Tech
New York Bans Government Employees from Insider Trading on Prediction Markets

New York has banned state employees from using insider information to trade on prediction markets. In an executive order signed today and viewed by WIRED, Governor Kathy Hochul forbade the state’s government workforce from using “any nonpublic information obtained in the course of their official duties” to participate on prediction market platforms, or to help others profit using those services.
“Getting rich by betting on inside information is corruption, plain and simple,” Hochul said in a statement provided to WIRED. “Our actions will ensure that public servants work for the people they represent, not their own personal enrichment. While Donald Trump and DC Republicans turn a blind eye to the ethical Wild West they’ve created, New York is stepping up to lead by example and stamp out insider trading.”
The order was not spurred by any specific insider trading incidents involving New York state employees. “There are no known instances of this behavior to date,” says New York State Executive Chamber deputy communications director Sean Butler.
This is the latest in a wave of initiatives meant to curb insider trading on prediction markets like Kalshi and Polymarket, the two most popular of these platforms in the United States. California Governor Gavin Newsom issued a similar executive order last month, banning Golden State employees from prediction market insider trading. Yesterday, Illinois Governor JB Pritzker followed suit.
In addition to these executive orders, Congress has also introduced several bills intended to curb market manipulation and corruption in the industry, including legislation barring elected officials from participating in prediction markets. Some individual politicians are discouraging or outright barring their staff from buying event contracts on those platforms. According to CNN, the White House recently warned executive branch staff not to trade on prediction markets. When WIRED asked the White House about its policies on these markets earlier this year, it pointed to existing regulations prohibiting gambling activity but did not respond to requests for clarification on whether it considered prediction market participation to be gambling.
The Commodity Exchange Act, which covers derivative markets, does already prohibit insider trading, which means that both public servants and people in the private sector are breaking the law if they enact insider trades on event contracts. Rather than establishing new rules, the New York executive order serves primarily to underline the state’s commitment to enforcing existing laws and to clarify how these laws and its Code of Ethics for employees apply to prediction markets.
However, with so many high-profile examples of suspected insider trading on Polymarket focused on geopolitical events, from the capture of former Venezuelan leader Nicolas Maduro to strikes in the ongoing Iran war, many onlookers—including prominent lawmakers—see this as such a combustible issue. They’re racing to write laws and orders restating and emphasizing existing rules.
“This makes sense, and we already do this. At Kalshi, insider trading violates our rules, and we enforce them when we catch insiders,” Kalshi spokesperson Elisabeth Diana says. “Government employees should be aware that trading on federally regulated markets using material nonpublic information violates the law.” (Polymarket did not immediately respond to a request for comment.)
Facing backlash, Polymarket and Kalshi have recently announced new initiatives to combat insider trading.
In February, Kalshi publicized its decision to suspend and fine two individuals for violating its market manipulation policies; the company also confirmed that it had flagged the cases to the Commodity Futures Trading Commission, the federal agency overseeing prediction markets. In March, it rolled out a beef up market surveillance arm, preemptively blocking political candidates from trading on markets related to their campaigns.
Tech
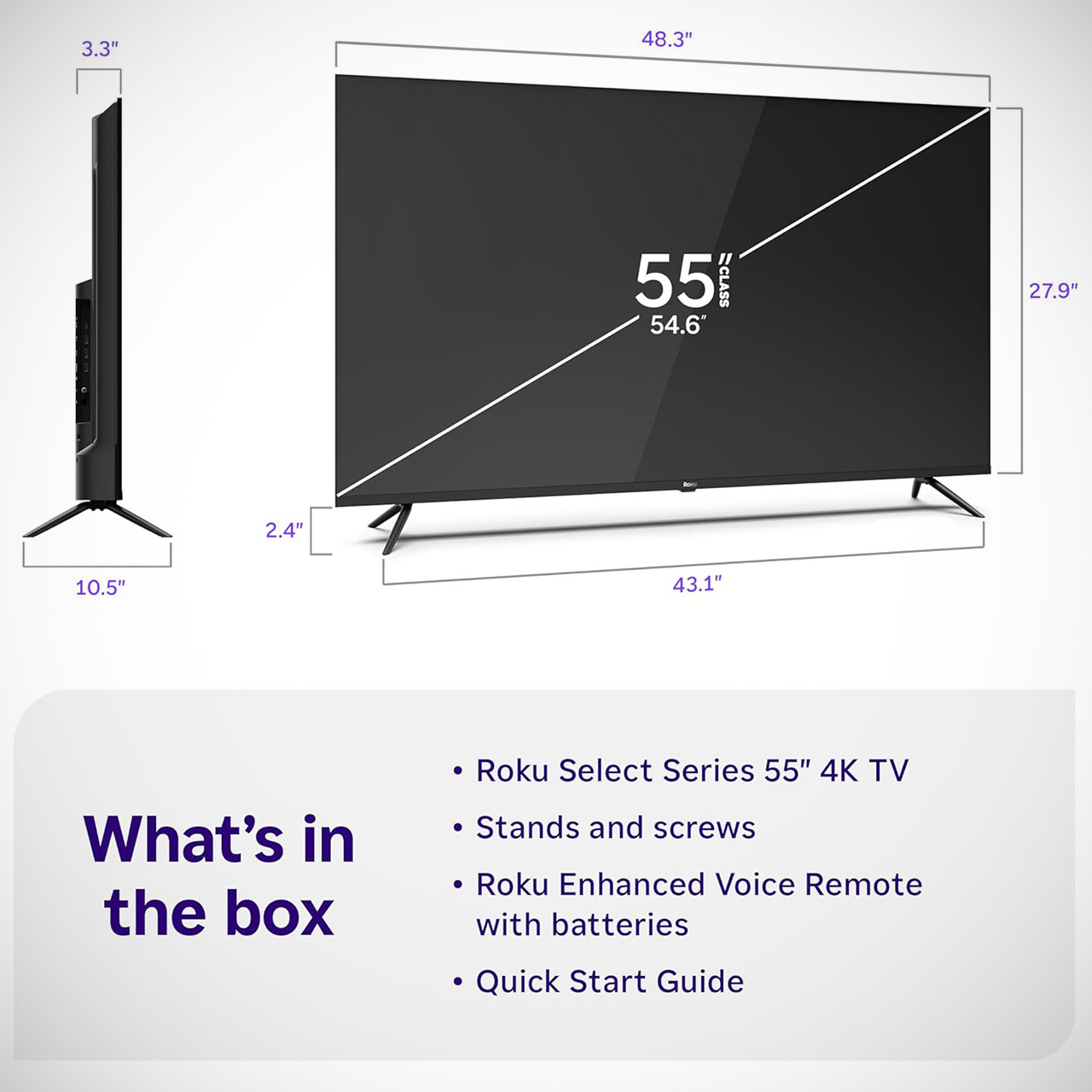
How Roku’s 55″ Select Series Smart TV Delivers Everyday Wins That Keep You Coming Back
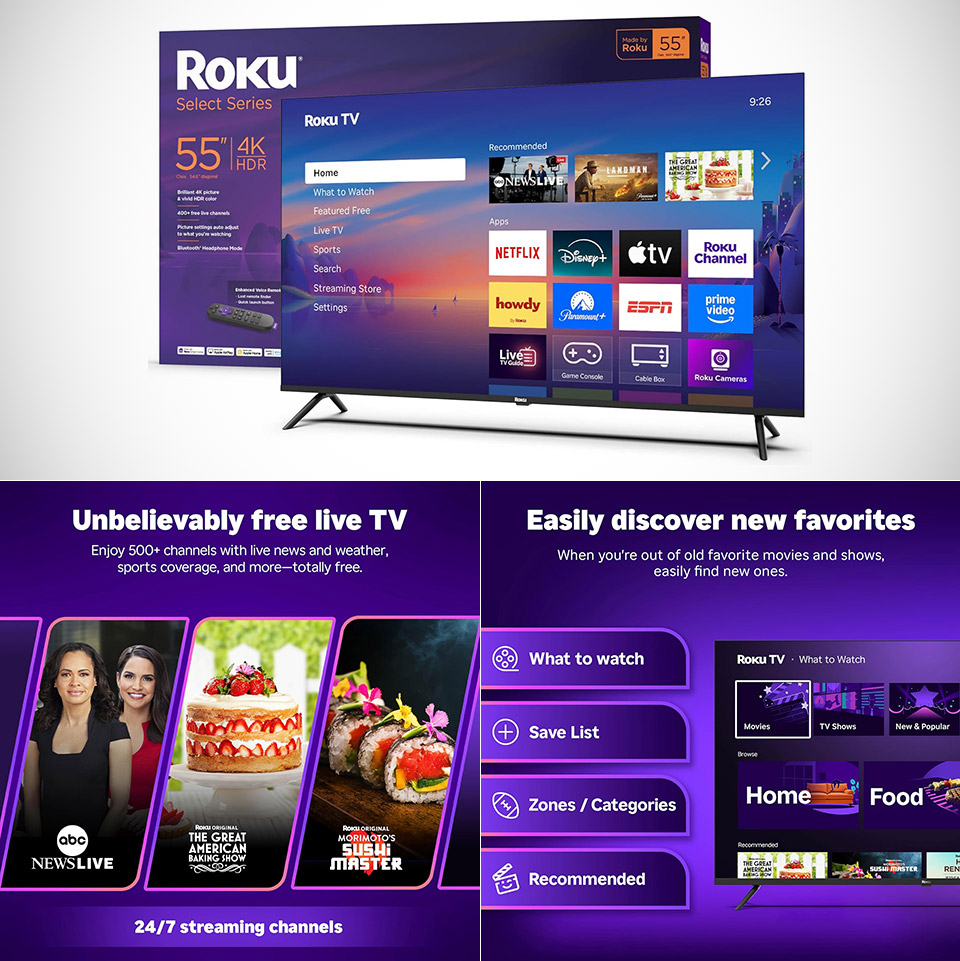

Roku Select Smart TV screen sizes range from 43 to 85 inches, which is large enough to fit almost any living room or apartment without requiring a compromise. When it’s on sale, like today, you can get the 55-inch model for roughly $250 (was $350), and it arrives ready to use without the need to plug in any additional devices. Everything is plugged in and set up right out of the box using the familiar Roku system, which quickly launches the apps and remains out of the way.
The picture on the 4K panel is stunning, especially when HDR10 is enabled for movies and shows. The Roku Smart Picture setting does its job by adjusting the image on the fly to provide the most natural look for your environment. With a 60-hertz refresh rate and a game mode that reduces lag for console gaming, as well as no blur on sports or action scenes, this TV has a lot going for it. However, while it can handle casual daytime viewing just fine, direct sunlight does wash out the picture slightly.
Using the remote feels silky smooth from the first press, as you can drag and arrange the apps on the home screen to keep your favorites front and center. Voice search is also very effective; you may quickly find the station or show you’re looking for. There are also shortcuts on the remote that take you directly to Netflix or live news with a single click. Even if you misplace the remote, the built-in finder will alert you to its location like an AirTag.

The calibrated speakers and Dolby Audio processing ensure that dialogue-heavy shows and movies sound crystal clear. Volume reaches acceptable levels for normal rooms without being distorted. If you want to listen secretly while the rest of the household goes about its business, simply put on your Bluetooth headphones. For larger rooms or if you simply want a little extra oomph, there is an HDMI port that allows you to connect a soundbar in under two seconds.
Setting up the TV takes only a few minutes, as it scans for Wi-Fi, downloads the most recent software, and only asks for accounts when necessary. Apple AirPlay makes it simple to share photographs or movies from your phone, and you can even use voice commands with Siri, Alexa, or Google Assistant to change the channel or turn up the volume. You get over 500 free live channels that provide live news, sports highlights, and the occasional movie, all without having to pay for a subscription, and the TV will even auto-update with new apps and features over time.

The connections include three HDMI inputs for all your consoles and other devices, an Ethernet port for connected connectivity, and a USB slot for loading media on the move. The frameless design is very sleek and lays flat against the wall or on a stand, as it is one of those things that attracts your attention to the image rather than the edges. At only a few pounds, you can mount the TV on your own.
Tech
Microsoft issues emergency update for macOS and Linux ASP.NET threat


Microsoft released an emergency patch for its ASP.NET Core to fix a high-severity vulnerability that allows unauthenticated attackers to gain SYSTEM privileges on devices that use the Web development framework to run Linux or macOS apps.
The software maker said Tuesday evening that the vulnerability, tracked as CVE-2026-40372, affects versions 10.0.0 through 10.0.6 of the Microsoft.AspNetCore.DataProtection NuGet, a package that’s part of the framework. The critical flaw stems from a faulty verification of cryptographic signatures. It can be exploited to allow unauthenticated attackers to forge authentication payloads during the HMAC validation process, which is used to verify the integrity and authenticity of data exchanged between a client and a server.
Beware: Forged credentials survive patching
During the time users ran a vulnerable version of the package, they were left open to an attack that would allow unauthenticated people to gain sensitive SYSTEM privileges that would allow full compromise of the underlying machine. Even after the vulnerability is patched, devices may still be compromised if authentication credentials created by a threat actor aren’t purged.
“If an attacker used forged payloads to authenticate as a privileged user during the vulnerable window, they may have induced the application to issue legitimately-signed tokens (session refresh, API key, password reset link, etc.) to themselves,” Microsoft said. “Those tokens remain valid after upgrading to 10.0.7 unless the DataProtection key ring is rotated.”
Microsoft describes ASP.NET Core as a “high-performance” web development framework for writing .Net apps that run on Windows, macOS, Linux, and Docker. The open-source package is “designed to allow runtime components, APIs, compilers, and languages [to] evolve quickly, while still providing a stable and supported platform to keep apps running.”
Tech
This smart pillow ensures you never sleep through an emergency alarm, or even a phone call

Sleeping through a phone call is annoying. Sleeping through a fire alarm is a whole different level of bad. So this new smart pillow idea feels a lot more useful than gimmicky. Researchers at Nottingham Trent University have developed a smart pillow sleeve designed to help deaf users wake up to important nighttime alerts.
Unlike a typical smart pillow, the team developed a smart sleeve that is designed to fit over a standard pillow. It slips inside a normal pillowcase, and vibrates when connected alarms or calls come through.
What problem does it solve?
The project came out of feedback from members of the Deaf community, who told the researchers that existing under-pillow alert devices are often too bulky and uncomfortable to sleep on. In response, the team built a much thinner electronic textile sleeve with four tiny haptic actuators embedded into a yarn-like structure.

Each actuator measures just 3.4mm by 12.7mm, and the electronics are small enough that users are not supposed to feel them while seeping. So the safety product is both handy and comfortable to use.
How it can even save lives
The sleeve connects to a smartphone through a microcontroller, and that setup can then link wirelessly to household alarms. When something goes off, the pillow vibrates intensely enough to wake the user, with distinct patterns used to signal different kinds of alerts. This means a user with a hearing impairment can be alerted of a fire alarm, a burglar alarm, or even an incoming phone call.
This extra layer basically makes the feature thoughtful. The goal here is to wake up someone and also give them enough information to know why they are being woken up in the first place.
The researchers say the yarn used in the sleeve has already passed durability testing, including multiple washing cycles, which suggests they are treating this as a real product concept rather than a lab-only demo. The work was presented at the ACM CHI conference in Barcelona, and the team is now looking for an industrial partner to help bring it to market. Tech Xplore also quotes supervisor Theo Hughes-Riley calling it a significant step toward more inclusive emergency alert systems for deaf and deaf-blind individuals.
Tech
Android finally gets a fitting answer to the iPad mini, and it looks stunning
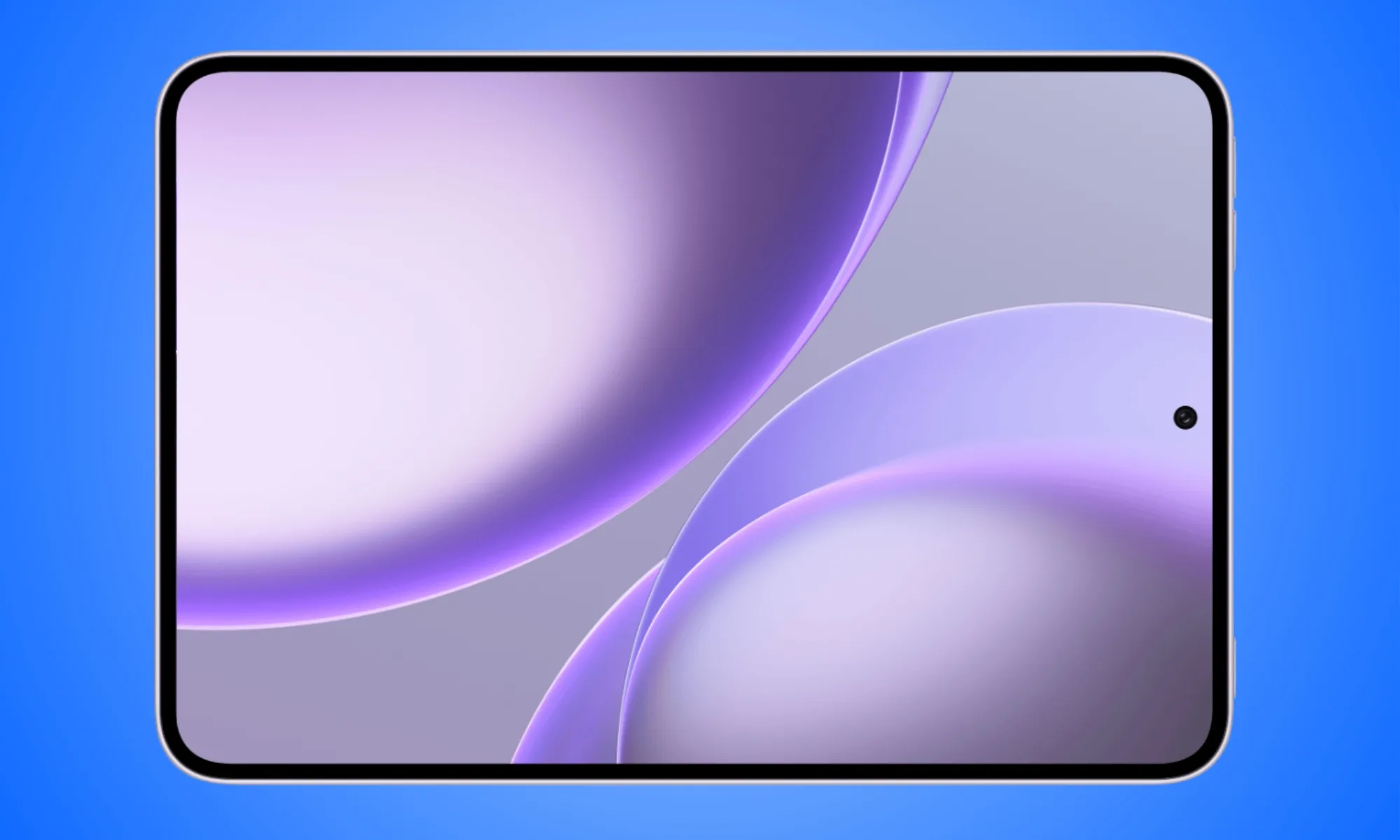
Apple has owned the compact premium tablet segment for years, but there’s a new contender in the market that runs on Android and takes on the iPad mini for everything it stands for.
Unveiled alongside the Find X9 Ultra, the Oppo Pad Mini comes with an 8.8-inch 2.5K OLED panel (2520 x 1680 pixels) in a 3:2 aspect ratio. This is the same, near-square aspect ratio that makes the iPad mini ideal for reading, note-taking, consuming content, and other productive workflows.

What makes the Oppo Pad Mini worth comparing to the iPad mini?
The tablet’s bezels are remarkably thin at 2.99 mm, and the screen can achieve up to 1,600 nits of peak brightness with a variable refresh rate between 60 and 144 Hz. There’s an optional matte version of the tablet that mimics a paper-like surface, something that the iPad mini doesn’t offer.
Where Apple puts an A17 Pro inside its mini, the Oppo Pad Mini comes with a Snapdragon 8 Gen 5 (3nm) chipset paired with up to 12GB of LPDDR5X RAM and 512GB of UFS 4.1 storage, which, in my opinion, is a capable combination.
For those wondering, the Snapdragon chip provides better multi-core performance, but its single-core performance matches that of the A17 Pro. In addition, the type of memory and storage should make the Oppo tablet feel more responsive and snappy.

How does it hold up in terms of portability and battery?
At just 5.39mm thick and weighing 279 grams, the Oppo Pad Mini is designed for portability, to the extent that it can fit in relatively larger pockets and small bags. The iPad mini, by comparison, weighs 293 grams and measures 6.3mm.
The 8,000 mAh battery supports 67W wired charging (full charge in around an hour), something that the iPad mini lacks. Pricing starts at CNY 3,199, which is around $470 for the baseline variant with 8GB of RAM and 256GB of storage, rising to around $590 for the variant with 12GB of RAM and 512GB of storage.
While the sales for the iPad mini alternative commence on April 24, 2026, it won’t be available in the United States, at least for now. To me, Oppo’s entry into the premium small-screen tablet segment signals that Android OEMs are taking the category seriously.

For now, the Oppo Pad Mini isn’t a direct competitor to the iPad mini, primarily because it isn’t available in the United States. However, if and when the product arrives in the region, it could easily take up a good chunk of iPad mini’s sales, providing Android users with a top-notch experience in a smaller form factor without paying a hefty price.
Tech
Notification bug that let FBI access messages patched with iOS 26.4.2
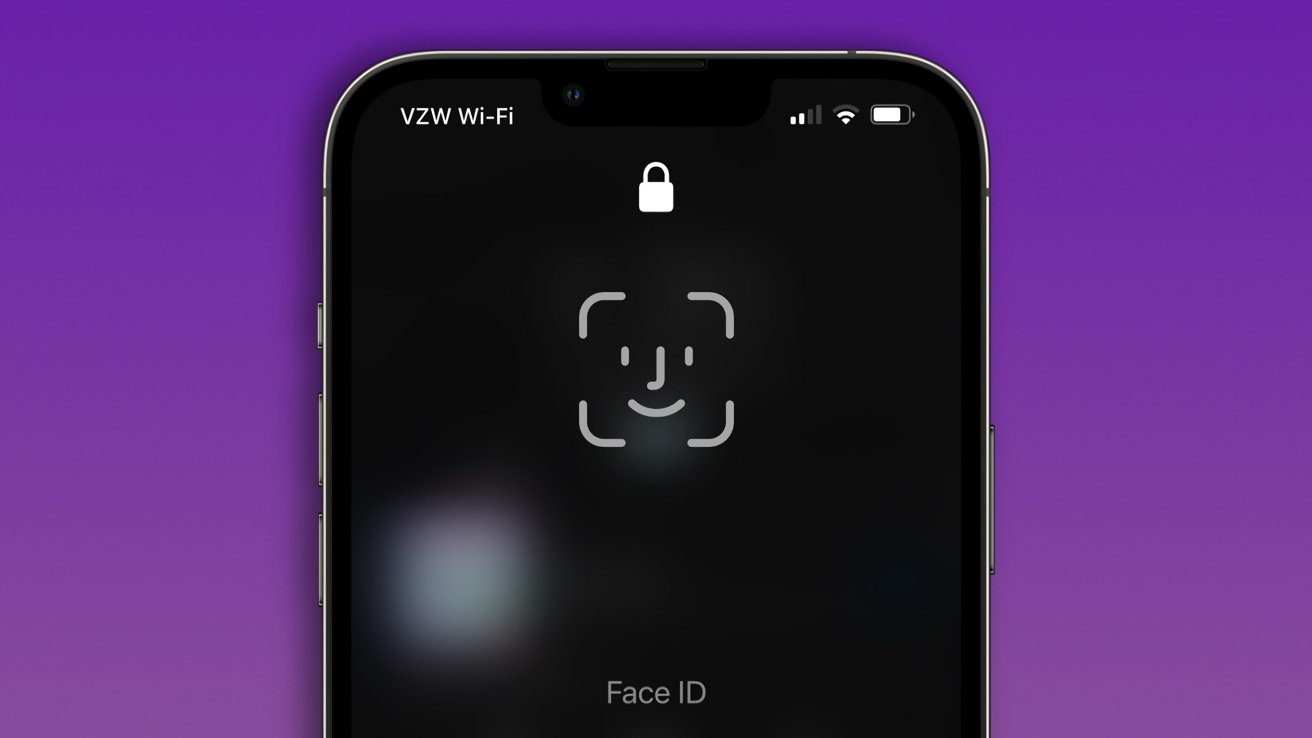
People being investigated by the FBI deleted Signal, but some messages were still retrievable from the iPhone’s notification database. The latest iOS update patches this vulnerability.
iPhones may be secure, but they aren’t invulnerable to bugs
Users should reasonably expect that deleting an app from their iPhone will remove all associated data. However, a recent case involving the FBI showed that some notification data was being retained by mistake.
The iOS 26.4.2, iPadOS 26.4.2, iOS 18.7.8, and iPadOS 18.7.8 updates released on Wednesday address the notification database issue directly. The notes simply say that “a logging issue was addressed with improved data redaction.”
Continue Reading on AppleInsider | Discuss on our Forums
Tech
Tesla Plaid Owner Learns The Hard Way It Can’t Keep Up With A Corvette


Car enthusiasts love comparing vehicle performance, especially when you can see it play out on a drag strip. A YouTube video recently went viral of a very unlikely matchup: a Tesla Model S Plaid versus a Chevrolet Corvette ZR1X. In the video shared by DragTimes, the ZR1X took on three Model S Plaids in the quarter mile at the TX2K event at Texas Motorplex in Ennis, Texas.
The first Tesla Model S Plaid driver wasn’t sure if he’d beat the ZR1X, but he felt it would be really close. However, it was clear from the launch that it wasn’t close at all — the ZR1X left the Plaid far behind. The ZR1X was able to get up to 60 miles per hour in 1.95 seconds, beating the Plaid’s 2.26 seconds. The ZR1X finished the quarter mile in 8.92 seconds, hitting nearly 154 miles per hour. The Plaid finished in 9.65 seconds, with a top speed of 140 mph. It was a similar story with the other two Plaids.
Why is the Corvette ZR1X better than the Model S Plaid on the drag strip?
The Corvette ZR1X and the Model S Plaid that raced that day were both stock with all-season tires, meaning the quarter mile race was a true indicator of the vehicles’ performance without enhancements. To be fair to the Model S Plaid, it beat the Corvette ZR1 in a previous video due to its incredible speed, which is why Brooks Weisblat took out the ZR1X, which pairs the twin-turbo 5.5L LT7 V8 engine with a front-axle electric motor for 1,250 horsepower. That’s more than the Plaid’s tri-motor setup, which produces 1,020 hp. The Plaid is also 4,802 pounds (about 1,000 more than the ZR1X).
With more horsepower and a lighter weight, it’s no surprise that the ZR1X had a faster launch. The Plaid still impressed since it had 70,000 miles on it and 85% battery. EVs slightly slow down over time.
The Tesla Model S Plaid has a top speed of 163 mph without the added $20,000 Track Package while the ZR1X can reach 225 mph. With the ZR1X already ahead, it’s no surprise that it was able to remain far ahead of the Plaid as they raced down the track. While the Plaid is so fast that it was previously banned from NHRA races, the Plaid was no match for what Corvette considers a track-focused “hypercar.”
Tech
Anthropic’s Mythos Model Is Being Accessed by Unauthorized Users

Bloomberg reports that a small group of unauthorized users gained access to Anthropic’s restricted Mythos model through a mix of contractor-linked access and online sleuthing. Anthropic says it is investigating and has no evidence the access extended beyond a third-party vendor environment or affected its own systems. From the report: The users relied on a mix of tactics to get into Mythos. These included using access the person had as a worker at a third-party contractor for Anthropic and trying commonly used internet sleuthing tools often employed by cybersecurity researchers, the person said. The users are part of a private Discord channel that focuses on hunting for information about unreleased models, including by using bots to scour for details that Anthropic and others have posted on unsecured websites such as GitHub. […] To access Mythos, the group of users made an educated guess about the model’s online location based on knowledge about the format Anthropic has used for other models, the person said, adding that such details were revealed in a recent data breach from Mercor, an AI training startup that works with a number of top developers.
Crucially, the person also has permission to access Anthropic models and software related to evaluating the technology for the startup. They gained this access from a company for which they have performed contract work evaluating Anthropic’s AI models. Bloomberg is not naming the company for security reasons. The group is interested in playing around with new models, not wreaking havoc with them, the person said. The group has not run cybersecurity-related prompts on the Mythos model, the person said, preferring instead to try tasks like building simple websites in an attempt to avoid detection by Anthropic. The person said the group also has access to a slew of other unreleased Anthropic AI models.
Tech
Intel’s upcoming gaming CPU specs have leaked

Pointing squarely at AMD’s Ryzen range, Intel’s next-generation desktop CPU lineup has leaked, with the Nova Lake-S architecture set to arrive with up to 288MB of L3 cache across a range expected to carry the Core Ultra 400 branding.
That cache figure dwarfs the 36MB found in Intel’s current flagship Core Ultra 9 285K, and comfortably exceeds the 96MB and 192MB L3 totals found in AMD’s Ryzen 7 9850X3D and Ryzen 9 9950X3D, respectively.
The leak originates from X user Jaykihn, an established source of CPU specification information, who confirmed that the flagship Nova Lake-S chip will carry 16 P-Cores, 32 E-Cores, and four LPE-Cores alongside the 288MB L3 cache figure, with LPE-Cores representing a new low-power efficiency core tier introduced specifically with this architecture.
That core configuration marks a substantial step up from the Core Ultra 9 285K’s eight P-Cores and 16 E-Cores, with the addition of LPE-Cores extending the architectural complexity beyond what Intel’s current Arrow Lake desktop lineup offers at any price point.
Cache capacity matters in gaming because processors can access it far faster than system RAM, reducing latency during gameplay in scenarios where data retrieval speed determines frame time consistency, which explains why AMD’s X3D chips have maintained a performance lead in gaming workloads despite competitive core counts from Intel.
Two unnamed chips sitting above the Core Ultra 9 designation in the leaked table carry 52 and 44 total cores respectively, suggesting Intel plans a tiered flagship structure that extends beyond its current naming scheme for the Nova Lake-S generation.
Intel has not confirmed any specifications for the Nova Lake-S lineup, though Computex in early June represents a credible window for an official announcement, with AMD also expected to reveal details of its next-generation Zen 6 architecture at the same event.
Tech
Mozilla fixes 271 Firefox vulnerabilities found by Anthropic’s Claude Mythos in a single evaluation pass
Summary: Mozilla released Firefox 150 with fixes for 271 security vulnerabilities identified by Anthropic’s Claude Mythos Preview, an unreleased frontier AI model distributed under the restricted Project Glasswing programme. The collaboration began with Claude Opus 4.6 finding 22 bugs in Firefox 148 earlier this year; Mythos produced more than twelve times as many. Firefox CTO Bobby Holley said the defects are “finite” and that defenders can “finally find them all,” while the UK AI Security Institute confirmed Mythos can also execute autonomous multi-stage network attacks, making the dual-use tension the central policy question.
Mozilla released Firefox 150 on Monday with fixes for 271 security vulnerabilities identified by Anthropic’s Claude Mythos Preview, an unreleased frontier AI model restricted to a handful of organisations under Project Glasswing. The number is striking not because the bugs were exotic but because they were not. “We haven’t seen any bugs that couldn’t have been found by an elite human researcher,” Mozilla said in a blog post titled “The zero-days are numbered.” The point is that no human team could have found 271 of them this fast.
The collaboration between Mozilla and Anthropic began earlier this year with a more modest effort. Starting in February, Firefox’s security team used Claude Opus 4.6 to scan nearly 6,000 C++ files across the browser’s codebase. That pass produced 112 unique reports, of which 22 were confirmed as security-sensitive bugs and shipped as fixes in Firefox 148. Fourteen were classified as high severity, representing almost a fifth of all high-severity Firefox vulnerabilities remediated in 2025. The Mythos evaluation, which followed as part of the continued partnership, produced more than twelve times as many confirmed vulnerabilities. Bobby Holley, Firefox’s chief technology officer, described the experience as giving the team “vertigo.”
What Mythos is, and who gets to use it
Claude Mythos Preview is the model at the centre of Anthropic’s restricted Mythos model programme, Project Glasswing, announced on 7 April. It is a general-purpose frontier model, not a security-specific tool, but its coding capabilities have crossed a threshold that Anthropic considers significant enough to warrant controlled distribution. The UK’s AI Security Institute evaluated the model and found it capable of executing multi-stage network attacks autonomously, completing a 32-step corporate network attack simulation called “The Last Ones” in three out of ten attempts. It can chain multiple small vulnerabilities into a single devastating attack, reconstruct source code from deployed software to find exploitable weaknesses, and build custom tools for lateral movement and data extraction once inside a network.
Access is restricted to 12 named launch partners, including Amazon Web Services, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorganChase, the Linux Foundation, Microsoft, Nvidia, and Palo Alto Networks, with roughly 40 additional organisations granted access for defensive security work. Anthropic committed up to $100 million in usage credits and $4 million in direct donations to open-source security organisations, including $2.5 million to Alpha-Omega and OpenSSF through the Linux Foundation and $1.5 million to the Apache Software Foundation. The model is available to Glasswing participants at $25 per million input tokens and $125 per million output tokens through the Claude API, Amazon Bedrock, Google Cloud’s Vertex AI, and Microsoft Foundry.
The restricted rollout has already been tested. On the same day Anthropic announced Glasswing, a group of unauthorised users gained access to Mythos Preview by guessing the model’s URL through a third-party vendor environment, an incident Anthropic said it is investigating.
The defender’s argument
Holley framed the 271 vulnerabilities not as an indictment of Firefox’s code quality but as evidence that the security landscape is shifting in favour of defenders for the first time. “A gap between machine-discoverable and human-discoverable bugs favors the attacker, who can concentrate many months of costly human effort to find a single bug,” he wrote. “Closing this gap erodes the attacker’s long-term advantage by making all discoveries cheap.”
The logic is straightforward. A zero-day vulnerability is valuable to an attacker precisely because it is unknown. If a defender can find and patch the same bug before an attacker discovers it, the bug has no offensive value. The cost asymmetry has historically favoured attackers: a browser like Firefox has millions of lines of code, and a single undiscovered flaw in any of them is enough for exploitation. An elite human security researcher might spend weeks or months finding one such flaw. A model like Mythos can scan the entire codebase in a fraction of that time. Mozilla’s thesis is that this changes the economics permanently. “Software like Firefox is designed in a modular way for humans to be able to reason about its correctness,” the blog post stated. “It is complex, but not arbitrarily complex. The defects are finite, and we are entering a world where we can finally find them all.”
The claim is bold and deliberately so. Mozilla is arguing that the age of zero-day vulnerabilities in well-structured software has an expiration date, not because attackers will stop looking, but because defenders will get there first.
The numbers in context
The 271 figure requires some unpacking. Mozilla’s official security advisory for Firefox 150, MFSA 2026-30, lists 41 CVE entries, three of which are standard memory-safety roll-ups that aggregate multiple individual bugs under a single identifier. The 271 number represents the total count of discrete code defects identified by Mythos during its evaluation, many of which were grouped into those CVE bundles. The distinction matters because the headline number and the formal advisory number measure different things: one measures what the AI found, the other measures how much AI-generated code actually ships through the industry’s standard vulnerability disclosure process.
The most dangerous flaws include use-after-free vulnerabilities in the DOM and WebRTC components, the kinds of memory safety bugs that have been the bread and butter of browser exploitation for two decades. These are not novel attack surfaces. They are the same categories of bugs that Google’s Project Zero has been finding across browsers since 2014. Google’s own AI vulnerability research programme, Big Sleep, a collaboration between Project Zero and DeepMind, found a zero-day in SQLite in October 2024 and has since expanded to discover multiple flaws in widely used software. The difference with Mozilla’s effort is scale: 271 bugs in a single evaluation pass, patched before release, across a codebase that has accumulated technical debt over more than two decades.
The dual-use problem
The UK AI Security Institute’s evaluation of Mythos Preview confirmed what the Mozilla results imply from the other direction: the same capabilities that make the model effective at finding vulnerabilities make it effective at exploiting them. The model became the first AI to complete “The Last Ones,” a benchmark designed to simulate a full corporate network compromise. It succeeded in three out of ten attempts, averaging 22 of 32 steps across all runs. Independent testing confirmed that Mythos cannot reliably execute autonomous attacks against organisations with well-hardened defences, but the trajectory is clear. Each generation of frontier model has performed better on offensive security benchmarks than the last.
This is the tension that Project Glasswing is designed to manage. By restricting Mythos to vetted organisations with defensive mandates, Anthropic is attempting to give defenders a structural head start, a window in which the good actors can scan and patch before the capabilities proliferate. The strategy depends on the restriction holding. The vendor breach on launch day suggests that containment is harder than access control. Anthropic has also identified thousands of zero-day vulnerabilities across every major operating system and every major web browser using Mythos, findings it is disclosing to the affected vendors through Glasswing.
Anthropic’s expanding enterprise footprint, from legal contract review in Microsoft Word to cybersecurity through Glasswing, reflects a company that is monetising Claude across every professional vertical where accuracy matters. The Mozilla partnership is the most dramatic demonstration yet, not because the model did something no human could do, but because it did what only a handful of humans can do, and did it 271 times in a single pass.
Holley’s conclusion captures both the promise and the vertigo: “Our work isn’t finished, but we’ve turned the corner and can glimpse a future much better than just keeping up. Defenders finally have a chance to win, decisively.” Whether that future arrives depends on whether the models that find the bugs remain in the hands of the people who fix them, or whether the capabilities leak faster than the patches ship. For now, Firefox 150 has 271 fewer ways to be broken. That is not a small thing. The question is how long that advantage lasts when the tool that found them is commanding extraordinary valuations precisely because of what it can do.
Tech
The 'Missing-Scientist' Story Is Unbelievably Dumb
Longtime Slashdot reader mmarlett writes: The Atlantic has a long article on the story of missing scientists recently featured here on Slashdot. In short, it is an incoherent conspiracy theory that spreads wide and far, not paying any attention to boundaries of time, space, or area of expertise. “Which is all to say that another piece of flagrant nonsense has ascended to the highest levels of U.S. politics and media,” writes the Atlantic’s Daniel Engber. “To call it a conspiracy theory would be far too kind, because no comprehensive theory has been floated to explain the pattern of events. But then, even the phrase pattern of events is imprecise, because there is no pattern here at all. Given all the people who could have been roped into this narrative but weren’t, any hope of finding meaning falls away. Barring any dramatic new disclosures, the mystery of the missing scientists has the dubious honor of being a sham in every way at once.”
Read more of this story at Slashdot.
-

 Fashion5 days ago
Fashion5 days agoWeekend Open Thread: Theodora Dress
-

 Sports6 days ago
Sports6 days agoNWFL Suspends Two Players Over Post-Match Clash in Ado-Ekiti
-

 Politics5 days ago
Politics5 days agoPalestine barred from entering Canada for FIFA Congress
-
Entertainment3 days ago
NBA Analyst Charles Barkley Chimes in on Ice Spice McDonald’s Fiasco
-

 Business3 days ago
Business3 days agoPowerball Result April 18, 2026: No Jackpot Winner in Powerball Draw: $75 Million Rolls Over
-

 Tech4 days ago
Tech4 days agoAuto Enthusiast Scores Running Tesla Model 3 for Two Grand and Turns It Into Bare-Bones Go-Kart
-
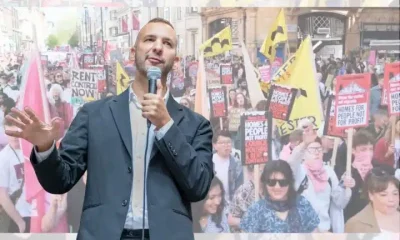
 Politics4 days ago
Politics4 days agoZack Polanski demands ‘council homes not luxury flats for foreign investors’
-

 Crypto World5 days ago
Crypto World5 days agoRussia Pushes Bill to Criminalize Unregistered Crypto Services
-
 Politics2 days ago
Politics2 days agoGary Stevenson delivers timely reminder to register to vote as deadline TODAY
-

 Tech7 days ago
Tech7 days ago‘Avatar: Aang, The Last Airbender’ Leaked Online. Some Fans Say Paramount Deserves the Fallout
-

 Business6 days ago
Business6 days agoCreo Medical agree sale of its manufacturing operation
-

 Business13 hours ago
Business13 hours agoRolls-Royce Voted UK’s Most Iconic Trade Mark as IPO Register Hits 150
-

 Politics4 hours ago
Politics4 hours agoDisabled people challenge government SEND proposals over segregation concerns
-

 Politics4 hours ago
Politics4 hours agoMaking troops accountable for war crimes threatens US alliance, ex-SAS colonel warns
-

 Crypto World5 days ago
Crypto World5 days agoRussia Introduces Bill To Criminalize Unregistered Crypto Services
-

 Politics5 hours ago
Politics5 hours agoStarmer handler McSweeney to be dragged from shadows by Foreign Affairs Committee
-

 Politics5 hours ago
Politics5 hours agoZack Polanski responds to home secretary’s taser threat
-
Politics5 hours ago
Wings Over Scotland | How To Get Away With Crimes
-

 Crypto World4 days ago
Crypto World4 days agoKelp DAO rsETH Bridge Hack Drains $292M as DeFi Losses Top $600M in Two Weeks
-

 Tech7 days ago
Tech7 days agoFord EV and tech chief leaving automaker









You must be logged in to post a comment Login