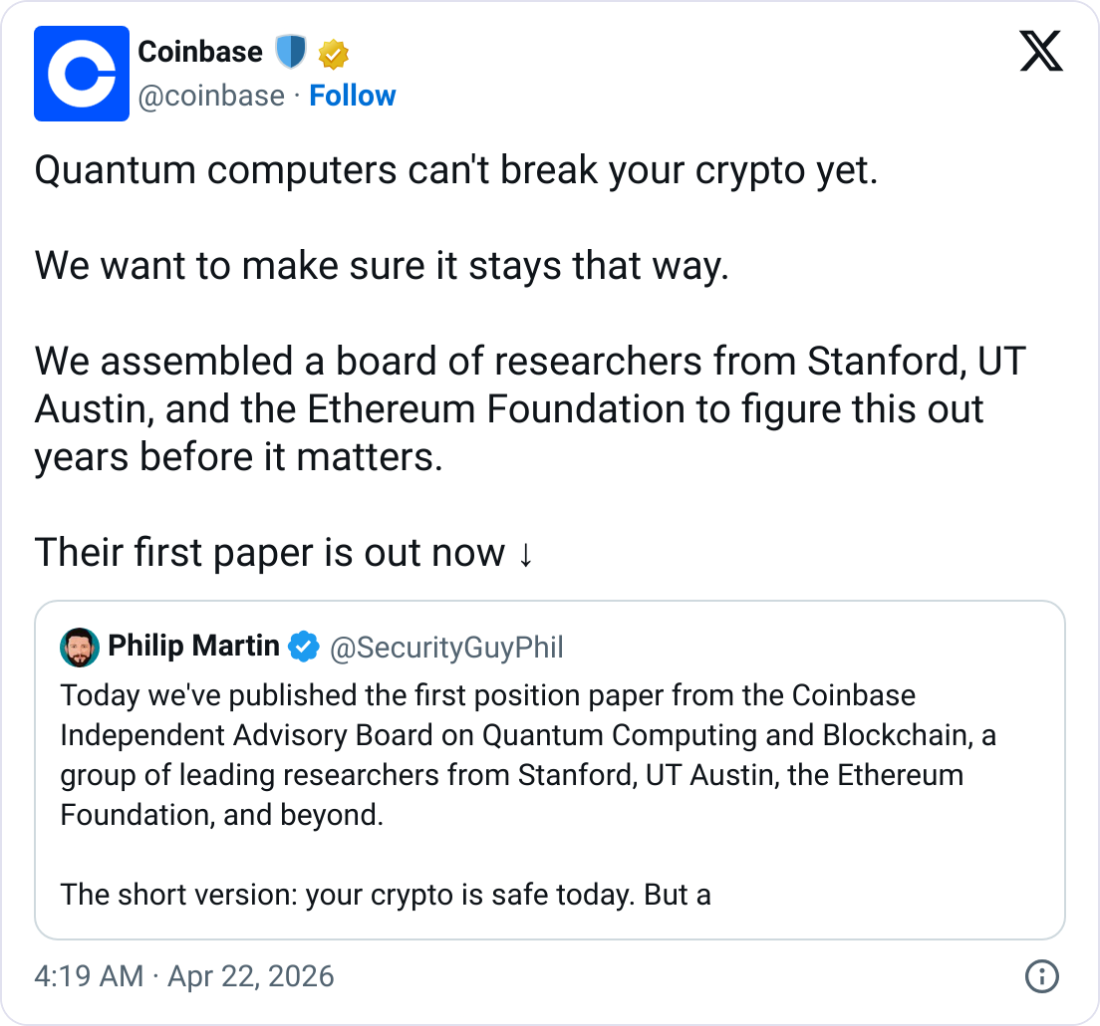
A 50 page quantum computing crypto risk assessment published Tuesday by Coinbase’s independent advisory board concludes that while today’s blockchains remain secure, a fault-tolerant quantum computer capable of breaking widely used encryption is increasingly plausible and that preparation must begin now, warning that “waiting for it to be urgent is not a good idea.”
Summary
- The 50 page paper, authored by an independent board including Stanford cryptographer Dan Boneh, Ethereum Foundation researcher Justin Drake, and EigenLayer founder Sreeram Kannan.
- Replacing today’s signatures with quantum-resistant alternatives could expand blockchain data sizes by up to 38 times, according to one estimate in the report, meaning the transition carries significant engineering costs and performance tradeoffs.
- Bitcoin wallets that have already revealed their public keys are identified as the most immediately vulnerable category of holdings in any future quantum attack scenario.
Quantum computing crypto risk has its most authoritative industry assessment yet. The Coinbase advisory board, a group of world-class cryptographers and blockchain researchers convened by Coinbase in January 2026, released its first major position paper Tuesday: a 50 page analysis of how future quantum computers could affect blockchain security and what the industry must do before that threat becomes real.
“Waiting for it to be urgent is not a good idea,” the paper states, emphasizing that transitions across blockchains, wallets, and exchanges could take years to execute safely even after all the technical standards are in place.
The board members who authored the paper include Dan Boneh, the director of the Stanford Center for Blockchain Research; Justin Drake of the Ethereum Foundation; Sreeram Kannan, the founder of EigenLayer; Yehuda Lindell, Coinbase’s head of cryptography; and Dahlia Malkhi, an expert in resilient distributed systems. Their institutional breadth gives the paper a credibility that no single-company security assessment would carry.
What the Report Found and What Makes It Credible
The paper’s core conclusion is carefully calibrated: quantum computers today cannot crack the cryptography underpinning Bitcoin, Ethereum, or any major blockchain. Breaking standard encryption would require fault-tolerant quantum machines with vastly more error-corrected qubits than current hardware provides, and achieving that is still considered a major engineering challenge. The report does not predict when that will happen. It argues that the timeline uncertainty itself is the problem.
The threat the paper focuses on most is the harvest now, decrypt later attack: adversaries can collect encrypted blockchain data today and store it, waiting for quantum hardware to mature enough to crack it retroactively. For long-held assets, this is a material risk that begins now rather than when the quantum threat becomes practical. Bitcoin addresses that have already revealed their public keys on-chain are specifically identified as the most immediately exposed category of holdings.
Why the Transition Will Be Harder Than It Sounds
The technical solution to quantum vulnerability already exists: NIST has standardized post-quantum cryptographic algorithms that are mathematically resistant to quantum attacks. The problem is implementation at blockchain scale. Post-quantum digital signatures can be tens to hundreds of times larger than the signatures in use today. One estimate in the Coinbase report suggests that replacing current signatures with quantum-proof alternatives could expand block sizes by up to 38 times.
For a network like Bitcoin, which processes blocks under a strict size limit and where any upgrade requires consensus among a decentralized set of stakeholders with no central authority, a 38-times expansion of signature data is not a parameter adjustment. It is a fundamental architectural change that touches every node, wallet, exchange, and application in the ecosystem. The debate among Bitcoin developers, already underway, reflects exactly this tension between urgency and the cost of change.
What Crypto Networks Are Already Doing
The Coinbase report arrives alongside parallel actions across the ecosystem. Ripple published a four phase XRPL post-quantum roadmap targeting completion by 2028. The Ethereum Foundation has elevated post-quantum security to a top strategic priority with a dedicated research team. Bitcoin developers are actively debating BIP 361, a proposal for a structured migration away from legacy address types that expose public keys.
For the Bitcoin quantum risk assessment specifically, researchers estimate approximately 4.5 million Bitcoin held in early or reused addresses may be exposed to future quantum attacks. The quantum threat debate in Bitcoin has become one of the most contested governance questions in the community, precisely because the solutions require either forcing coin migration or accepting that some portion of the supply may eventually be at risk.
Crypto World
U.S. military commander flags Bitcoin’s cybersecurity role in Senate hearing


A senior U.S. military commander has described Bitcoin as a cybersecurity tool with potential use in national defense.
Summary
- A U.S. military commander said Bitcoin can function as a cybersecurity tool, noting its proof-of-work design raises the cost for potential attackers.
- Lawmakers examined Bitcoin’s role in national security during a Senate hearing focused on Indo-Pacific threats and cyber risks from state-linked actors.
At a Senate Armed Services Committee hearing on Tuesday, Samuel Paparo said Bitcoin’s role goes beyond financial use cases and can support security systems tied to U.S. strategic interests.
“It is a valuable computer science tool, as a power projection,” Paparo said, adding that the network’s proof of work design “imposes more cost” on attackers attempting to interfere with it.
“Outside of the economic formulation of it, it has got really important computer science applications for cybersecurity.”
The hearing focused on the U.S. military’s posture in the Indo-Pacific, with discussions spanning ongoing conflicts in Ukraine and the Middle East, China’s military activity, and threats linked to North Korea.
Paparo’s remarks follow earlier comments from Jason Lowery, who has argued that proof-of-work networks can be used to secure digital systems in a cyber conflict. He said Bitcoin is often seen only as a monetary system, while its design can also secure “all forms of data, messages, or command signals.”
State-linked cyber operations have increased in recent years, with attacks such as ransomware, phishing, and denial of service targeting infrastructure and financial systems. The Lazarus Group remains one of the most prominent examples, having stolen billions in crypto over the past decade, funds that U.S. officials say have supported North Korea’s nuclear program.
Paparo’s comments came after Tommy Tuberville asked how the U.S. could lead in Bitcoin-related competition, noting that Chinese policy groups are also examining the asset as a strategic tool. Paparo did not directly address policy steps but pointed to Bitcoin’s underlying structure.
“Bitcoin is a reality. It is a peer to peer zero trust transfer of value. Anything that supports all instruments of national power for the United States of America is to the good,” he said.
Concern over reliance on foreign-made mining hardware has also drawn attention in Washington, even as the U.S. holds the largest Bitcoin reserves among nation states and a significant share of global hashrate.
Last month, Bill Cassidy and Cynthia Lummis introduced the Mined in America Act, aimed at expanding domestic production of Bitcoin mining equipment. The proposal also seeks to formalize the Strategic Bitcoin Reserve established under an executive order signed by Donald Trump.
Crypto World
Kelp Exploiter Moves $175M of Stolen Funds: Arkham
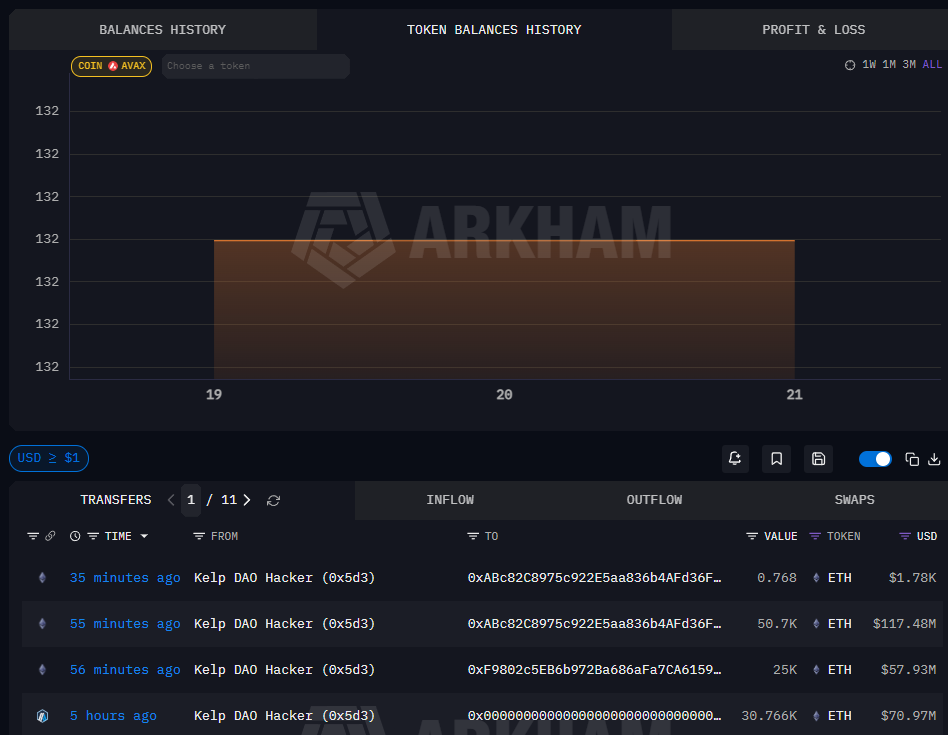
The attacker behind the roughly $290 million Kelp DAO exploit began moving tens of thousands of Ether to newly created blockchain addresses on Tuesday, in what appears to be an effort to start laundering the stolen funds.
The wallet tagged by Arkham as linked to the Kelp DAO exploit moved about 75,700 Ether (ETH) worth roughly $175 million across three transactions on Tuesday, including a 25,000 ETH transfer to one newly created address and transfers of 50,700 ETH and 0.7 ETH to another.
Blockchain investigator ZachXBT wrote in a Tuesday Telegram post that addresses tied to the exploit had begun moving funds through THORChain and Umbra. He flagged three THORChain transactions totaling about $1.5 million and a separate $78,000 transfer through Umbra.
On Saturday, an attacker drained about 116,500 restaked Ether (rsETH), worth roughly $290 million to $293 million at the time, from Kelp DAO’s LayerZero-powered rsETH bridge.
LayerZero said Kelp DAO’s 1/1 decentralized verifier network (DVN) setup created a single point of failure by relying on a single verifier path for cross-chain messages. LayerZero said it had previously advised against that configuration.
Fallout spreads across DeFi
The transfers came hours after Arbitrum said its 12-member security council had taken emergency action to freeze 30,766 ETH tied to the exploit and move the funds into an “intermediary frozen wallet” accessible only through Arbitrum governance.

The exploit also hit other DeFi protocols, including Aave, where the attacker used the stolen funds as collateral to borrow against the protocol. Early estimates put the hole at about $195 million, but Aave’s Monday incident report later outlined two potential outcomes: roughly $123.7 million in bad debt under one scenario and about $230.1 million under another.
The transfers suggest the attackers had begun moving funds through non-custodial protocols that can complicate tracing and recovery. THORChain does not require traditional Know Your Customer checks.
During the $1.4 billion Bybit hack in 2025, attackers converted about 83% of the stolen Ether into Bitcoin (BTC), with 72% of the funds moving through THORChain, according to Bybit CEO Ben Zhou. Zhou said at the time that 77% of the stolen funds were still traceable.
Related: ZachXBT asks MemeCore to explain valuation and token supply
Aave unfreezes Ethereum V3 market as borrow rates spike
On Tuesday, Aave said it had unfrozen Wrapped Ether (WETH) reserves on the Ethereum Core V3 market, enabling users to supply WETH to the V3 lending protocol once again. However, WETH reserves across Ethereum Prime, Arbitrum, Base, Mantle and Linea remain frozen.

Meanwhile, the thinning liquidity saw Aave’s borrowing rates for USDt (USDT) rise from 3% to 14%, marking the highest figures since December 2024, wrote Julio Moreno, the head of research at analytics platform CryptoQuant, in a Monday X post.
Fears over a potential contagion caused significant outflows from Aave, as its total value locked (TVL) fell by about $10 billion since the exploit to $16.4 billion as of Tuesday, DefiLlama data shows.
Magazine: 53 DeFi projects infiltrated, 50M NEO tokens could be ‘given back’: Asia Express
Crypto World
Canton, ZKsync Clash Over How Blockchains Enforce Rules

Banks are moving onchain through competing models that take different approaches to how financial rules are enforced.
On the one hand are blockchain-native builders like Matter Labs co-founder Alex Gluchowski, who argue that financial systems require rules to be enforced across all participants. On the other are networks built for institutions like Canton, which prioritize privacy, control and interoperability over global state.
Gluchowski is among the most vocal critics of the latter approach, arguing it reproduces the limitations of traditional finance in a new form. The core of the critique is whether rules can be enforced across an entire network. That’s not possible in systems like Canton, he claimed.
“But they are possible with blockchains — specifically with zero-knowledge systems anchored to public blockchains like Ethereum, which is an environment all parties can trust because it cannot be captured by any single corporate interest,” Gluchowski told Cointelegraph.
Crypto’s institutional adoption is bringing banks and financial institutions onchain, but it’s also splitting the industry along a deeper fault line than geography or regulation.

What counts as a blockchain?
Canton has gained traction by targeting privacy and regulatory requirements, connecting banks and asset managers through a network where transactions are shared only with relevant counterparties rather than broadcast system-wide. The network includes institutional participants such as JPMorgan and Goldman Sachs.
Whether Canton counts as a blockchain depends on how the term is defined and what properties it is expected to guarantee.
For Gluchowski, a blockchain’s core feature is a single shared ledger that allows rules to be enforced across all participants at once. He claimed Canton does not qualify. The network connects institutions through bilateral or trilateral relationships, where each party sees and verifies the transactions it is directly involved in.
“Before blockchains, banks had to enter bilateral relationships and define how they handle edge cases through contracts and API interactions,” Gluchowski said. “It’s just taking these existing relationships and workflows and putting them into a tokenized form.”
Gluchowski said Canton’s model limits what the system can guarantee. While participants can verify the transactions they are directly involved in, they cannot independently verify system-wide properties such as total asset supply or other rules that apply across all users. He added that those kinds of guarantees require a shared state that everyone can check.

Related: Privacy tools are rising behind institutional adoption, says ZKsync dev
“[Gluchowski] is correct that Canton does not have a global shared state, but he is incorrect in implying that this negatively affects Canton’s trust model,” Shaul Kfir, co-founder of Digital Asset, responded through a statement shared with Cointelegraph.
“In Canton, as in all other blockchains, I only trust my own validator and assume anyone else can be malicious. This ‘don’t trust, verify’ approach is very different from a distributed API system,” Kfir added.
In Canton’s model, trust does not come from a single system-wide view, but from each party independently checking the transactions it is involved in.
Network rules clash with issuer control
Following the conversation with Cointelegraph, Gluchowski took part in a live debate with another Digital Asset co-founder, Yuval Rooz. He reiterated his argument that financial rules must be enforced across an entire network in a blockchain network.
Rooz countered that system-wide enforcement doesn’t eliminate reliance on trusted parties, as public blockchain users still depend on token issuers. Rooz pointed to hacks that involved assets like USDC to argue that issuers remain the key enforcement mechanism.

Related: Instant settlement strains crypto’s capital efficiency: Ethan Buchman
“Actually, we would have been happier — as we’ve seen a lot of the crypto space saying if the centralized issuer were to intervene sooner rather than allowing these assets being traded and swapped into permissionless assets where then they can no longer interfere,” Rooz said.
“On Canton, no different than any other public chain, the issuer is centralized in real world assets, and they have different properties or similar properties to what they would have on public permissionless chains,” he added.
Gluchowski argued that issuance limits can be embedded directly into smart contracts. He said that on networks like Ethereum, activity beyond a certain threshold can be restricted or require additional approval, rather than relying solely on the issuer’s infrastructure.
“On Canton, you rely solely on the multisig. On Ethereum, you rely on smart contracts that are enforced by the network,” Gluchowski said.
“It’s just absolutely not true,” Rooz replied.
Kfir, whose statement was shared with Cointelegraph after the live debate, said that Gluchowski is “confusing the capabilities of Canton” with how it is used by centralized RWA issuers.
“When there’s a centralized RWA issuer, e.g. a stablecoin issuer, you’re already trusting them with the ‘mint’ function, and you’re trusting them and their auditors that the amount onchain is backed by reserves off-chain,” Kfir said.
Competing visions for bringing banks onchain
Canton and Matter Labs are competing to solve the same problem of how institutional finance moves onchain. Matter Labs, the developer of ZKsync, is targeting institutional use cases with Prividium, a model that keeps transactions private while anchoring verification to Ethereum through zero-knowledge proofs.
Kfir argued that systems like Prividium risk concentrating trust in a different place. In his view, users are no longer independently validating the relevant state, forcing them to reconcile their own records against what an operator reports happened onchain.
“ZKsync relies on Prividium operators who create ZKPs, but ZKsync’s own open source client doesn’t verify these proofs,” he said. “And even if a user does verify, it doesn’t verify which smart contract logic is running. The user is completely at the mercy of the Prividium operator.”

Rooz did concede one point during the debate, which is that Canton does not have public verifiability, while adding that there are plans to introduce it in the future.
For now, the divide remains unresolved. Canton is built around privacy and institutional control, while ZKsync’s Prividium attempts to preserve those features while anchoring verification to a public network. Both claim to offer a viable path for bringing banks onchain, but they are built on fundamentally different assumptions about how financial systems should work.
Magazine: Adam Back says current demand is ‘almost’ enough to send Bitcoin to $1M
Crypto World
Kalshi Eyes Crypto Perpetuals Launch, Positioning for Showdown With Coinbase (COIN)

Key Takeaways
- Kalshi is preparing to introduce perpetual futures contracts for cryptocurrency trading in the U.S. market
- The initial rollout will feature perpetuals linked to digital assets including Bitcoin
- The platform operates under CFTC regulatory oversight and secured recent authorization for margin trading capabilities
- This expansion creates intensified rivalry with established players like Coinbase, Crypto.com, and Gemini
- Competing prediction platform Polymarket has similarly disclosed intentions to enter the perpetual futures arena
Kalshi, primarily recognized for its prediction market operations, is gearing up to introduce perpetual futures trading for cryptocurrencies within U.S. borders. According to a report from The Information, sources with knowledge of the initiative have confirmed the development.
https://twitter.com/CoinMarketCap/status/2046633854945902850?s=20
The platform intends to begin its offering with perpetual futures contracts connected to major cryptocurrencies such as Bitcoin. These derivative instruments enable market participants to take positions on price movements without directly purchasing the underlying digital assets, and they feature no set expiration timeline.
Differing from conventional futures contracts, perpetual futures can remain open indefinitely provided the trader maintains adequate collateral backing. The mechanism keeps contract prices aligned with spot market values through periodic transfers between long and short position holders, commonly referred to as funding rate mechanisms.
Perpetual futures contracts have dominated trading activity on international crypto platforms for numerous years. BitMEX pioneered the widespread adoption of this contract structure within cryptocurrency markets. Currently, U.S.-based trading venues are working aggressively to establish domestic alternatives.
[[LINK_START_0]]Kalshi[[LINK_END_0]] operates under Commodity Futures Trading Commission supervision. The company maintains several CFTC licenses and just obtained clearance to provide margin trading services, establishing the regulatory foundation necessary for lawful derivatives operations.
CFTC Chair Michael Selig has indicated these financial products may soon become accessible to U.S. traders, as regulatory bodies work to redirect transaction volume from unregulated international platforms.
Intensifying Rivalry in Derivatives Markets
This strategic pivot places Kalshi in heightened competition with Coinbase. Coinbase has been broadening its derivatives portfolio and has unveiled products resembling perpetuals through extended-expiration futures contracts available to international clients. The exchange has yet to launch authentic perpetual contracts for U.S. customers.
Kraken has similarly deployed tokenized equity perpetual futures for its international user base. Meanwhile, Crypto.com and Gemini have rolled out prediction market offerings, demonstrating the growing convergence between these two financial sectors.
Earlier this week, Polymarket, another prediction market operator and Kalshi’s direct competitor, announced via X that it intends to launch perpetual futures products. Additional specifics were not disclosed.
Daily trading volumes for perpetual futures across cryptocurrency markets currently sit at approximately half their historical peaks but still reached close to $20 billion on Tuesday, based on DeFiLlama analytics.
The Convergence of Prediction Markets and Cryptocurrency Trading
Cryptocurrency trading activity has contracted in recent months amid broader market weakness. Simultaneously, prediction market engagement has experienced substantial growth, attracting both participants and investment funding.
This dynamic has prompted crypto exchanges to explore prediction market features while prediction platforms venture into crypto derivatives territory. Both sectors are now pursuing the same trader demographics.
Kalshi’s strategic expansion may ultimately reach beyond cryptocurrency assets. According to a source briefed on the plans, the company could eventually adapt the perpetual futures framework to additional asset categories.
The organization has not issued formal confirmation regarding launch schedules or specified which digital tokens beyond Bitcoin will receive initial support.
Crypto World
Algorand, Aptos Quantum-Ready, Proof-Of-Stake Exposed: Coinbase
Coinbase’s quantum researchers have highlighted Algorand and Aptos’ work to prepare their networks for potential threats from quantum computing in a report on Tuesday, as they warned that other proof-of-stake chains may be more vulnerable to attacks.
Coinbase’s Independent Advisory Board on Quantum Computing and Blockchain released a paper outlining the threat that quantum computers pose to blockchains and suggested ways to prepare networks for the technology.
“A sufficiently powerful quantum computer could one day break the cryptography that secures digital assets across major blockchains,” Coinbase said. “The board has high confidence this type of machine will eventually be built.”

Quantum computers are an emerging technology expected to be significantly more powerful than today’s top supercomputers, which has some crypto analysts worried that the technology could eventually crack blockchains’ algorithms and break into crypto wallets.
Algorand and Aptos more prepared for quantum
Coinbase said in its report that the layer-1 blockchain Algorand has a “staged roadmap toward full quantum readiness,” and is among the first networks to have deployed cryptography designed to be secure against quantum computers.
“At the transaction and execution layers, Algorand already provides the cryptographic tools necessary to support quantum-resistant accounts,” the report said, adding that users can create such accounts “without requiring protocol modifications.”
It added that Algorand had recently completed its first quantum-resistant transaction on mainnet, but block proposals and committee voting mechanisms “remain vulnerable to quantum attacks,” which the blockchain is researching ways to secure.
Coinbase said that Aptos, a competing layer-1 blockchain, was “well positioned for the transition to post-quantum secure transactions.”
It explained that on Aptos, a user’s public key is stored as metadata associated with the account, and a user’s address isn’t derived from the hash of the user’s public key.
“Users who want to become post-quantum secure need only sign a transaction that updates their authentication key to a post-quantum public key,” Coinbase said. “There is no need to move assets to a new account.”
Proof-of-stake chains may be at greater risk
Coinbase warned that proof-of-stake blockchains, including Ethereum and Solana, may be at greater risk to quantum computing because of the signature schemes validators use to secure the network, according to the board.
Related: Adam Back says Bitcoin’s post-quantum shift may reveal true Satoshi stash
However, Coinbase acknowledged that Solana has created a new signature scheme, and users can move their tokens to a new address based on the upgraded scheme and will be “no longer exposed to a quantum attacker.”
Ethereum, too, “has a clear roadmap to address this in the near future,” Coinbase said, which includes upgrading signatures to be quantum-resistant.
The report also discussed how networks could deal with quantum-vulnerable tokens and wallets, suggesting that blockchains could tell their users to migrate to quantum-proof wallets and that wallets with assets that are quantum-vulnerable would be revoked and lost forever.
However, the board said that the threat of quantum computing “doesn’t exist yet,” as a computer that could threaten crypto “would need to be orders of magnitude more powerful than anything available today,” which could take at least a decade.
Magazine: Bitcoin may face hard fork over any attempt to freeze Satoshi’s coins
Crypto World
US Law Firm Apologizes For AI Hallucinations in Filing
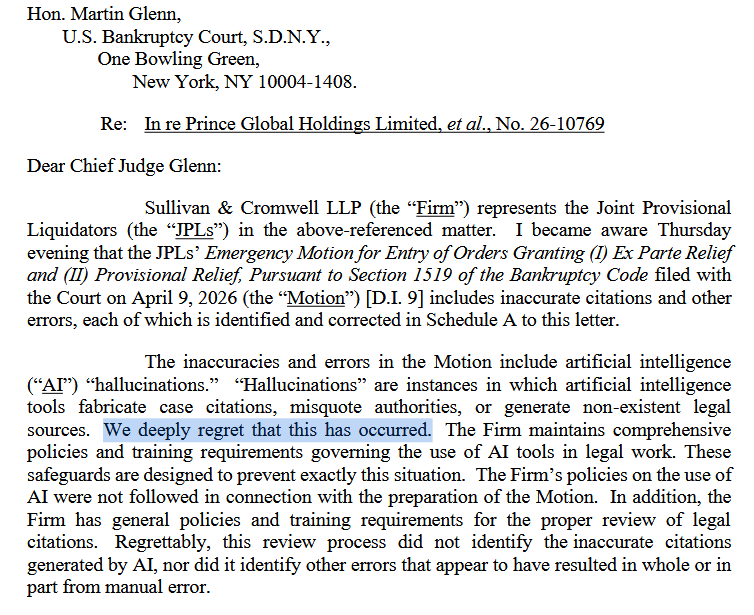
Sullivan & Cromwell’s Andrew Dietderich said the company has AI policies to prevent incorrect citations and other errors, but procedures weren’t followed on this occasion.
Wall Street law firm Sullivan & Cromwell has apologized to a federal judge after submitting a court filing that contained around 40 incorrect citations and other errors caused by AI hallucinations.
“We deeply regret that this has occurred,” Andrew Dietderich, co-head of Sullivan & Cromwell’s global restructuring team, wrote Friday in a letter to Chief Judge Martin Glenn of the US Bankruptcy Court for the Southern District of New York.
“The Firm and I are keenly aware of our responsibility to ensure the accuracy of all submissions including under Local Bankruptcy Rule 9011-1(d), and I take responsibility for the failure to do so,” he said of an emergency motion filed nine days earlier.

The incident highlights the risk AI tools can pose in high-stakes professional work without proper oversight. A database managed by legal technologist Damien Charlotin has recorded 1,334 incidents of AI hallucinations in court filings around the world, including more than 900 in the US.
Charlotin pointed out that most of these hallucinations involve fabricated citations, though AI-generated legal arguments have also occasionally been identified.
Dietderich said Sullivan & Cromwell has policies in place for the use of AI tools, which include a review of the citations it uses, but said the policies weren’t followed.
“Regrettably, this review process did not identify the inaccurate citations generated by AI, nor did it identify other errors that appear to have resulted in whole or in part from manual error.”
Sullivan & Cromwell is one of the largest law firms in the US by revenue, ranking 30th on the AmLaw Global 200. The firm also represented crypto exchange FTX in its bankruptcy case.
Sullivan & Cromwell is conducting an internal investigation
Dietderich said the law firm took “immediate remedial measures,” including a full review of the circumstances that led to the errors.
Related: Coinbase’s AI payments protocol x402 launches app store for AI agents
The firm is also “evaluating whether further enhancements to its internal training and review processes are warranted,” Dietderich said.
Dietderich also noted that the errors were spotted by a rival law firm.
“I also called Boies Schiller Flexner LLP on Friday to thank them for bringing this matter to our attention and to apologize directly to them as well,” he said.
Magazine: IronClaw rivals OpenClaw, Olas launches bots for Polymarket — AI Eye
Crypto World
Umbra Shuts Front End, Roman Storm Says It’s Not Enough
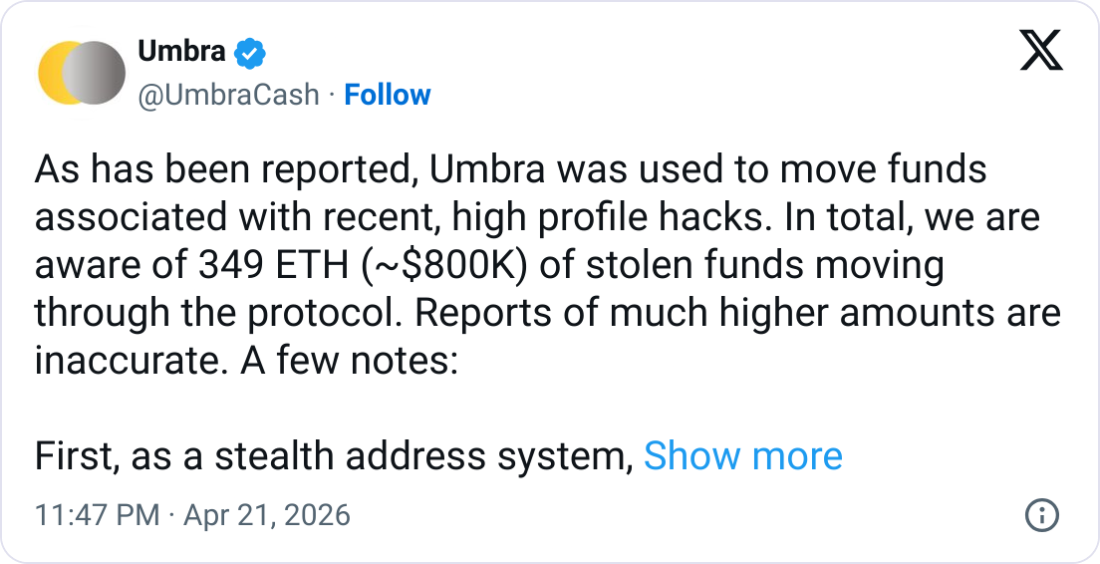
Privacy-focused crypto protocol Umbra said it has taken down its front-end website to make it more difficult for hackers who have been using it to move funds from recent “high-profile hacks.”
Umbra posted to X on Tuesday that it is aware that around $800,000 worth of stolen funds was moved via its protocol.
It added that it made the decision to move the hosted version of its front end into maintenance mode and would restore it “as soon as we are assured that doing so won’t create obstacles to the current recovery efforts.”
It comes just days after the Kelp protocol was exploited for over $280 million, which is suspected to have been carried out by North Korean hackers. Recent reports pointed to Umbra as among the protocols that the exploiter has been attempting to bridge funds from Ether to Bitcoin.
North Korean hacking groups are heavily sanctioned by the US, and multiple crypto platforms have worked to freeze or stifle the hackers’ efforts to move the funds.

Umbra said, however, that there was “nothing we can do” to stop anyone from using its smart contracts or a local or self-hosted version of its open-source front end.
Roman Storm warns front end freeze isn’t enough
Roman Storm, co-founder of the crypto mixer Tornado Cash, argued the move to pause the front end may not be enough to avoid ire from authorities.
Storm was convicted in August of conspiring to operate an unlicensed money transmitting business, despite arguing that he was not in control of how the protocol was used.
“Prosecutors in my case called me a liar when I said that I can’t control Tornado Cash,” said Storm, who beat charges of conspiring to violate US sanctions.
He claimed that authorities viewed “changing a front end is the same thing as controlling an entire protocol.”
Related: Crypto hackers stole $17B over past 10 years: DefiLlama
“If you can make changes to the user interface, including further updates through new builds on IPFS, then you are in full control,” he added.
In its post, Umbra said that its protocol was “useful for protecting the identity of the receiver, not the sender,” and wasn’t useful for hackers wanting to obscure their money trail.
“All the stolen funds moved through the protocol can be identified, and we have been in touch with security researchers who are involved,” it added.
Magazine: South Korea gets rich from crypto… North Korea gets weapons
Crypto World
XRP (XRP) Gains Banking Access as SoFi Onboards Millions While Institutional Interest Soars

Key Highlights
- SoFi Bank now enables XRP deposits, allowing millions to hold XRP alongside BTC, ETH, and SOL in an OCC-regulated banking environment
- The platform provides deposit functionality for 12 digital assets and trading access to 27 cryptocurrencies
- XRP Ledger’s real-world asset volume has skyrocketed 875%, approaching $2.5 billion in tokenized value
- XRP trades above $1.40 with critical resistance zones at $1.50–$1.55 and support levels at $1.30–$1.35
- Prominent financial institutions like BlackRock, Franklin Templeton, and Mastercard are exploring XRP Ledger integration
XRP is experiencing a wave of institutional validation and practical integration, marking a shift from speculative interest to tangible banking adoption. The most recent milestone involves SoFi Technologies, an OCC-regulated U.S. bank with national charter status.

On April 21, SoFi revealed that XRP deposits are now available on its platform, joining Bitcoin, Ethereum, and Solana. The fintech company facilitates trading for 27 different cryptocurrencies while supporting 12 assets for direct deposits.
This positions SoFi among a select group of federally chartered U.S. banks offering comprehensive XRP services—including buying, selling, storing, and depositing—within a single platform that millions use for standard banking operations like bill payments and account management.
Ripple acknowledged the development on X, stating: “More access to XRP with SoFi means more people can participate, and that’s exactly how utility grows.”
SoFi has taken a measured approach to cryptocurrency integration. The company introduced SoFi Crypto last November, enabling customers to trade Bitcoin, Ethereum, and Solana from FDIC-protected accounts. February saw the platform become the first nationally chartered bank in the U.S. to offer Solana deposits. The XRP integration represents a continuation of this methodical expansion strategy.
XRP Ledger Attracts Enterprise-Level Activity and Real-World Applications
Beyond SoFi’s integration, the XRP Ledger is experiencing substantial institutional engagement. During the Digital Assets Forum 2026, Odelia Torteman, a World Bank FinTech specialist, characterized the XRP Ledger as architecturally designed for multi-asset, transparent payment infrastructure.
Real-world asset tokenization on the network has exploded by 875%, with aggregate tokenized value nearing the $2.5 billion threshold. Additionally, a major Japanese travel company is reportedly transitioning prepaid payment infrastructure to the ledger, targeting a domestic market valued at ¥30 trillion.
Financial heavyweights including BlackRock, Franklin Templeton, and Mastercard have demonstrated interest in leveraging the XRP Ledger. Ripple’s leadership has highlighted a $13 trillion payments market opportunity accessible through its Treasury infrastructure.
XRP Price: Critical Technical Zones in Focus
XRP is currently holding ground above $1.40, hovering near its 50-day exponential moving average, a level that has consistently capped rallies. Trading volume remains subdued, typically indicating markets are awaiting directional clarity.
Key support resides at $1.35, with additional backing at $1.30. Overhead resistance concentrates around $1.50 and $1.55. A sustained breakout above the 100-day EMA at $1.53 could pave the way toward 21Shares’ year-end projection of $2.69.
Macro strategist Dr. Jim Willie has outlined a potential $3–$25 valuation scenario if financially distressed banks adopt XRP for settlement purposes. Certain long-term forecasts extend to $27 by 2030, contingent upon widespread banking sector integration.
As of April 21, XRP deposit functionality is operational on SoFi’s platform, accessible to its 13.7 million user base.
Crypto World
Ethereum (ETH) Price Analysis: Major Whales Acquire 700K ETH Amid Bullish Technical Signals

Key Highlights
- Large Ethereum holders accumulated approximately 700K ETH from Thursday through Monday
- Spot ETH ETFs saw continuous inflows for eight days straight, totaling $493.7 million
- Bitmine acquired 101,627 ETH in their biggest weekly purchase of 2026
- The SuperTrend technical indicator turned bullish for the first time since the beginning of 2025
- Negative funding rates persisted for six consecutive days, creating downward pressure below $2,400
Ethereum is currently hovering near $2,300 following a period marked by substantial whale buying activity and robust ETF capital inflows, though futures market dynamics continue to constrain upward price movement.
Data from CryptoQuant reveals that addresses containing over 10,000 ETH added close to 700,000 ETH to their holdings from Thursday through Monday. Exchange reserves of Ethereum have declined by approximately 458,000 ETH since Thursday, indicating strengthening demand from buyers.
Institutional participation has also intensified. US-based spot Ethereum ETFs registered their eighth consecutive day of positive net inflows, accumulating a combined $493.7 million, based on data from SoSoValue.
Bitmine Immersion Technologies executed the year’s largest weekly ETH acquisition, purchasing 101,627 ETH. This transaction elevated their aggregate holdings to 4.976 million ETH. Chairman Tom Lee of Bitmine suggested that the cryptocurrency bear market might be nearing its conclusion sooner than market consensus anticipates, referencing historical cycle patterns dating back to 2015.
Bitmine Adds 101,627 ETH in Biggest Weekly Accumulation in 4 Months
Bitmine Immersion Technologies added 101,627 ETH last week, marking its fastest pace of accumulation since the week of December 15, 2025. As of April 19, 2026, the company holds a total of 4,976,485 ETH,… pic.twitter.com/j6EGixRZTK
— Wu Blockchain (@WuBlockchain) April 20, 2026
Lee highlighted that each cryptocurrency bear market since 2015 has aligned with equity market corrections exceeding 20%. By contrast, the 2026 equity pullback measured just 8%, forming the basis of his argument that the present downturn could prove more abbreviated.
Smart money analytics platform Lookonchain identified multiple significant whale movements throughout the week. Among them, a freshly created wallet pulled 35,000 ETH off Binance before moving the assets to custodial service BitGo.
Technical Indicator Turns Positive
Crypto analyst Ali Martinez shared on X that Ethereum’s daily SuperTrend indicator has switched to bullish territory for the first time since the start of 2025. Martinez observed that the previous occurrence of this technical flip was followed by an extended uptrend. He additionally noted that Bitcoin has yet to breach its corresponding SuperTrend resistance threshold.
SuperTrend flips bullish on Ethereum $ETH for the first time in over a year. pic.twitter.com/hMIDJ6ojrr
— Ali Charts (@alicharts) April 20, 2026
Derivatives Market Creates Headwinds
Notwithstanding robust demand in spot markets, Ethereum funding rates remained in negative territory for six consecutive days. This condition indicates that derivatives market participants maintain a bearish stance, contributing to price weakness below the $2,400 level.
Over the preceding 24-hour period, ETH experienced $53.4 million in total liquidations. Long position liquidations accounted for the majority at $28.4 million.
Examining the four-hour timeframe, ETH is positioned above its 20-period, 50-period, and 100-period exponential moving averages, which are grouped between $2,268 and $2,323. Immediate resistance is located at $2,388, while support levels are found at $2,267 and $2,263.
The 14-day Relative Strength Index registers 55, suggesting a slight advantage for buyers over sellers. Conversely, both the 9-day Stochastic and 14-day Stochastic RSI oscillators are positioned around 40, indicating diminishing upward momentum.
Over the past 30 days, ETH has climbed from approximately $2,155 to above $2,320, though it has retreated roughly 2% on the weekly timeframe from a peak of $2,450.
Crypto World
Volo Protocol Security Breach: $3.5M Drained From Sui-Based Liquid Staking Platform

Key Highlights
- A security breach at Volo Protocol, a liquid staking service on Sui, resulted in approximately $3.5 million in stolen funds
- Three separate vaults containing WBTC, XAUm, and USDC were compromised in the incident
- Within half an hour of disclosure, Volo managed to freeze $500,000 worth of stolen assets
- The protocol’s other vaults, holding $28 million in total value locked, remain secure
- The development team has committed to covering all losses without impacting users
On April 21, Volo Protocol—a liquid staking service operating on the Sui blockchain—disclosed that it had fallen victim to a security exploit resulting in roughly $3.5 million in stolen user funds.
The breach impacted three specific vaults within the protocol’s infrastructure. These vaults contained Wrapped Bitcoin, a gold-pegged asset known as XAUm, and USDC stablecoin. No other vaults within the platform were compromised.
The team behind Volo revealed the incident via X, explaining that they immediately reached out to the Sui Foundation and ecosystem collaborators upon detecting the breach. As a precautionary measure, all vaults were frozen to prevent additional fund drainage.
Remarkably, just 30 minutes after making the exploit public, Volo reported successfully freezing $500,000 of the misappropriated assets. The specific mechanism used to accomplish this freeze was not disclosed.
According to Volo’s statement, the $28 million in assets held across its remaining vaults faces no exposure to risk. The team clarified that these unaffected vaults operate independently and do not contain the same security flaw.
Team Commits to Full User Reimbursement
The Volo development team announced it would shoulder the entire financial burden of the exploit rather than passing any costs to its user base. “We want to be clear: Volo is prepared to absorb this loss,” the team stated on X.
Details regarding the specific security vulnerability exploited in the attack have not been made public. Similarly, the perpetrator’s identity remains unknown.
Volo confirmed that all vaults will remain in a frozen state until investigators complete a comprehensive post-mortem analysis and establish a proper remediation strategy. The team has enlisted on-chain forensic experts to assist in tracking and potentially recovering the outstanding stolen funds.
Emphasizing their commitment to the community, the protocol stated: “We understand that trust is earned, and right now, we are focused entirely on actions,” according to Volo’s public statement.
Latest in a Series of DeFi Security Incidents
This security breach at Volo comes on the heels of a significantly larger exploit targeting Kelp DAO, a LayerZero-powered cross-chain bridge that suffered a devastating $292 million loss in a separate attack.
Security researchers have attributed the Kelp DAO compromise to the Lazarus Group, a North Korean state-sponsored cyber operation with an established history of attacking cryptocurrency infrastructure.
Volo’s team has made no indication that their exploit shares any connection with the Kelp DAO breach.
No specific timeline has been provided for when the frozen vaults will resume normal operations. A detailed post-mortem analysis is anticipated following the completion of the ongoing investigation.
As of now, the $500,000 in frozen assets represents the only confirmed portion of the stolen funds that has been secured.
-

 News Videos7 days ago
News Videos7 days agoSecure crypto trading starts with an FIU-registered
-

 Fashion5 days ago
Fashion5 days agoWeekend Open Thread: Theodora Dress
-

 Politics4 days ago
Politics4 days agoPalestine barred from entering Canada for FIFA Congress
-

 Sports5 days ago
Sports5 days agoNWFL Suspends Two Players Over Post-Match Clash in Ado-Ekiti
-
Entertainment2 days ago
NBA Analyst Charles Barkley Chimes in on Ice Spice McDonald’s Fiasco
-

 Business3 days ago
Business3 days agoPowerball Result April 18, 2026: No Jackpot Winner in Powerball Draw: $75 Million Rolls Over
-
 Politics3 days ago
Politics3 days agoZack Polanski demands ‘council homes not luxury flats for foreign investors’
-

 Crypto World4 days ago
Crypto World4 days agoRussia Pushes Bill to Criminalize Unregistered Crypto Services
-
 Politics1 day ago
Politics1 day agoGary Stevenson delivers timely reminder to register to vote as deadline TODAY
-

 Tech3 days ago
Tech3 days agoAuto Enthusiast Scores Running Tesla Model 3 for Two Grand and Turns It Into Bare-Bones Go-Kart
-

 Tech6 days ago
Tech6 days ago‘Avatar: Aang, The Last Airbender’ Leaked Online. Some Fans Say Paramount Deserves the Fallout
-

 Business5 days ago
Business5 days agoCreo Medical agree sale of its manufacturing operation
-

 Crypto World4 days ago
Crypto World4 days agoRussia Introduces Bill To Criminalize Unregistered Crypto Services
-

 Sports6 days ago
Sports6 days agoBritish climbers complete new route in Swiss Alps
-

 Crypto World3 days ago
Crypto World3 days agoKelp DAO rsETH Bridge Hack Drains $292M as DeFi Losses Top $600M in Two Weeks
-

 Sports6 days ago
Sports6 days ago“Felt Much Better Today”: Josh Hazlewood Opens Up On His Recovery Win Over LSG
-

 Tech6 days ago
Tech6 days agoFord EV and tech chief leaving automaker
-

 Business6 days ago
Business6 days agoCheaper Doritos and Lays helps PepsiCo win back struggling snackers
-

 Entertainment6 days ago
Entertainment6 days agoClavicular Says Streaming May Not Work Without Substances
-

 Entertainment6 days ago
Entertainment6 days agoRuby Rose Accuses Katy Perry Of Sexual Assault, Police React










You must be logged in to post a comment Login