- Fake iCloud deletion emails are pressuring Apple users into dangerous clicks
- Poor grammar in iCloud alerts remains a clear sign of fraud
- Clicking fake iCloud upgrade links can expose banking and personal data
A wave of deceptive emails is attempting to pressure Apple users into believing their iCloud data is at immediate risk of deletion, using increasingly aggressive language to force quick reactions.
The messages often claim a user’s storage limits have been exceeded or that an account has been blocked, followed by threats that photos and videos will be permanently erased on a specified date.
In some cases, recipients receive repeated follow-ups, including what appears to be a final warning stating, “We have tried to contact you several times before… all your data will be completely deleted.”
Article continues below
What the scam email looks like
Warning of the scam, UK consumer body Which? said, “Every Apple user needs to know about this nasty scam doing the rounds.”
“These sneaky fake emails that look like they’re from iCloud and threaten you with claims that ‘all your photos will be deleted.’”
One of the scam emails seen by The Guardian says, “We’ve blocked your account! Your photos and videos will be deleted on [date].” It is headlined “iCloud Storage Alert” and goes on to say: “Storage limit reached… your iCloud account has reached its maximum storage capacity.”
Others read, “Your payment method has expired!… Your cloud service has been disabled,” or “Payment failed for your Cloud storage renewal.”
The timing of these emails can make them appear plausible, especially when they arrive alongside legitimate storage notifications.
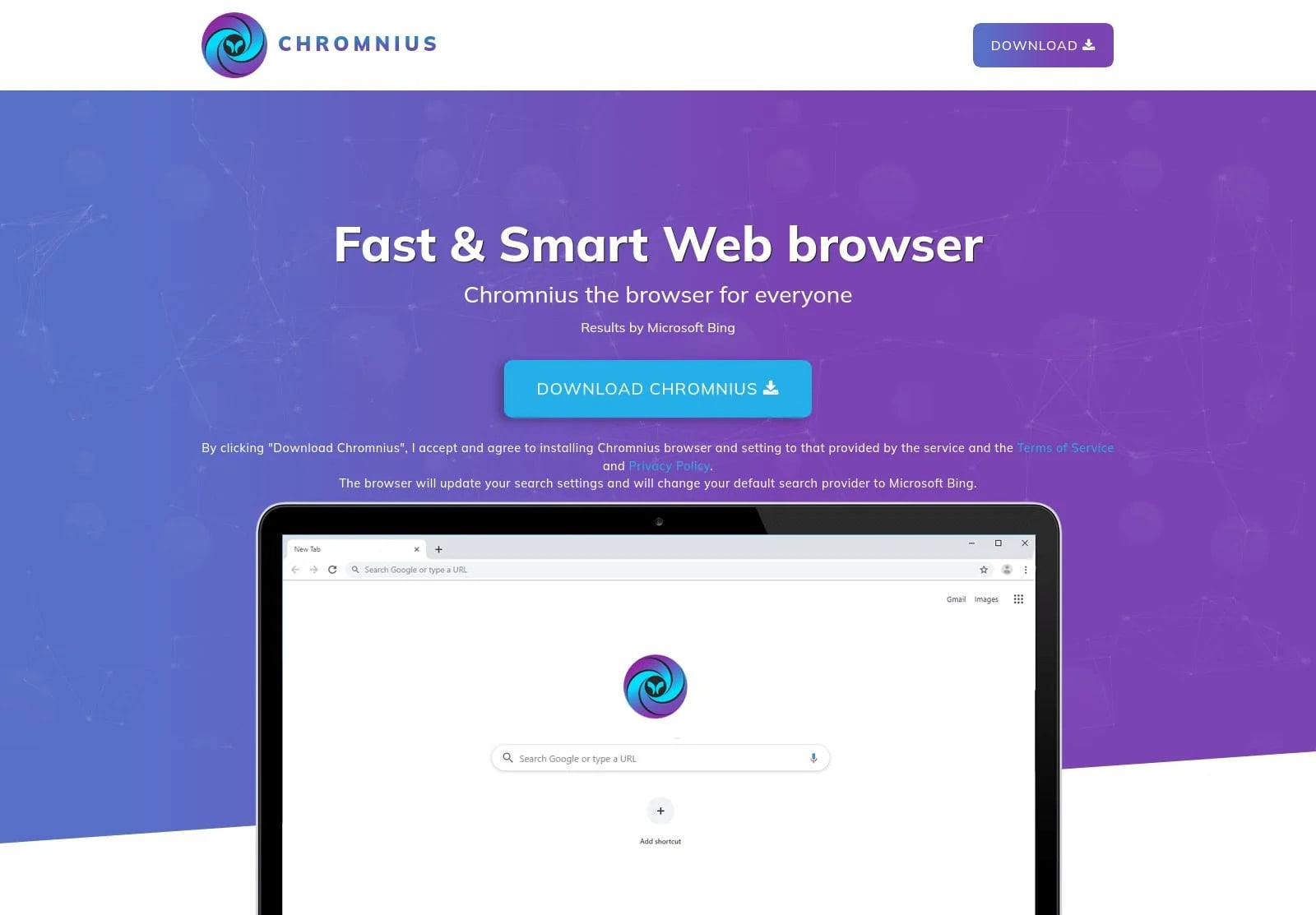
However, the email structure typically follows a predictable pattern — an alarming claim, a deadline, and a call to action — all designed to bypass scrutiny.
It usually includes a button or link claiming to offer an easy “update” to tackle the situation but redirects users to fraudulent pages.
These pages are designed to extract sensitive data, and users can unknowingly hand over personal and banking information, which may then be used for unauthorized transactions or identity theft and distributed through illicit channels.
The initial interaction may appear harmless, but it opens pathways for additional security risks, particularly if users reuse passwords across multiple accounts.
Despite the convincing tone in the message, these phishing emails frequently contain inconsistencies that reveal their origin – for example, the sender address often includes unusual domains that do not align with Apple’s infrastructure, with some referencing unrelated regions or obscure domain extensions.
Grammar issues remain another persistent flaw, with phrases such as “Your account may expires today” indicating a lack of authenticity.
The presence of familiar branding and interface design on phishing pages can delay suspicion, making it more difficult for users to recognize the deception until after information has already been submitted.
While a good antivirus program could help in this situation, avoiding interaction with suspicious emails remains the most effective response — a single click can escalate risk levels.
Users are also advised to verify storage status directly through device settings rather than relying on email prompts.
Reporting such emails helps limit their spread, while maintaining updated security practices, including a properly configured firewall, reduces the likelihood of broader system compromise.
Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews, and opinion in your feeds. Make sure to click the Follow button!
And of course you can also follow TechRadar on TikTok for news, reviews, unboxings in video form, and get regular updates from us on WhatsApp too.






















.jpg)








![Tom Lee: Important Warning To All Ethereum Holders - The Bottom Is Already In [2026 Prediction]](https://wordupnews.com/wp-content/uploads/2026/04/1776284749_maxresdefault-80x80.jpg)


































You must be logged in to post a comment Login