Crypto World
DOJ Says Tornado Cash Developer Made 250 Changes to the Protocol: Is the Immutable Code Defense Dead?
The DOJ core legal theory in the Roman Storm crypto case has never been that writing code is a crime. It’s that exercising operational control over a platform that processes more than $1 billion in illicit funds – while explicitly declining to implement feasible anti-money-laundering controls – constitutes running a criminal business.
That distinction is the mechanism that makes this case matter far beyond Tornado Cash.
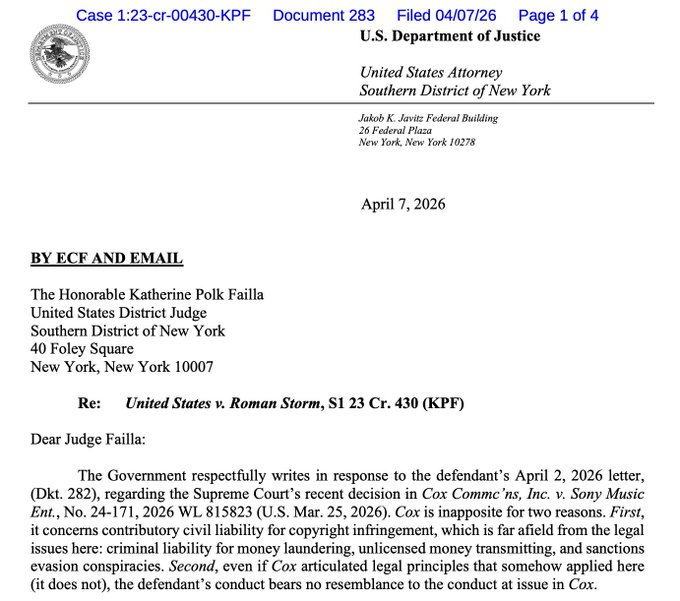
Prosecutors filed a letter Tuesday rejecting Storm’s attempt to leverage a March Supreme Court ruling in Sony Music v. Cox Communications as grounds for dismissal.
The DOJ called the analogy “inapposite” – and the reasoning behind that rejection defines exactly what level of developer involvement triggers federal criminal liability under the current enforcement framework.
The unresolved question: where is the legal floor for DeFi developers who upgrade protocols, manage governance, and selectively respond to compliance inquiries? After Tuesday’s filing, that floor is still undefined – and prosecutors are pushing to make Storm’s retrial the place where it gets drawn.
- The Dismissal Attempt: Storm’s attorneys cited the Supreme Court’s Cox ruling – which shielded the ISP from liability for users’ copyright infringement – as precedent for dismissing criminal charges. DOJ prosecutors rejected the parallel as inapplicable to Storm’s conduct.
- The Control Argument: Prosecutors documented over 250 changes made to the Tornado Cash infrastructure during the charged period, directly contradicting Storm’s defense that the protocol was immutable code beyond his control. That operational record is central to the money laundering conspiracy charge.
- The Partial Conviction: A jury in August 2025 convicted Storm on conspiracy to operate an unlicensed money-transmitting business but deadlocked on money laundering conspiracy and sanctions evasion – the two charges prosecutors now want retried in October 2026.
- The Privacy Protocols Precedent: DOJ’s framing – that developers who implement changes and knowingly forgo compliance measures are operators, not bystanders – applies directly to any upgradeable DeFi protocol with identified founders or core teams.
- The Exposure: Storm faces up to 40–45 years in prison if convicted on all counts. The retrial scope covers the two deadlocked charges; the money transmitting conviction stands.
- What to Watch: The conference between Storm’s defense and Judge Katherine Polk Failla’s court will determine whether October 2026 becomes a firm retrial date – the specific scheduling order is the next legal trigger that confirms or compresses the timeline.
Explore: The best pre-launch token sales with asymmetric upside potential
What the DOJ’s Cox Rejection Actually Establishes – and Why the ‘Immutable Code’ Defense Is Running Out of Road
Storm’s legal team drew a specific parallel: the Supreme Court found Cox Communications shouldn’t be held liable for its users’ infringing activity because Cox had a robust, 98%-effective termination policy for repeat infringers.
The argument was that Storm, like Cox, was a neutral infrastructure provider. Prosecutors dismantled that comparison in a single filing.
The DOJ’s letter to Judge Failla emphasized that Cox actively discouraged the illegal conduct occurring on its network – while Storm and his co-conspirators at Tornado Cash did the opposite.
Prosecutors stated that Storm “actively lied in response to inquiries from victims, telling them he had little control over the protocol when in fact he and his co-conspirators implemented over 250 changes to Tornado Cash infrastructure during the charged time period and explicitly discussed – but forwent – feasible measures to curb criminality on their platform.”
That last clause is the legal weight-bearing element. Under the money laundering and unlicensed money transmission statutes at issue, the question isn’t whether a developer wrote code – it’s whether they operated a system they knew was being used for money laundering, had the capacity to limit that use, and chose not to.
The Bank Secrecy Act’s anti-money-laundering compliance obligations attach to operators, not passive bystanders. Prosecutors’ position is that Storm was an operator by every functional measure.
“In short, the defendant’s reaction to criminal use of his company was window dressing at best and outright misdirection at worst” – prosecutors’ letter to Judge Failla, filed Tuesday.
The August 2025 jury conviction on the unlicensed money transmission count already rejected Storm’s passive-developer framing once.
The October 2026 retrial targets the money laundering conspiracy and sanctions evasion charges directly – the counts where the jury deadlocked, not where it acquitted. That distinction matters: deadlock means twelve jurors couldn’t reach unanimity, not that the evidence was insufficient to convict.
Discover: The Best Crypto Presales Live Right Now
The post DOJ Says Tornado Cash Developer Made 250 Changes to the Protocol: Is the Immutable Code Defense Dead? appeared first on Cryptonews.
Crypto World
Web3 Projects Lost $464.5M in Q1 2026 as Hacks Shift Beyond Code: Hacken
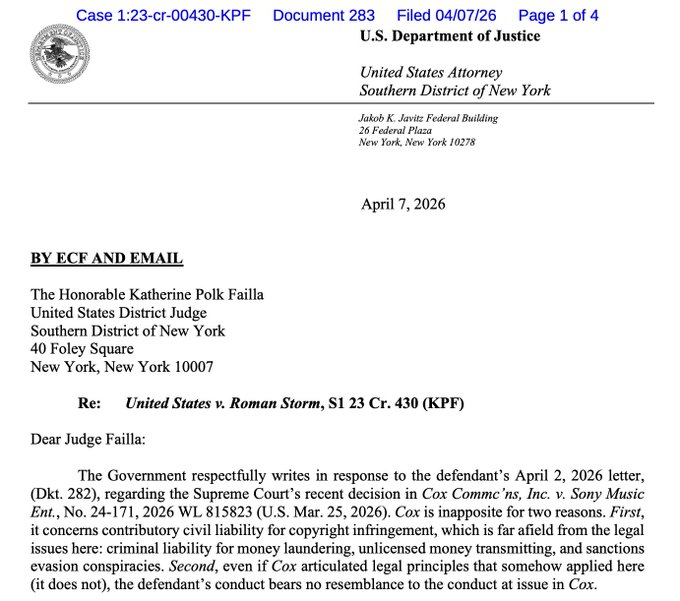
Web3 projects lost $464.5 million to hacks and scams in the first quarter of 2026, while multi-billion-dollar “mega hacks” gave way to a larger number of mid-sized incidents, according to blockchain security company Hacken.
According to Hacken’s Q1 2026 report, phishing and social engineering attacks dominated the period, accounting for $306 million in losses in a quarter that saw 43 incidents overall. A single $282 million hardware wallet scam in January was responsible for 81% of the quarter’s damage.
Smart contract exploits totaled $86.2 million, with access control failures, including compromised keys and cloud services, driving an additional $71.9 million in losses.
The losses place this quarter as the second-lowest first quarter since 2023, with the absence of a single mega hack on the scale of Bybit, which lost $1.46 billion in Q1 2025, the primary driver of the year-over-year decline.
Hacken’s incident mapping shows the largest failures increasingly occurring outside onchain code, in operational and infrastructure layers that traditional audits rarely touch. Yev Broshevan, chief executive and co-founder at Hacken, told Cointelegraph the most expensive failures “happen outside the code layer entirely.”
Related: Aethir halts bridge exploit, promises compensation after $90K loss
According to Hacken, that shift is drawing greater scrutiny from regulators and institutional counterparties, with frameworks such as the Markets in Crypto-Assets Regulation (MiCA) and Digital Operational Resilience Act (DORA) in the European Union moving further into enforcement and raising expectations around continuous security monitoring and incident response.
Legacy code, fake VC calls and key compromises
Broshevan pointed to $306 million in phishing, a $40 million North Korea-linked fake venture capitalist (VC) call against Step Finance, and a $25 million AWS key management service compromise at Resolv Labs. Even where smart contracts were at fault, the costliest bugs often sat in legacy deployments and known vulnerability classes. Truebit lost $26.4 million to a bug in a Solidity contract deployed around five years ago, while Venus Protocol was hit by a donation attack pattern documented since 2022.

Six audited projects, including Resolv with 18 audits and Venus with five separate firms, still accounted for $37.7 million in losses. On average, that was more than their unaudited peers because higher total value locked (TVL) protocols attract more sophisticated attackers and exploits.
Global watchdogs harden incident response expectations
In Q1, MiCA and DORA in the EU shifted further into active enforcement, Dubai’s regulator, the Virtual Assets Regulatory Authority, tightened expectations around its Technology and Information Rulebook, Singapore enforced Basel-aligned capital and one-hour incident notification rules, and the United Arab Emirates’ new Capital Market Authority took over federal digital asset oversight with broader powers and higher penalties.

Related: Crypto hackers steal $169M from 34 DeFi protocols in Q1: DefiLlama
Hacken ties those regimes to a new benchmark for “regulator-ready” stacks that includes proof-of-reserves attestations backed by daily internal reconciliation, 24/7 onchain monitoring across treasury wallets and privileged roles, automated circuit-breakers on minting and governance functions and incident notification clocks calibrated to the strictest applicable standard.
The report highlights “realistic” targets of awareness within 24 hours, labeling within four hours, and blocking in 30 seconds, with “aspirational” goals as low as 10 minutes for detection and 1 second to block, based on guidance from Global Ledger’s 2025 Laundering Race data.
At the human layer, Hacken flags North Korean clusters as the most consistent operational threat, with Step Finance’s $40 million loss and Bitrefill’s infrastructure breach extending a playbook of fake VC outreach, malicious video call tooling and compromised employee endpoints that extracted roughly $2.04 billion from the sector in 2025.
Magazine: XRP yet to ‘price in’ 3 bullish catalysts, Bitcoin to $80K? Trade Secrets
Crypto World
Bitcoin nears breakout above $75,000 with short squeeze risk building
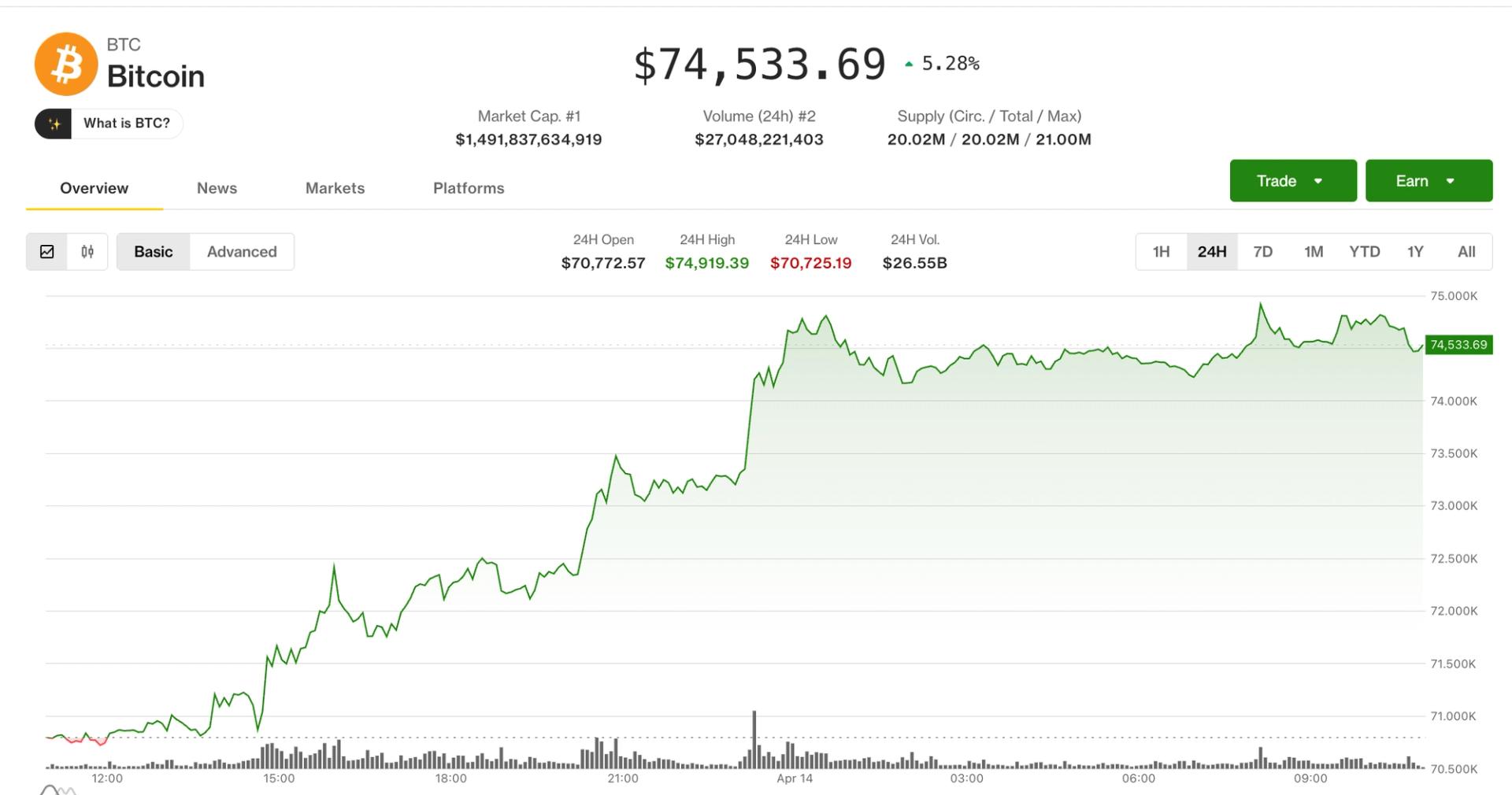
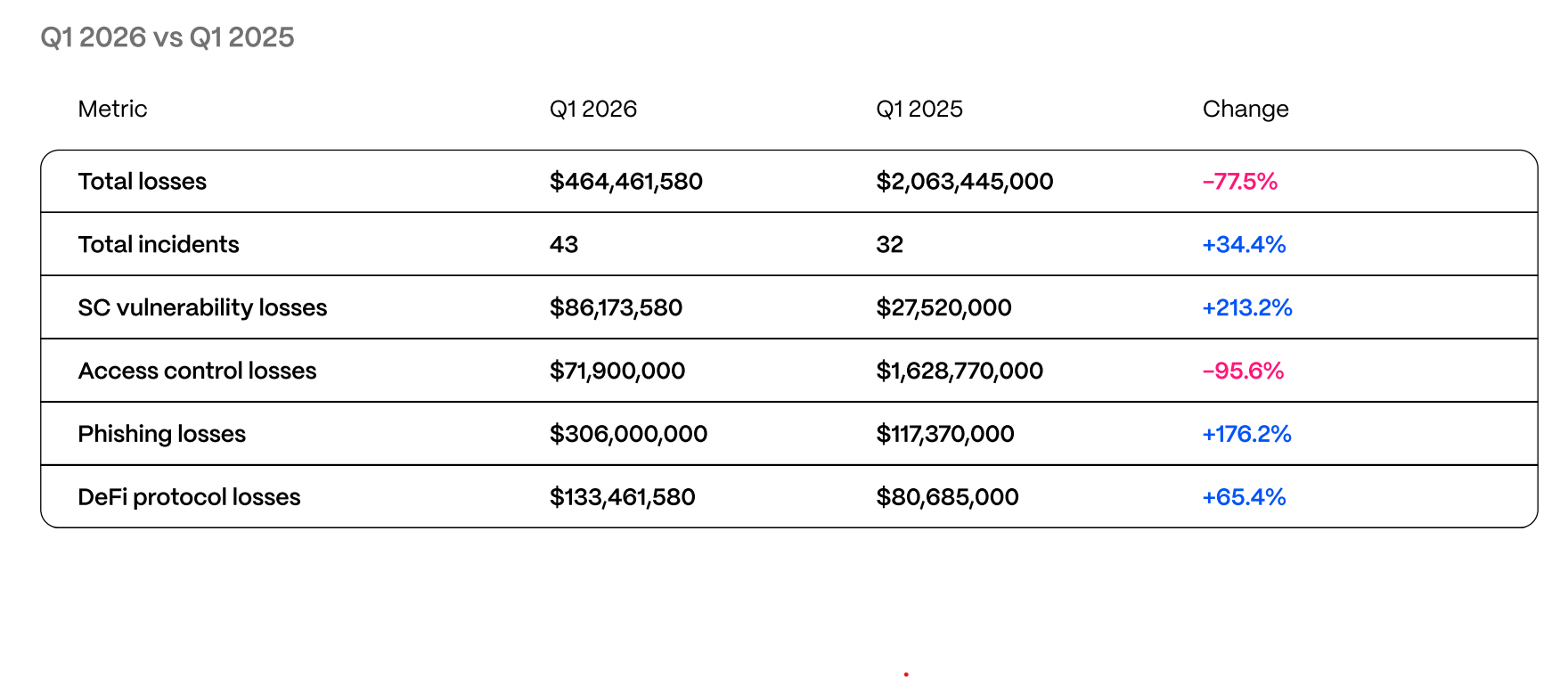
Bitcoin is pressing up against $75,000, a price it has repeatedly failed to surpass since early February, putting the broader crypto market on breakout watch after more than two months of range-bound trading.
Traders have been building short positions around that level, betting on another rejection. Data from CoinGlass shows roughly $200 million in shorts would be liquidated if BTC pushes above $75,500 — a dynamic that could accelerate any upside move.
At the same time, macroeconomic sentiment is improving. U.S. equities rallied Monday, with the S&P 500 index posting its highest close since before the Iran conflict escalated, after President Donald Trump signaled willingness to strike a deal with Tehran.
Precious metals also made a comeback on Tuesday with silver rallying by 2.9% since midnight UTC while gold added 0.7% to $4,775 per ounce.
Derivatives positioning
- Notional open interest (OI) in crypto futures rose to $126 billion, the most since Jan. 31, according to Coinglass.
- Ether’s OI surged to 14.99 million ETH ($35.79 billion), the highest since July. The growth likely stems from increased demand for bullish bets because the 24-hour cumulative volume delta (CVD) is positive, indicating that aggressive buying is dominating the flow. Positive funding rates also suggest the same.
- Bitcoin OI has surged to a record high of 767,000 BTC, while positive CVD and funding rates also signal bullish positioning.
- ZEC, SOL and HYPE are other notable coins displaying bullish patterns.
- It’s worth noting that while funding rates are positive for most tokens, they are not unusually high. This is a sweet spot for a grind higher, and indicates that the market is not overheated.
- However, the 30-day implied volatility (IV) indexes for bitcoin and ether, BVIV and EVIV, have stopped declining over the past two days. Until recently, the spot-price rally was accompanied by falling IV, a dynamic that has now shifted, with IV stabilizing even as prices continue to rise. If this divergence persists or widens, it could raise questions about the sustainability of the price gains.
- Data from Deribit shows that dealer gamma positioning is deeply negative at $75,000. So, if BTC rises past this level, dealers could buy into the rising market to hedge their exposure back to neutral. This could accelerate the uptrend. Similarly, if prices turn lower from $75,000, dealers could sell into a falling market, accelerating the decline.
- Bitcoin puts remain pricier than calls across all time frames, risk reversals show. In ether’s case, the sentiment has flipped bullish in favor of calls in short-term expiries. The long-end continues to show a bias for puts.
Token talk
- The altcoin market is taking a back seat for Tuesday’s breakout attempt, with the bitcoin-dominant CoinDesk 5 (CD5) and CoinDesk 20 (CD20) indexes posting gains of 0.5%-0.7% since midnight, beating the benchmarks weighted toward altcoins.
- Ether (ETH) is up by 0.7% since midnight, beating majors XRP and SOL, which are down by 0.2% and 0.5%, respectively. ADA lost 2.2% overnight.
- Memecoins BONK, FLOKI and WIF have cooled after a sector-wide rally on Monday, each losing between 2.4% and 3% since midnight as traders focus on the potential bitcoin breakout.
- Ethena (ENA) gained 5.6% over the past 24 hours, before giving back 4% during Asian and European hours.
- The altcoin market is delicately poised. If bitcoin breaks above $75,000 and consolidates, fresh capital will rotate into more speculative bets. For now the focus is on BTC.
Crypto World
Natural Gas: key support amid renewed escalation

A key development on 13 April was the start of a naval blockade of Iranian ports, a direct consequence of the collapse of negotiations in Islamabad on 12 April. The blockade covers all vessels entering and leaving Iranian ports in the Persian Gulf and the Gulf of Oman. Around 20% of global natural gas trade passes through the Strait of Hormuz, and the renewed escalation has once again heightened risks to global LNG supplies. European TTF has previously reacted with sharp widening spreads during earlier flare-ups, while the Asian JKM benchmark also remains sensitive to regional disruptions.
Against this backdrop, natural gas as an asset class is caught between two opposing forces: a geopolitical risk premium is providing price support at the global level, while a structural supply surplus — record production, accelerated injections into storage, and an unusually warm spring in the Northern Hemisphere — is weighing on prices from a fundamental perspective.
Technical picture

On the daily chart of XNGUSD, the move from the December 2025 high near 5.200 remains downward but structurally uneven: the sequence of interim highs and lows does not form a classic trending impulse. Volatility is compressing, and each rebound is shorter than the previous one, indicating a gradual loss of selling momentum as price approaches a key support level. Quotes are now trading close to the psychological 2.600 level, which has acted as an important reference point since late 2024.
The volume profile shows a Point of Control (POC) in the 3.150–3.200 range, where the bulk of trading activity is concentrated. This zone acts as the first major barrier to any recovery. The 3.400 level remains the next significant resistance above.
The RSI with Moving Averages reads 34 / 40 / 42, with all three metrics remaining below the neutral 50 level and the moving averages pointing lower, signalling continued downside pressure.
Summary
Natural gas prices are approaching the key psychological level of 2.600, the lower boundary of a consolidation range that has been in place since late 2024, while the blockade of Iranian ports keeps global energy markets in a state of heightened uncertainty. The RSI with Moving Averages remains below the neutral threshold across all three readings.
Start trading commodity CFDs with tight spreads (additional fees may apply). Open your trading account now or learn more about trading commodity CFDs with FXOpen.
This article represents the opinion of the Companies operating under the FXOpen brand only. It is not to be construed as an offer, solicitation, or recommendation with respect to products and services provided by the Companies operating under the FXOpen brand, nor is it to be considered financial advice.
Crypto World
The Hidden War for Speed in DeFi

In decentralized finance, everyone talks about yield, liquidity, and tokenomics—but almost no one talks about time. Yet beneath the surface, a silent battle is unfolding. Not for users. Not for tokens.
But for milliseconds.
Welcome to the latency wars—where speed isn’t just an advantage… It’s alpha.
Speed Is No Longer a Feature—It’s a Weapon
In traditional finance, high-frequency trading firms spend millions shaving microseconds off execution time. DeFi is now heading down the same path—just dressed in smart contracts and liquidity pools.
Here’s the brutal reality:
- The faster your transaction executes, the better your price
- The earlier you interact with liquidity, the higher your yield
- The quicker you react to market signals, the more edge you capture
In a permissionless system, speed becomes the closest thing to an unfair advantage.
Faster Execution = Better Yield
Yield in DeFi isn’t static—it’s constantly shifting.
Opportunities like:
- Liquidations
- Arbitrage gaps
- Yield farming rewards
…are often claimed in seconds.
If your transaction arrives late:
- The liquidation has already taken place
- The arbitrage is already closed
- The yield is already diluted
Speed determines who gets paid—and who gets leftovers.
This is why advanced players invest in:
- Private RPC endpoints
- Optimized gas strategies
- Transaction bundling
- MEV-aware routing
Because in DeFi, being right isn’t enough—you have to be first.
Cross-Chain Latency Arbitrage
As DeFi expands across multiple chains, a new frontier has emerged: cross-chain latency arbitrage.
Prices don’t update instantly across ecosystems. That delay—sometimes just seconds—creates exploitable gaps.
Example:
- Asset price updates on Chain A
- Chain B lags behind
- Arbitrage bots exploit the difference before equilibrium returns
The profit window is tiny. The competition is brutal.
This has led to:
- Cross-chain bots operating 24/7
- Ultra-fast bridge monitoring systems
- Predictive routing based on latency patterns
It’s not just about where liquidity is anymore.
It’s about who reaches it first across chains.
The Infrastructure Arms Race
Behind every fast trade is a stack of invisible infrastructure.
We’re seeing an arms race across:
1. RPC Optimization
Custom nodes reduce lag and improve transaction broadcast speed.
2. Block Builders & MEV Relays
Specialized actors reorder transactions for optimal execution—sometimes capturing value before it even reaches the public mempool.
3. Geographic Advantage
Physical proximity to validators can shave off critical milliseconds.
4. Parallel Execution Chains
New blockchains are being designed specifically for speed—processing transactions simultaneously instead of sequentially.
Who Wins the Latency Wars?
Not necessarily the smartest.
Not even the most capitalized.
The winners are:
- The fastest infrastructure
- The best-connected systems
- The most optimized execution pipelines
This creates a subtle shift in DeFi’s philosophy.
What started as a level playing field is evolving into a system where:
- Technical edge = financial edge
- Infrastructure = strategy
- Speed = profit
The Trade-Off: Speed vs Fairness
There’s a growing tension at the heart of DeFi:
- Faster systems improve efficiency
- But they also centralize advantage
If only a handful of players can afford ultra-low latency infrastructure, the ecosystem risks drifting toward the same inequalities seen in traditional finance.
This raises big questions:
- Should DeFi optimize for fairness or efficiency?
- Can protocols be designed around latency advantages?
- Will new mechanisms (like fair ordering or batch auctions) rebalance the game?
Crypto World
Phishing Drives Majority of Web3 Losses to $464M in Q1, Hacken

Hacken’s Q1 2026 security snapshot tallies $464.5 million in losses across 43 Web3 incidents, underscoring a shift in where attackers hit and how damage accumulates. The report highlights phishing and social-engineering campaigns as the dominant threat, totaling $306 million in losses for the quarter. A separate, highly disruptive incident—a $282 million hardware-wallet scam in January—was responsible for 81% of the quarter’s damage, according to Hacken. Smart-contract exploits reached $86.2 million, while access-control failures, including compromised keys and cloud-service breaches, accounted for $71.9 million. The quarter stands as the second-lowest first quarter since 2023, helped by the absence of a Bybit-scale mega hack that drove much of the year-ago decline.
Hacken’s chief executive and co-founder, Yev Broshevan, emphasized a notable trend: the costliest failures increasingly occur outside the code itself. “The most expensive failures happen outside the code layer entirely,” he told Cointelegraph, pointing to real-world weaknesses in operational and infrastructure layers that traditional code audits often miss.
For context, Hacken’s review arrives as regulators and institutional players sharpen expectations around security. The report notes that regulatory regimes such as the European Union’s Markets in Crypto-Assets Regulation (MiCA) and the Digital Operational Resilience Act (DORA) are moving from framework to enforcement, while regulators in the UAE, Singapore, and Dubai’s regulator, among others, tighten oversight and incident-response requirements. These shifts are shaping what Hacken calls “regulator-ready” security stacks that demand continuous monitoring and rapid containment measures.
Key takeaways
- $464.5 million in losses across 43 incidents in Q1 2026, with phishing/social engineering driving $306 million of that total. A single January incident of $282 million hardware-wallet theft accounted for a large share of the quarter’s damage.
- Smart-contract exploits totaled $86.2 million, while $71.9 million stemmed from access-control and compromised-key or cloud-service failures.
- The quarter marks the second-lowest first quarter since 2023, aided by the absence of a mega hack on the scale of Bybit’s 2025 incident.
- Attack patterns are shifting toward operational and infrastructure risk, reinforcing the view that audits of on-chain code alone are insufficient to measure a protocol’s security posture.
- Regulators are tightening expectations. MiCA, DORA, Dubai’s VARA, Singapore’s Basel-aligned requirements, and the UAE’s Capital Market Authority push for stronger incident reporting, continuous monitoring, and defined response timelines.
Operational risk dominates the early 2026 landscape
The Hacken analysis stresses a transition in the vulnerability ledger from purely on-chain code issues to failures rooted in operations and infrastructure. The most expensive losses, the report suggests, arise from misconfigurations, compromised credentials, and weak third-party integrations rather than only from bugged smart contracts. This is consistent with a broader industry message: a robust security program must cover people, processes, and technology in parallel with code audits.
Hacken’s interview with Broshevan reinforces this view: the most consequential incidents tend to emerge from non-contract layers, such as identity and access management, cloud configurations, and supply-chain dependencies. The result is a security problem that requires defense-in-depth measures that extend beyond formal audits of deployed code.
Legacy code and multi-year vulnerabilities persist
Even as the industry grapples with modern attack vectors, the report highlights several high-cost incidents rooted in legacy deployments or well-known vulnerability patterns. Notably, a $26.4 million loss at Truebit stemmed from a Solidity contract bug deployed roughly five years ago. Venus Protocol faced a donation-style attack that exploited long-standing patterns around contract governance. In another example, a $40 million loss occurred via a North Korea-linked fake venture-capital outreach targeting Step Finance, illustrating how social-engineering campaigns still deliver significant damage.
In parallel, Resolv Labs experienced a compromise of its AWS key-management service, illustrating how access-control failures can underpin large losses even when the code itself isn’t the root cause. Hacken’s incident mapping also flags the broader “playbook” that attackers used in 2025—fake VC outreach, malicious video-call tooling, and endpoint compromises—that reportedly contributed to roughly $2.04 billion in sector-wide losses that year.
Beyond these marquee cases, six audited projects—among them Resolv (18 audits) and Venus (five auditing firms)—accounted for $37.7 million in losses. The data hints at a nuanced relationship between audit activity and loss exposure: higher-value protocols with more assets at stake may attract more sophisticated attackers, even if audited.
Audits, TVL, and the resilience gap
The finding that six audited projects were responsible for millions in losses despite having undergone multiple audits raises a practical question for builders: does audit severity or frequency translate into real-world risk reduction? Hacken notes that these audited protocols typically carry higher total value locked (TVL), which equates to bigger prize pools for attackers. In other words, audits alone may not solve the complex, multi-layer risk profile faced by high-TVL projects, underscoring the need for continuous security monitoring and layered defenses.
Regulatory tightening and the move toward “regulator-ready” security
The quarter’s regulatory backdrop reinforces the story that security is becoming a market and a compliance issue. MiCA and DORA are moving deeper into enforcement, with regional regulators increasing expectations for ongoing security practices. In Dubai, the Virtual Assets Regulatory Authority tightened its Technology and Information Rulebook, while Singapore has enforced Basel-aligned capital and rapid incident-notification timelines. The UAE’s new Capital Market Authority has assumed broader digital-asset oversight with stiffer penalties. Hacken frames these developments as a call to operators to demonstrate constant security readiness, not just to pass a one-off audit.
As part of this shift, Hacken advocates a concrete framework for “regulator-ready” security architectures. The blueprint includes:
- Proof-of-reserves attestations backed by daily internal reconciliation;
- 24/7 on-chain monitoring across treasury wallets and privileged roles;
- Automated circuit-breakers for minting and governance actions;
- Incident notification clocks calibrated to the strictest applicable standard.
Hacken also references a spectrum of response-time targets, distinguishing between “realistic” and “aspirational” goals. Realistic aims include awareness within 24 hours, labeling within four hours, and blocking within 30 seconds. Aspirational targets envision detection within 10 minutes and a 1-second block, drawing on data from Global Ledger’s 2025 Laundering Race. While ambitious, these benchmarks outline concrete steps for projects seeking to align with regulator expectations and institutional counterparties.
Threat actors, playbooks, and the evolving risk landscape
The report keeps returning to the human factor: North Korean actor clusters are identified as the most consistent operational threat in Q1 2026. The combination of social-engineering campaigns, fake professional outreach, and compromised employee endpoints continues to provide a reliable pathway to large losses. The Step Finance case and the Bitrefill-related infrastructure breach illustrate a broader pattern where attackers blend social manipulation with technical exploitation to extract value, often targeting high-value protocols with sophisticated tooling.
For investors, developers, and operators, the takeaway is clear: a successful‑looking deployment with strong smart contracts can still be undermined by weak operational practices, poor key management, or insufficient incident response readiness. The evolving threat landscape demands a multi-layered security approach, ongoing monitoring, and a clear plan for rapid containment—precisely what regulators are now pushing as non-negotiable standards. For builders, this means integrating security into product design from day one and maintaining a culture of continuous testing, diligence, and resilience.
Further reading and related reporting reinforce the broader context: industry-wide security incidents in early 2026 came with a cautionary reminder that DeFi risk resides not just in code but in how projects operate, govern, and respond under pressure. As enforcement tightens and security expectations rise, market participants will be watched not just for audits and audits’ results, but for visible, verifiable resilience across people, processes, and technologies.
Looking ahead, observers will be watching whether Q2 2026 echoes the Q1 trend toward infrastructure and operational risks or whether new defenses and policy measures begin to close the gap. The balance between code quality, operational hygiene, and regulatory compliance will determine how quickly the ecosystem can move toward a posture that can withstand both sophisticated attacks and tougher supervisory regimes.
Crypto World
Senhwa Biosciences inks up to $16M funding deal with GEM to boost AI drug discovery
Senhwa Biosciences, a clinical-stage biopharmaceutical company based in Taiwan, has entered a partnership with a global investment group to accelerate its artificial intelligence-related drug development.
Summary
- Senhwa Biosciences secured up to $16 million from Global Emerging Markets affiliate GEM to advance its clinical pipeline and AI-driven drug discovery platform.
- The firm is expanding oncology programs and leveraging C2S “cell-to-sentence” technology with CellType to accelerate identification of combination cancer therapies.
- Early AI validation supports its “cold-to-hot tumor” strategy, positioning Senhwa within the emerging immuno-oncology 2.0 space.
According to an April 14 report, Senhwa Biosciences has signed a Memorandum of Understanding (MOU) with GEM Yield Bahamas Limited, an affiliate of Global Emerging Markets, where the latter will provide up to $16 million in capital to support Senhwa’s strategic growth.
These include the advancement of its clinical pipeline, the expansion of its oncology programs, and the scaling of its machine learning discovery platform.
Besides focusing on cancer research, the firm has been looking into innovative ways to interpret complex biological datasets. After leveraging its connections with Y Combinator, it collaborated with the biotech firm CellType to implement next-generation cell-to-sentence technology.
This system has led researchers to identify actionable insights more quickly, allowing for a more structured approach to finding combination treatments for various malignancies.
The AI-enabled validation process has shown that Senhwa’s lead compounds can effectively modulate immune responses within the tumor microenvironment.
It reinforces its cold-to-hot tumor strategy and thus enables Senhwa to stand out as a leader in the immuno-oncology 2.0 field. This comes as AI-assisted drug discovery becomes a standard for modern medicine. For instance, the ability to predict how a drug interacts with a resistant tumor can significantly shorten the time required for clinical trials.
As per Senhwa, the strategic funding will enable it to move its clinical trials forward alongside its technological expansion. This would significantly strengthen the company’s position in the global biopharmaceutical market.
At the same time, the partnership will likely open new doors for international collaborations and future commercialization.
Crypto World
Oklo (OKLO) Stock Climbs 7.2% Despite $50M Insider Share Dump
Key Takeaways
- Oklo (OKLO) shares advanced 7.2% Monday, finishing at $53.85 with approximately 8.29 million shares changing hands
- Wall Street maintains a “Moderate Buy” consensus with an $84.30 average price target, despite recent downgrades from UBS, Citi, and B. Riley
- The company’s Q4 earnings per share came in at −$0.27, falling short of analyst expectations of −$0.17
- Company insiders offloaded more than 818,000 shares valued at approximately $50.9 million during the past quarter
- The company plans to bring its inaugural Aurora reactor online in Idaho by 2027, projecting revenues of $36 million by 2028
Shares of Oklo (OKLO) surged 7.2% during Monday’s trading session, settling at $53.85. The stock peaked at $53.96 intraday, representing a solid gain from Friday’s closing price of $50.25. Approximately 8.29 million shares traded hands, falling roughly 17% short of the stock’s typical daily volume of 10 million.
The upward movement occurs as nuclear energy equities maintain investor attention, fueled by escalating electricity demands from artificial intelligence operations and data center expansion.
Oklo’s current valuation stands at approximately $9.35 billion. The stock trades significantly below its 50-day moving average of $60.16 and its 200-day moving average of $89.90.
Wall Street Analysts Lower Price Expectations
Analyst sentiment toward Oklo has moderated somewhat over recent weeks. UBS slashed its price objective from $95 down to $60 while maintaining a “neutral” stance. Citi reduced its target from $95 to $73.50, also with a “neutral” rating. B. Riley lowered expectations from $129 to $92 while retaining a “buy” recommendation.
Cantor Fitzgerald maintained its “overweight” position with a $122 price objective. Wedbush similarly preserved its “outperform” assessment.
The overall Wall Street consensus stands at “Moderate Buy” with an $84.30 average price target. While this remains substantially above current trading levels, analyst expectations have been trending downward.
Among 19 analysts tracking the stock, two assign a Strong Buy rating, nine recommend Buy, six suggest Hold, and two advise Sell.
Regarding financial performance, Oklo posted a quarterly loss of $0.27 per share, underperforming analyst projections of −$0.17 by $0.10. Wall Street forecasts a full-year loss of −$8.20 per share for the current fiscal year.
Company Executives Unload Significant Stock Holdings
Insider transactions have increased notably. CFO Richard Craig Bealmear divested 16,342 shares on April 1st at $51.08 per share, generating proceeds of approximately $834,749. This transaction decreased his holdings by about 4%.
William Carroll Murphy Goodwin, another insider, sold 2,820 shares in March at $56.69 each, reducing his position by approximately 15%.
Collectively, company insiders have sold 818,766 shares valued at roughly $50.9 million throughout the previous quarter. Despite these sales, insiders maintain 18.9% ownership, while institutional investors control 85.03%.
Oklo’s Aurora microreactor technology delivers 1.5 MW of power independently and can expand to 75 MW per installation. The platform is designed for remote and off-grid applications, utilizing metallic uranium fuel capable of operating approximately ten years between refuelings.
The company currently generates minimal revenue. Its inaugural 75 MW Aurora Powerhouse reactor deployment in Idaho is scheduled for 2027. Additionally, Oklo secured a U.S. Department of Defense agreement to construct a reactor at Eielson Air Force Base in Alaska.
Revenue projections show growth from less than $1 million in 2026 to $36 million by 2028.
Crypto World
Why is Crypto Up? Ether, HYPE, and Solana Lead Following US Grand Deal

Why is crypto going up? Ethereum is about to tap $2,400, while Solana mirrors Bitcoin’s gain as it pushes toward $75,000 on the back of what analysts are calling the “US grand deal.” It’s a macro catalyst that may have more runway than most expect.
The rally is broad-based; Aave, HYPE, Ethereum, and Solana are all leading gains as risk appetite floods back into digital assets. Positive regulatory sentiment under the current US administration, combined with accelerating institutional inflows into ETH products, appears to be driving the move. Citi’s 12-month ETH target of $5,440 is suddenly getting attention again.
The question now is not why crypto is up, but how far it can run, and which assets offer the most asymmetric upside from here.
Discover: The best pre-launch token sales
Why? Why is Crypto Going Up Today?
The Grand Deal. It is the macro layer that changes institutional math. It is maybe covering the peace deal on the US-Iran war, but it could also change the tailwinds on structured DeFi access, custody frameworks, and tokenized asset classification, and removing the compliance ambiguity that has been keeping institutional crypto allocations capped at exploratory positions.
The Grand Deal can also, in the end game passes key legislative hurdles, compliance teams greenlight expanded exposure, Bitcoin $75K becomes a structural target rather than a speculative one, and ETF inflow data confirms the repositioning over the following two to three weeks. Yes, when politicians stop thinking about war, they can start thinking about the Clarity Act more.
For Altcoins like Solana, the picture is similarly constructive, SOL is tracking ETH’s momentum with the broader risk-on move, though specific technical levels remain in flux.
The macro tailwind, driven by the same geopolitical and trade deal sentiment that has lifted Bitcoin toward $75,000, provides a supportive floor for both assets.
Discover: The best crypto to diversify your portfolio with
LiquidChain Targets Early Mover Upside as Altcoins Test Key Levels
Altcoins at the current price are already priced in a significant recovery. To 4x from here, big coins like Ether and SOL need to reach something beyond a multi-year horizon, but hardly the asymmetric bet it was in 2022. Early-stage infrastructure projects launching into a bull market tend to offer a different risk/reward profile entirely.
LiquidChain is a Layer 3 infrastructure project positioning itself as the cross-chain liquidity layer — fusing Bitcoin, Ethereum, and Solana liquidity into a single execution environment. The core architecture includes a Unified Liquidity Layer, Single-Step Execution, Verifiable Settlement, and a Deploy-Once framework that lets developers reach all three ecosystems simultaneously without rebuilding protocol stacks.
The presale is currently priced at $0.01449, with more than $660K raised to date. The coin also offers 1600% APY staking bonus for new buyers.
Research LiquidChain’s presale terms before the next pricing tier closes is worth the 10 minutes.
The post Why is Crypto Up? Ether, HYPE, and Solana Lead Following US Grand Deal appeared first on Cryptonews.
Crypto World
Bitcoin holds steady above $74K as US blocks hormuz amid Iran talks

Key takeaways
- BTC is approaching $75,000 after adding nearly 5% to its value since Monday.
- The rally comes despite the ongoing crisis in the Middle East.
Bitcoin (BTC) has stabilized above $74,000 as of Tuesday’s press time, following a 5% rally the previous day. This price surge comes as the US enforces a blockade on the Strait of Hormuz during ongoing peace talks with Iran. US Vice President JD Vance hints at a grand deal in the works, demanding an end to Iran’s nuclear ambitions.
Market sentiment recovers with $500M in liquidations
The broader cryptocurrency market is seeing a recovery, with over $500 million in liquidations across the last 24 hours, primarily driven by short squeezes. Aave (AAVE), Algorand (ALGO), and Ethereum (ETH) are leading the charge in the market’s upward momentum.
As negotiations between the US and Iran progress, the US military has started blocking the Strait of Hormuz, halting the movement of transiting ships. Vice President JD Vance emphasized that the situation is now in Iran’s hands, with the primary focus of US talks being Iran’s nuclear material exit and halting uranium enrichment. Former President Donald Trump also commented that “the other side” has approached him for a deal.
The peace talks appear to be fueling a “risk-on” sentiment, especially in the cryptocurrency market. According to CoinGlass data, the last 24 hours saw $531 million in liquidations, with $426 million attributed to short liquidations. This massive short squeeze indicates a major bearish wipeout.
Bitcoin is approaching key resistance levels
The BTC/USD 4-hour chart remains bearish and efficient despite the recent rally. Bitcoin remains in a neutral-to-bullish trend, holding above its 50-day Exponential Moving Average (EMA) at $71,019. However, it is still capped below the 100-day EMA at $75,309.
Immediate resistance lies near the 100-day EMA and the 23.6% Fibonacci retracement level at $75,623, from a previous downtrend spanning $126,199 to $60,000. A daily close above this range would signal potential upward movement, with the next target being the 200-day EMA at $82,936, followed by the 50% Fibonacci retracement at $93,099.

Market momentum is favoring the bulls, with the Relative Strength Index (RSI) at around 62 and the Moving Average Convergence Divergence (MACD) in positive territory, both suggesting upward pressure is gaining traction.
On the downside, Bitcoin’s initial support is found at the 50-day EMA around $71,019. A break below this support could weaken the current bullish momentum and push the price lower, potentially testing the Fibonacci support level near $60,000.
Crypto World
STRC trading surge drives record volume and signals largest bitcoin purchase since launch
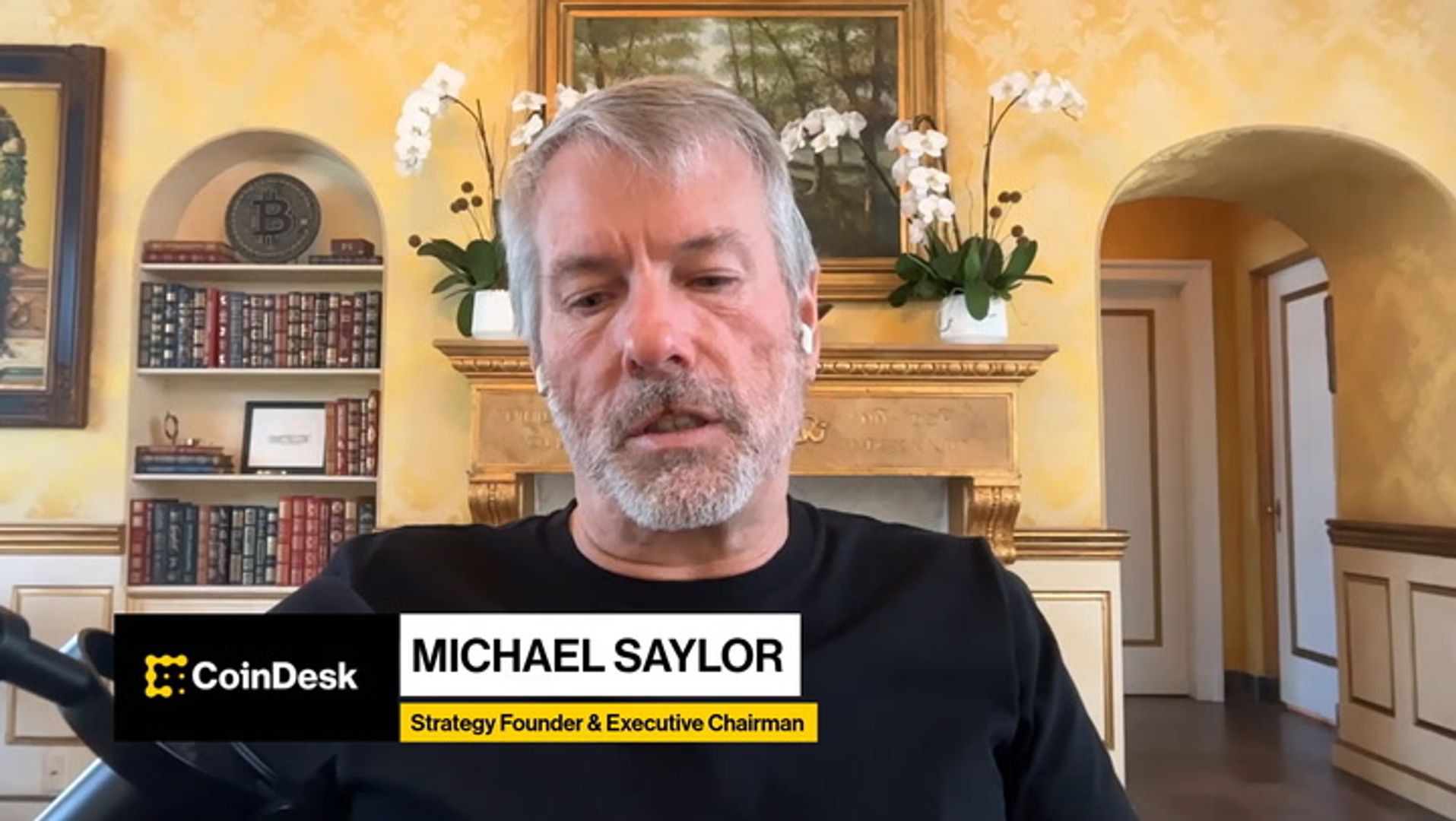
Stretch (STRC), the perpetual preferred security sold by Strategy (MSTR) to fund its bitcoin purchases, posted record trading volume on Monday, funding the biggest single-day buying splurge through the company’s at-the-market (ATM) program.
The world’s largest publicly traded bitcoin holder is estimated to have added 7,800 BTC, according STRC.live, as STRC volume surged to $1.16 billion, more than four times the 30-day average of $278 million.
This comes after Strategy purchased $1 billion worth of bitcoin last week, funded entirely by STRC, which offers an 11.5% annual dividend, paid monthly in cash. The stock maintained its $100 par value throughout the entire trading session.
Historically, the trading day preceding the ex-dividend date, the cutoff date after which new buyers are no longer entitled to the next dividend payment, tends to see the highest trading volume. That’s Wednesday, so it’s possible trading on Tuesday may be even higher than Monday’s record.
STRC now has a market capitalization of $6.4 billion, exceeding the combined market cap of the company’s other preferred securities, including STRD at $1.1 billion, STRK at $1 billion, and STRF at $1.2 billion, according to the MSTR dashboard.
The common stock rose 2.9% on Monday and was 3.7% higher in pre-market trading.
Read More: The one metric investors are overlooking in Michael Saylor’s Strategy
-

 Politics4 days ago
Politics4 days agoUS brings back mandatory military draft registration
-

 Sports4 days ago
Sports4 days agoMan United discover Nico Schlotterbeck transfer fee as defender reaches Dortmund agreement
-

 Fashion4 days ago
Fashion4 days agoWeekend Open Thread: Veronica Beard
-

 Tech7 days ago
Tech7 days agoHow Long Can You Drive With Expired Registration? What Florida Law Says
-
 Politics4 days ago
Politics4 days agoMalcolm In The Middle OG Turned Down ‘Buckets Of Money’ To Appear In Reboot
-

 Politics2 days ago
Politics2 days agoWorld Cup exit makes Italy enter crisis mode
-

 Crypto World5 days ago
Crypto World5 days agoCanary Capital Files SEC Registration for PEPE ETF
-

 Business4 days ago
Business4 days agoTesla Model Y Tops China Auto Sales in March 2026 With 39,827 Registrations, Beating Cheaper EVs and Gas Cars
-

 Fashion7 days ago
Fashion7 days agoLet’s Discuss: DEI in 2026
-

 Crypto World6 days ago
Crypto World6 days agoBitcoin recovers as US and Iran Agree a Ceasefire Deal
-

 Crypto World16 hours ago
Crypto World16 hours agoThe SEC Conditionalises DeFi Platforms to Be Avoided for Broker Registration
-

 NewsBeat2 days ago
NewsBeat2 days agoPep Guardiola and Gary Neville agree over Arsenal title problem that benefits Man City
-

 Crypto World13 hours ago
Crypto World13 hours agoSEC Signals Exemption for Crypto Interfaces From Broker Registration
-

 Business4 days ago
Business4 days agoOpenAI Halts Stargate UK Data Centre Project Over Energy Costs and Copyright Row
-

 Business3 days ago
Business3 days agoIreland Fuel Protests Enter Day 5 as Blockades Spark Shortages and Government Prepares Support Package
-

 Politics4 days ago
Politics4 days agoLBC Presenter Mocks Trump Over Iran War Failures
-

 Crypto World3 days ago
Crypto World3 days agoFederal judge blocks Arizona from bringing criminal charges against Kalshi
-
 Tech4 days ago
Tech4 days agoA version of Windows 10 released a decade ago is now eligible for additional security patches
-

 NewsBeat2 days ago
NewsBeat2 days agoJD Vance announces ‘no agreement’ with Iran over nuclear weapons fear
-
 Business3 days ago
Business3 days agoIMF retains floor for precautionary balances at SDR 20 billion



 Iran has offered to pause nuclear activity for up to 5 years but Trump wants 20 years.
Iran has offered to pause nuclear activity for up to 5 years but Trump wants 20 years.
 ⟁
⟁







You must be logged in to post a comment Login