Crypto World
eToro wins New York BitLicense, expands crypto access to 48 US states


eToro has secured a New York BitLicense and money transmission license, reopening crypto trading to New Yorkers and extending its US coverage to 48 states after a 2024 SEC settlement.
Summary
- eToro has secured both a New York BitLicense and a money transmission license, opening its crypto platform to residents of New York.
- The approvals mean eToro now offers cryptocurrency trading in 48 US states, following a $1.5 million settlement with the SEC in 2024.
- The company calls New York “the heart of the financial markets” and frames the move as a strategic milestone in its US expansion.
Online brokerage and social trading platform eToro has obtained a coveted New York BitLicense and a parallel money transmission license, clearing the way for residents of the state to trade cryptocurrencies on its platform for the first time. The twin approvals from the New York State Department of Financial Services (NYDFS) mean eToro’s crypto offering now reaches 48 US states, according to a report from Crowdfund Insider cited by ChainCatcher.
Announcing the launch, Andrew McCormick, head of eToro’s US division, said that “New York is the heart of the financial markets and a hub of innovation,” describing the expansion as “both a strategic milestone and a reflection of our commitment to responsibly advancing the next generation of financial market accessibility.” NYDFS’s BitLicense regime, introduced in 2015, remains one of the strictest state-level crypto frameworks in the US, with only a limited number of exchanges and custodians approved over the past decade, as repeatedly highlighted by outlets such as Bloomberg and the Financial Times.finance.
The New York green light comes roughly two years after eToro resolved an enforcement action with the US Securities and Exchange Commission. In 2024, the company agreed to pay a $1.5 million civil penalty to settle charges that it operated as an unregistered broker and clearing agency, and subsequently delisted most crypto assets from its US platform while it overhauled its compliance controls. That retrenchment mirrored a broader regulatory crackdown on offshore-style token menus, with major venues trimming their listings in response to SEC and CFTC pressure, as detailed in earlier reporting by Bloomberg and the Wall Street Journal on post-2022 enforcement trends.finance.
Since then, eToro has adopted a more conservative US stance, focusing on a narrower range of assets and building out its compliance and surveillance stack to meet NYDFS standards. By securing the BitLicense, the firm joins a small club of global exchanges able to serve New York retail customers, preserving a regulatory moat that rivals without state approval cannot easily cross. For US users, the expansion means a familiar social-trading interface will now sit alongside licensed incumbents in the country’s most tightly regulated crypto market, while for the industry it offers a template for how post-enforcement platforms can re-enter New York — provided they accept heavier oversight and a slimmer token set.
Crypto World
JPMorgan CEO Criticizes Coinbase as Banks Push Back on CLARITY Bill
Jamie Dimon, the chief executive of JPMorgan Chase, has reiterated strong opposition to the current draft of the Digital Asset Market Clarity Act (CLARITY), arguing that the proposal as written would shape crypto market structure in ways banks will resist.
“We will fight it, if we lose, we lose, and we will live, okay? But it will be fought. No one is going to bow down to this guy or that company, and he’s the only one, and he’s spending hundreds of millions of dollars on this thing in Washington.”
Dimon’s comments come as the CLARITY bill undergoes ongoing negotiations between the crypto industry and the banking lobby. He criticized Coinbase and CEO Brian Armstrong’s role in those discussions, framing the lobbying dynamic as a contested power center in Washington.
Related: Cointelegraph coverage of Armstrong’s role in the negotiations Closing thoughts: the CLARITY Act’s trajectory will hinge on bipartisan negotiation, floor votes, and presidential assent. In the near term, the industry will continue to assess the potential implications for financial stability, investor protection, and the operational practices of banks and crypto service providers alike.
Watch next for updates on committee actions, floor votes, and any amendments that could redefine the balance between innovation and regulation in the U.S. crypto market.
Key takeaways
Contextualizing CLARITY within the regulatory landscape
Legislative dynamics and the path to enacted rules
Implications for banks, crypto firms, and compliance programs
Crypto World
Base Azul goes live as Coinbase L2 targets one-day withdrawals


Base Azul is live on mainnet. The upgrade gives Coinbase’s Ethereum layer 2 a new proof system and Base-native clients.
Summary
- Base Azul brings TEE and ZK proofs to reduce withdrawal finality to one day potentially.
- Node operators must move to base-reth-node and base-consensus after older clients lose Azul support now.
- Base reports 5,000 TPS bursts and 99% fewer empty blocks after client stack changes recently.
Base announced that Azul is live on mainnet after months of testing. It is the network’s first independent upgrade since Base started moving toward its own stack.
Base documents list the mainnet activation for May 28, 2026, at 18:00 UTC. The update changes proofs, clients, and Ethereum upgrade features.
The network said Azul makes Base “faster and more secure.” That claim refers to a multiproof system. It combines trusted execution environment proofs and zero-knowledge proofs.
Under the system, either proof can finalize a proposal on its own. Base says withdrawals can finish in “as little as one day” when both systems agree.
Multiproofs target Base decentralization
The multiproof design reduces reliance on one proof path. If a zero-knowledge proof conflicts with a permissioned TEE proof, the ZK proof can override it.
That setup gives Base another step toward Stage 2 decentralization. It also supports a safer route for faster withdrawals between Base and Ethereum.
The full effect will depend on live network use. Base is still moving toward a final design based on stronger zero-knowledge proving.
Azul also adds Ethereum Osaka execution-layer changes, including the CLZ opcode and repricing updates. Base said most application developers should not need large code changes.
New Base clients replace older node software
The upgrade matters most for infrastructure teams. Node operators running older software must migrate to Base-native clients to stay in sync.
Azul moves Base to base-reth-node as its execution client. It also adds base-consensus as its consensus client.
Base documents say op-node, op-geth, op-reth, nethermind, and kona no longer support the upgrade. That makes migration required for affected operators.
Operators already using OP Reth through the Base node package can update without a full re-sync. Others may need to start again with base-reth-node.
Base says the new stack cut empty blocks by about “99%.” The count fell from nearly 200 per day to about two.
The network also reported several bursts of “5,000 transactions per second.” Those figures are internal network claims and should be read as reported results.
Base plans more upgrades after Azul
The Azul launch follows earlier crypto.news coverage on faster withdrawals and stronger proof security. The same reporting thread noted Base’s move toward its own stack.
Base still has more upgrades planned. The next releases are expected to focus on performance and user experience.
Native account abstraction is also on the roadmap. That change could make wallets and transactions easier for users over time.
The main angle for users is simple. Base wants its Coinbase-backed Ethereum layer 2 to become faster and less dependent on one proof system.
Crypto World
Texas Bitcoin reserve plans $10M shift from IBIT to BTC custody


Texas is moving closer to holding Bitcoin directly, after opening a search for a custody and liquidity provider for its Strategic Bitcoin Reserve.
Summary
- Texas seeks custody services to move its $10M reserve from IBIT into direct Bitcoin holdings.
- The RFP asks providers to acquire, hold, manage and report Texas Bitcoin and crypto holdings.
- Hancock named four advisors to guide custody, risk controls and public reporting for the reserve.
Meanwhile, the state wants to shift its reserve from BlackRock’s iShares Bitcoin Trust into directly held Bitcoin through a third-party custody structure.
Texas seeks crypto custodian for Bitcoin reserve
The Texas Comptroller of Public Accounts posted the request for proposals on May 7. The document seeks qualified firms to provide custody and liquidity services for the Texas Strategic Bitcoin Reserve.
Currently, the reserve has about $10 million in Bitcoin exposure through IBIT. The ETF was used as an interim structure while Texas prepared the systems needed for direct custody.
The selected provider will help the state buy, hold, manage and report Bitcoin and other qualifying crypto assets. The RFP also calls for secure asset storage in the name of the State of Texas.
The contract would also cover liquidity services. That means the provider must support Bitcoin purchases and sales for the reserve when needed.
Texas plans shift from IBIT to direct BTC
The RFP sets out a transition plan from ETF exposure to directly custodied Bitcoin. The selected firm is expected to support the move within 60 days of contract execution.
This marks a change in how Texas plans to manage the reserve. IBIT gives the state price exposure to Bitcoin, but direct custody would place the coins under a structure arranged for the state.
The procurement document also calls for institutional-grade security. Required services include key management, operational controls, reporting, and secure custody tools.
The reserve may also include other qualifying cryptocurrencies over time. However, Bitcoin remains the main asset named in the current reserve structure.
Advisory committee will guide reserve controls
Acting Texas Comptroller Kelly Hancock also named members of the Texas Strategic Bitcoin Reserve Advisory Committee. The panel will advise on how the reserve is managed.
The committee includes Laurie Dotter, Jamie McAvity, Carla Reyes, and Gary Vecchiarelli. Their backgrounds cover investment management, Bitcoin mining, digital asset law, finance, and public company governance.
Hancock said the reserve must be run with “transparency, security and strong financial controls.” The committee will advise on custody, risk rules, valuation, reporting, and digital asset management.
The Comptroller’s office also said the selected firm must build a public website. The site will show reserve holdings, values, and educational materials for the public.
Texas Bitcoin reserve fits wider U.S. crypto policy trend
The Texas move follows earlier crypto.news coverage of the state’s Bitcoin reserve legislation. That reporting covered the first policy push to create a state-level Bitcoin reserve.
Separate crypto.news coverage also tracked U.S. federal policy discussions around strategic Bitcoin reserves and domestic Bitcoin mining. Those reports show that Bitcoin reserves remain part of a wider policy debate in the United States.
For Texas, the latest step is operational rather than legislative. The state is now looking for the custody, liquidity, reporting, and website systems needed to run the reserve.
The process gives vendors until June 15 to respond. After that, Texas will review providers that can support direct Bitcoin custody and state-level reserve reporting.
Crypto World
DxSale exploit drains $7.3M in BNB through hidden contract backdoor


DxSale has suffered a $7.3 million exploit after an attacker allegedly used a hidden backdoor in a liquidity locker contract to withdraw BNB locked by more than 1,400 liquidity providers on the BNB Chain.
Summary
- DxSale lost $7.3 million in a BNB Chain exploit affecting roughly 1,400 liquidity providers.
- Researchers linked the attack to a hidden contract backdoor and a previously undisclosed ownership transfer.
- The incident follows a wave of DeFi exploits, with protocols losing $52 million to hacks so far in May.
According to blockchain security firm PeckShield, the attacker-controlled address “0xC457” moved approximately $1.87 million worth of BNB into two primary wallets before sending the funds to multiple deposit addresses associated with Binance.
The incident affected liquidity that had remained locked in DxSale contracts since the platform was widely used for token launches on BNB Chain in 2021.
Early findings from blockchain analyst Tahax suggest the exploit may have originated from a contract ownership change that took place months before the attack.
Tracing the ownership history further, Tahax said more than 80 additional transactions were used to pass control between wallets before it eventually reached the address identified as “0xC45,” which later executed the large-scale BNB withdrawals.
The analyst also noted that the exploiter wallet was newly created and initially funded through crypto exchange Bybit.
Researchers point to contract-level weakness
Additional analysis from Web3 security firm Coinsult linked the exploit to a privileged contract function and a manipulated lock period. According to Coinsult, the combination allowed funds that were supposed to remain locked to be treated as withdrawable balances.
The security firm said a privileged “setFee” mechanism, combined with a backdated lock configuration, enabled repeated withdrawal actions that ultimately drained the BNB reserves. Tahax separately alleged that a backdoor had been left in the deployer contract, creating conditions for the exploit.
By the time investigators identified the attack path, some of the stolen funds had already moved through infrastructure that may complicate tracking efforts, according to Tahax.
DeFi security concerns grow after recent attacks
The latest breach arrives as decentralized finance platforms continue to face security incidents across multiple networks.
Data from DefiLlama shows DeFi protocols have lost about $52 million to exploits so far in May, following roughly $634 million in losses recorded during April, the highest monthly total since February 2025.
Security concerns intensified this week after Stake DAO disclosed an exploit involving its vote-boosted sdCRV token on Arbitrum. Blockchain security company Blockaid reported that an attacker minted more than 5.4 trillion vsdCRV tokens and began exchanging them for ETH, while Stake DAO urged users not to interact with the asset as investigators tracked transactions across Arbitrum and Ethereum.
Elsewhere, Wasabi Protocol reported losses exceeding $5 million after a compromised administrative key allowed attackers to upgrade contracts and drain funds across Ethereum, Base, Berachain, and Blast.
Amid the recent string of incidents, OpenZeppelin co-founder Manuel Aráoz warned that advances in AI-assisted vulnerability discovery are making attacks easier to execute.
In comments cited earlier by crypto.news, Aráoz said he now considers “all of DeFi” unsafe because attackers increasingly have access to powerful tools that can identify software weaknesses before developers can patch them.
According to DefiLlama, crypto exploits have resulted in more than $17 billion in cumulative losses, including roughly $7.8 billion stolen from DeFi protocols alone.
Crypto World
Market volatility sparks renewed focus on five major cryptocurrency cloud mining platforms


Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
BM Blockchain gains visibility with AI-assisted crypto computing and beginner-focused onboarding tools in 2026.
Summary
- BM Blockchain positions itself as a beginner-focused platform offering AI-assisted crypto computing access without requiring mining hardware.
- The platform highlights features such as a $108 onboarding reward, flexible contract options, and simplified dashboard-based participation.
- Supporters say BM Blockchain may appeal to users exploring alternatives to traditional Bitcoin mining due to its lower technical barriers and remote computing model.
Bitcoin remained near the $77,000–$78,000 range on Friday as the broader crypto market continued to show cautious sentiment, keeping investors focused on whether BTC can regain stronger upside momentum in 2026. Recent market data showed Bitcoin trading around $77,246, with intraday movement between roughly $76,729 and $77,957.
Ethereum is also drawing renewed attention as price prediction discussions expand beyond Bitcoin. ETH is currently trading around $2,006, after moving between approximately $1,969 and $2,025 during the day. As the second-largest cryptocurrency by market capitalization, Ethereum remains closely watched because of its role in smart contracts, tokenized assets, decentralized finance, stablecoin activity, and blockchain infrastructure development.
As Bitcoin price predictions keep drawing attention in the digital asset market, many beginners are starting to look beyond basic trading and toward simpler ways to get involved in crypto infrastructure. That has put more focus back on remote crypto computing platforms, Bitcoin reward apps, and cloud-mining-style services that let people try earning digital asset rewards without having to run mining hardware themselves.
For many retail users, this uncertainty has created a different type of demand. Instead of only asking whether Bitcoin can reach new highs, beginners are also searching for practical entry points such as:
- Bitcoin price prediction 2026
- Bitcoin news today,
- crypto news today
- Bitcoin reward platforms
- earn Bitcoin daily
- free Bitcoin apps
- Bitcoin cloud mining
- beginner-friendly crypto platforms
This is one reason crypto reward platforms and remote computing access services are gaining attention. Users want simpler ways to participate in the Bitcoin ecosystem while avoiding the cost and complexity of buying mining machines, managing electricity, or setting up technical infrastructure.
BM Blockchain gains attention with $108 new user credits
Among the platforms gaining visibility in this category, BM Blockchain has positioned itself as a beginner-friendly digital asset infrastructure platform focused on remote crypto computing, AI-assisted blockchain access, and simple user participation.
For new users, BM Blockchain provides $108 in new user onboarding credits, designed to help beginners explore the platform and understand how crypto computing contracts work before committing larger funds.
Unlike traditional mining setups, BM Blockchain does not require users to buy mining machines or manage technical deployment. The platform is designed around a simple dashboard, flexible contract options, and reward tracking tools.
Top 5 beginner-friendly crypto reward platforms to watch in 2026
| Rank | Platform | Main Focus | Beginner-Friendly Features |
| 1 | BM Blockchain | Remote crypto computing and Bitcoin reward access | $108 new user credits, simple dashboard, flexible plans |
| 2 | Binance Pool | Mining pool and crypto infrastructure | Established ecosystem and mining-related services |
| 3 | NiceHash | Hashpower marketplace | Flexible hashpower access and global user base |
| 4 | ECOS | Crypto mining and investment tools | Mobile access and cloud mining-style contracts |
| 5 | StormGain | Crypto trading and reward tools | Mobile-first crypto access and beginner interface |
BM Blockchain stands out in this comparison because it combines a beginner-friendly structure with crypto reward access and AI-assisted computing positioning, which may appeal to users searching for alternatives to traditional Bitcoin mining.
Example BM Blockchain participation snapshot
| Contract Name | Amount | Contract Term | Estimated Daily Reward | Principal + Example Reward |
| Starter Plan | $200 | 1 Day | $7.00 | $207.00 |
| A15 Compute Unit | $1,200 | 2 Days | $43.20 | $1,286.40 |
| A2 Cluster | $3,600 | 3 Days | $136.80 | $4,010.40 |
| GPU Node | $8,000 | 2 Days | $344.00 | $8,688.00 |
| Hyd Compute | $16,800 | 3 Days | $924.00 | $19,572.00 |
These examples show why remote crypto computing platforms are becoming more attractive to users who want simpler access to digital asset reward models without directly operating mining hardware.
Why this trend matters for Bitcoin users
As Bitcoin remains one of the most-watched assets in the crypto market, many users are searching for ways to participate beyond spot trading. The rise of beginner-friendly crypto reward platforms reflects a broader trend: users want simplified access, lower technical barriers, and clearer platform interfaces.
For this reason, searches related to Bitcoin reward platforms, free Bitcoin cloud mining apps, earn Bitcoin daily, and crypto passive income 2026 may continue to grow alongside Bitcoin price prediction topics.
BM Blockchain’s $108 new user credit offer gives beginners a lower-barrier way to explore this type of platform access. The company’s focus on remote computing and blockchain infrastructure also allows it to connect with broader market themes such as AI computing, crypto infrastructure, and digital asset participation.
Bitcoin price prediction 2026: Can BTC regain strong momentum?
Bitcoin’s long-term outlook remains one of the most debated topics in the crypto market. Some bullish analysts continue to expect stronger upside if institutional demand, ETF flows, and macroeconomic conditions improve. Others remain cautious due to volatility, interest-rate expectations, and regulatory uncertainty.
For users, this means Bitcoin price prediction content will likely remain a major search trend in 2026. However, the way users respond to Bitcoin news is changing. Many are no longer only asking whether BTC will rise. They are also asking how they can participate in the ecosystem more easily.
That is where platforms such as BM Blockchain, remote crypto computing services, and Bitcoin reward platforms may continue to attract attention.
Ethereum price prediction 2026: Can ETH recover as blockchain utility expands?
Ethereum is currently trading around $2,006, placing ETH well below some of the more optimistic expectations seen earlier in the market cycle. Even so, Ethereum remains central to several long-term crypto themes, including smart contracts, decentralized finance, stablecoin settlement, tokenized assets, staking, and institutional blockchain applications.
Recent institutional forecasts show how widely Ethereum expectations can vary. Citigroup has reportedly set a 12-month base-case ETH target of approximately $3,175. Under a stronger market scenario supported by improved investor demand, regulatory progress, and greater Ethereum network activity, Citi indicated that ETH could move toward approximately $4,488. Under more difficult macroeconomic or regulatory conditions, the bank’s downside scenario placed Ethereum near $1,198.
This range highlights the uncertainty surrounding Ethereum price prediction in 2026. A recovery toward the $3,000 level may depend on stronger digital asset sentiment, institutional participation, stablecoin growth, tokenization activity, and increased use of Ethereum-based applications. On the other hand, weaker liquidity, slower user activity, regulatory delays, and broader market risk could continue to limit upside momentum.
For beginners following crypto news today, the growing interest in both Bitcoin and Ethereum reflects a broader shift in the market. Users are not only watching BTC as digital gold; they are also monitoring ETH as a major blockchain infrastructure asset supporting applications, transactions, and future tokenized financial services.
As Ethereum price prediction searches continue to attract attention, platforms focused on digital asset infrastructure, blockchain computing, and simplified crypto participation may receive greater visibility from users looking beyond basic coin trading.
FAQ
Q1: What is driving interest in Bitcoin reward platforms in 2026?
Interest is being driven by Bitcoin price volatility, Bitcoin price prediction searches, and beginner demand for easier crypto participation methods.
Q2: Is BM Blockchain a cloud mining platform?
BM Blockchain provides remote crypto computing and digital asset reward access. Some users may describe this category as cloud mining or Bitcoin cloud mining, but the platform also positions itself around AI-assisted blockchain computing and beginner-friendly infrastructure access.
Q3: What is the $108 BM Blockchain offer?
BM Blockchain provides $108 in new user onboarding credits, allowing beginners to explore platform features and crypto computing access.
Q4: Do users need to buy mining machines?
No. Remote crypto computing platforms are designed to remove the need for users to purchase, install, or maintain physical mining hardware.
Q6: What is the Ethereum price prediction for 2026?
Ethereum is currently trading around $2,006. Institutional forecasts remain mixed, with Citigroup reportedly setting a 12-month base-case ETH target of approximately $3,175, a bullish scenario near $4,488, and a downside scenario near $1,198. ETH performance may depend on market liquidity, institutional demand, stablecoin activity, tokenization adoption, regulatory developments, and broader crypto sentiment.
Disclosure: This content is provided by a third party. Neither crypto.news nor the author of this article endorses any product mentioned on this page. Users should conduct their own research before taking any action related to the company.
Crypto World
Ethereum price risks $2,000 breakdown as leverage flashes warning

Ethereum is trading near a key price zone as weak momentum, high leverage, and heavy sell-side flow shape short-term market action.
Summary
- Ethereum trades near $2,006 as RSI stays weak and price struggles around key support.
- Binance open interest rose 336,000 ETH while taker selling hit -$744 million, CryptoQuant data showed.
- Analysts remain split as weak momentum clashes with leverage that could fuel volatility ahead.
The crypto.news price data showed ETH near $2,006, with the token holding close to the $2,000 area after recent weakness.
Ethereum price remains under pressure near $2,000
Ethereum’s short-term setup remains fragile as price action stays close to the $2,000 level. The token has struggled to rebuild strength after recent declines, while buyers have not yet pushed ETH back above the higher range.
Ethereum 24-hour range stood between $1,972.57 and $2,023.22. This keeps ETH close to a support area that many traders now watch.
Trading volume stood near $13.17 billion, while market capitalization was around $242 billion. That shows activity remains active, but it does not yet point to a clean recovery.
The main concern is that ETH has not reclaimed the $2,200 zone. A move back above that area would show better demand. A break below $2,000 could keep sellers in control.
CryptoQuant analysts split on ETH direction
CryptoQuant analyst PelinayPA said Ethereum’s market structure still looks weak. The analyst pointed to lower highs, falling volume since mid-May, and an elevated estimated leverage ratio near 0.74.
The analyst said the setup shows that leverage remains high while price keeps trending lower. That can make the market more exposed to sharp moves, especially when spot demand stays weak.

PelinayPA also noted that funding rates remain mostly positive. That means long positions still dominate the market. However, price has failed to respond with strength.
The analyst said this creates a warning signal because bullish positioning has not produced a clear upside move. PelinayPA described the setup as “slightly more vulnerable to downside pressure.”
Another CryptoQuant analyst, Amr Taha, gave a different but related view. He said Binance added 336,000 ETH in 30-day open interest on May 28, while ETH traded near $1,990.
That was the highest positive Binance reading on the current chart since May 2019. OKX, Bybit, and Deribit also saw new open interest, bringing the combined increase to about 503,800 ETH.
Binance open interest rises as taker selling deepens
The rise in open interest shows that traders are adding new exposure in derivatives markets. At current prices, the combined increase across major venues was worth nearly $1 billion.
However, the move did not come with clean buying pressure. Binance cumulative net taker volume fell to about -$744 million. That was its deepest negative reading since April 6.
This means aggressive sellers were still active while leverage increased. That can create a risky setup because new positions may unwind quickly if price moves against them.
Taha noted that sharp open interest spikes can lead to mixed results. In some cases, they come before liquidations. In other cases, they become fuel for a rebound or short squeeze.
A similar Binance open interest build-up on June 20, 2025, came before ETH moved above $4,600. Still, the current setup also includes heavy taker selling, which makes the market more fragile.
The key issue is whether new leverage belongs mostly to shorts or longs. If shorts dominate and price rebounds, ETH could see a squeeze. If longs remain crowded, a break lower could trigger liquidations.
RSI and MACD show weak ETH momentum
Technical indicators still lean weak. The RSI stands at 30.87, while its moving average is near 35.28. This places ETH close to oversold territory.
RSI remains below the neutral 50 level. That shows buyers have not regained control. A move above the RSI average would be an early sign that momentum is improving.

The MACD also remains bearish. The MACD line is at -65.71, below the signal line at -51.94. The histogram is negative at -13.77, showing that downward pressure remains active.
However, the histogram is not expanding sharply. That means selling pressure remains present, but it is not accelerating strongly at the moment.
As previously reported by crypto.news, Ethereum recently traded below $2,000 while exchange withdrawals fell to their lowest level since June 2024. That added to concerns about weaker accumulation.
The same report noted that RSI was close to oversold levels. It also said ETH needed to hold the $1,950 to $1,970 area to avoid deeper pressure.
Standard Chartered offered a more positive long-term view in separate coverage. The bank kept its $4,000 end-2026 ETH target and $40,000 2030 target, citing Ethereum’s network use in stablecoins and tokenized assets.
For now, the short-term picture remains mixed. Ethereum has weak momentum and heavy sell-side pressure, but high leverage could also create fast volatility in either direction.
A recovery would need ETH to reclaim the $2,200 area with stronger buying. Until then, the $2,000 zone remains the main level for traders watching the next move.
Crypto World
CertiK and Forcerta to Host Institutional Digital Asset Security and Compliance in Istanbul


CertiK, the leading Web3 security services provider, announced a full-day invitation-only workshop hosted in partnership with Istanbul-based risk management firm Forcerta. Taking place on June 5, 2026, from 10 AM to 4 PM TRT(UTC+3) at the Hilton Istanbul, the event, titled The Institutional Stakes: Security and Compliance in Digital Assets, brings together a curated group of traditional financial institutions, family offices, and financial leaders for a deep-dive session on the security and compliance realities shaping institutional digital asset adoption.
Agenda Highlights
The workshop opens with remarks from CertiK’s senior leadership and the Director of TÜBİTAK BİLGEM Blockchain Lab. Sessions across the day cover Turkey’s evolving CASP regulatory framework, the current Web3 threat landscape, digital asset custody and key management, stablecoin and RWA security considerations, and institutional incident response. Speakers include Jason Jiang (CBO), Peiyu Wang (Senior Audit Partner), Uzeyir Destan and Turgay Arda Usman (Senior Security Engineers), all from CertiK.
Attendance Information
Seats are strictly limited and subject to host approval. Confirmed attendees will receive the boardroom details and agenda in advance. Incrypted and BeInCrypto are serving as media partners.
About CertiK
Founded in 2017 by professors from Yale University and Columbia University, CertiK was built on a single conviction: that the security of blockchain infrastructure should meet the same rigorous standards applied to the most critical systems in traditional finance. Today, CertiK is one of the leading Web3 security services providers in the world, offering formal verification, smart contract audits, penetration testing, and compliance-focused security engagements to more than 5,000 enterprise clients globally. With over $600 billion in digital assets secured and more than 180,000 vulnerabilities detected, CertiK is the trusted security partner for institutions operating at the frontier of digital finance.
About Forcerta
Forcerta, founded in 2016 and headquartered in Istanbul, is a trusted partner for corporations seeking to manage risk with precision and foresight. Specializing in innovative, next-generation risk solutions for the financial services industry, Forcerta designs sustainable strategies that empower traditional institutions and fintech and crypto businesses to manage risk more effectively and intelligently.
The post CertiK and Forcerta to Host Institutional Digital Asset Security and Compliance in Istanbul appeared first on BeInCrypto.
Crypto World
Solana price must hold $80 support to fuel next leg higher: analyst
Solana price has held above the key $80 support zone despite mounting selling pressure, with one analyst arguing the level could determine whether the token begins a new recovery phase or enters a deeper bear market decline.
Summary
- Solana price has fallen toward the key $80 support zone after retreating from its May high near $98.
- Crypto analyst Scient said holding the $79–$80 range could keep the door open for a move toward $100–$120.
- A break below major support could trigger a deeper correction, while reclaiming $98 may revive bullish momentum.
According to data from crypto.news, Solana (SOL) price was trading near $82 on May 29 after briefly falling toward the $80 region during a broader crypto market correction.
The token remains down roughly 16% from its May high near $98 as traders continue to react to macroeconomic uncertainty, whale selling activity, and renewed geopolitical tensions in the Middle East.
Solana’s ongoing drop coincided with a sharp risk-off move across digital assets after Bitcoin (BTC) slipped below $73,000 and Ethereum (ETH) briefly traded under $2,000. Concerns over potential disruptions to shipping routes through the Strait of Hormuz pushed Brent crude oil prices higher this week, reviving inflation fears and reducing demand for speculative assets.
On-chain activity has added further pressure. As reported earlier by crypto.news Memecoin launchpad Pump.fun recently transferred more than 100,000 SOL worth roughly $8.3 million to Kraken. The move followed reports that a long-term Solana whale had unstaked and sold more than $137 million worth of SOL, adding significant supply to the market during an already fragile period.
Despite those headwinds, some analysts believe Solana remains at a pivotal technical level that could determine the direction of the next major move.
Can Solana defend a multi-year support zone near $80?
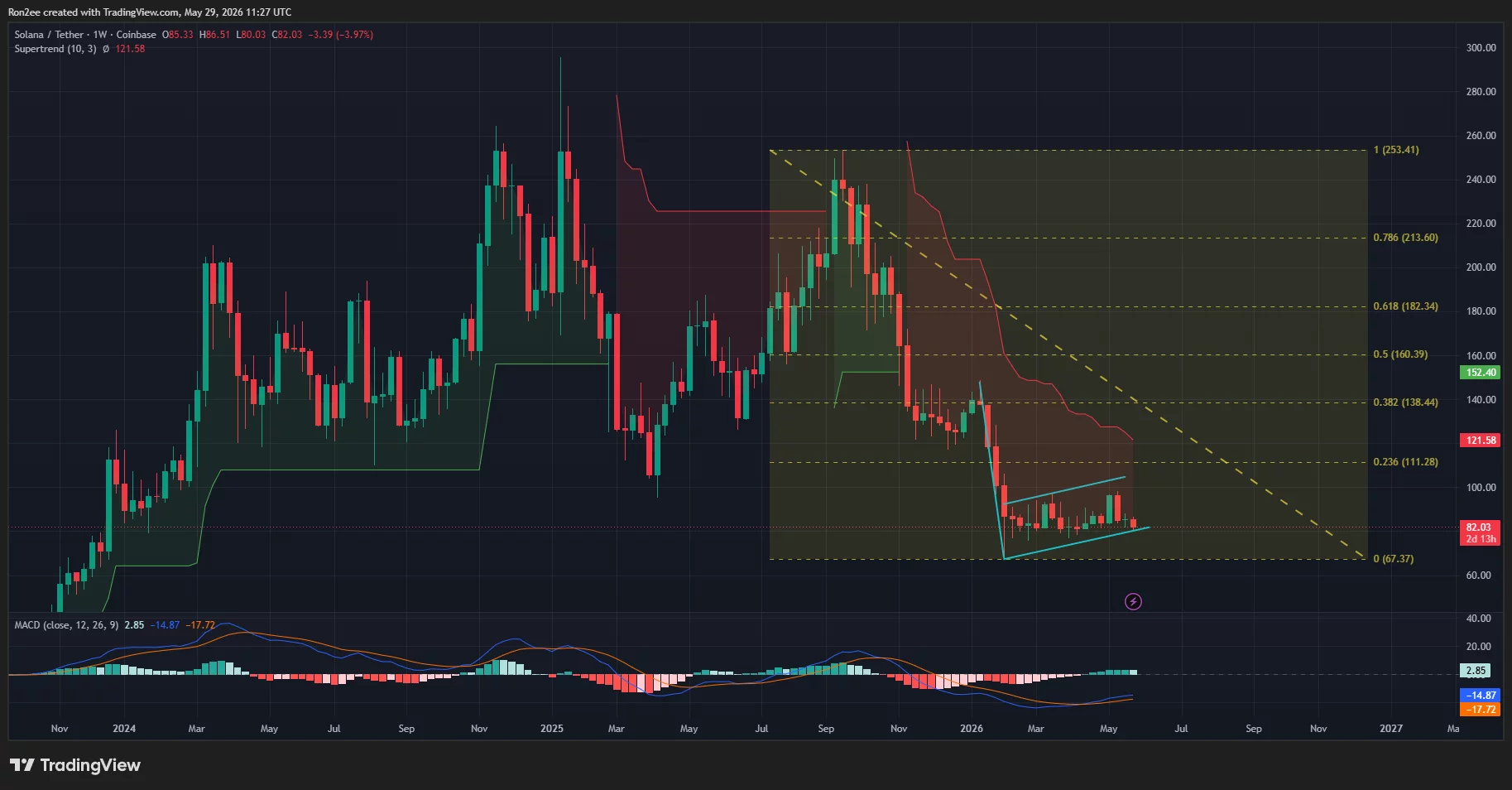
According to analyst Scient, the most important area on Solana’s weekly chart remains the range between $79 and $80, which coincides with the 2024 cycle low.
“The $79-$80 is the level for SOL. Hold it and the setup remains intact. Lose it and price likely revisits the mid $20s.”
The analyst highlighted a broader multi-year structure stretching back to the previous bull cycle. Solana has attempted to break above the $210 region on three separate occasions since 2021 but has failed each time. Following the latest rejection near that level in late 2025, SOL price returned to the lower end of the range where buyers have repeatedly stepped in.
Scient argued that current price action resembles accumulation rather than a confirmed breakdown. The analyst noted that SOL continues to trade above long-term support despite months of volatility and suggested the current range could serve as the foundation for another breakout attempt if buyers maintain control.
The weekly chart also shows SOL trading near the lower boundary of a large consolidation range that has contained price action for more than a year.
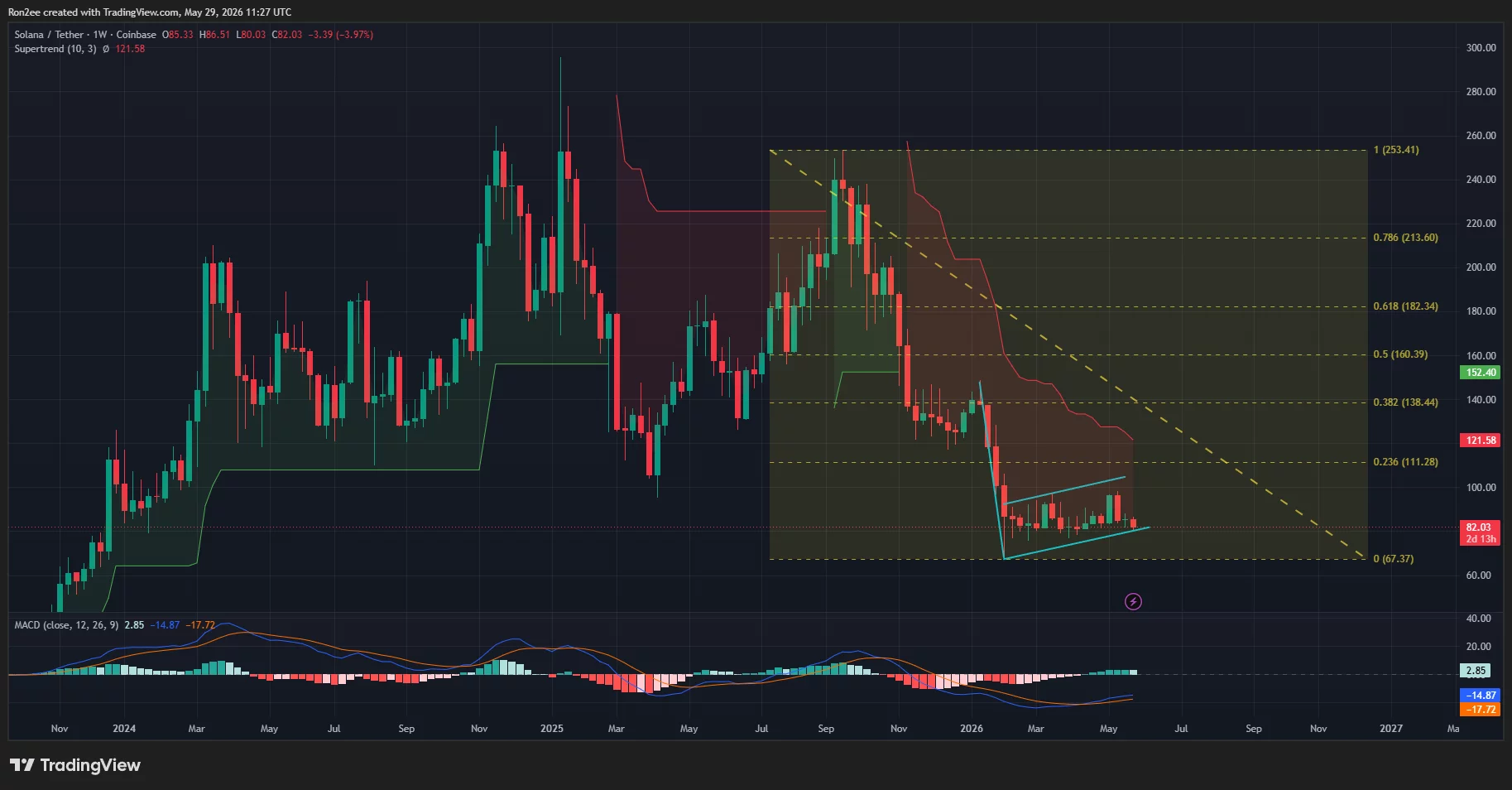
While the token remains well below the 0.236 Fibonacci retracement level near $111 and the weekly Supertrend resistance around $121, the $79-$80 support area has continued to attract buyers during repeated selloffs.
According to analysts at More Crypto Online, Solana could decline toward $62 if it fails to hold the key $72–$78 support zone. Conversely, a rebound above the May 12 high near $98 could pave the way for a move toward the $110 level.
Institutional sentiment toward Solana has remained mixed. Reports that Goldman Sachs liquidated its Solana ETF exposure earlier this year removed a notable source of institutional demand, while several asset managers continue pursuing crypto-related investment products tied to major layer-1 networks.
Traders have increasingly focused on whether fresh institutional participation emerges if market conditions stabilize during the second half of the year.
What technical risks could invalidate the bullish thesis?
The daily chart presents a more cautious picture. Solana price recently formed a bearish double-top pattern after failing twice near the $98 resistance area, first in March and again in May. The structure developed as momentum weakened across the recovery rally and sellers repeatedly defended the same overhead resistance zone.

The chart shows that SOL has already fallen below several short-term support levels near $90 and $85. The daily Supertrend indicator remains bearish around $91, while the MACD has crossed lower and continues to trend below its signal line.
A separate longer-term chart structure also warrants attention. The weekly timeframe shows SOL trading inside what appears to be a bearish flag formation following its collapse from the 2025 highs.
Technical analysis treats such formations as continuation patterns, with breakdowns often producing another leg lower in the direction of the previous trend.
Derivatives positioning remains defensive as well. Open interest across Solana perpetual futures has declined during the recent correction, suggesting traders have reduced leveraged long exposure rather than adding new bullish bets.
Funding rates on several major exchanges have remained negative, showing that short sellers continue to dominate positioning.
CoinGlass liquidation data highlights another important battleground around current prices. A large cluster of leveraged positions sits near the $80 level, making it one of the most significant liquidity zones on the chart. Additional liquidation pools are concentrated around $84, $85, and $86, where short sellers could face pressure if price stages a recovery.
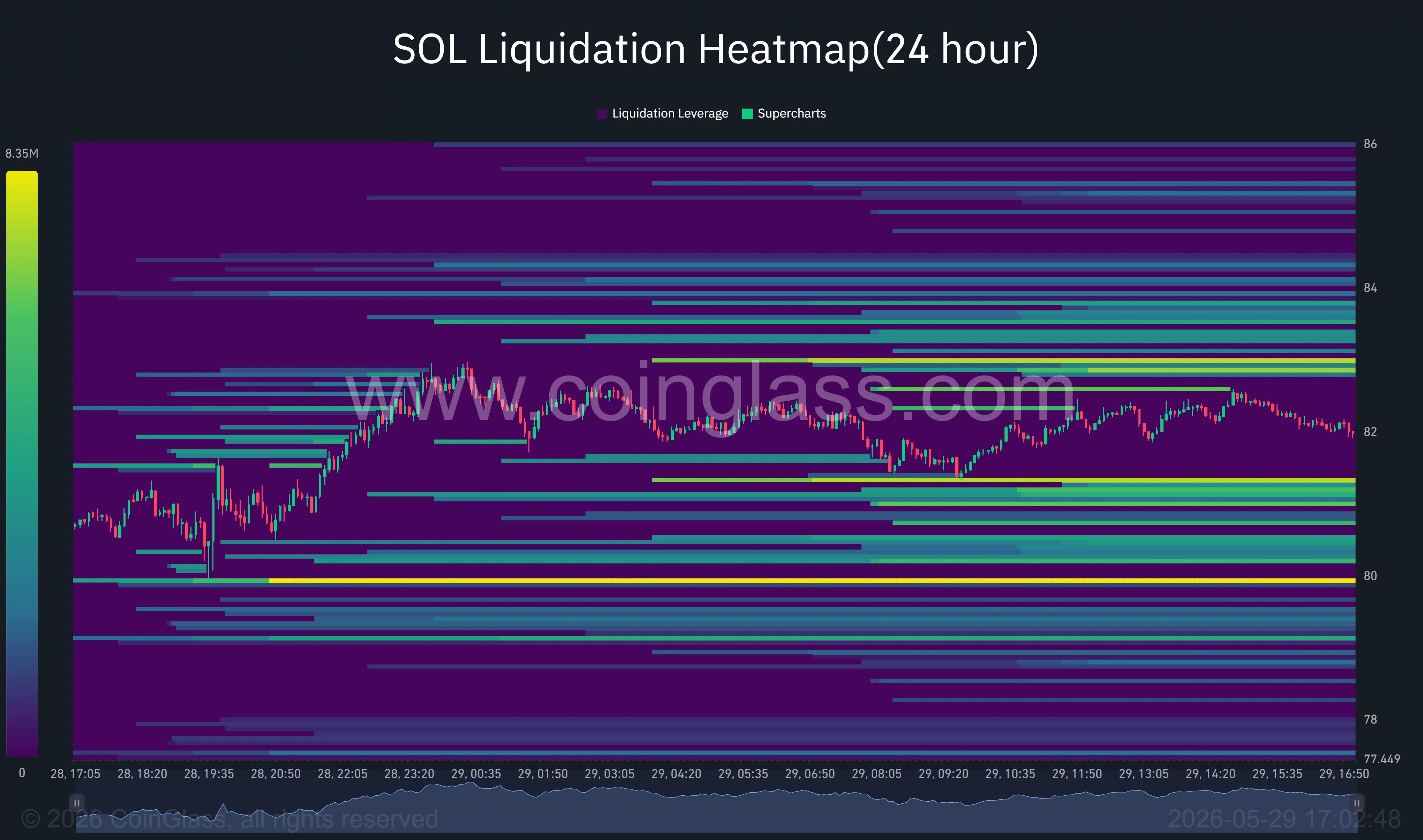
The heatmap suggests volatility could increase sharply if SOL breaks away from its current range. A move below $80 could trigger another wave of long liquidations and expose support near the $75-$77 region. Conversely, a recovery above $84 may force short-covering activity and create room for a move toward the $88 resistance cluster.
Macro conditions remain another source of uncertainty. Elevated oil prices have complicated expectations for Federal Reserve rate cuts later this year, particularly after recent inflation data showed price pressures remain stubbornly above target.
Higher borrowing costs and tighter financial conditions have historically weighed on high-beta cryptocurrencies such as Solana.
For now, traders appear focused on a single level. While daily charts continue to show a bearish double-top structure and weekly charts hint at a larger bearish flag, Scient’s thesis remains valid as long as the $79-$80 support zone survives.
Holding that area could allow buyers to target a recovery toward $100 and potentially $120, where volume profile data shows relatively limited resistance.
A decisive break beneath support, however, would invalidate the accumulation narrative and shift attention toward deeper downside targets that some analysts believe could extend well below the current trading range.
Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
Crypto World
TON price prediction 2026-2030: the Telegram takeover


Toncoin (TON) traded between $2.39 and $2.89 in late May 2026, doubling in roughly ten days after sitting at $1.30 on April 28. The catalyst was a single sentence from Pavel Durov on May 4. Telegram, the 950-million-user messaging app he founded, would replace the TON Foundation as the largest validator and primary force behind The Open Network. This isn’t a governance reshuffle. It’s a 950-million-monthly-active-user messaging platform formally fusing its entire ecosystem to one blockchain.
Summary
- Telegram’s takeover of TON as the network’s largest validator helped drive a rally from $1.30 to $2.89, supported by technical upgrades and new ecosystem developments.
- The bullish outlook depends on successful Telegram integration, stronger user adoption through TON Pay and Stars, and continued execution of the MTONGA roadmap.
- Regulatory setbacks, weak user adoption, or delays in Telegram’s rollout plans could keep TON under pressure and limit long-term growth.
The Catchain 2.0 upgrade (completed April 2026) brought block finality to 0.6 seconds, among the fastest of any major Layer 1. Transaction fees dropped 6x to $0.0005 per transaction. TON Pay 2.0 launches Q2 2026 for instant in-app payments. TON Teleport launches mid-2026, bringing Bitcoin liquidity into the ecosystem. TON Tech launched Agentic Wallets April 28 for AI agents operating on the network.
The MTONGA roadmap (“Make TON Great Again”) represents Durov’s 7-step plan for full Telegram-TON integration. Belarus approved TON for licensed banking and custody services on May 14, 2026. The network processed 1.5 billion transactions in Q1 2026 alone. TVL reached $1.2 billion. TON’s daily transaction volumes briefly surpassed Solana’s average during peak periods.
Telegram Ad Platform creates a demand loop: advertisers buy ad placements using TON, channel owners receive 50% crypto revenue share in TON. Telegram Stars expansion planned for Q3 2026.
The honest read: TON is the rare Layer-1 with distribution already solved. The risk sits entirely on execution, on Telegram delivering MTONGA on schedule, on users actually converting from messaging to payments, and on Durov’s French legal situation resolving without disrupting operations.
This piece walks through the mechanics, the bull case ($8 to $18 by 2030), the base case ($3 to $6), and the bear case ($0.80 to $2), with the specific variables that determine which one materializes.
Why TON is at $2.50 right now
The current Toncoin price reflects the resolution of one of the most concrete catalyst events in crypto for 2026: the formal Telegram takeover of the TON network announced May 4-5.
The starting point: TON traded around $1.30 on April 28, 2026, having declined 83% from its June 2024 all-time high of $8.24. The decline reflected uncertainty about Telegram-TON relationship clarity, broader altcoin weakness, and ecosystem development questions. TON had built substantial usage metrics (1.5B transactions Q1 2026, $1.2B TVL) without translation to proportional token appreciation.
The May 4-5 catalyst: Pavel Durov announced on May 4 that Telegram will replace the TON Foundation as the driving force behind TON and become its largest validator. The exact wording: “Telegram to replace the TON Foundation as the driving force behind TON and to become its largest validator.” Short, deliberate, and structurally big.
The structural significance: this is not governance reshuffling. It’s Telegram formally fusing its 950 million monthly active users to a single blockchain. The validator role means Telegram has direct economic stake in TON network performance. The “driving force” designation indicates Telegram will lead technical development, ecosystem building, and strategic direction rather than a community-run foundation managing these functions.
The immediate market response: TON ran from $1.354 open to $1.598 intraday high on $309 million volume (324% volume explosion). Subsequent days saw continued appreciation as the market priced in the structural change. By May 7, TON reached $2.89, representing 110+% appreciation from the April 28 close.
The Catchain 2.0 upgrade: completed in April 2026, the consensus upgrade brought block finality to 0.6 seconds, making TON among the fastest major Layer 1 blockchains. The technical capability matches or exceeds Solana (~400ms) and Aptos/Sui (sub-second). The performance enables consumer applications that require near-instant settlement.
The fee reduction: transaction fees dropped 6x to $0.0005 per transaction. The change enables economic viability for microtransactions and high-frequency consumer applications that previous fee structures couldn’t support. TON Pay 2.0 (Q2 2026 launch) targets sub-$0.0005 cost per transaction for Telegram-integrated payments.
The agentic wallets launch: April 28, 2026, TON Tech launched Agentic Wallets as an open standard for AI agents operating on the TON blockchain. The launch positions TON for the AI-crypto convergence narrative competing with NEAR’s positioning. AI agents can execute autonomous transactions through native TON infrastructure.
The MTONGA roadmap: Durov’s 7-step plan for fully integrating Telegram’s ecosystem with the TON blockchain. Sequential elements include Catchain 2.0 (completed), validator transition (in progress), TON Pay 2.0 Q2 2026, TON Teleport mid-2026 (Bitcoin liquidity integration), expanded Telegram Stars Q3 2026, and additional development phases through 2026-2027.
The regulatory developments: Belarus approved TON for licensed banking and custody services on May 14, 2026. This represents jurisdiction-specific regulatory acceptance that may signal a pathway for additional regulatory clarity. CLARITY Act framework could provide US regulatory clarity for TON as a commodity classification.
The transaction volume context: TON processed 1.5 billion transactions in Q1 2026, briefly surpassing Solana’s daily average during peak periods. The volume reflects existing Telegram-TON integration through mini-apps, Telegram Stars, and the ad platform without yet incorporating full MTONGA roadmap deployment.
The ad platform revenue loop: Telegram Ad Platform creates a demand loop where advertisers buy ad placements using TON, and channel owners receive a 50% crypto revenue share paid in TON. Every ad purchased creates buying pressure on TON. Every payout circulates TON through the ecosystem. The demand loop is different in kind from speculative demand cycles.
What the price action signals structurally: the May 2026 catalyst event represents one of the most concrete structural transformations in crypto. The market is repricing TON for the new reality where Telegram is formally driving network development with 950M MAU distribution. The current $2.50 level reflects partial repricing plus uncertainty about the execution timeline for the MTONGA roadmap. Significant additional appreciation depends on successful execution of the announced changes.
The bull case: $8-$18 by 2030
The bull case for TON requires the MTONGA roadmap to successfully execute across all phases plus significant user conversion to TON transaction activity.
The user conversion success: Telegram successfully converts a meaningful fraction of its 950 million monthly active users into TON transaction activity. Conservative bull case assumes 10-20% of users (95-190M users) become regular TON transactors. Average user transactions translate to substantial network volume and fee revenue. The conversion happens through TON Pay 2.0 (instant in-app payments), Telegram Stars expansion, mini-app integration, and creator economy applications.
The MTONGA roadmap execution: all 7 steps deploy successfully across the 2026-2027 timeline. TON Pay 2.0 launches Q2 2026 with seamless Telegram integration. TON Teleport mid-2026 brings Bitcoin liquidity, creating multi-chain utility. Expanded Telegram Stars Q3 2026 drives transaction volume. Additional development phases deliver promised functionality on schedule. The execution proves Telegram can deliver complex technical roadmap.
The payment volume scaling: TON Pay processing scales to billions of transactions monthly. The transaction volume drives validator economics, fee revenue, and structural TON demand through Universal payment dynamics. Telegram becomes the largest consumer-facing crypto payments network globally, leveraging WhatsApp/Messenger competitive gap in crypto integration.
The ad platform expansion: Telegram Ad Platform revenue scales significantly through expanded targeting capabilities, additional ad formats, and creator economy integration. The advertiser TON purchases and creator TON payouts create a sustained demand loop at increasing scale. Annual ad platform volume scales from current levels to billions of dollars equivalent.
The validator economics: Telegram’s validator role shows that institutional infrastructure can sustainably operate TON validators. Validator rewards (20+% APR mentioned in some sources) create attractive returns that drive additional staking participation. Staking ratio expands creating supply lock-up dynamics.
The competitive positioning: TON captures a meaningful share of the consumer crypto market from Solana, Ethereum L2s, and other competitors. The Telegram distribution advantage proves decisive for consumer adoption. While other chains compete for DeFi and institutional positioning, TON dominates consumer crypto through its messaging app integration.
The AI agents integration: Agentic Wallets standard enables AI agents to operate natively on TON. As AI agents become commercially significant, TON captures meaningful share through technical capability plus Telegram distribution. The positioning competes with NEAR for AI-crypto convergence.
The regulatory clarity: CLARITY Act framework provides US regulatory clarity. Belarus banking approval extends to additional jurisdictions. Durov’s legal situation resolves favorably without disrupting Telegram or TON operations. The regulatory pathway opens for institutional adoption beyond current crypto-native investor base.
The TON ETF potential: spot TON ETF eventually filed and approved following the patterns set by Bitcoin, Ethereum, Solana, and other crypto ETFs. Institutional accessibility expands beyond crypto-native investors to broader institutional and retail capital.
If multiple bull case conditions materialize, the price targets are:
- 2026 year-end: $5-9
- 2027 year-end: $7-13
- 2028 year-end: $8-16
- 2029 year-end: $8-17
- 2030 year-end: $8-18
The bull case requires sustained execution across user conversion, technical deployment, ecosystem expansion, and regulatory navigation. The most probable bull case outcome per multiple analyst frameworks targets $6-15 range over 2-4 years if Telegram-TON integration delivers expected user adoption and transaction volume.
The base case: $3-$6 by 2030
The base case assumes meaningful but not big MTONGA roadmap execution plus moderate user conversion.
The user conversion scenario: Telegram converts 3-8% of 950M MAU (28-76M users) to regular TON transaction activity. The conversion is meaningful but doesn’t reach the scale required for the bull case. User adoption develops gradually as TON Pay 2.0 launches and Stars expands.
The MTONGA execution: most roadmap steps deploy with some delays or modified scope. TON Pay 2.0 launches but with an extended rollout timeline. TON Teleport ships but Bitcoin liquidity integration takes longer to scale. Telegram Stars expansion happens but reaches a smaller portion of the user base than the bull case envisions.
The payment volume: TON Pay processes meaningful but modest transaction volume relative to the bull case. Hundreds of millions of monthly transactions rather than billions. Fee revenue grows from current levels without reaching transformative scale.
The ad platform: Telegram Ad Platform revenue continues at a moderate pace. Some advertisers adopt TON payments, some channel owners receive TON revenue share. The demand loop functions without explosive growth.
The validator economics: Telegram maintains validator role successfully. Additional institutional validators join. Staking ratio expands moderately. Validator economics stays sustainable.
The competitive dynamics: TON holds its position as a significant consumer-focused Layer 1, but faces continued competition from Solana, Ethereum L2s, and others. Market share is stable or slightly expanding rather than dominating consumer crypto.
The AI agents adoption: Agentic Wallets achieve some traction, but AI-crypto convergence happens across multiple platforms. TON captures specific use cases without dominating the AI agents market.
The regulatory environment: regulatory clarity develops gradually. Some jurisdictions approve TON for specific uses. Durov’s legal situation resolves without major disruption. ETF approval comes in 2027-2028 with modest initial flows.
Base case targets:
- 2026 year-end: $2.50-4
- 2027 year-end: $3-4.50
- 2028 year-end: $3-5
- 2029 year-end: $3-5.50
- 2030 year-end: $3-6
The base case represents meaningful appreciation from current $2.50 levels plus continued volatility around catalyst developments. The support comes from Telegram integration and ecosystem development without producing big price action.
The bear case: $0.80-$2 by 2030
The bear case requires either Telegram-specific setbacks or execution failures disrupting the MTONGA thesis.
The Durov regulatory action: Durov’s legal situation in France or other jurisdictions escalates significantly. Telegram faces restrictions on operations in major markets. The platform’s ability to drive TON integration is compromised by external regulatory pressure on Telegram’s broader business.
The user conversion failure: Telegram users don’t convert to TON transaction activity at meaningful scale. The 950M MAU number proves to be a vanity metric rather than predictive of crypto adoption. Telegram users use the messaging app without engaging with crypto features. TON Pay 2.0 launches but achieves low adoption.
The MTONGA execution failures: roadmap steps face significant delays, scope reductions, or quality issues. Telegram’s technical team encounters challenges delivering complex blockchain infrastructure. Multiple roadmap items get delayed beyond their announced timelines.
The competitive displacement: Solana captures consumer crypto market share through superior performance, deeper liquidity, and broader application ecosystem. WhatsApp or Messenger eventually launch competing crypto integrations leveraging their larger user bases. Telegram-TON loses competitive advantage.
The Telegram strategic shift: Telegram leadership changes priorities, reducing TON integration commitment. Alternative crypto strategies (Telegram Open Network 2.0, multi-chain approach, exit from crypto) emerge. The validator transition is reversed or significantly modified.
The validator economics failure: validator participation declines as institutional validators exit. Staking yields decline. The 20+% APR proves unsustainable. Network security concerns emerge.
The AI agents disappointment: agentic wallets fail to attract meaningful AI agent adoption. NEAR or other AI-focused chains capture the AI-crypto convergence market. TON’s positioning becomes incremental rather than differentiated.
The regulatory deterioration: CLARITY Act stalls or fails. International regulatory pressure increases on consumer crypto applications. Telegram faces restrictions on cryptocurrency features specifically. ETF approval is delayed indefinitely or rejected.
The technical failures: Catchain 2.0 or subsequent upgrades encounter post-deployment issues. Network outages affect user experience. Security incidents damage trust. The technical foundation supporting consumer adoption develops vulnerabilities.
The macro deterioration: broader crypto market weakness disproportionately impacts altcoins including TON. Consumer crypto applications face headwinds during risk-off periods.
Bear case targets:
- 2026 year-end: $0.90-1.80
- 2027 year-end: $0.80-1.80
- 2028 year-end: $0.80-1.90
- 2029 year-end: $0.80-1.95
- 2030 year-end: $0.80-2
The bear case represents significant downside from current levels but assumes TON retains some ecosystem positioning. Complete failure scenarios (price below $0.50) would require Telegram completely abandoning TON integration plus severe market dynamics.
The five variables that determine outcome
Five specific variables determine which scenario materializes.
Variable 1: TON Pay 2.0 launch and adoption (Q2 2026). The most important single near-term variable. Successful launch with meaningful user adoption validates Telegram-TON integration thesis. Delayed or limited launch signals execution challenges. Monitor: TON Pay 2.0 launch announcements, user activation metrics, transaction volumes through Pay 2.0, merchant adoption patterns, and Telegram integration completeness.
Variable 2: MTONGA roadmap execution across staying steps. Catchain 2.0 completed. Validator transition in progress. TON Pay 2.0 Q2 2026. TON Teleport mid-2026. Telegram Stars expansion Q3 2026.
Variable 2: MTONGA roadmap execution across staying steps. Catchain 2.0 completed. Validator transition in progress. TON Pay 2.0 Q2 2026. TON Teleport mid-2026. Telegram Stars expansion Q3 2026. Monitor: Pavel Durov public statements on roadmap progress, technical deliverable announcements, specific milestone completion dates, and quality assessments of deployed features.
Variable 3: User conversion to TON transaction activity. 950M Telegram MAU represents potential. Actual conversion to regular TON transactors is what drives sustainable value. Monitor: TON network active wallet counts, mini-app usage growth, Stars transaction volumes, ad platform participation rates, and overall on-chain activity metrics.
Variable 4: Validator transition status and economics. Telegram replacing TON Foundation as the largest validator is in progress. Sustainable validator economics with attractive yields drives staking participation. Monitor: validator participation rates, staking APR sustainability, TON staked supply growth, additional institutional validator announcements, and validator transition completion timeline.
Variable 5: Regulatory environment specifically affecting Telegram and TON. Durov’s legal situation, CLARITY Act passage affecting TON classification, additional jurisdiction approvals (following the Belarus pattern), and international regulatory dynamics. Monitor: Durov-related legal developments, regulatory announcements affecting Telegram, country-specific TON approvals or restrictions, and ETF filing developments.
The variables interact significantly. TON Pay 2.0 success drives user conversion. MTONGA roadmap execution validates Telegram commitment. Validator economics affect network security. Regulatory clarity enables broader institutional adoption. User conversion creates demand that affects everything else.
What this means for TON holders and traders
For current TON holders, the practical implication is that the asset has undergone a fundamental structural shift through the May 2026 Telegram takeover announcement. The five variables framework provides a way to evaluate whether the MTONGA roadmap is delivering expected outcomes. The current price reflects partial repricing for the new structural reality, with significant additional appreciation depending on execution.
For potential TON buyers, the practical implication is that entry at current $2.50 levels represents the post-catalyst price after the initial structural shift announcement. The risk-reward depends on assessment of MTONGA execution probability and user conversion potential. The Telegram distribution advantage is unique among Layer-1 tokens, but execution risk is concentrated in Telegram’s ability to deliver complex blockchain infrastructure.
For traders specifically, the practical implication is that TON has shown significant catalyst sensitivity (110+% appreciation in 10 days following announcement). Trading around MTONGA roadmap milestones requires monitoring Pavel Durov announcements, technical deliverable dates, and user adoption metrics. The catalyst-driven volatility creates both opportunities and risks.
For institutional investors evaluating TON allocation, the practical implication is TON offers exposure to consumer crypto adoption through unique Telegram distribution. The investment case depends on the belief that messaging app integration can produce sustainable crypto adoption at scale. Belarus banking approval and the CLARITY Act framework provide a regulatory pathway. ETF accessibility may develop following set crypto ETF patterns.
For Telegram users curious about TON adoption, the practical implication is the platform is actively building toward seamless crypto integration. TON Pay 2.0 (Q2 2026) and Telegram Stars expansion (Q3 2026) will provide direct user touchpoints for TON activity. The user experience improvements may make crypto more accessible than current alternatives.
The honest bottom line
On May 4, Pavel Durov announced that Telegram, not the TON Foundation, would run TON. Two days later, TON doubled. The market wasn’t pricing a governance reshuffle. It was pricing a messaging app with 950 million monthly active users formally tying its product roadmap to a single blockchain. TON Pay 2.0 is the next test. If it ships in Q2 and a meaningful slice of Telegram users actually use it for payments, the May rally is the beginning. If it slips or lands without traction, $2.50 is the top, not the floor.
The May 2026 Telegram takeover is fundamentally big. Pavel Durov’s announcement that Telegram replaces TON Foundation as the largest validator and primary driving force represents 950 million monthly active users formally fusing to one blockchain. This is unprecedented in crypto: no other Layer 1 has comparable distribution advantage through an existing major platform.
The technical capabilities are competitive. Catchain 2.0 produces 0.6-second finality matching or exceeding Solana, Aptos, Sui. Transaction fees at $0.0005 enable microtransactions. TON Pay 2.0 will integrate directly into Telegram for instant in-app payments. The technical foundation supports the consumer adoption thesis.
The main risks are real and material: Durov’s legal situation in France could escalate, affecting Telegram operations. User conversion to TON activity may prove difficult despite distribution access. MTONGA roadmap execution requires Telegram to deliver complex blockchain infrastructure on schedule. Competitive pressure from Solana and emerging consumer chains. Telegram strategic shifts could alter TON commitment.
The 2030 price range across scenarios is wide: $0.80-$18 depending on how the structural variables resolve. The base case ($3-$6) represents meaningful appreciation from current $2.50 levels, assuming MTONGA executes successfully with moderate user conversion. The bull case ($8-$18) requires big user conversion plus successful technical execution. The bear case ($0.80-$2) assumes execution failures or regulatory setbacks.
TON’s distribution problem is solved. What hasn’t been proven is whether Telegram can ship blockchain infrastructure on schedule. The distribution advantage is real and unique. The execution challenge is substantial. The next 6-12 months will determine whether Telegram can deliver the MTONGA roadmap on the announced timeline.
The TON Pay 2.0 launch is the most important near-term catalyst variable. Q2 2026 deployment with meaningful user adoption would validate the integration thesis. Delayed or limited launch would signal execution challenges.
User conversion is the most important sustainability variable. 950M MAU represents potential. Actual conversion to regular TON transactors determines whether the distribution advantage translates to sustainable token demand.
The Durov regulatory situation is the most important downside variable. Adverse developments could disrupt Telegram operations, affecting TON integration. Favorable resolution would remove an overhang affecting institutional positioning.
For 2026 specifically, expect TON to trade in the $2-$5 range with significant catalysts around TON Pay 2.0 launch, MTONGA roadmap milestones, user adoption metrics, and Durov-related developments. The support at $2-$2.50 reflects current Telegram integration positioning. The upside ($4-$7) depends on a successful TON Pay 2.0 launch and meaningful user adoption.
For 2027-2030, the structural variables compound. Sustained execution across roadmap delivery, user conversion, validator economics, and regulatory clarity produces a bull case trajectory. Deterioration produces a bear case. The base case assumes mixed outcomes producing meaningful appreciation.
The TON story is ultimately about whether messaging app distribution can produce sustainable crypto adoption at consumer scale. The early evidence is promising: 1.5B Q1 2026 transactions, $1.2B TVL, growing ad platform revenue, Telegram formal commitment through validator transition. The execution challenges are substantial but identifiable. The next phase will determine whether TON achieves the consumer crypto positioning that 950M MAU distribution makes possible.
Frequently Asked Questions
What happened with Pavel Durov’s TON announcement?
On May 4, 2026, Telegram CEO Pavel Durov announced Telegram would replace the TON Foundation as the driving force behind The Open Network and become its largest validator. This represents 950 million monthly active users formally fusing to one blockchain. TON surged from $1.30 (April 28) to $2.89 (May 7), representing 110+% appreciation in 10 days.
Can Toncoin reach $10 by 2030?
$10 is within the bull case range ($8-$18 by 2030). Required conditions: TON Pay 2.0 successful Q2 2026 launch with meaningful adoption, MTONGA roadmap executing across all 7 steps, significant user conversion from Telegram’s 950M MAU to TON activity, Telegram Stars expansion driving transaction volume, validator economics scaling sustainably, and a regulatory environment supporting institutional access. The base case for 2030 is $3-$6.
What is the MTONGA roadmap?
MTONGA stands for “Make TON Great Again” – Pavel Durov’s 7-step roadmap for fully integrating Telegram’s ecosystem with the TON blockchain. Sequential elements include: Catchain 2.0 upgrade (completed April 2026), validator transition (in progress), TON Pay 2.0 (Q2 2026), TON Teleport for Bitcoin liquidity (mid-2026), expanded Telegram Stars (Q3 2026), and additional development phases through 2026-2027.
How does TON’s 0.6-second finality compare to other chains?
Catchain 2.0 brought TON’s block finality to 0.6 seconds, among the fastest of any major Layer 1. Comparison: Solana ~400ms (Alpenglow target 150ms), Aptos sub-second, Sui sub-second, Ethereum L1 ~12 seconds, Bitcoin ~10 minutes. TON’s performance enables consumer applications requiring near-instant settlement and supports microtransactions at $0.0005 fee level.
What are the main risks to TON’s bull case?
Six primary risks: (1) Pavel Durov’s legal situation escalating, affecting Telegram operations, (2) user conversion failing to materialize at meaningful scale, (3) MTONGA roadmap execution facing significant delays or scope reductions, (4) competitive displacement by Solana or emerging consumer chains, (5) Telegram strategic shifts reducing TON integration commitment, (6) regulatory deterioration affecting Telegram messenger or TON specifically.
What is TON Pay 2.0?
TON Pay 2.0 is the next major version of TON’s Layer 2 payment network, designed specifically for the Telegram ecosystem. It aims to make peer-to-peer and merchant payments nearly instant and extremely cheap, targeting sub-$0.0005 cost per transaction. The Q2 2026 launch is positioned to enable seamless microtransactions for Telegram’s billion-plus user base.
How does TON compare to Solana for consumer crypto?
Both target consumer applications with high performance. Solana advantages: deeper DeFi ecosystem ($5.5B TVL vs TON’s $1.2B), broader institutional adoption (Solana ETFs trading vs no TON ETFs yet), longer track record. TON advantages: 950M MAU Telegram distribution advantage (Solana has no comparable consumer platform), formal validator commitment from a major tech platform, Catchain 2.0 sub-second finality. Different consumer crypto adoption pathways.
Should I buy TON given the recent rally?
This piece does not provide investment advice. Current $2.50 represents partial repricing after the May 2026 shift. Further appreciation depends on MTONGA roadmap execution and user conversion. The asymmetric upside potential (if execution succeeds) versus downside risk (if execution fails or Durov regulatory issues escalate) requires individual assessment. The five-variable framework provides objective monitoring signals.
This article is for informational purposes and does not constitute financial or investment advice. Cryptocurrency markets are highly volatile, and price predictions are inherently speculative. The figures and analysis described reflect data available as of late May 2026. Always do your own research and consult with qualified financial professionals before making investment decisions.
Crypto World
Trump vows to push pro-Bitcoin policies; SHRMiner cloud mining’s $7,000 passive income opportunity draws attention


Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
Trump’s crypto support boosts interest in Bitcoin and cloud mining platforms like SHRMiner among retail investors.
Summary
- Donald Trump’s recent pro-crypto remarks have increased optimism around a potentially friendlier U.S. regulatory environment for digital assets.
- Platforms such as SHRMiner are gaining attention by offering cloud mining access that removes the need for expensive hardware or technical mining expertise.
- SHRMiner provides multiple cloud mining contract options designed for users seeking either short-term flexibility or longer-term crypto mining reward exposure.
In an article published on Truth Social, Trump accused former SEC Chairman Gary Gensler and the “anti-crypto army” of nearly destroying the U.S. digital asset market by “pushing innovation overseas.”
“The United States is now the cryptocurrency capital of the world,” Trump wrote. He even pledged to establish a “future-proof digital asset market structure that those cryptocurrency opponents cannot shake.”
U.S. President Donald Trump recently publicly expressed his support for the cryptocurrency industry. His statement has bolstered optimism and is viewed by the market as a significant indication that the regulatory environment for digital assets in the U.S. may become more relaxed in the future. With improved policy expectations, more and more investors are refocusing on Bitcoin and cryptocurrency-related market opportunities.
The cloud mining model — exemplified by platforms such as SHRMiner — is rapidly gaining market attention. By offering rentable computing power services that yield mining rewards, this model eliminates the need for users to purchase expensive hardware or master specialized technical expertise, thereby making the economics of cryptocurrency mining more accessible to the average investor.
This article will delve into the core operational logic, participation methods, and market development trends of cloud mining and explore why, in 2026, an increasing number of investors are beginning to view cloud mining as a new wave of opportunities for generating cryptocurrency returns.
What is SHRMiner cloud mining?
SHRMiner is a leading global innovator in cloud mining services, dedicated to empowering the global Bitcoin network through its industry-leading cloud mining platform, rapidly expanding infrastructure, and innovative mining services, providing miners at all levels with the only way to access full cloud mining and earn BTC mining rewards.
How to earn passive income from BTC through SHEMiner cloud mining
Anyone can start earning money in just three simple steps.
1. Create an account: Complete registration to receive $15 in free computing power and earn $0.60 per day by purchasing a free trial contract (click here to complete registration).
2. Select a mining contract plan: Choose a popular short-term or long-term cloud mining contract (1–50 days available) based on financial preferences.
3. Start earning profits: After purchasing the contract, profits will be automatically settled within 24 hours without any additional management or operation. Users can withdraw their profits to their cryptocurrency wallet address at any time according to their own needs, or reinvest the profits to obtain higher returns.
The main advantage of this model is that it significantly lowers the barrier to entry. There is no need to research specific mining hardware models or computing power configurations, nor is there a need to build a personal system environment; simply complete account registration, deposit assets, and select a mining plan to start earning profits.
Selected popular cloud mining contract plans
SHRMiner offers a variety of yield-based cloud mining contract options to meet the investment preferences and financial goals of different users. Whether seeking flexible short-term returns or prioritizing stable long-term returns, users can find a suitable option on the platform.
Example of mining contract revenue
Contract Name
Price
Profit
Days
Principal+TotalReturn
NewUserExperienceAgreement
$100
$4
2
$100+$8
Bitdeer Sealminer A2 Pro
$500
$6.25
5
$500.00 + $31.25
Litecoin Miner L9
$1000.00
$13.00
10
$1000.00 + $130
Bitcoin Miner S21 XP Imm
$5000.00
$70.00
25
$5000.00 + $1750
Bitcoin Miner S21e XP Hyd
$10000.00
$150.00
35
$10000.00 + $5250
ANTSPACE HK3
$30000.00
$510.00
40
$30000.00 + $20400
For example, by leasing 300 TH/s of computing power — equivalent to a Bitcoin Miner S21 XP Imm mining rig — users can generate a BTC return of $1,750. Users can track their mining earnings in real-time via the control panel.
(Click here for more contract details).
Platform Core Advantages
- Zero Learning Curve: No technical skills required, no hardware needed, no complex procedures, and no hidden fees — simply click to earn.
- Bank-Grade Security: Dual security certification from McAfee® and Cloudflare®.
- Multi-Currency Mining Support: Earn major cryptocurrencies such as BTC, XRP, ETH, DOGE, USDC, USDT, SOL, LTC, BCH, and more.
- Global Coverage: Serving over 5 million users across more than 180 countries and regions. Enjoy 100% remote access; cloud-based operations are fully accessible via the SHRMiner app or web browser.
- UK-Compliant Operations: Holds a UK operating license, ensuring full regulatory compliance and transparency.
- 24/7 Technical Support: Our system operates with rock-solid stability around the clock, backed by a team of experienced experts and customer service representatives available to assist 24/7.
With SHRMiner, there is no need to be a technical expert or operate personal hardware. Users can directly invest in ASIC high-performance mining: completely transparent, zero-cost mining, and stable daily returns.
Affiliate Program:
Now, in addition to experiencing SHRMiner’s cloud mining services, users can also easily earn up to $30,000 in commission rewards through the platform’s limited-time affiliate promotion program.
Simply share an exclusive invitation link — whether via social media or by inviting friends to join — and get the opportunity to generate ongoing promotional earnings. This means that what is received daily is not merely income, but digital assets with the potential to appreciate in value over time.
An unimaginable earning opportunity
What sets SHRMiner apart is its extraordinary daily passive income potential, offering users the opportunity to earn $7,700 — or even more — every day, thereby realizing their dream of achieving financial success online. Imagine generating substantial income without the need for constant effort or complex setups — this is precisely what SHRMiner delivers.
In short
For those who are looking for ways to generate passive income, cloud mining is an excellent choice. When utilized effectively, these opportunities can help them effortlessly accumulate cryptocurrency wealth on “autopilot,” requiring only a minimal time commitment. At the very least, they should be far less time-consuming than any form of active trading. Passive income is the ultimate goal for every investor and trader, and with SHRMiner, maximizing passive income potential has never been easier.
For more information about SHRMiner, please visit its official website.
Disclosure: This content is provided by a third party. Neither crypto.news nor the author of this article endorses any product mentioned on this page. Users should conduct their own research before taking any action related to the company.
-

 Business5 days ago
Business5 days agoNYT Strands Answers May 24 2026 Revealed for Puzzle No. 812 Theme Summer Essentials
-

 Politics5 days ago
Politics5 days agoBridgerton Season 5: Cast, Release Date And Everything We Know So Far
-

 Crypto World7 days ago
Crypto World7 days agoRobinhood crypto COO Tanya Denisova exits
-

 Business3 days ago
Business3 days agoSelena Gomez Reportedly Upset Over Benny Blanco’s Comments on Her ‘Terrible’ Diet
-

 Tech5 days ago
Tech5 days agoMicrosoft’s quiet Claude Code retreat and the real cost of enterprise AI
-

 Crypto World3 days ago
Crypto World3 days agoMicron Crosses $1 Trillion Market Cap as AI Demand Reshapes Memory Sector
-

 NewsBeat3 days ago
NewsBeat3 days agoIsrael says it has killed new Hamas military leader in Gaza City airstrikes
-
 Business5 days ago
Business5 days agoBTS Sells Out Four Las Vegas Shows at Allegiant Stadium for ARIRANG World Tour
-

 Tech3 days ago
Tech3 days agoThe Samsung pay deal is the moment Korean unions changed register
-

 Tech3 days ago
Tech3 days agoMillions of AI agents imperiled by critical vulnerability in open source package
-

 Tech22 hours ago
Tech22 hours agoWaymo dominates autonomous vehicle registrations as Tesla trails behind
-
 Tech5 days ago
Tech5 days agoWestone Audio and Etymotic Acquired by Fidelity Collective in Major IEM Market Move
-

 Tech4 days ago
Tech4 days agoChina assigns ID codes to 28,000+ humanoid robots
-
Crypto World5 days ago
Nvidia (NVDA) CEO Calls on Super Micro to Strengthen Export Controls Amid Smuggling Probe
-

 Crypto World3 days ago
Crypto World3 days agoSpaceX’s $2 Trillion IPO: Why Tech Giants Nvidia (NVDA), Apple (AAPL), and Microsoft (MSFT) May Face Pressure
-

 Tech3 days ago
Tech3 days agoNASA taps Blue Origin to deliver lunar rovers for Moon Base initiative
-

 Crypto World5 days ago
Crypto World5 days agoBrian Armstrong Outlines Crypto Vision for the Future Financial System
-

 Entertainment4 days ago
Entertainment4 days ago‘Breaking Bad’ Star’s Easy-to-Binge 6-Part Crime Series Spin-Off Is Finally Heading to Free Streaming
-

 Crypto World3 days ago
Crypto World3 days agoSpain blocks prediction markets Polymarket Kalshi
-

 Business5 days ago
Business5 days agoYatra Online, Inc. 2026 Q4 – Results – Earnings Call Presentation (NASDAQ:YTRA) 2026-05-25










You must be logged in to post a comment Login