Crypto World
AI Sparks Bug-Bounty Surge in Crypto, but Low-Quality Reports Grow
Crypto security programs are rethinking vulnerability disclosure as AI tools flood bug bounty submissions across the industry. While bug bounties reward researchers for responsibly flagging flaws, the surge in AI-assisted reports is both an aid and a challenge—helping teams comb through code faster, but also increasing false positives and noise.
Industry voices say AI-assisted analysis is changing how programs must triage and verify findings, a shift with potential implications for developers, operators, and users of decentralized protocols.
Key takeaways
- AI-enabled tooling is accelerating bug-bounty submissions, expanding both legitimate reports and noise that security teams must sort through.
- Cosmos Labs reports a roughly 900% jump in submission volume, translating to about 20–50 reports per day and a mix of valid findings and false positives.
- Leading researchers note rising low-quality submissions and AI-sourced noise, prompting calls for smarter triage and stricter reporting standards.
- Industry data from HackerOne indicates 85,000 valid bounty submissions in 2025, up 7% from 2024, underscoring growing engagement in bug bounty programs.
AI-driven flood tests bug bounty programs
Co-CEO Barry Plunkett of Cosmos Labs described a dramatic change in how bug bounty programs operate. “Our program has seen a 900% increase in submission volume from last year, on the order of 20–50 per day,” he said, noting that the influx encompasses both credible vulnerability reports and a significant amount of noise. The volume surge has pushed teams to deploy more stringent triage and verification workflows to separate real threats from false alarms.
Across other organizations, developers have reported a similar pattern. Kadan Stadelmann, CTO at Komodo Platform, told Cointelegraph that bug bounty submissions and payouts have risen notably, with a noticeable uptick in low-quality reports and false positives. He suggested that AI-driven tooling may be lowering the cost of producing vulnerability submissions, thereby fueling the higher throughput.
The phenomenon isn’t isolated to crypto software. In January, Daniel Stenberg, the creator of curl—a widely used open-source tool responsible for data transfers in many blockchain infrastructures—announced he would end his personal bug bounty program due to an overwhelming tide of “AI slop in vulnerability reports,” making it exhausting to sift through submissions.
HackerOne, one of the largest bug bounty platforms, also highlighted the broader trend, reporting that 85,000 valid bounty submissions were filed in 2025, up 7% from the previous year. The data underscores how AI-enabled automation is reshaping the volume and pace at which researchers engage with security programs.
AI could be both the cause and the solution
Cosmos Labs has begun adapting in response to the surge by tightening its scoring framework and prioritizing trusted researchers with proven track records. Plunkett said the team is collaborating with other bug bounty providers that offer more advanced triage capabilities, aiming to separate signal from noise more efficiently as volumes rise.
Stadelmann similarly underscored the potential of defensive AI to help teams withstand the deluge. “Blockchain teams will have to create AI deterrents to sift through incoming bug bounties. The smaller the team, the bigger the problem of increased bug bounties will become. Software engineers won’t have the capacity to examine everything,” he cautioned. A defensive AI approach could automatically filter and rank reports, reducing the burden on human reviewers.
“This is where defensive AI systems to automatically sift through incoming bug bounties will be crucial. Teams dependent on bug bounties will need to develop stricter standards on their bug bounty programs as a means of lowering the number of incoming reports.”
Taken together, the episode highlights a central tension in bug bounty ecosystems: AI can amplify vigilance by widening the net for vulnerability discovery, but it can also swamp teams with untenable volumes of reports. The path forward appears to hinge on smarter triage tools, more rigorous reporter verification, and standardized quality controls across platforms.
What this means for developers and ecosystems
Bug bounty programs have long been a cornerstone of security for decentralized networks, offering a carrot for researchers to disclose flaws before attackers can exploit them. The current spike in AI-assisted submissions tests the sustainability of those programs, especially for teams with limited security staff. The emerging consensus among practitioners is that AI will be a necessary ally, but only if paired with robust triage protocols and tighter verification standards.
For builders and operators, the development suggests several practical shifts: invest in AI-enabled triage that can coarsely filter reports, cultivate a trusted researcher network to fast-track credible findings, and align with bounty providers that offer deeper automated review capabilities. These moves can help ensure that the bounty ecosystem remains a reliable line of defense rather than a flood of trivial or erroneous submissions.
As the industry experiments with stronger screening and smarter automation, observers will want to watch for how quickly bug bounty platforms roll out standardized quality controls and how crypto projects adapt incentive structures to maintain high signal-to-noise ratios. The degree to which smaller teams can implement effective defensive AI and whether regulators begin to steer disclosure practices will shape the resilience of crypto security in the near term.
Readers should stay tuned for updates on AI-driven triage innovations, platform policy changes, and real-world outcomes from ongoing vulnerability disclosures across leading DeFi and non-DeFi protocols.
Looking ahead, the balance between rapid vulnerability discovery and manageable review workloads will determine how bug bounty programs influence security in an increasingly automated landscape. The next few quarters could define whether AI remains a force multiplier for defense or becomes a bottleneck that teams must outpace with smarter tooling and stricter reporting standards.
Crypto World
Lazarus Group Malware Targets Crypto, Business Execs via macOS
Security researchers have linked a new macOS malware campaign to the Lazarus Group, the North Korea-linked hacking operation behind some of the crypto industry’s biggest thefts.
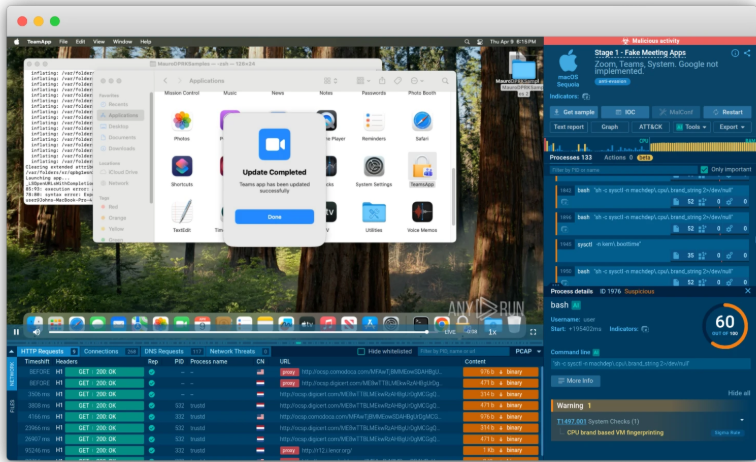
Flagged on Tuesday, the new “Mach-O Man” malware kit is distributed via “ClickFix” social engineering schemes across traditional businesses and crypto companies, according to Mauro Eldritch, offensive security expert and founder of threat intelligence company BCA Ltd.
Victims are lured into a fake Zoom or Google Meet call where they are prompted to execute commands that download the malware in the background, allowing attackers to bypass traditional controls without detection to gain access to credentials and corporate systems, the security researcher said in a Tuesday report.
Researchers said the campaign can lead to account takeovers, unauthorized infrastructure access, financial losses and the exposure of critical data, underscoring how Lazarus continues to expand its targeting beyond crypto-native companies.
The Lazarus Group is the main suspect in some of the largest-ever cryptocurrency hacks, including the $1.4 billion hack of Bybit exchange in 2025, the industry’s largest so far.

“Mach-o Man” kit seeks to implement hidden stealer malware
The final stage of the campaign is a stealer designed to extract browser extension data, stored browser credentials, cookies, macOS Keychain entries and other sensitive information from infected devices.

After collection, the data is archived into a zip file and exfiltrated through Telegram to the attackers. Finally, the malware’s self-deletion script removes the entire kit using the system’s rm command, which bypasses user confirmation and permissions when removing files.
The novel malware kit was reconstructed by the security expert through cloud-based malware sandbox Any.run’s macOS analysis capabilities.
Related: CZ sounds alarm as ‘SEAL’ team uncovers 60 fake IT workers linked to North Korea
Earlier in April, North Korean hackers used AI-enabled social engineering schemes to steal about $100,000 worth of funds from crypto wallet Zerion, after gaining access to some team members’ logged-in sessions, credentials and the company’s private keys, Cointelegraph reported on April 15.
Magazine: 53 DeFi projects infiltrated, 50M NEO tokens could be ‘given back’: Asia Express
Crypto World
RaveDAO’s vertical day sits on top of a 95% crash scandal
RaveDAO (RAVE) is up about 106% on $418m volume after a 95% crash that erased nearly $6b, as ZachXBT alleges insiders ran a pump‑and‑dump and OKX funds the probe.
Summary
- RaveDAO (RAVE) is trading around $1.27, up roughly 106% in 24 hours with about $418 million in volume, a parabolic move driven almost entirely by narrative and flow.
- Structurally, today’s candle looks like a late‑stage momentum blow‑off: vertical price, volume exceeding or matching market cap, and likely extreme intraday overbought readings.
- The spike comes just days after a 95% crash from roughly $26 to near $1 that prompted OKX to fund ZachXBT’s investigation into alleged insider manipulation around RAVE.
RaveDAO is in full trader mode. CoinGecko and major exchanges show RAVE near $1.27, up about 106% on the day, with roughly $418 million in 24‑hour turnover — enough to rank among the top gainers on the market and to push daily volume to parity or above its entire market capitalization.
On the chart, this is a classic vertical session: multi‑X intraday range, most of the candle body glued near the highs, which technicians treat as textbook late‑stage momentum, not a calm trend extension.
As Yellow’s recent note put it after a similar spike, “daily volume exceeded market cap by approximately 22%,” and in that context “tokens rarely sustain gains beyond 72 hours” before mean‑reverting.
Derivatives data tell the same story. CoinGlass tracks RAVE futures with open interest swelling sharply into big days and then partially washing out as late longs get liquidated, a pattern consistent with “100% daily moves” driven by leveraged chase rather than organic spot demand.
Overlay a 1‑hour to 4‑hour RSI heatmap on a move like this and you are almost certainly looking at readings in the 80–90+ band — extreme overbought, which in practice usually precedes a cooling phase or outright reversal rather than another clean leg higher.
All of this is happening against a very ugly backdrop. As detailed in a recent crypto.news story, RAVE previously exploded about 11,000% from roughly $0.25 to around $27.33 in under two weeks before crashing roughly 95% back to near $1, wiping out almost $6 billion in paper market cap.
On‑chain investigator ZachXBT has alleged that “wallets linked to early distribution controlled about 95% of RAVE’s 1 billion token supply,” calling the pattern “a textbook pump and dump” and arguing that the mismatch between value lost and just $52 million in liquidations “is not normal in a healthy market structure.”
OKX founder Star Xu has since pledged an extra $25,000 toward ZachXBT’s bounty, saying the exchange’s “risk engine is monitoring the situation closely” and that OKX would “support any efforts to uncover insider abuse and protect users,” while Bitget and Binance have launched internal reviews.
In trading terms, that makes today’s parabolic bounce even more clearly a speculator’s playground than an investor’s setup.
Short‑term mean‑reversion probabilities are rising; the risk skew is toward a sharp retrace once open interest stops climbing and intraday RSI rolls over, with seasoned traders typically fading strength — not weakness — when volume starts to slow and price begins to chop at the top of the range.
Crypto World
WalletConnect Integrates with TradFi-Focused Chain Canton Network


WalletConnect’s ecosystem of 700 crypto wallets and 70,000 dApps now supports the enterprise- and privacy-focused blockchain network.
WalletConnect has added support for Canton Network, a blockchain built for institutional finance. The two companies first revealed the partnership at EthCC in Cannes, during a panel moderated by The Defiant’s senior editor Olivia Capozzalo, before releasing the news publicly today, April 22.
The deal aims to bring Canton’s privacy-focused infrastructure to WalletConnect’s global ecosystem, enabling access to stablecoin payments, tokenized real-world assets, and DeFi applications. According to a press release viewed by The Defiant, the crypto infrastructure firm’s ecosystem supports 700 crypto wallets, 70,000 decentralized applications, and 55.5 million users, all of which can now connect to the protocol, which is within the top-20 chains by market cap, per CoinGecko.
Canton currently boasts over $8 trillion in tokenized assets processed monthly and more than $350 billion in U.S. Treasuries settled daily, per the release.
Data from RWAxyz shows that all of the nearly $330 billion in tokenized RWAs on Canton are represented asset value, meaning they use the blockchain for recordkeeping and operational efficiency, but don’t allow for on-chain distribution.
WalletConnect CEO Jess Houlgrave framed Canton’s privacy model as “a requirement for institutions to work at scale.”
The announcement arrives, however, amid an ongoing debate over Canton’s self-description as a “public, permissionless blockchain” — a characterization many in the industry contest. As The Defiant has reported, critics argue that Canton is closer to a permissioned database than a true blockchain, with validator admission controlled by a governance committee of incumbent institutions.
Canton has been accumulating serious institutional momentum in recent months. JPMorgan’s USD-denominated deposit token is set to be issued natively on Canton in phases throughout 2026, as The Defiant reported, and the DTCC selected Canton to tokenize a subset of U.S. Treasury securities it holds, citing the platform’s privacy features, per The Defiant’s earlier coverage.
The broader race for institutional-grade privacy is heating up on multiple fronts: Boundless, a ZK proving network, recently integrated with the XRP Ledger to bring native zero-knowledge proof verification to the Layer 1 for the first time, enabling institutions to build financial applications on XRPL that execute privately while maintaining regulatory compliance, as The Defiant reported.
This article was written with the assistance of AI workflows. All our stories are curated, edited and fact-checked by a human.
Crypto World
Mostbet uz kirish: bonus qo‘llanmasi



1. Mostbet ga ro‘yxatdan o‘tish: bosqichma‑bosqich
Mostbet uz kirish uchun avvalo ro‘yxatdan o‘tish kerak. Saytning asosiy sahifasida “Ro‘yxatdan o‘tish” tugmasini bosganingizda, sizga oddiy forma taqdim etiladi – ism‑familiyangiz, elektron pochta manzilingiz, telefon raqamingiz va parol.
Ma’lumotlarni kiritgandan so‘ng, tasdiqlash kodi SMS orqali keladi. Kodingizni kiritgandan keyin hisobingiz aktivlanadi va darhol kirish imkoniyati paydo bo‘ladi. Agar sizga qo‘shimcha yordam kerak bo‘lsa, mostbet uz sahifasida “Yordam” bo‘limiga murojaat qilishingiz mumkin.
2. Kirish va hisobga kirish usullari
Kirish jarayoni juda soddadir: foydalanuvchi nomi (yoki elektron pochta) va parolni kiritish kifoya. Ba’zi foydalanuvchilar mobil telefon orqali “SMS kod” bilan kirishni afzal ko‘rishadi, bu usul qo‘shimcha xavfsizlik qatlamini qo‘shadi.
Agar parolingizni unutgan bo‘lsangiz, “Parolni tiklash” tugmasini bosib, ro‘yxatdan o‘tgan telefon yoki email manziliga yuborilgan havolani kuzatib, yangi parol yaratishingiz mumkin. Kiritilgan ma’lumotlar har doim himoyalangan, SSL sertifikati orqali shifrlanadi.
3. Bonuslar va aksiyalar – boshlovchilar uchun foydali tavsiyalar
Mostbet uz kirish bilan birga, yangi foydalanuvchilarga “Welcome Bonus” taklif etiladi. Bu bonusning asosiy sharti – birinchi depozitni kamida 10 000 so‘m miqdorida amalga oshirish.
Bonusni olishdan oldin, “Wagering requirements” (bet o‘ynash talablari) ni diqqat bilan o‘rganing. Masalan, 5 x bonus miqdori talab qilinadi, ya’ni siz bonusni 5 marta o‘yinlarda qayta tiklashingiz kerak. Bu talabni bajarganingizdan so‘ng, nafaqat bonus, balki yutgan pul ham hisobga qo‘shiladi.
4. To‘lov usullari va pul yechish tezligi
Mostbet o‘z mijozlariga keng to‘lov tizimlari to‘plamini taklif etadi. O‘zbekiston foydalanuvchilari uchun qulay variantlar: Click, Payme, Uzcard, Visa/Mastercard.
Yechish jarayoni odatda 10‑30 daqiqada amalga oshadi, lekin bu tanlangan usulga qarab farq qiladi. Ba’zi usullarda kun oxirigacha to‘lovni kutish kerak bo‘lishi mumkin.
| Usul | Minimal depozit | Qayta ishlash vaqti | Komissiya |
|---|---|---|---|
| Click | 10 000 so‘m | 1‑5 daqiqa | Yo‘q |
| Payme | 5 000 so‘m | 3‑10 daqiqa | 0,5 % |
| Uzcard | 10 000 so‘m | 5‑15 daqiqa | Yo‘q |
| Visa/Mastercard | 20 000 so‘m | 10‑30 daqiqa | 1 % |
5. Mobil ilova va live casino tajribasi
Mostbet mobil ilovasi Android va iOS platformalarida mavjud. Ilova orqali siz nafaqat sportga, balki live casino o‘yinlariga ham real vaqt rejimida kirishingiz mumkin. Live dealerlar bilan o‘ynash, kartalar yoki rulet stollarida qatnashish, mobil qurilmangizdan ham professional darajadagi tajriba taqdim etadi.
Ilova interfeysi intuitiv, bir necha bosqichda depozit va pul yechish imkoniyatlari ham mavjud. Push-xabarlar orqali yangi bonuslar va turnirlar haqida xabar olish, foydalanuvchini doimo yangiliklardan habardor qiladi.
6. Mijozlarni qo‘llab‑quvvatlash va xavfsizlik
Mostbet uz kirish bilan bog‘liq savollarni 24/7 jonli chat, email va telefon orqali hal qilish mumkin. Mijozlarga xizmat ko‘rsatish jamoasi ko‘p tilli, shu jumladan o‘zbek tilida ham yordam beradi.
Xavfsizlik nuqtai nazaridan, sayt litsenziyali va regulatsiyalangan. Barcha foydalanuvchi ma’lumotlari shifrlanadi, KYC (Know Your Customer) protseduralari orqali firibgarlik va kimlik o‘g‘irlashga qarshi himoya amalga oshiriladi.
7. Qonunchilik, litsenziya va mas’uliyona gambling
Mostbet Curacao licensiyasiga ega bo‘lib, xalqaro standartlarga mos keladi. O‘zbekiston qonunchiligiga muvofiq, sayt faqat yoshi 18 yoshdan yuqori bo‘lgan foydalanuvchilar uchun mo‘ljallangan.
Mas’uliyona gambling bo‘limida o‘yinchilarga limitlar, o‘yin vaqtini nazorat qilish va o‘z hisobini o‘chirib tashlash imkoniyatlari beriladi. Bu, foydalanuvchilarni ortiqcha qimor o‘ynashdan saqlashga yordam beradi.
8. Tez-tez beriladigan savollar (FAQ)
- Mostbet uz kirish uchun minimal yosh qancha? 18 yoshdan katta bo‘lishi shart.
- Bonusni qanday olish mumkin? Birinchi depozitni amalga oshirganingizdan keyin avtomatik tarzda welcome bonus beriladi.
- Pul yechish uchun qancha vaqt kerak? Tanlangan to‘lov usuliga qarab 10‑30 daqiqada.
- Mobil ilova orqali o‘yin o‘ynash bepulmi? Ilova orqali o‘ynash bepul, lekin haqiqiy pul bilan o‘yinlar uchun depozit talab qilinadi.
Ushbu qo‘llanma “mostbet uz kirish” haqida barcha asosiy ma’lumotlarni qamrab oladi. Sizga muvaffaqiyatli o‘yinlar, foydali bonuslar va xavfsiz to‘lov operatsiyalari tilaymiz!
Crypto World
UK FCA raids eight illegal peer-to-peer trading hubs


The U.K.’s Financial Conduct Authority (FCA) has carried out its first coordinated crackdown on illegal peer-to-peer crypto trading, targeting eight locations across London in a joint operation with His Majesty’s Revenue & Customs (HMRC) and the South West Regional Organised Crime Unit (SWROCU).
Officials issued cease-and-desist notices at each site and gathered evidence that is now feeding into several criminal investigations, according to the FCA.
The FCA stated that the sites were suspected of facilitating peer-to-peer (P2P) crypto trading, where individuals buy and sell crypto directly with one another, without the required registration or anti-money laundering controls.
Under U.K. law, anyone operating as a crypto exchange provider must register with the FCA. The regulator confirmed there are currently no registered peer-to-peer crypto traders or platforms in the country.
“Unregistered peer-to-peer crypto traders operating in the U.K. are doing so illegally and pose a financial crime risk,” said Steve Smart, the FCA’s executive director of enforcement and market oversight.
Law enforcement agencies framed the operation as part of efforts to cut off routes used to move illicit funds. DI Ross Flay of SWROCU said unregistered traders can enable criminals to “move, disguise and spend illegal money.”
The action builds on earlier enforcement steps. The FCA has prosecuted operators of illegal crypto ATMs for several years and worked with police to arrest individuals linked to an unregistered crypto exchange in 2024.
Last year, it also took action against offshore platform HTX over unlawful financial promotions and expanded oversight of social media figures promoting high-risk crypto products.
The crackdown comes as the UK prepares to roll out a broader regulatory regime for crypto by October 2027, with a licensing window expected to open in September 2026. The current framework focuses mainly on anti-money laundering compliance and financial promotions.
The FCA urged consumers to check whether firms are registered using its online register. It also warned that users dealing with unregistered P2P traders lack access to the Financial Ombudsman Service or compensation schemes and may face risks if transactions involve stolen funds.
Crypto World
CoinGecko Launches Market Intelligence Tools and Partner Platform
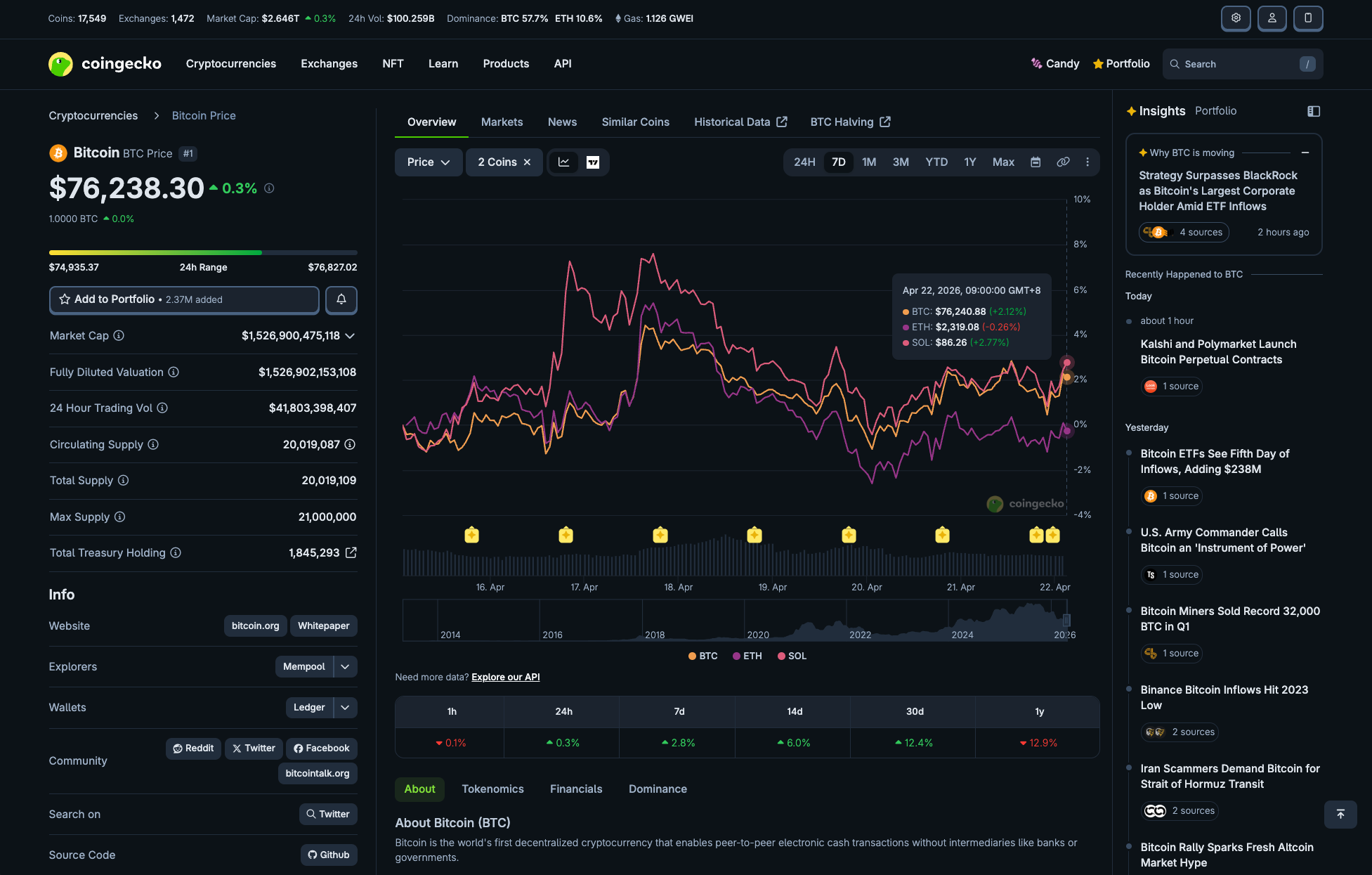
CoinGecko announced a major product expansion this week, adding market intelligence features and a unified Partner Platform to its crypto data aggregator.
The Singapore-based company said the update reflects a shift from pure price tracking toward contextual analysis for investors and growth infrastructure for Web3 projects.
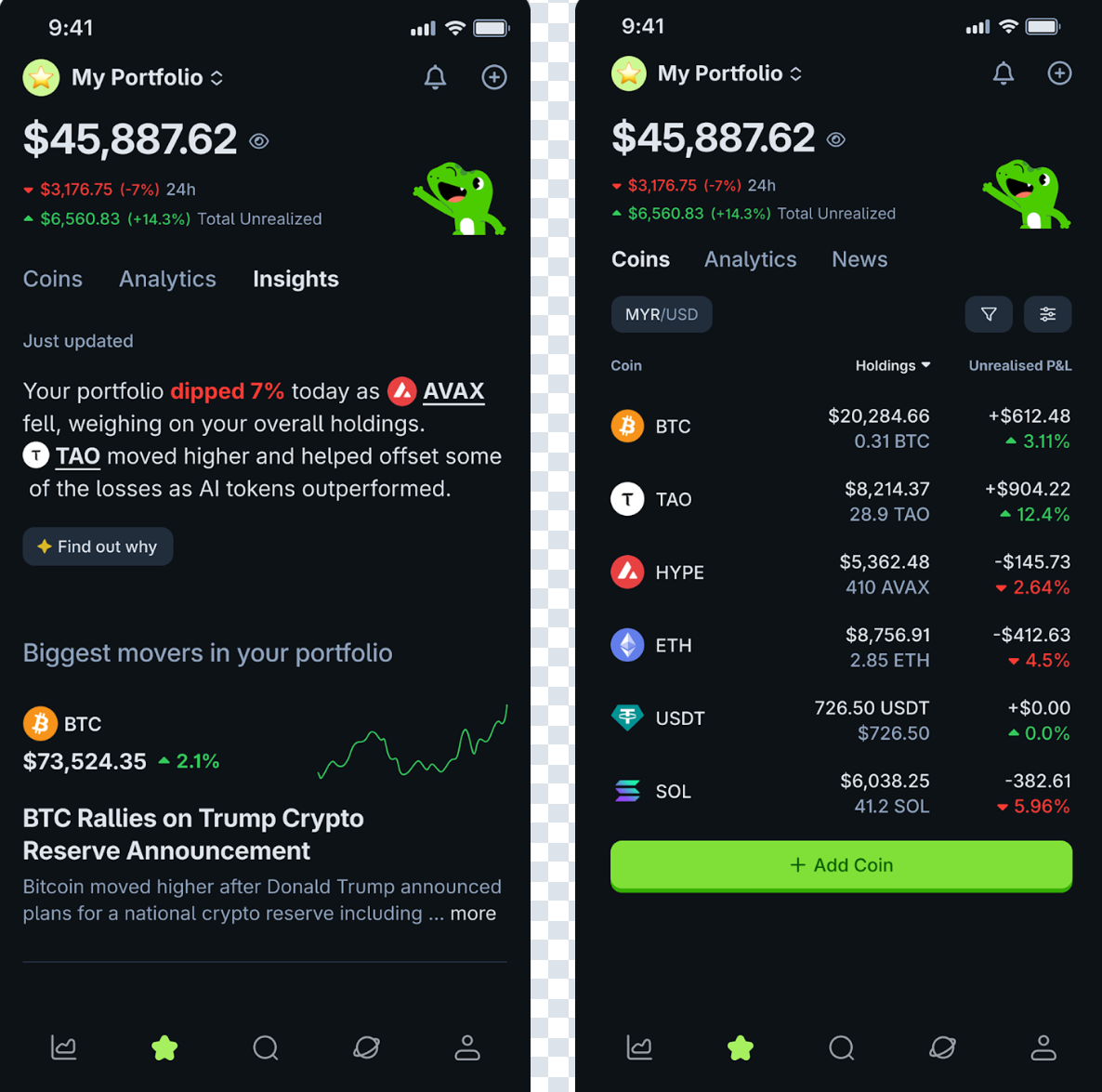
AI-Powered Insights and Advanced Charting
CoinGecko’s new Market Insights feature aggregates signals from news and social media discussions, then uses AI-generated summaries to explain what is driving price movements across coins and categories.
The company also introduced Advanced Charts, which let users compare price movements across multiple cryptocurrencies in a single view.
Charts are shareable and downloadable, giving investors tools previously limited to expensive terminals.
“Better data leads to better decisions, but today, data alone isn’t enough. Context is the missing layer, and that’s what we’re building,” read an excerpt in the announcement, citing Bobby Ong, co-founder and CEO of Coingecko, highlighting how the crypto market has outgrown basic data displays.
Follow us on X to get the latest news as it happens
The third consumer feature, Portfolio Insights, consolidates wallet tracking across EVM-compatible networks.
It shows profit-and-loss metrics and average buy prices, with AI-generated summaries that explain what is driving portfolio changes. Multichain support is expected in the coming months.
Partner Platform Targets Crypto Project Growth
For crypto projects, CoinGecko launched a Partner Platform that combines listing management, advertising campaigns, and performance tracking across both CoinGecko and GeckoTerminal.
The platform serves over 30 million monthly visitors and millions more on GeckoTerminal. Projects can submit listings, update token information, and use tools like Fast Pass to speed up time-to-listing.
CoinGecko plans to add deeper analytics, including pageview and watchlist data, in future updates.
The expansion follows a period of leadership restructuring and renewed product investment at CoinGecko.
With over 36 million tokens now tracked across hundreds of blockchains, the company is positioning itself as both a consumer intelligence layer and a distribution channel for the projects building on those networks.
The post CoinGecko Launches Market Intelligence Tools and Partner Platform appeared first on BeInCrypto.
Crypto World
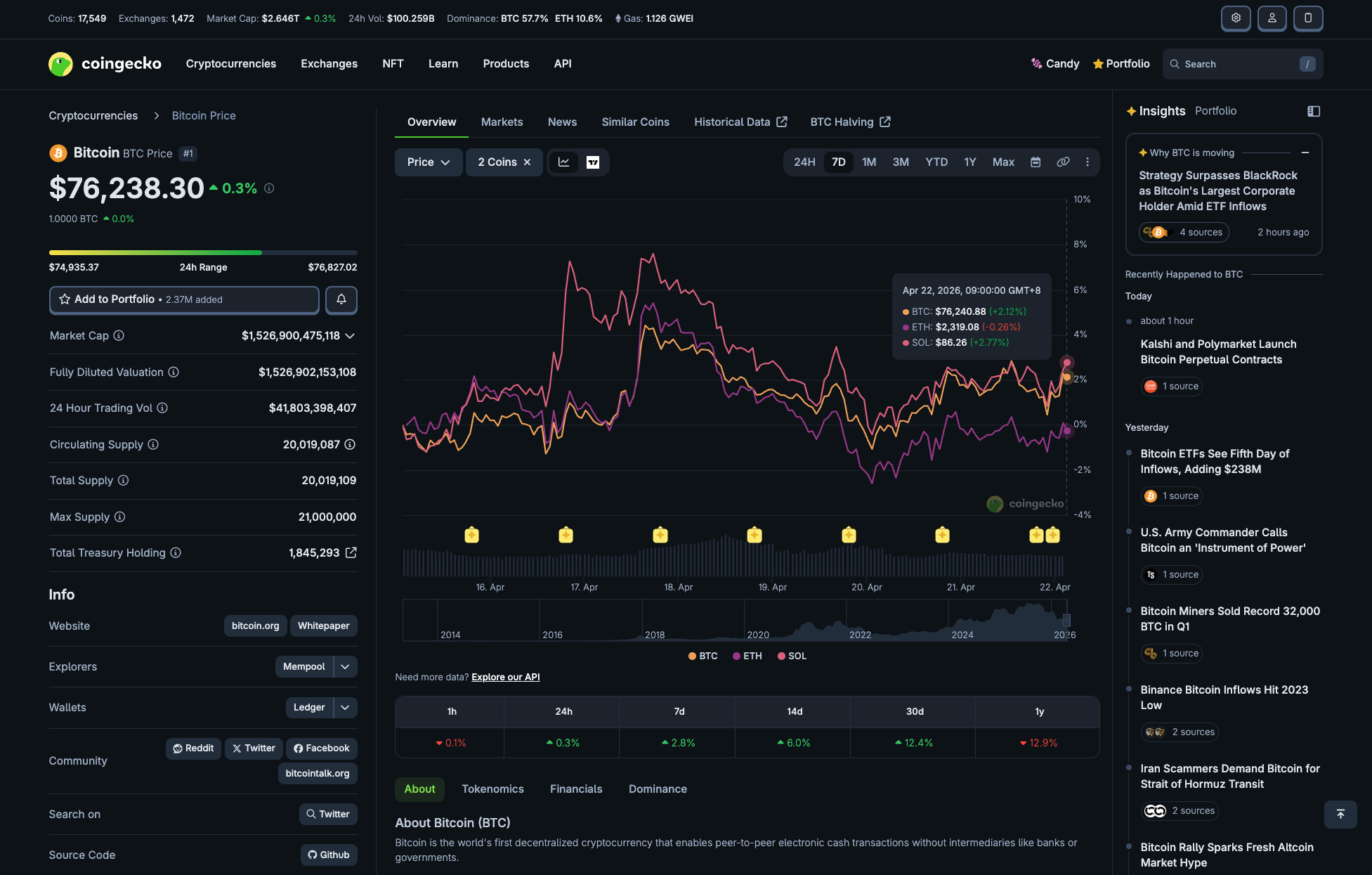
BitMEX Launches the Trading Circuit Campaign Featuring a 100,000 USDT Weekly Prize Pool

BitMEX, one of the safest crypto exchanges, announced today the launch of its Trading Circuit Campaign, allowing traders to win their share of a weekly 100,000 USDT prize pool by completing a series of trading missions.
The campaign will run from 22 April 2026 at 12:00 PM (UTC) to 13 May 2026 at 11:59 PM (UTC). Users can participate at any time during the campaign period.
Rewards will be distributed across 3 categories:
- The Running Start: All traders can claim up to $300 in rewards by reaching trading volume targets.
- The Top Traders’ Edge: By placing in the top 20 for trading volume on selected contracts, participants can claim up to $200 in rewards.
- The Sprinters’ Bonus: All participants who achieve at least two tiers for all three weeks of the campaign’s duration can claim an annual TradingView Plus subscription.
To participate in the Trading Circuit Campaign, traders must be fully verified on BitMEX. Competition details and registration can be found here.
About BitMEX
BitMEX is the OG crypto derivatives exchange, providing professional crypto traders with a platform that caters to their needs through low latency, deep crypto native liquidity and unmatched reliability.
Since its founding, no cryptocurrency has been lost through intrusion or hacking, allowing BitMEX users to trade safely in the knowledge that their funds are secure. So too that they have access to the products and tools they require to be profitable.
BitMEX was also one of the first exchanges to publish their on-chain Proof of Reserves and Proof of Liabilities data. The exchange continues to publish this data twice a week – proving assurance that they safely store and segregate the funds they are entrusted with.
For more information on BitMEX, please visit the BitMEX Blog or www.bitmex.com, and follow Telegram, Twitter, Discord, and its online communities. For further inquiries, please contact press@bitmex.com.
The post BitMEX Launches the Trading Circuit Campaign Featuring a 100,000 USDT Weekly Prize Pool appeared first on BeInCrypto.
Crypto World
Justin Sun sues World Liberty Financial for freezing his 2.94B WLFI tokens


- Justin Sun says WLFI froze 2.94 billion tokens and removed voting rights.
- Lawsuit filed after failed attempts to resolve the dispute privately.
- WLFI has introduced a Governance proposal that may lock tokens for non-consenting holders.
Justin Sun has filed a lawsuit in a California federal court against World Liberty Financial (WLFI), alleging that the project froze his holdings of 2.94 billion WLFI tokens and stripped him of key investor rights without justification.
The move escalates a growing dispute between one of crypto’s most recognisable entrepreneurs and a project that has positioned itself around decentralised governance and early-stage token distribution.
In his public statement, Sun confirmed that he is seeking legal protection of his rights as a WLFI token holder.
Sun also emphasised that the lawsuit does not change his political stance or his support for the Trump administration’s pro-crypto direction. According to him, the dispute is strictly about investor treatment and token governance, not politics.
Frozen tokens and removed voting rights
At the centre of the case is Sun’s claim that WLFI froze all 2.94 billion of his tokens (540 million of unlocked tokens and 2.4 billion locked tokens). He argues that this action made it impossible for him to transfer, sell, or otherwise use his holdings.
The value of the holdings has dropped from over $107 million at the September 2025, when they were frozen, to around $43–$60 million by April 2026.
Sun also alleges that WLFI removed his governance voting rights tied to those tokens. This means he was unable to participate in key decisions affecting the protocol, including recent governance changes introduced by the project team.
Sun further claims that WLFI went beyond freezing his position and threatened to permanently destroy part of his holdings through token “burning.”
According to his statement, these actions were taken without clear justification and without providing him a fair opportunity to respond.
He also says he attempted to resolve the issue privately with WLFI before taking legal action. However, he claims the project team refused to restore access to his tokens or reinstate his governance rights, leaving him with no option but to proceed to court.
Sun has described his position as straightforward: he wants to be treated the same as other early investors who received WLFI tokens, without special privileges and without restrictions that are not applied equally.
Justin Sun also disagrees with WLFI’s Governance proposal
The legal conflict comes alongside disagreement over a WLFI governance proposal released on April 15.
Sun has openly opposed the proposal, arguing that it introduces conditions that could lock users’ tokens indefinitely if they do not actively accept new terms.
The proposal reportedly includes a requirement for 10% of advisor tokens to be permanently burned. It also introduces a structure for early purchaser tokens involving a two-year cliff followed by a two-year vesting schedule.
Under the same framework, users who do not explicitly accept the new terms could have their tokens locked indefinitely.
Sun has raised concerns that this creates an uneven system where investor rights depend on active consent after the fact. He also pointed out a structural conflict in his own situation.
Because his tokens are currently frozen, he says he cannot vote either in favour of or against the proposal, despite being directly affected by it.
This has added another layer to the dispute, as governance participation is typically considered a core function in token-based systems.
World Liberty Financial (WLFI) position
WLFI has pushed back against Sun’s claims, arguing that token restrictions were applied due to internal concerns related to security and compliance.
The project maintains that its governance mechanisms include administrative controls that can be used to protect the platform and its participants.
The disagreement highlights a broader tension in crypto governance systems, particularly in projects that market themselves as decentralised while still retaining centralised control features such as token freezing or administrative overrides.
Sun’s lawsuit places the focus on whether such controls were properly disclosed and whether they can be applied to large early investors without clear procedural safeguards.
With 2.94 billion tokens at the centre of the dispute, the outcome could influence how governance authority and investor rights are interpreted in similar token-based ecosystems going forward.
Crypto World
How UK investors can now hold crypto in their ISAs once more


Investors in the U.K. can once again hold cryptocurrency exchange-traded notes (ETNs) in a tax-free vehicle after fintech startup Stratiphy received approval to offer them in a special class of individual savings account (ISA), according to a report by the Financial Times on Wednesday.
Stratiphy, a fintech platform that allows users to personalize their investment strategies, is offering both crypto ETNs and Innovative Finance ISAs (IFISAs), the wrapper authorized to invest in them, the FT reported.
ISAs allow users to save up to 20,000 pounds ($27,000) a year without paying income tax or capital gains tax on the returns. The two most common types are cash ISAs, which pay interest, and stocks and shares ISAs, which invest in equities and exchange-traded instruments.
At the end of February, the U.K.’s tax authority, His Majesty’s Revenue and Customs (HMRC), classified crypto ETNs as instruments only available in IFISAs from the start of the current tax year on April 6.
This essentially made last year’s decision to lift the ban on retail users accessing crypto ETNs redundant because no mainstream investment platform offered IFISAs. The few that did had no plans to offer crypto products.
The decision drew criticism from some commentators, who said it risked making the U.K. an outlier among markets where exchange-traded products (ETPs) have made crypto investment available to a far broader base of retail investors.
Stratiphy will offer access to three ETNs provided by 21Shares: those covering bitcoin , ether (ETH) and one combining BTC and gold.
The London-based investment platform, which opened for business in August last year, manages 4 million pounds ($5.4 million) for 2,000 retail and corporate clients.
“We see a disproportionate level of interest in these [crypto] products,” CEO Daniel Gold said, according to the newspaper.
“It’s a really interesting way to diversify your portfolio. It’s a new asset class with low correlation to other asset classes.”
Stratiphy did not immediately respond to CoinDesk’s request for comment.
Crypto World
Crypto giant GSR launches its first ETF to give investors an easy way to bet on the big three


Crypto trading firm GSR has launched its first exchange-traded fund (ETF), entering a fast-growing segment of the digital asset market as investor demand for regulated crypto exposure continues to rise.
The GSR Crypto Core3 ETF, trading under the ticker BESO on Nasdaq, offers exposure to three major cryptocurrencies, including bitcoin , ether (ETH) and solana (SOL). The fund carries a 1% management fee and includes both active portfolio management and the ability to earn staking rewards on eligible assets.
The launch comes as crypto ETFs have gained traction with both retail and institutional investors seeking easier access to digital assets through traditional brokerage accounts. While most U.S.-listed crypto ETFs to date have focused on single assets, particularly bitcoin, some have moved to basket funds, similar to Core3, which bundles multiple tokens into a single product and adjusts allocations on a weekly basis.
GSR said the fund aims to reflect two main themes in crypto markets: bitcoin’s role as a macro asset and the growth of blockchain platforms such as Ethereum and Solana, which support applications like stablecoins and tokenized assets.
“The fund allocates actively across the three assets and rebalances weekly based on research-driven signals designed to pursue additional returns,” GSR said in a press release.
Framework Digital Advisors will serve as the fund’s investment adviser.
The move expands GSR’s business beyond trading and market making into asset management.
The firm has spent more than a decade providing liquidity and over-the-counter trading services in crypto markets and is now looking to package that expertise into investment products.
The ETF also introduces staking rewards, a feature not commonly available in traditional investment vehicles but one that has been added to some existing crypto ETFs, including the largest, BlackRock’s iShares Bitcoin Trust (IBIT). This feature the fund to generate yield from certain blockchain networks while holding assets.
“GSR has spent over a decade building efficient crypto markets, and with Core3, we are extending that expertise into a product accessible to a broader range of investors,” GSR CEO Xin Song said.
-

 Fashion5 days ago
Fashion5 days agoWeekend Open Thread: Theodora Dress
-

 Sports5 days ago
Sports5 days agoNWFL Suspends Two Players Over Post-Match Clash in Ado-Ekiti
-

 Politics5 days ago
Politics5 days agoPalestine barred from entering Canada for FIFA Congress
-
Entertainment3 days ago
NBA Analyst Charles Barkley Chimes in on Ice Spice McDonald’s Fiasco
-

 Business3 days ago
Business3 days agoPowerball Result April 18, 2026: No Jackpot Winner in Powerball Draw: $75 Million Rolls Over
-

 Crypto World5 days ago
Crypto World5 days agoRussia Pushes Bill to Criminalize Unregistered Crypto Services
-

 Tech4 days ago
Tech4 days agoAuto Enthusiast Scores Running Tesla Model 3 for Two Grand and Turns It Into Bare-Bones Go-Kart
-
 Politics3 days ago
Politics3 days agoZack Polanski demands ‘council homes not luxury flats for foreign investors’
-
 Politics2 days ago
Politics2 days agoGary Stevenson delivers timely reminder to register to vote as deadline TODAY
-

 Tech7 days ago
Tech7 days ago‘Avatar: Aang, The Last Airbender’ Leaked Online. Some Fans Say Paramount Deserves the Fallout
-

 Business6 days ago
Business6 days agoCreo Medical agree sale of its manufacturing operation
-

 Business6 hours ago
Business6 hours agoRolls-Royce Voted UK’s Most Iconic Trade Mark as IPO Register Hits 150
-

 Crypto World5 days ago
Crypto World5 days agoRussia Introduces Bill To Criminalize Unregistered Crypto Services
-

 Crypto World4 days ago
Crypto World4 days agoKelp DAO rsETH Bridge Hack Drains $292M as DeFi Losses Top $600M in Two Weeks
-

 Sports6 days ago
Sports6 days agoBritish climbers complete new route in Swiss Alps
-

 Tech6 days ago
Tech6 days agoFord EV and tech chief leaving automaker
-

 Sports6 days ago
Sports6 days ago“Felt Much Better Today”: Josh Hazlewood Opens Up On His Recovery Win Over LSG
-

 Entertainment7 days ago
Entertainment7 days agoRuby Rose Accuses Katy Perry Of Sexual Assault, Police React
-

 Business6 days ago
Business6 days agoCheaper Doritos and Lays helps PepsiCo win back struggling snackers
-

 Entertainment6 days ago
Entertainment6 days agoClavicular Says Streaming May Not Work Without Substances










You must be logged in to post a comment Login